Securely Connect Remote IoT: P2P SSH Options You Can Download Free
Are you feeling a bit stuck with your remote devices, maybe getting those frustrating messages like, "Your device is at risk because it's out of date and missing important security and quality updates"? It's a common worry, really. Perhaps you've even seen warnings pop up, like "This connection is untrusted you have asked firefox to connect securely to bay173.mail.live.com, but we can't confirm that your connection is secure." These alerts, as Jerrywoods2 mentioned, can show up across different browsers, making it seem like there's no way around them. It's truly a problem when you just want your gadgets to work safely, isn't it?
Connecting to things far away, especially those small smart gadgets, can feel like a puzzle. You want to check on them, send new instructions, or just make sure they are doing okay. But there's always that big question about keeping everything private and safe. You certainly don't want just anyone peeking in or messing with your valuable information, so that's a real concern for many.
Good news, though! There are practical ways to get your devices talking securely, even when they're far off. We're going to explore how you can securely connect remote IoT devices using something called P2P SSH, and yes, we'll talk about options you can download free. It's about getting you back on track so your smart things can run more securely, and that's what we'll cover.
- Just Give Me My Money
- Do Female Cats Spray
- Filmy Fly Com
- Sophiexyz Spiderman
- Surrealism Dress To Impress
Table of Contents
- Understanding Your Remote IoT Security Challenges
- What is P2P SSH for IoT?
- Getting Started: Free Tools to Securely Connect Remote IoT
- Step-by-Step: Securely Connecting Your IoT Device
- Keeping Your IoT Connections Safe and Sound
- Common Hurdles and Simple Solutions
Understanding Your Remote IoT Security Challenges
When you have smart devices out there, whether it's a camera, a sensor, or a tiny computer, keeping them safe is a big deal. These gadgets are often connected to the internet, and that connection can sometimes be a weak spot. It's like having a front door that's a bit flimsy; you want to make sure it's as strong as possible, so that's a good way to think about it.
The Risks of Outdated Devices
You know how your computer sometimes tells you it's "out of date and missing important security and quality updates"? Well, that's a very real concern for smaller smart devices too. Just like your Windows 11 PC needing updates to log in securely, as Albert Edelstein found with his PIN not working, these tiny devices need fresh software too. Old software can have little holes that bad actors might use to get in, which is pretty unsettling.
When software gets old, it's like leaving a window open for trouble. These little openings are called vulnerabilities, and they can allow someone to sneak into your device. This could lead to your device being controlled by someone else, or your information being stolen, so it's a pretty serious matter.
- Kimberly Guilfoyle Before And After
- How Long Does It Take For Eyelashes To Grow Back
- How Many Dogs Does Steve Horstmeyer Have
- Is Clarke From Love Island Trans
- Jasmine Crockett Husband
Keeping your devices updated is truly one of the simplest and most effective ways to keep them safe. It's like putting a fresh, strong lock on that front door we talked about, and that's a step you really don't want to skip.
Why Connections Feel Untrusted
Have you ever seen that message, "This connection is untrusted you have asked firefox to connect securely to www.xxxxxxxxxxxx.com, but we can't confirm that your connection is secure"? That's a common alert, and it means your browser isn't sure if the place you're trying to reach is really who it says it is. This often happens because of something called a security certificate, which is like an ID card for a website or a device, so it's quite important.
If that ID card is missing, expired, or just not right, your browser gets suspicious. It's trying to protect you from potentially fake or harmful places. For your own remote IoT devices, if you set them up without proper certificates, your browser or connecting software might give you the same scary warning, which is certainly something to consider.
This "untrusted" message is a good sign that you need to check things out. It means there's a problem connecting securely, and you want to fix that before you send any sensitive commands or data to your remote device, so it's a useful alert.
The Need for a Better Way
Given these worries about outdated systems and untrusted connections, it's clear we need a solid plan for remote IoT. You want a way to connect that feels direct, private, and doesn't cost an arm and a leg. Nobody wants to deal with constant security warnings or the thought of their devices being exposed, so that's a big motivator.
We need methods that bypass common pitfalls, like complicated network setups or relying on third-party servers that might introduce their own risks. The goal is to have a secure line straight to your device, giving you peace of mind, and that's what we're aiming for.
This is where understanding P2P SSH comes in handy. It offers a path to that direct, secure communication you're looking for, often with free tools that make it accessible to everyone, which is really quite helpful.
What is P2P SSH for IoT?
Let's break down what P2P SSH means for your small smart devices. It's a combination of two powerful ideas that, when put together, create a very secure way to talk to your gadgets from afar. It's a bit like having a secret handshake and a private telephone line, so it's pretty clever.
SSH: Your Secure Remote Door
SSH stands for Secure Shell. Think of it as a very strong, encrypted tunnel for your commands and data. When you use SSH, anything you send between your computer and your remote device is scrambled up so no one else can read it. It's a bit like sending a message in a secret code that only your device and your computer know how to crack, and that's a huge plus for security.
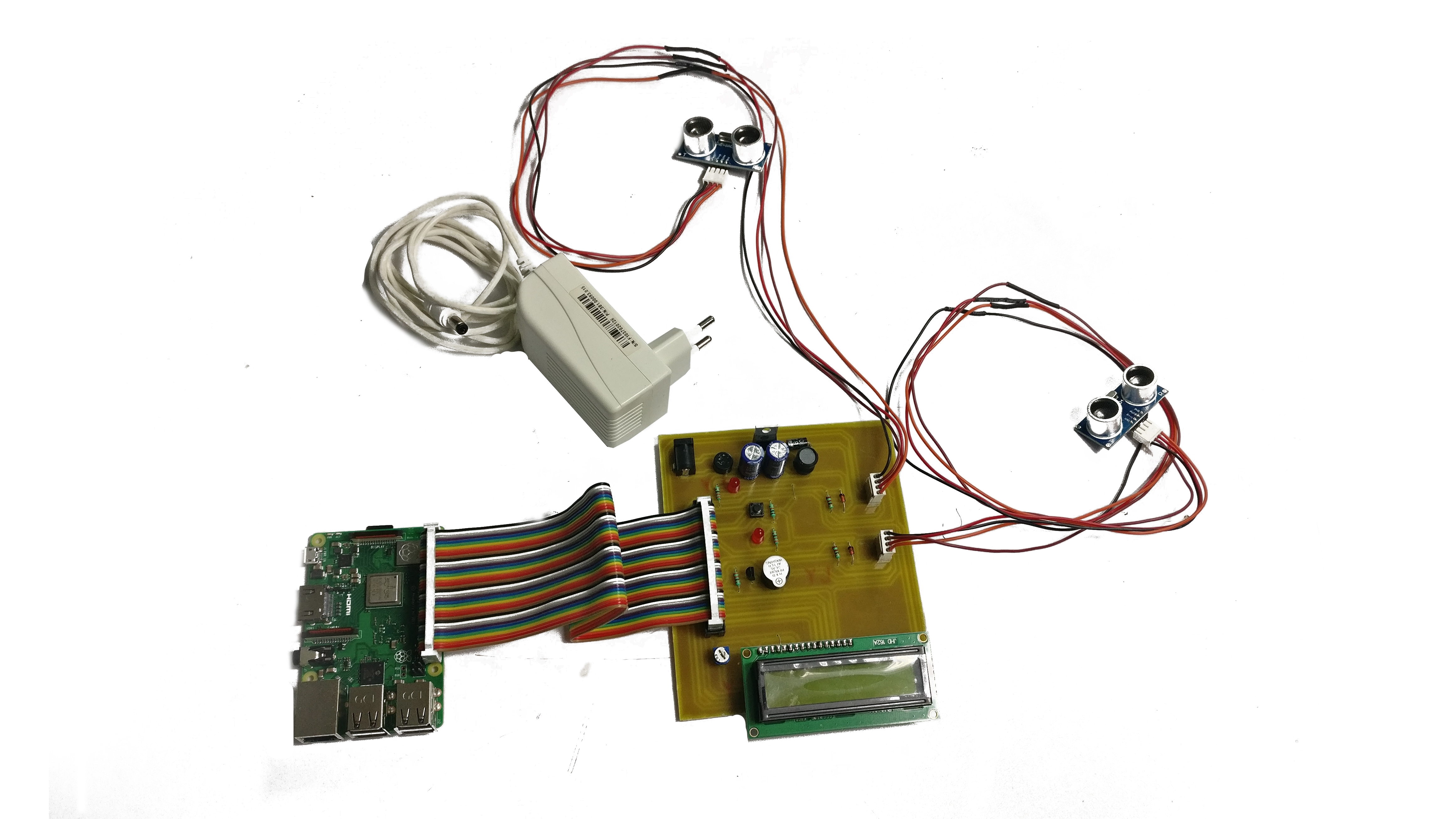
Many remote devices, like a Raspberry Pi, have SSH built right in. This means you can send commands, move files, and even run programs on them as if you were sitting right in front of them, but you're doing it safely from anywhere, which is incredibly convenient.
SSH is widely used by professionals because it's so reliable and secure. It's a foundational tool for remote administration, and it's also available as free software, which is great for anyone looking to securely connect remote IoT devices.
P2P: Direct Device Talk
P2P means "Peer-to-Peer." In simple terms, it means your computer talks directly to your IoT device, without a big central server in the middle acting as a go-between. This can be really good for speed and privacy, as your data isn't bouncing through extra places, so it's a more streamlined approach.
For IoT, true P2P can be tricky because devices are often behind home routers that block direct incoming connections. However, "P2P-like" solutions use clever tricks to make a direct path, even through these network obstacles. It's like finding a secret tunnel around a big wall, which is pretty neat.
The benefit of a P2P approach is that it can reduce reliance on external services, potentially lowering costs and increasing privacy. It means your connection is more self-contained, and that's a very appealing idea for many users.
Why This Combo Works for IoT
Combining SSH's strong encryption with a P2P or P2P-like connection method gives you a very powerful setup for remote IoT. You get the security of SSH protecting your data, and the directness of P2P making your connection efficient and often more resilient, which is a really good combination.
This approach helps solve the "untrusted connection" problem because you're creating your own secure tunnel. You're not relying on public certificates for a website, but rather on the strong encryption and key-based authentication of SSH itself, so it's a different kind of trust.
And the best part? Many of the tools to achieve this are open-source and free to download. This makes securely connecting remote IoT devices accessible to almost anyone, which is a fantastic opportunity for many.
Getting Started: Free Tools to Securely Connect Remote IoT
Alright, so you're ready to get your hands dirty and set up these secure connections. The good news is that you don't need to spend any money on fancy software. There are plenty of free, reliable tools out there that can help you achieve this, so it's pretty accessible.
Choosing Your Free SSH Client
On your computer, you'll need an SSH client. This is the software that lets you talk to your remote IoT device. If you're using Linux or macOS, you probably already have OpenSSH built right in. You just open your terminal or command prompt, and it's ready to go, which is super convenient.
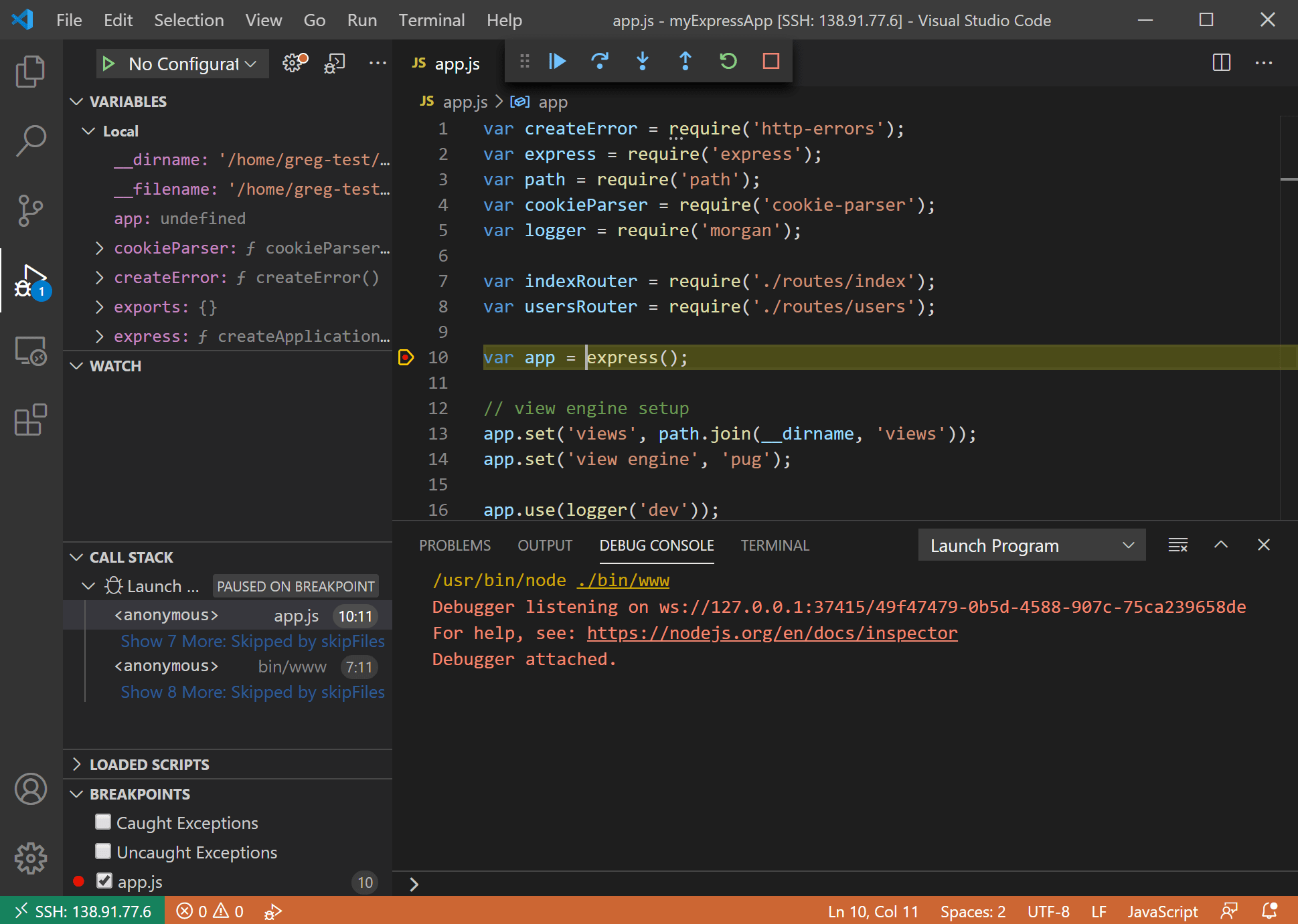
For Windows users, things have gotten much easier. Modern versions of Windows 10 and 11 also include OpenSSH client, so you can use it directly from PowerShell or Command Prompt. If you have an older Windows version or prefer a graphical interface, PuTTY is a very popular and free choice, and it's been around for ages, so it's very reliable.
These clients are truly your gateway to your remote devices. They handle the secure encryption and allow you to send commands safely, which is the core of our secure connection plan.
Setting Up SSH on Your IoT Device
Most small IoT computers, like a Raspberry Pi, can have SSH enabled very easily. Often, it's just a setting you flip on during the initial setup or a quick command you run. This makes your device ready to accept secure connections from your client, so it's not a complicated process.
For example, on a Raspberry Pi, you can use the `raspi-config` tool or simply create an empty file named `ssh` in the boot partition of your SD card before you even start it up. This tells the device to turn on SSH, which is a neat trick.
Make sure your IoT device is connected to your local network, at least initially. You'll need to know its local IP address to connect to it for the first time, and that's a key piece of information.
Establishing a P2P-like Connection
Achieving a direct "P2P" connection to an IoT device behind a typical home router can be a bit of a challenge due to network address translation (NAT). However, there are free tools and methods that create a *P2P-like* secure tunnel, making it feel direct.
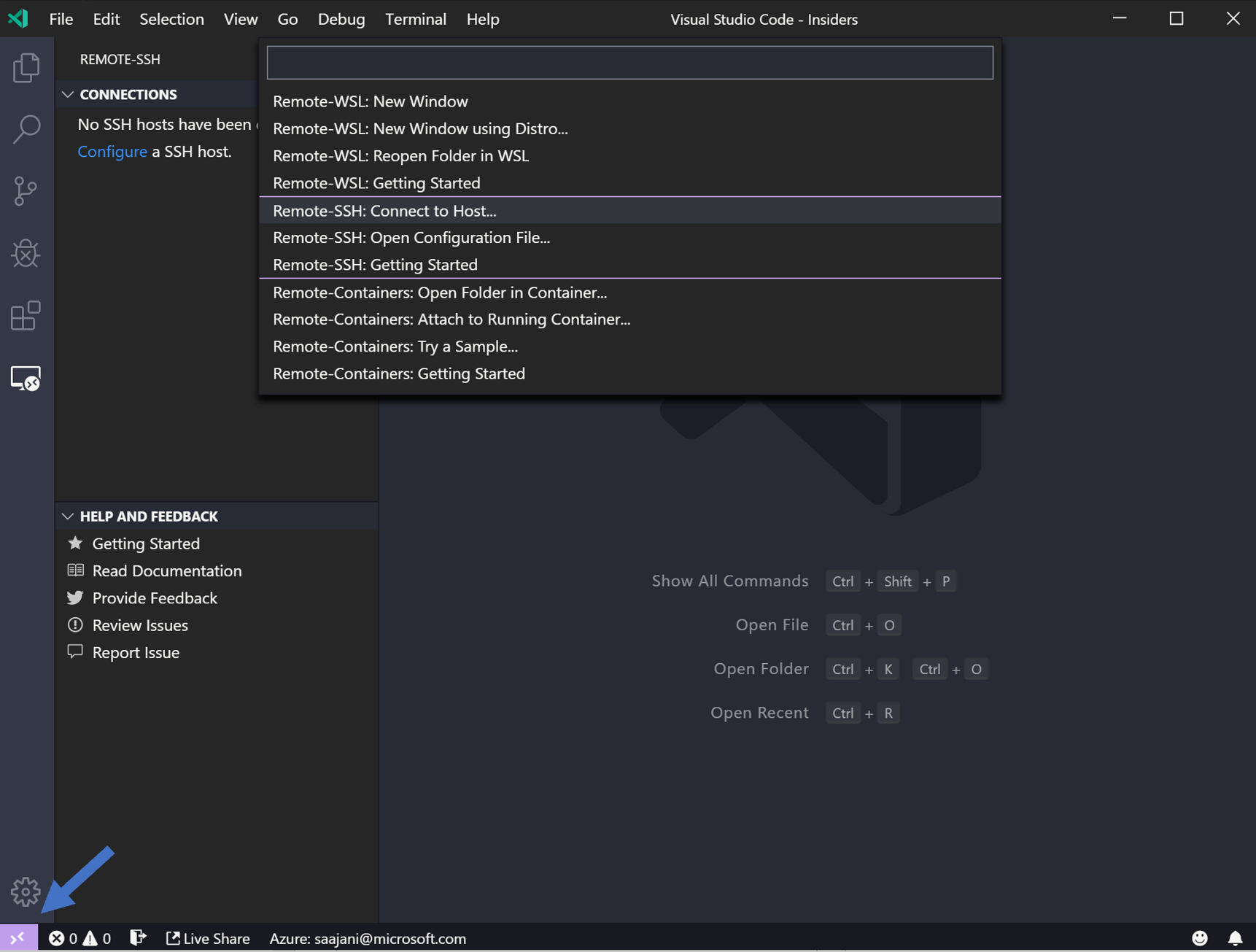
One common way is using a virtual private network (VPN) solution that supports P2P tunneling. Tools like ZeroTier or Tailscale offer free tiers that create a virtual network where all your devices, no matter where they are, can talk to each other as if they're on the same local network. This effectively creates a P2P-like environment for your SSH connection, which is pretty clever.
You install a small client on both your main computer and your IoT device, and they then join this virtual network. Once they're part of it, you can SSH directly to your IoT device using its virtual IP address, bypassing many of the usual router headaches. This is a powerful way to securely connect remote IoT devices without complex port forwarding, and it's very convenient.
Step-by-Step: Securely Connecting Your IoT Device
Let's walk through the general steps to get your remote IoT device securely connected. This isn't super complicated, but it does involve a few key actions to make sure everything is safe and sound, so pay attention to these parts.
Preparing Your Device
Before you do anything else, make sure your IoT device's software is completely up to date. This means running any system updates and making sure all its programs are current. Remember, outdated software is a big security risk, so this is a really important first step.
Also, change any default usernames and passwords immediately. Many IoT devices come with common, easy-to-guess credentials, and leaving them as is makes your device an easy target. Pick something strong and unique, and that's a basic but vital security measure.
Make sure your device has a stable internet connection. A shaky connection will make remote access frustrating, so that's something to check before you start trying to connect.
Generating SSH Keys for Stronger Security
While you can use passwords with SSH, a much more secure method is using SSH keys. This involves creating a pair of digital keys: a public key that you put on your IoT device, and a private key that stays secret on your computer. It's a bit like having a very special, uncopyable lock and key, which is very secure.
On your computer, you can generate these keys using the `ssh-keygen` command in your terminal or PowerShell. It will create two files, typically `id_rsa` (your private key) and `id_rsa.pub` (your public key). Keep your private key very safe, as anyone with it can access your devices, so that's a critical piece of information.
You then copy the public key (`id_rsa.pub`) to your IoT device's `~/.ssh/authorized_keys` file. This tells your IoT device to trust connections from your computer when it presents the matching private key, and that's how the secure handshake happens.
Configuring P2P-like Access
If you're using a service like ZeroTier or Tailscale for P2P-like connectivity, the next step is to install their client software on both your control computer and your IoT device. Follow their instructions to join both devices to the same virtual network. This usually involves copying a network ID or token, so it's fairly straightforward.
Once both devices are connected to the virtual network, they will each get a virtual IP address. This IP address is what you'll use to connect to your IoT device, no matter where it is in the world. It's a truly powerful way to bypass tricky network setups, and it makes things much simpler.
This method truly simplifies remote access, especially for devices behind firewalls or complex network setups. It creates a secure, direct path for your SSH traffic, which is exactly what we want for securely connecting remote IoT devices.
Connecting Remotely and Safely
With your IoT device ready and your P2P-like network established, you can now connect using your SSH client. Open your terminal or PuTTY, and use the virtual IP address of your IoT device. The command might look something like `ssh username@virtual_ip_address`, and that's how you initiate the connection.
If you set up SSH keys correctly, you won't even need to type a password. Your computer will automatically present your private key, and if it matches the public key on the IoT device, you'll be logged in securely. This is not only more secure but also much faster than typing passwords, so it's a win-win.
Once connected, you have full command-line access to your IoT device. You can update software, check sensor readings, run scripts, or troubleshoot issues. You're securely connected, and you're in control, which is the whole point of this exercise.
Keeping Your IoT Connections Safe and Sound
Getting that initial secure connection is a big step, but keeping it safe over time requires ongoing attention. It's not a "set it and forget it" kind of deal; you need to be a bit proactive, so that's important to remember.
Regular Updates are Key
We talked about it before, and it's worth repeating: always keep your IoT device's software up to date. This includes the operating system, any installed applications, and even the firmware. Updates often contain fixes for security flaws that bad actors might try to exploit, so they're truly vital.
Set up a routine to check for updates, maybe once a month or whenever you hear about new versions. It's a simple habit that can prevent many headaches down the line, and it's a very good practice.
Remember how "My text" mentioned devices being at risk because they're out of date? This is exactly why regular updates are so important for your remote IoT gadgets. It's about staying ahead of potential problems, and that's a smart move.
Strong Passwords and Keys
If you do use passwords for SSH, make them long, complex, and unique. Never reuse passwords from other accounts. Better yet, stick with SSH keys, as they are significantly more secure and less prone to brute-force attacks, so that's a much better option.
Protect your private SSH keys on your computer. Don't share them, and if your computer is stolen or compromised, revoke those keys on your IoT devices immediately. Think of them as the master keys to your remote kingdom, and you want to guard them very carefully.
This simple step can truly make a huge difference in preventing unauthorized access. It's a fundamental part of keeping your remote IoT connections secure, and it's something you should always do.
Smart Firewall Rules
On your IoT device,
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide