Securely Connect Remote IoT P2P SSH Ubuntu Server: Keeping Your Devices Safe
It can feel really frustrating when your important devices, like those little IoT gadgets or even a home server, tell you they are at risk. Maybe you have seen messages saying your device is out of date, perhaps missing important security and quality updates. It's a bit like getting a warning that a connection is untrusted, or that you have asked your browser to connect securely to a website, but it just cannot confirm that your connection is truly safe. This kind of problem connecting securely to a website can make anyone feel a bit stuck, you know?
Many folks, just like you, might be trying different programs and still finding no solution. You might feel like there is no other option when these kinds of messages pop up. The good news is that for your remote IoT devices or Ubuntu servers, there are ways to set up a direct, secure path, so you can stop worrying about those untrusted warnings. This approach helps you get back on track, making your connections run much more securely, and that is a pretty good feeling, honestly.
This article is here to walk you through how to securely connect remote IoT devices to an Ubuntu server using P2P SSH. We will cover why this method is so helpful, what you will need to get started, and step-by-step instructions to set it all up. We will also talk about keeping everything safe with good practices, so your connections stay trusted and your systems stay updated, which is very important.
- Brandi Passante Pics
- Kendrick Lamar Mustard Song
- Bianca Censori Before Kanye
- What Does Ig Mean
- How Many Legs Does A Spider Have
Table of Contents
- Why P2P SSH for IoT?
- Getting Ready: What You'll Need
- Setting Up Your P2P SSH Connection
- Step 1: Update Your Ubuntu Server
- Step 2: Install OpenSSH Server
- Step 3: Generate SSH Keys
- Step 4: Copy Public Key to IoT Device
- Step 5: Configure SSH Daemon
- Step 6: Enabling P2P Discovery (Optional but helpful)
- Step 7: Testing Your Connection
- Keeping Things Safe: Best Practices
- Regular Updates are a Must
- Strong Passphrases for Keys
- Disable Password Login
- Limit User Access
- Firewall Rules
- Monitoring Activity
- Common Issues and Quick Fixes
- Frequently Asked Questions
Why P2P SSH for IoT?
When you have a small device, like something in the Internet of Things, sitting out there, you often need to reach it. Maybe you want to check its status, send new instructions, or get some data from it. Traditionally, this might involve setting up complicated network rules or using a central server that all your devices connect to. But what if you just want a direct, private line between your main computer and that one IoT gadget? That is where P2P SSH comes in, and it is pretty useful, you know.
Think about those times you have seen a message like, "This connection is untrusted you have asked firefox to connect securely to www.xxxxxxxxxxxx.com, but we can't confirm that your connection is secure." That sort of thing really highlights the need for trusted connections. P2P SSH helps make sure your connection is private and secure from one point directly to another. It does not rely on a middleman, which can reduce risks. It is a bit like having a secret handshake between your devices, so only they can talk directly, which is quite clever.
This method is especially good for devices that might be behind tricky home network setups, like those without a public IP address. It offers a way to get around those network barriers, letting your Ubuntu server talk directly to your remote IoT gadget. It helps keep your information private and makes sure that only authorized people can access your devices, which is a big deal for security, apparently. It means your data stays safe, and your device is less likely to be messed with by someone who should not be there.
- Taper Fade Black Men
- Somber Smithing Stone 6
- King Edward Love Chair
- Eminence In Shadow Season 3
- Securely Connect Remote Iot Vpc Raspberry Pi Download Windows Free
Getting Ready: What You'll Need
Before we start connecting things, it is a good idea to gather your tools. You will need a couple of things to make this work smoothly. First, you will want an Ubuntu server, maybe a desktop or a virtual machine, that you can access easily. This will be your main control point, more or less. You will also need your IoT device, the one you want to connect to, and it should be running some form of Linux, like a tiny Ubuntu or Raspberry Pi OS, which is pretty common for these sorts of gadgets.
You will also need a stable internet connection for both your Ubuntu server and your IoT device. This seems obvious, but a shaky connection can really mess things up during setup. It is also good to have basic knowledge of how to use the command line, just a little bit. We will be typing some commands, so being comfortable with that will help a lot. Lastly, you will want to make sure both your server and your IoT device are physically turned on and ready to go, which is a simple step, but sometimes overlooked, actually.
Setting Up Your P2P SSH Connection
Setting up a direct SSH connection between your Ubuntu server and your IoT device takes a few steps. We will go through each one carefully. This process is all about making sure that when you try to connect, your system does not give you warnings about untrusted connections. It is about creating a secure path, so your data flows safely, which is definitely what we want.
Step 1: Update Your Ubuntu Server
It is really important to start with a fresh, updated system. You know how sometimes you get a message saying, "Your device is at risk because it's out of date and missing important security and quality updates"? We want to avoid that. So, open up a terminal on your Ubuntu server. Type these commands to get all the latest updates and security fixes. This helps your system run more securely right from the start, and it is a good habit to get into, basically.
sudo apt update sudo apt upgrade -y This makes sure your server has all the newest bits, which can prevent a lot of headaches later on. It is a foundational step, honestly, for any secure setup.
Step 2: Install OpenSSH Server
Next, we need to make sure your Ubuntu server can accept SSH connections. OpenSSH is the tool for this, and it is very reliable. If you do not have it installed already, you can add it with a simple command. This prepares your server to listen for incoming secure connections from your IoT device. It is a pretty quick step, generally.
sudo apt install openssh-server -y After it is installed, the SSH service usually starts on its own. You can check its status to be sure it is running. This just confirms that the door is open for secure connections, in a way.
sudo systemctl status ssh Step 3: Generate SSH Keys
Instead of passwords, which can be guessed, we will use SSH keys. These are like super-secure digital fingerprints. You will generate a pair of keys on your Ubuntu server: one public and one private. The private key stays secret on your server, and the public key goes to your IoT device. This is how they recognize each other securely, which is rather clever. When you run the command, just press Enter for the default location and no passphrase for now, though we will talk about passphrases later.
ssh-keygen -t rsa -b 4096 This command creates a strong, 4096-bit RSA key pair. It will typically save them in a hidden folder called `.ssh` in your home directory. The private key is `id_rsa`, and the public key is `id_rsa.pub`. Keep that private key very safe, you know.
Step 4: Copy Public Key to IoT Device
Now, we need to get that public key onto your IoT device. This is the part where your IoT device learns to trust your Ubuntu server. You will use a command called `ssh-copy-id`. You will need to know the username and IP address of your IoT device for this. This command is pretty handy because it puts the public key in the right place on the IoT device, so it is ready to go, more or less.
ssh-copy-id user@your_iot_device_ip Replace `user` with the actual username on your IoT device and `your_iot_device_ip` with its IP address. You might need to type the IoT device's password one last time during this step. After this, your IoT device will know your server's public key, allowing for password-less, secure access, which is pretty convenient, actually.
Step 5: Configure SSH Daemon
To make sure your SSH setup is as secure as possible, we should adjust a few settings on your Ubuntu server. We will edit the SSH daemon configuration file. This file tells the SSH service how to behave. One very important change is to disable password-based logins, forcing everyone to use those secure SSH keys instead. This really cuts down on potential risks, you know.
sudo nano /etc/ssh/sshd_config Inside this file, find the line that says `PasswordAuthentication yes` and change it to `PasswordAuthentication no`. Also, make sure `PubkeyAuthentication yes` is uncommented and set to `yes`. This makes your server only accept connections using SSH keys. After making these changes, save the file and restart the SSH service so the new settings take effect. This is a crucial step for security, honestly.
sudo systemctl restart ssh Step 6: Enabling P2P Discovery (Optional but helpful)
For true P2P connections, especially if your IoT device is behind a tricky network, you might need a way for them to find each other without a public IP. Tools like ZeroTier or ngrok can create a virtual network, allowing devices to talk directly as if they were on the same local network, even if they are miles apart. This is not strictly SSH itself, but it creates the network path SSH needs. You would install a client on both your Ubuntu server and your IoT device, then join them to the same virtual network. This makes direct communication much simpler, in a way, especially for remote IoT setups.
For example, with ZeroTier, you would sign up for an account, create a network ID, and then install the ZeroTier client on both devices. You then join them to your network ID. This gives them a virtual IP address that they can use to connect directly via SSH. It is a very effective way to bypass network hurdles, you know, making that direct P2P connection possible even without public IPs. Learn more about secure network setups on our site.
Step 7: Testing Your Connection
After all that setup, it is time to see if it works! From your Ubuntu server, try to connect to your IoT device using SSH. You should not be asked for a password. If everything went well, you will be logged into your IoT device's command line directly. This is a pretty satisfying moment, honestly, because it means your secure P2P SSH connection is working.
ssh user@your_iot_device_ip If you get in, great! If not, double-check the previous steps, especially the key copying and SSH daemon configuration. Sometimes, a tiny typo can cause problems. But once it works, you have a secure, direct link to your remote IoT gadget, which is rather nice. This direct access helps prevent those "problem connecting securely to this website" messages, as your connection is now explicitly trusted by both ends.
Keeping Things Safe: Best Practices
Setting up the connection is just the start. Keeping it secure over time is just as important. Just like your main computer might need updates because it is missing important security and quality updates, your IoT devices and server need ongoing care. Here are some simple ways to make sure your secure P2P SSH setup stays that way, you know.
Regular Updates are a Must
Remember that message about your device being at risk because it is out of date? That applies to your IoT devices and Ubuntu server too. Software updates often include important security fixes. Make it a habit to update both your server and your IoT devices regularly. This closes known security holes and keeps your systems protected from new threats. It is a bit like getting a flu shot for your devices, honestly, keeping them healthy.
You can set up automatic updates or just make a note to run `sudo apt update && sudo apt upgrade -y` every week or so. This simple step can prevent a lot of potential security issues down the road, and it is a very good practice, generally speaking.
Strong Passphrases for Keys
When you generated your SSH keys, you might have skipped the passphrase. For higher security, especially for keys on your main Ubuntu server, it is a good idea to add a strong passphrase to your private key. This means even if someone gets hold of your private key, they cannot use it without knowing the passphrase. It adds an extra layer of protection, which is pretty smart, you know.
You can add a passphrase to an existing key using `ssh-keygen -p`. Pick something long and hard to guess, but something you can remember. This makes your secure connection even more robust, which is definitely a plus.
Disable Password Login
We already touched on this, but it is worth repeating: make sure password login is completely turned off for SSH on your Ubuntu server. This forces everyone to use SSH keys, which are much harder to crack than passwords. If you did not do this in Step 5, go back and do it now. It is a critical security measure, honestly, for any server you want to keep safe. This helps prevent those "untrusted connection" warnings by making sure only key-authenticated users can even attempt to connect.
Limit User Access
Do not use the 'root' user for everyday SSH connections. Create a regular user account for yourself and give it just enough permissions to do what you need. If you need to perform administrative tasks, use `sudo` after logging in. This limits the damage if your account somehow gets compromised, which is a pretty good idea, you know. It is about minimizing risk, in a way.
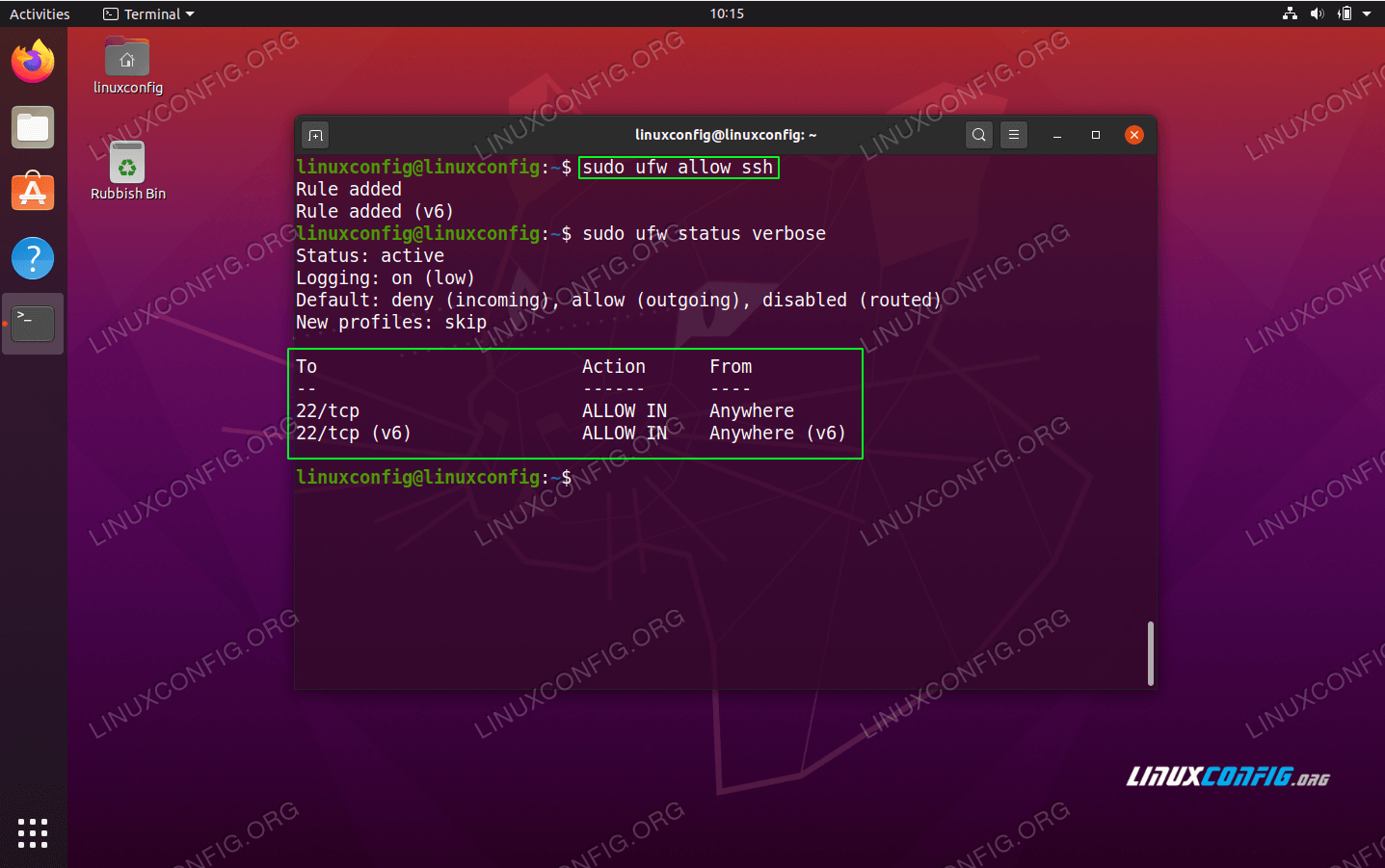
Firewall Rules
A firewall acts like a gatekeeper for your server, blocking unwanted connections. Configure a firewall, like UFW (Uncomplicated Firewall) on Ubuntu, to only allow SSH traffic from trusted sources or specific virtual network interfaces if you are using ZeroTier. This prevents random attempts to connect to your server, making it much harder for bad actors to even try to get in. It is a very effective barrier, generally.
sudo ufw enable sudo ufw allow ssh You might need to allow other ports if your IoT device needs them, but always be specific. This helps keep your server's doors mostly closed, only opening them for what is absolutely necessary, which is a smart security move, honestly.
Monitoring Activity
Keep an eye on who is trying to connect to your server. Tools like `fail2ban` can automatically block IP addresses that try to guess your SSH login too many times. Checking your SSH logs (`/var/log/auth.log`) occasionally can also give you an idea of any unusual activity. Being aware of what is happening on your server helps you react quickly if something seems off, which is a pretty good idea, you know. It is about staying alert, in a way.
Common Issues and Quick Fixes
Even with careful steps, sometimes things do not work exactly as planned. If you are having trouble connecting, do not worry, it is pretty common. One issue could be that your key permissions are wrong. SSH keys need very specific file permissions to work. Your private key on the Ubuntu server should only be readable by you. You can fix this with a simple command, which is a quick check, you know.
chmod 400 ~/.ssh/id_rsa Another problem might be firewall settings. If you set up a firewall, make sure it is allowing SSH traffic on port 22. If it is blocking SSH, you will not be able to connect. Check your firewall rules, and if needed, allow SSH access. Sometimes, the IoT device might not be on the network, or its IP address changed. Always double-check that your IoT device is online and you are using the correct IP address. These little things can often be the cause of connection problems, and they are usually easy to fix, honestly. You can also link to this page for more troubleshooting tips.
Frequently Asked Questions
What does P2P SSH mean for IoT?
P2P SSH for IoT means setting up a direct, secure connection between your main computer (like an Ubuntu server) and an IoT device without needing a central hub or public IP address for the IoT device. It is a bit like creating a private, encrypted tunnel directly between them, which is very handy for remote access, you know.
Why is my device showing "untrusted connection" warnings?
Messages like "This connection is untrusted" often pop up because your system cannot verify the identity of the server you are trying to connect to, or the connection itself is not encrypted. For IoT, this might mean you are trying to access it insecurely, or the device's software is out of date. Using SSH keys and keeping systems updated helps prevent these warnings by creating a trusted, secure path, which is pretty important, honestly.
How do I keep my remote IoT connections secure over time?
Keeping your connections secure means regular maintenance. This includes always applying security updates to both your Ubuntu server and IoT devices, using strong passphrases for your SSH keys, disabling password logins for SSH, setting up a firewall, and regularly checking for any unusual activity. These steps help protect your devices from new threats and keep your connections safe, which is a good habit to maintain, you know.
Date of publication: May 15, 2024, 02:00 PM PDT
- Highest Block Blast Score
- Goob From Meet The Robinsons
- A Court Of Shaded Truths
- How Many Legs Does A Spider Have
- How To Cook Scallops
How To Use Ssh On Ubuntu Server

How To Securely Connect Remote IoT P2P SSH Ubuntu
Firewall Friday: SSH - Securely Connect to Your Remote Server