IoT Remote SSH Connection Example: Securely Accessing Your Devices
In an era where the internet of things (IoT) seamlessly connects billions of devices—ranging from smart home appliances to industrial sensors—remote management and reliable monitoring have become absolutely vital. This is, in a way, about making sure everything stays connected and working, even when you are far away. You see, an IoT remote SSH connection is a perfect way to securely monitor these diverse devices. It truly offers a dependable path to keep an eye on things, providing peace of mind and operational control from almost anywhere.
The internet of things, or IoT, refers to the collective network of connected devices and the technology that facilitates communication between devices and the cloud, as well as between the devices themselves. These physical objects, like vehicles or appliances, are usually embedded with software, sensors, and other bits that allow them to gather and exchange data without direct human help. So, it's about making the physical world more digitally interactive, you know?
With the widespread use of IoT devices, getting to them from afar and handling them has become quite important for keeping things safe and running well. Secure Shell, often called SSH, is a widely used protocol that helps with this. It's one of the most popular ways to manage connected devices in a remote format, offering a secure channel for all your interactions. This article will help you understand how to use an IoT remote SSH connection example, making sure you can access your devices without any big worries.
- Baby Alien Fan Bus
- Help I Accidentally Summoned Mahoraga
- Kimberly Guilfoyle Before And After
- Camarones A La Diabla
- Shasha Prasad
Table of Contents
- What is IoT and Why Remote Access Matters
- Understanding SSH for IoT Devices
- Setting Up an IoT Remote SSH Connection Example
- Security Best Practices for IoT SSH
- When SSH Might Not Be Enough: Considering Alternatives
- Frequently Asked Questions About IoT Remote Access
What is IoT and Why Remote Access Matters
The internet of things, or IoT, stands for the interconnectedness of physical devices, like appliances and vehicles, that are embedded with software, sensors, and network bits. These items can transfer data to one another without human intervention, which is pretty amazing. According to Lewis, IoT is the integration of people, processes, and technology with connectable devices and sensors to enable remote monitoring and status updates. It's about bringing the physical world into a digital view, you know, for better control.
Simply put, the term internet of things refers to the entire network of physical devices, tools, appliances, equipment, machinery, and other smart objects that have the capability to collect data. This data is then exchanged with other devices or systems over the internet. The concept itself was first introduced by computer scientist Kevin Ashton, and it's been growing ever since. This interconnectedness allows for things like smart homes, industrial automation, and even health monitoring, which is actually quite useful.
Remote access to these devices has become absolutely essential. Think about it: you can't always be physically next to every smart light bulb, factory sensor, or remote weather station. So, being able to check on them, fix issues, or update their software from a distance is a huge time-saver and makes operations much smoother. This is where an IoT remote SSH connection example really shines, offering a way to keep everything running without needing to be right there, which is a big deal for businesses and individuals alike.
- What Does Nvm Mean
- What Is A Femboy
- Remoteiot P2p Download
- Timothee Chalamet Net Worth
- How To Ripen Avocados
Understanding SSH for IoT Devices
SSH, which stands for Secure Shell, is a network protocol used to securely access and manage computers and other devices over an unsecured network. It provides a secure channel over an insecure network by using strong encryption. This means that any information you send or receive through an SSH connection is protected from being seen by others, which is very important for privacy and security. It's one of the most reliable tools available for ensuring secure connections between devices, so you can really trust it.
For IoT devices, SSH is especially valuable because these devices are often deployed in various locations, sometimes in places that are hard to get to. SSH IoT access is one of the most popular ways to manage connected devices in a remote format, allowing administrators to execute commands, transfer files, and even set up tunnels for other services. This guide, for example, will delve into the details of remote access for IoT devices using SSH, helping you grasp how it all works. It's a pretty straightforward process once you get the hang of it.
To fully grasp an IoT remote SSH example, it's important to understand the basics of SSH itself. This article aims to simplify the complexities of remote IoT device SSH connections, offering practical examples and expert tips to help you master the process. By the end of this, you should feel much more comfortable with setting up and using SSH for your IoT projects. It's a tool that truly offers a lot of control and security, which is pretty cool.
Setting Up an IoT Remote SSH Connection Example
Setting up an IoT remote SSH connection involves a few key steps. It's not too difficult, but paying attention to the details helps. You'll need to prepare your IoT device, generate secure keys, and then make the connection. This section will walk you through the process, providing a clear IoT remote SSH connection example that you can follow. It's all about making sure your devices are reachable and safe, you know?
Prerequisites for Your Device
Before you try to connect, your IoT device needs to be ready. First, it should be connected to a network, either Wi-Fi or Ethernet, that has internet access. Second, you'll need to make sure SSH is enabled on the device itself. Many Linux-based IoT devices, like Raspberry Pis, usually have an SSH server pre-installed, but it might need to be turned on. You might need to access the device locally first, perhaps with a keyboard and monitor, to enable this feature. This is, you know, a pretty standard first step.
Also, you'll want to know your device's IP address on the network. This is how you'll tell your computer where to connect. You can usually find this by logging into your router's administration page or by running a command on the IoT device itself, like `ifconfig` or `ip addr show`. Knowing the user account and its password on the IoT device is also a must. For many default setups, there's often a common username like "pi" for Raspberry Pi devices, but it's always good to check. So, have those details handy, that's what you need.
Generating SSH Keys
Using SSH keys for authentication is a much more secure method than relying solely on passwords, which is something you really want for your IoT devices. SSH keys come in pairs: a public key and a private key. The public key goes on your IoT device, and your private key stays safe on your computer. When you try to connect, the device checks if your private key matches its public key, which is a pretty clever way to verify who you are.
To generate these keys on your computer, you can use a tool like `ssh-keygen` in your terminal or command prompt. You'll typically run `ssh-keygen -t rsa -b 4096`, which creates a strong 4096-bit RSA key pair. It will ask you where to save the keys and if you want to set a passphrase for your private key. Setting a passphrase is a very good idea, as it adds an extra layer of security, so you should definitely consider it. Once generated, you'll have two files, usually `id_rsa` (your private key) and `id_rsa.pub` (your public key).
After generating the keys, you need to copy the public key to your IoT device. The `ssh-copy-id` command is a convenient way to do this: `ssh-copy-id username@your_device_ip`. If that command isn't available, you can manually copy the contents of your `id_rsa.pub` file to the `~/.ssh/authorized_keys` file on your IoT device. This step essentially tells your IoT device, "Hey, trust this specific key for access." It's a pretty critical part of the setup, you know, for secure access.
Connecting to Your IoT Device
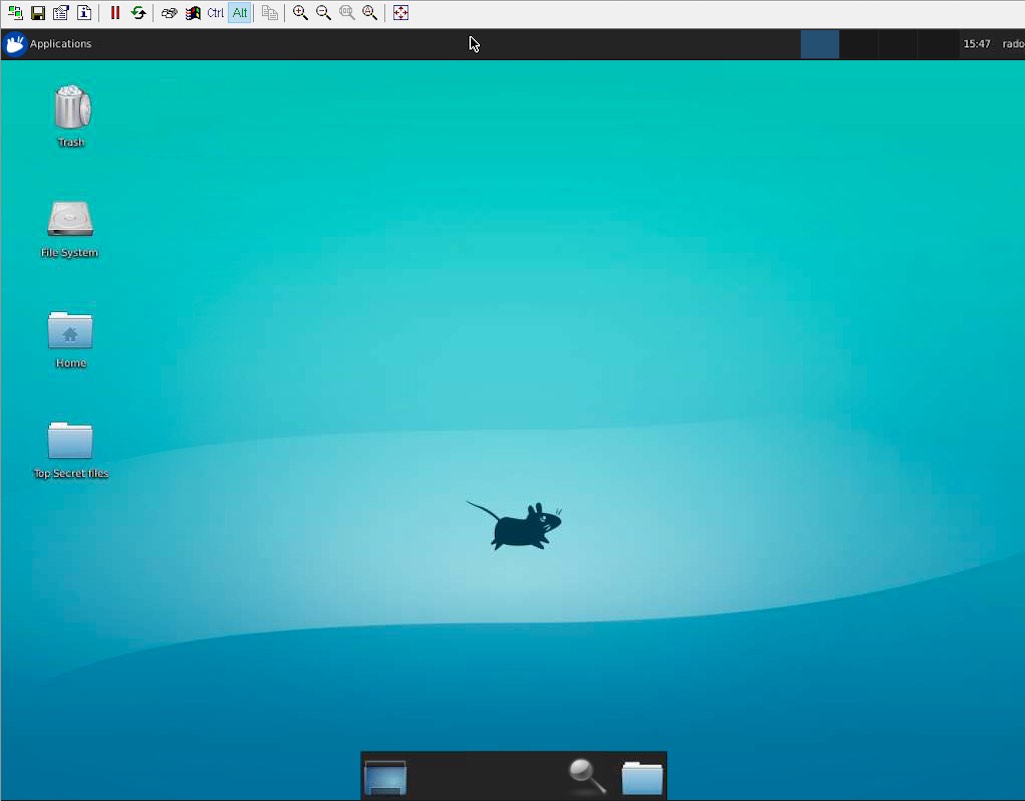
Once your public key is on the IoT device, you can establish an SSH connection from your computer. The basic command is `ssh username@your_device_ip`. If you set a passphrase for your private key, you'll be prompted to enter it. After successful authentication, you'll be logged into your IoT device's command line, just as if you were sitting right in front of it. This is where the magic of remote access truly happens, and it's quite satisfying when it works, really.
For example, if your IoT device's username is "pi" and its IP address is 192.168.1.100, you would type `ssh pi@192.168.1.100`. From here, you can run commands, install software, check system status, or even restart the device. This kind of remote control is what makes managing a fleet of IoT devices so much more practical. It's a fundamental step for any kind of serious IoT deployment, so you want to get it right.
You can also use SSH for more than just a command line. For instance, you can securely transfer files between your computer and the IoT device using `scp` (Secure Copy Protocol) or `sftp` (SSH File Transfer Protocol). This means you can easily update device firmware or upload new scripts. An IoT remote SSH connection example isn't just about getting in; it's about doing meaningful work once you are connected, which is actually pretty useful.
Security Best Practices for IoT SSH
Establishing an optimal SSH connection for IoT environments involves understanding the unique challenges of IoT devices, network constraints, and security considerations. Because IoT devices can be scattered and often have limited resources, keeping them secure is paramount. SSH is one of the most reliable tools available for ensuring secure connections between devices, but its effectiveness depends on how well you implement security best practices. So, you know, it's not just about setting it up, but setting it up smartly.
Strong Passwords and Key Management
Even though SSH keys are preferred, some situations might still require password authentication. If you use passwords, make sure they are very strong: long, complex, and unique for each device. Never use default passwords, as these are often the first targets for attackers. More importantly, always use SSH key-based authentication whenever possible, as it provides a much higher level of security. And remember to protect your private SSH keys with a strong passphrase, and never share them. This is, like, absolutely critical for security.
Managing your SSH keys properly is also a big deal. Regularly audit the public keys stored on your IoT devices to make sure only authorized keys are present. If an employee leaves or a device is decommissioned, remove their associated public keys from all devices. This helps prevent unauthorized access down the line. It's a bit like changing the locks when someone moves out; it just makes sense, you know, for ongoing safety.
Limiting User Access
When setting up an IoT remote SSH connection example, it's a good idea to create separate user accounts for different purposes or individuals, rather than using a single "root" or administrator account for everything. Give each user only the permissions they need to perform their tasks, nothing more. This concept, known as the principle of least privilege, reduces the potential damage if an account is compromised. For instance, a user who only needs to read sensor data shouldn't have the ability to modify system files, so that's a key point.
You can also configure SSH to restrict certain users to specific commands or directories. This adds another layer of security, preventing accidental or malicious actions. For example, you might set up an SSH user that can only run a specific script to gather data and nothing else. This kind of fine-grained control is very helpful for maintaining system integrity, especially with many devices, which is pretty important.
Regular Updates and Patching
Keeping your IoT devices and their SSH software up-to-date is absolutely essential for security. Software vulnerabilities are discovered all the time, and manufacturers release updates or patches to fix these issues. Ignoring these updates leaves your devices exposed to known exploits. Make it a habit to regularly check for and apply updates to your device's operating system, firmware, and any SSH-related software. This is, you know, just good practice for any connected device.
Automating updates where possible can help ensure your devices are always protected, especially if you have many of them. However, always test updates on a small group of devices first to avoid any unexpected issues. A proactive approach to patching means you're always one step ahead of potential threats, which is a much better position to be in. So, really, don't skip those updates, they matter a lot.
When SSH Might Not Be Enough: Considering Alternatives
While an IoT remote SSH connection is a powerful and secure way to manage individual devices, it's important to recognize that it might not be the most scalable or efficient solution for every scenario. Learn how to access IoT devices remotely with SSH and why SMBs outgrow it fast. Discover smarter, scalable alternatives for IT admins, as the text suggests. For small deployments or one-off tasks, SSH works wonderfully, but as your IoT network grows, its limitations can become apparent, which is something to consider.
Scalability Concerns
Managing hundreds or thousands of IoT devices individually via SSH can become a logistical nightmare. Each device requires its own connection, and keeping track of all the SSH keys, user accounts, and configurations can be incredibly time-consuming and prone to errors. Imagine trying to update software on 500 devices one by one using SSH; it would take forever. This is where the manual nature of SSH for large-scale operations really shows its drawbacks, so that's a big point.
For larger deployments, you'll likely need solutions that offer centralized management, automated provisioning, and group-based policies. These systems can push updates, deploy configurations, and monitor device health across your entire fleet from a single dashboard. While SSH might still be used as an underlying protocol, it's often abstracted away by these more sophisticated platforms. This shift from individual device management to fleet management is, you know, a natural progression for growing IoT systems.
Centralized Management Needs
As the internet of things continues to evolve, secure remote access to IoT devices using SSH has become a critical requirement for modern businesses. However, for many businesses, especially those with many devices, a more centralized approach is often better. This article delves deep into IoT remote SSH examples, explaining how to set up secure connections, best practices for implementation, and the tools needed to manage IoT. But it also hints at the need for something beyond just SSH for comprehensive control.
Centralized IoT management platforms, like those offered by cloud providers, can provide a single point of control for all your devices. These platforms often include features like device registries, secure communication channels (which might use protocols other than or in addition to SSH), over-the-air (OTA) updates, and data ingestion services. They help you handle device authentication, authorization, and monitoring at scale. SSH IoT device anywhere AWS example is a hot topic right now, and for good reason; it’s all about enabling remote access to IoT devices without compromising security, but often through a broader cloud framework. You can learn more about secure device management on our site, which is pretty useful.
These platforms also typically offer better integration with other business systems and analytics tools, allowing you to get more value from your IoT data. While SSH remains a fundamental tool for direct device interaction, particularly for troubleshooting or initial setup, a comprehensive IoT strategy for larger organizations will usually involve a more holistic management solution. For instance, using a cloud-based IoT platform can simplify device onboarding and ongoing maintenance significantly, which is a definite plus. You can also check out this guide on IoT cloud integration for more details.
Frequently Asked Questions About IoT Remote Access
Here are some common questions people ask about getting to their IoT devices from afar.
What is the Internet of Things (IoT) exactly?
The Internet of Things, or IoT, refers to a network of physical devices, vehicles, appliances, and other physical objects that are embedded with sensors, software, and network bits. These items can connect and exchange data with other devices and systems over the internet. So, it's basically about everyday things having digital brains and being able to talk to each other, which is pretty neat, you know?
Why is SSH considered secure for IoT devices?
SSH is considered secure because it uses strong encryption to protect the communication channel between your computer and the IoT device. This means that any data, commands, or files transferred are scrambled and cannot be easily intercepted or read by unauthorized parties. It helps ensure that only authorized individuals can access and manage your devices, which is very important for keeping your data safe, so that's a big reason.
Are there any risks to using SSH for IoT remote access?
Yes, there can be risks if SSH is not configured properly. Weak passwords, unmanaged SSH keys, or outdated software can create vulnerabilities that attackers might exploit. It's really important to follow security best practices, like using strong keys, limiting access, and keeping software updated, to minimize these risks. When done right, SSH is very secure, but neglecting these steps can cause problems, you know, like with any powerful tool.
- How Long Does It Take For Eyelashes To Grow Back
- Do A Barrel Barrel Roll
- Sophie Rain Spiderman Video
- How To Cook Scallops
- Just Give Me My Money

IoT SSH Remote Access - SocketXP Documentation

How to Remote Access IoT SSH over the Internet
IoT Remote Access