Securely Connect Remote IoT P2P Raspberry Pi Free: Your Guide To Safe Home Automation
It's almost like magic, isn't it? The idea of controlling devices from anywhere, seeing what your home's little sensors are picking up, or maybe even getting a quick look at your pet from across town, all powered by a tiny Raspberry Pi. That dream of smart living is very real for many, yet it often comes with a bit of a nagging worry: is it safe? You see, connecting your gadgets to the outside world, especially if your current setup feels a little out of date or those connections just seem untrusted, can leave you feeling a little exposed.
A lot of people, quite honestly, have run into frustrating messages like "This connection is untrusted" or worries about devices missing important security updates. It's a common story, whether you're using a web browser or trying to get your home automation gear talking. The good news is that getting your Raspberry Pi to talk to you, securely and without a big price tag, is totally doable. You don't have to put your personal space at risk just to enjoy the convenience of a smart home or a remote project.
This guide will walk you through practical ways to keep your Raspberry Pi IoT projects safe, even when you're connecting to them from far away. We'll look at how to make those connections trusted, how to handle things like login problems, and how to keep your little computer running smoothly and securely, all without spending a dime. So, if you're ready to take charge of your IoT security, let's get going.
- Sophie Rain Spiderman Video
- What Does Ig Mean
- Julesari Leaks
- Two Person Yoga Poses
- Drew Pritchard Divorce
Table of Contents
- Why Secure Remote Access Matters for Your Raspberry Pi IoT Projects
- Understanding Peer-to-Peer (P2P) for IoT
- Practical Ways to Securely Connect Your Remote IoT Raspberry Pi for Free
- Essential Security Practices for Your Raspberry Pi
- Troubleshooting Common Connection Issues
- Frequently Asked Questions (FAQ)
Why Secure Remote Access Matters for Your Raspberry Pi IoT Projects
When you set up a Raspberry Pi for an IoT task, like maybe monitoring your garden or controlling your lights, you probably want to check in on it from anywhere. That's the whole point, right? But here's the thing: every time you open a door to your Pi from the internet, you're also opening it to everyone else, and that includes folks with less-than-good intentions. It's sort of like leaving your front door unlocked when you go out; you just wouldn't do it, would you?
The challenge, it seems, is making sure that only *you* get to walk through that digital door. A lot of people, myself included, have found that their devices can be at risk because they're a little out of date, missing important security bits. This can lead to those really annoying "connection is untrusted" messages you sometimes see, which are basically your computer trying to tell you that something isn't quite right with the way it's trying to talk to another system. It's a clear sign that security needs a closer look, and arguably, that's where we need to start.
The Risks of Unsecured Connections
Think about what could happen if your Raspberry Pi, sitting there happily automating your life, isn't properly protected. For one, someone could gain unauthorized access to your Pi itself. This means they could mess with your code, steal data, or even use your Pi as a stepping stone to get into other devices on your home network. That's a pretty scary thought, isn't it?
- Abbey Love On The Spectrum
- Morty And Rick Cast
- What Is A Femboy
- Timothee Chalamet Net Worth
- What Does Nvm Mean
Another problem is that an unsecured connection could allow someone to snoop on the information your Pi is sending or receiving. If your IoT project is collecting sensitive data, like maybe temperature readings from inside your home or even video feeds, that information could fall into the wrong hands. It's a bit like having someone listen in on your private phone calls, which is definitely not something anyone wants. Very often, these kinds of issues stem from outdated software or simple oversight.
Also, an exposed Pi could be used for malicious activities, like launching attacks on other websites or sending out spam. You might not even know it's happening, but your internet service provider could flag your connection, or worse, your Pi could become part of a larger botnet. This connection is untrusted, after all, and that's a big red flag. So, protecting your Pi isn't just about your data; it's about being a good internet citizen, too.
The "Free" Advantage: Why DIY Security is Appealing
Now, you might be thinking, "This all sounds expensive. Do I need to buy fancy security software?" The great news is, no, not necessarily! Many powerful and effective security tools are completely free and open-source. This means you can secure your Raspberry Pi without adding to your project budget, which is a big plus for hobbyists and makers.
The appeal of "free" isn't just about saving money; it's also about control. When you use open-source solutions, you have a better idea of how they work, and you can tailor them to your specific needs. It gives you a lot more power over your own security setup, rather than relying on a black-box commercial product. This approach also helps you understand the underlying principles of secure connections, which is pretty valuable knowledge, honestly.
Plus, the community around Raspberry Pi and open-source software is huge and very supportive. If you run into a problem, chances are someone else has already solved it and shared the solution online. This collaborative spirit makes DIY security not just possible, but actually quite approachable for many. So, while you might find some challenges, there's always help available, which is a comforting thought.
Understanding Peer-to-Peer (P2P) for IoT
When we talk about connecting your remote IoT Raspberry Pi, one common way is through something called Peer-to-Peer, or P2P. Instead of your Pi always talking to a central server somewhere, which then talks to your phone or laptop, P2P lets your devices talk directly to each other. It's like having a direct phone line between your Pi and your control device, rather than going through a big switchboard.
This can be really efficient, especially for IoT, because it can reduce delays and sometimes even save on bandwidth. Imagine your Pi needs to send a quick update to your phone; with P2P, it just sends it straight over. There's no middleman to slow things down, which is pretty neat. However, this direct connection also means you need to be extra careful about who is actually on the other end of that line, because you're bypassing some of the usual network protections.
How P2P Works for Your Devices
In a typical P2P setup for IoT, your Raspberry Pi and your remote device (like your smartphone or laptop) both try to find each other on the internet. This usually involves a small "introducer" service, which isn't a central server that relays all your data, but rather one that helps your devices discover each other's internet addresses. Once they know where each other are, they try to establish a direct link.
This direct link is often established using techniques like "NAT traversal," which helps devices behind home routers (which usually block incoming connections) find a way to communicate. Once that direct connection is made, all the data flows between your Pi and your remote device. It's a very clever way to get around the limitations of typical home networks, and it's why P2P is so popular for things like video calls and file sharing, too.
For IoT, this means your Pi can send sensor data directly to your phone, or your phone can send commands directly to your Pi, without needing a third-party cloud service to relay everything. This can give you more privacy and control, since your data isn't sitting on someone else's server. It's a very appealing model for those who like to keep things local and private, in a way.
P2P Security Challenges and Solutions
While P2P offers great benefits, it also brings its own set of security challenges. Because connections are direct, it's really important to make sure that only authorized devices can connect. Without proper security, anyone who figures out your Pi's address could potentially try to connect to it, just like someone trying to connect to an untrusted website. This is where the "securely" part of "securely connect remoteiot p2p raspberry pi free" becomes absolutely vital.
One big challenge is authentication: how do you confirm that the device trying to connect is actually *your* device, and not some stranger? Another is encryption: how do you make sure that the data flowing between your Pi and your remote device can't be read by anyone else if they manage to intercept it? These are the core questions we need to answer to make P2P safe for your IoT projects. It's not enough to just connect; you have to connect safely.
The solutions typically involve strong encryption, like TLS/SSL, which scrambles your data so only the intended recipient can read it. They also involve robust authentication methods, such as digital certificates or strong cryptographic keys, rather than just simple passwords. This ensures that even if someone knows your Pi's address, they can't just connect without the right "secret handshake." We'll look at specific free tools that implement these solutions in the next section, which is very helpful.
Practical Ways to Securely Connect Your Remote IoT Raspberry Pi for Free
Now for the good stuff: how do you actually make these secure, free connections happen? There are several proven methods you can use, each with its own advantages. We'll explore some of the most popular and effective ones, giving you options to fit your comfort level and specific project needs. Remember, the goal is to make your connection trusted, unlike those annoying messages about untrusted websites.
Option 1: SSH Tunneling with Key-Based Authentication
SSH (Secure Shell) is probably the most fundamental tool for remote access to your Raspberry Pi. It's built into virtually every Linux system, including Raspberry Pi OS. While you can use SSH with a password, the truly secure way to do it is with key-based authentication. This means you generate a pair of cryptographic keys: a public key that goes on your Raspberry Pi, and a private key that stays on your remote computer or phone. You keep that private key very, very safe.
When you try to connect, your remote device uses its private key to prove its identity to the Pi. If the keys match, you're in, without needing to type a password. This is much more secure than passwords, which can be guessed or brute-forced. It also helps avoid those "untrusted connection" warnings because the cryptographic handshake is very strong. You can even set up SSH to create a "tunnel," which encrypts other types of traffic (like web interfaces) through the secure SSH connection.
To set this up, you'll typically:
- Enable SSH on your Raspberry Pi (using `sudo raspi-config`).
- Generate an SSH key pair on your remote machine (e.g., `ssh-keygen` on Linux/macOS, or PuTTYgen on Windows).
- Copy the public key to your Raspberry Pi's `~/.ssh/authorized_keys` file.
- Disable password authentication for SSH on your Pi for maximum security.
- Configure your home router to forward a specific port to your Pi's SSH port (usually 22). This step requires care to ensure only SSH traffic is allowed in.
Option 2: VPNs (Virtual Private Networks) – Free Tiers and Self-Hosting
A Virtual Private Network (VPN) creates a secure, encrypted "tunnel" over the internet between your remote device and your home network. Once connected to your home VPN, your remote device acts as if it's physically connected to your home network. This means you can access your Raspberry Pi and any other devices on your local network just as if you were sitting right there, all while your connection is very much secure.
For a free solution, you have two main choices:
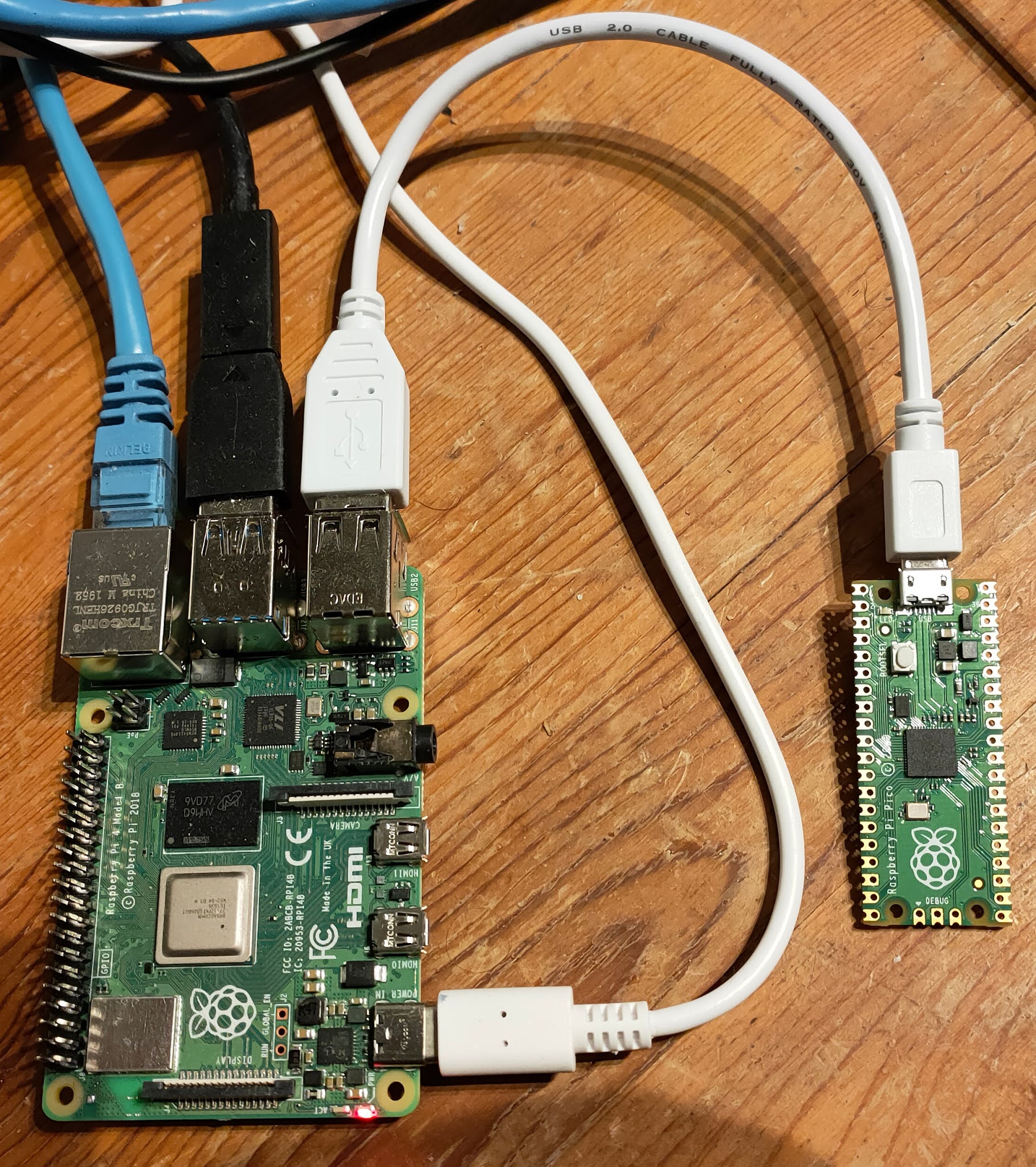
- Self-hosting a VPN server on your Raspberry Pi: You can install open-source VPN software like OpenVPN or WireGuard directly on one of your Raspberry Pis. This Pi then acts as your personal VPN server. When you're away, you connect your phone or laptop to this VPN server, and suddenly, you're "inside" your home network. This gives you complete control and is absolutely free after the initial Pi purchase. It's a bit more involved to set up, but there are tons of guides online. WireGuard, in particular, is known for being fast and relatively easy to configure.
- Using a VPN service with a free tier: Some commercial VPN providers offer a limited free tier, but these usually come with data caps or speed limits. While they can secure your connection *to the internet*, they don't necessarily give you direct access to your home network in the same way a self-hosted VPN does. For connecting *to your Pi*, self-hosting is usually the better and truly free option for full control. Still, it's worth knowing about these services for general browsing security.
Option 3: ZeroTier or Tailscale (Free Tiers for Personal Use)
ZeroTier and Tailscale are fantastic tools that create a "virtual local area network" (LAN) over the internet. Imagine connecting all your devices – your remote laptop, your phone, and your Raspberry Pi – as if they were all plugged into the same network switch, no matter where they are in the world. They do this by setting up secure, encrypted P2P connections between your devices. The beauty is, they handle the complex networking stuff like NAT traversal for you.
Both ZeroTier and Tailscale offer generous free tiers that are perfect for personal IoT projects. You simply install their client software on your Raspberry Pi and on your remote devices. Then, you join them all to the same virtual network through their web console. Once joined, each device gets a private IP address within that virtual network, and they can communicate directly and securely with each other.
The advantages here are significant:
- Ease of Use: Much simpler to set up than a self-hosted VPN, especially for handling router configurations.
- Automatic P2P: They automatically establish direct P2P connections whenever possible, making communication efficient.
- Built-in Security: All traffic within the virtual network is encrypted end-to-end, and devices are authenticated using cryptographic identities. This means your connections are inherently trusted.
Option 4: MQTT with TLS/SSL and Authentication
MQTT (Message Queuing Telemetry Transport) is a lightweight messaging protocol that's incredibly popular for IoT devices because it's designed for low-bandwidth, unreliable networks. Your Raspberry Pi can publish data to an MQTT "broker" (a central server), and your remote device can subscribe to that data. It's a bit like a post office for your IoT messages.
To make MQTT secure, you absolutely need to use TLS/SSL encryption. This is the same technology that secures websites (that little padlock icon in your browser). When you use TLS/SSL with MQTT, all messages exchanged between your Pi, the broker, and your remote device are encrypted. This prevents anyone from snooping on your data. You also need strong authentication, meaning only authorized devices can connect to the broker.
For a free setup:
- Self-host an MQTT broker with TLS: You can run an open-source MQTT broker like Mosquitto on your Raspberry Pi or another home server. Then, configure it to use TLS/SSL certificates and require username/password authentication. This keeps your data within your control and secure. You'll need to generate certificates and configure Mosquitto carefully, but there are many online guides to help. This also helps ensure that your connection is trusted, rather than getting those warnings.
- Use a free public MQTT broker (with caution): Some public MQTT brokers offer free access, but using them for sensitive data without proper encryption and authentication is a big risk. If you do use a public broker, ensure your Pi is sending data encrypted with TLS/SSL and using strong credentials. However, for true security and control, self-hosting is always the better free option for your Raspberry Pi IoT projects.
Essential Security Practices for Your Raspberry Pi
Beyond the connection methods, there are some fundamental security habits that every Raspberry Pi owner should adopt. These practices are crucial for maintaining the overall health and security of your device, preventing issues like those "your device is at risk" warnings, and ensuring your system runs more securely. They are pretty much the basics, but they are incredibly important.
Keeping Your Pi Updated
This is probably the single most important thing you can do. Software updates often include security patches that fix vulnerabilities. If your device is out of date and missing important security and quality updates, it's like leaving a known weakness in your system for attackers to exploit. It's one of the main reasons devices become vulnerable.
Make it a habit to regularly update your Raspberry Pi's software. You can do this with two simple commands in the terminal:
- `sudo apt update`
- `sudo apt full-upgrade`
Strong Passwords and User Management
Never, ever use the default password for your Raspberry Pi (which is `raspberry` for the `pi` user). Change it immediately after setting up your Pi. Use a strong, unique password that's long and includes a mix of uppercase and lowercase letters, numbers, and symbols. A password manager can help you create and store these securely.
Also, consider creating a new user account for yourself and disabling the default `pi` user if you don't need it. This adds an extra layer of security. If you're using key-based SSH authentication, you can even disable password logins entirely, which is the most secure approach. This makes it much harder for someone to guess their way into your system, which is a common attack method.
For any services running on your Pi that require authentication (like an MQTT broker or a web server), make sure they also use strong, unique passwords. Avoid reusing passwords across different services. This helps prevent a single compromised password from leading to a cascade of security breaches, which is a rather significant risk.
Firewall Rules and Network Segmentation
A firewall acts as a gatekeeper for your network, controlling what traffic can come in and go out. On your Raspberry Pi, you can use `ufw` (Uncomplicated Firewall) to easily set up rules. For example, you should only allow incoming connections on the ports you absolutely need (like SSH on port 22, or your VPN port). Block everything else.
If you're running multiple IoT devices, consider segmenting your network. This means putting your IoT devices on a separate part of your network (a separate VLAN, if your router supports it) from your main computers and sensitive data. If one IoT device gets compromised, it can't easily jump to your other devices. This is a bit more advanced, but it offers a much higher level of security, and it's something to consider as your IoT setup grows.
Even simple firewall rules can make a huge difference in protecting your Pi from unwanted attention. It's like putting up a fence around your property; it doesn't stop everyone, but it certainly deters a lot of casual intruders. It's a fundamental security measure, and it's pretty easy to implement, too.
Physical Security
Don't forget about the physical security of your Raspberry Pi. If someone can physically access your Pi, they can bypass many of your digital security measures. Keep your Pi in a secure location where unauthorized individuals can't easily get to it. This might seem obvious, but it's often overlooked.
For instance, if your Pi is running a security camera, make sure the Pi itself isn't easily stolen or tampered with. A secure enclosure or a locked cabinet can go a long way. It's a simple step, but a very effective one. You know, it's just like locking your doors; it's a basic but essential part of keeping things safe, in a way.
Troubleshooting Common Connection Issues
Even with the best intentions, you might run into problems connecting to your Raspberry Pi. Sometimes, you'll see messages like "There is a problem connecting securely to this website" or similar warnings when trying to reach a web interface on your Pi. These usually point to issues with encryption, certificates, or the way
- How To Erase Gel Nail Polish
- More Than A Married Couple
- Yes Yes Yes Meme
- Punta Cana Missing Girl
- Whats Jon Gruden Doing Now
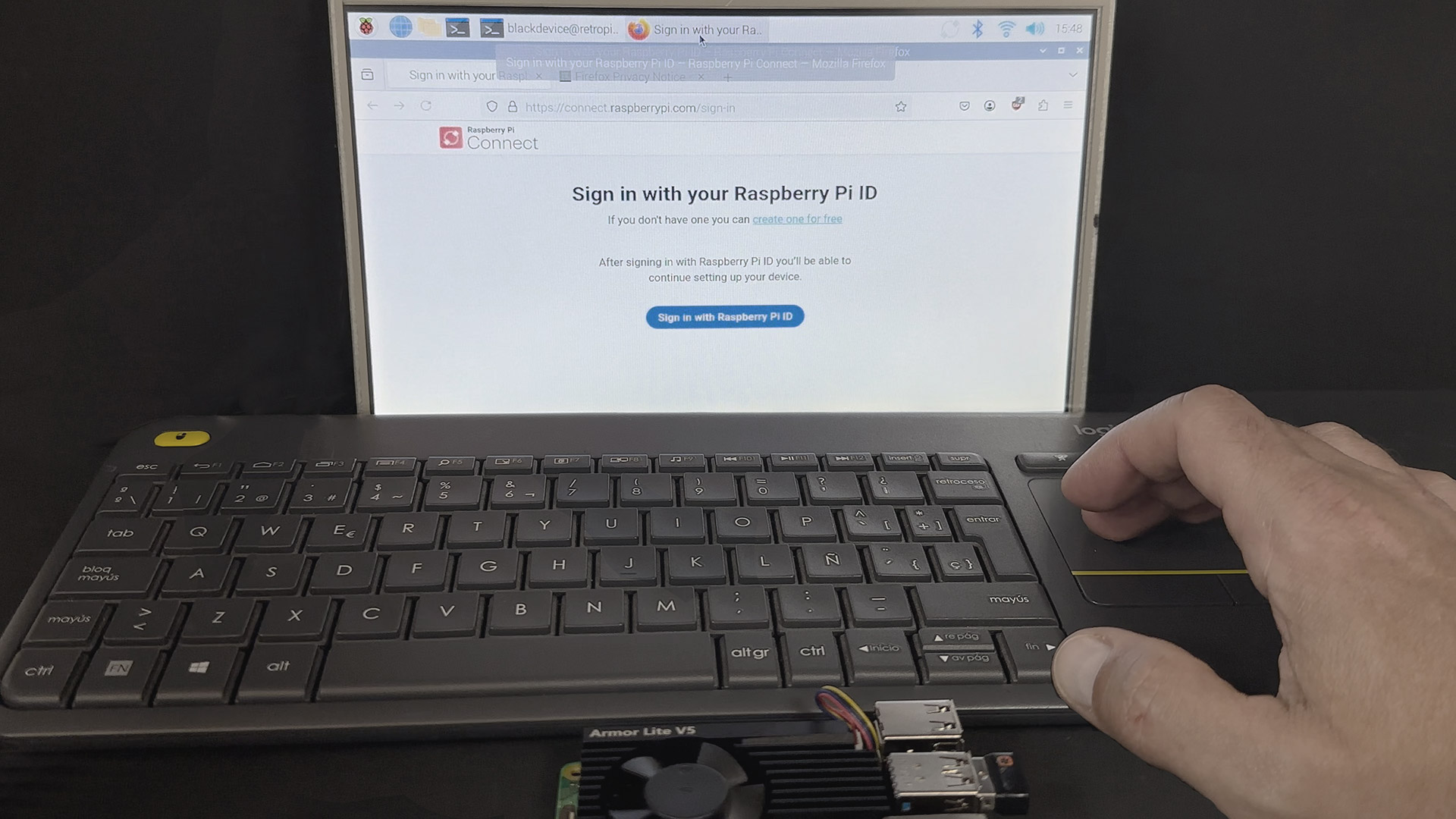
Connect to your Raspberry Pi remotely with Raspberry Pi Connect
Securely Connect RemoteIoT VPC Raspberry Pi: Free Download For Windows

Securely Connect Remote IoT VPC Raspberry Pi: Free Download For Windows