Securely Connect Remote IoT To AWS VPC: Essential Steps For Safe Operations
Your connected devices are a bit like your home. If the doors are unlocked and windows open, you are inviting trouble. Similarly, when your remote IoT devices connect to your cloud, especially to an AWS Virtual Private Cloud (VPC), security is just so vital. Think about those messages you might have seen, like "Your device is at risk because it's out of date and missing important security and quality updates." Or perhaps, "This connection is untrusted you have asked Firefox to connect securely to bay173.mail.live.com, but we can't confirm that your connection is secure." These warnings are very real for IoT too.
Connecting many remote IoT gadgets to your private cloud space on AWS can seem like a big job. You want all your data to flow smoothly and, well, safely. It's about making sure only the right devices talk to your private network. This helps keep your important information away from curious eyes or bad actors. Sometimes, it's like having trouble connecting securely to a website, as Jerrywoods2 mentioned, where you try different browsers and nothing helps. That kind of frustration is what we want to avoid with your IoT setup.
This guide will walk you through the key ways to make sure your remote IoT devices link up with your AWS VPC in a very secure way. We will look at practical steps and good habits to protect your systems. You will learn how to set up connections that you can trust. This way, your Windows systems, or any operating system, can run more securely, and your data stays protected. It's almost about getting you back on track so everything works as it should, without those nagging security worries.
- What Is A Torta
- Space City Home Network
- How To Ripen Avocados
- Blowout Taper Straight Hair
- How Did Technoblade Die
Table of Contents
- Why Secure Connections Matter for Remote IoT and AWS VPC
- Understanding AWS IoT and VPC for Secure Connectivity
- Key Strategies to Securely Connect Remote IoT to AWS VPC
- Real-World Scenarios and Best Practices
- Frequently Asked Questions (FAQs)
- Conclusion
Why Secure Connections Matter for Remote IoT and AWS VPC
The Dangers of Untrusted Connections
Imagine your remote device sending data without any protection. It's like shouting your secrets in a crowded room. You might see warnings like "This connection is untrusted," or experience problems connecting securely to a website. These issues are not just annoying; they are a sign of real risk. An insecure IoT connection means your data could be spied on, changed, or even deleted by someone bad. This is a very serious concern.
Think about the "out of date" messages for your device, missing important security updates. That's a huge open door. If your IoT devices are not kept current, they become easy targets. Attackers can use these weak spots to get into your private network, perhaps your AWS VPC. This could mess up your operations, steal sensitive information, or even let them control your devices. It's pretty much a recipe for disaster.
Protecting Your Data and Operations
Keeping your IoT connections safe is about more than just avoiding trouble. It is about building trust in your systems. When connections are secure, you can be confident that the data coming from your remote sensors or machines is accurate and hasn't been tampered with. This is really important for making good decisions based on that data. For example, if you're tracking valuable assets, you want to know the location data is correct.
- Niece In Spanish Language
- Korean Language For I Love You
- Help I Accidentally Forgot How Gravity Works
- Whats Jon Gruden Doing Now
- Surrealism Dress To Impress
A secure setup also helps you meet rules and standards. Many industries have strict guidelines about how data should be handled, especially personal or sensitive information. By securing your IoT connections to your AWS VPC, you are showing that you take these responsibilities seriously. It helps prevent legal issues and keeps your business's reputation strong. So, it's not just a technical task, but also a business one.
Understanding AWS IoT and VPC for Secure Connectivity
What is AWS IoT Core?
AWS IoT Core is a cloud service that lets many IoT devices connect easily and safely to the AWS cloud. It acts like a central hub for all your devices. It can handle billions of messages from millions of devices. This service helps devices talk to other AWS services without too much fuss. It's almost like a very efficient post office for your IoT data.
IoT Core also helps with device management. You can keep track of all your connected gadgets. It also provides tools for security, like making sure only trusted devices can connect. This is a really big part of keeping your entire IoT system safe. You can set up rules for how devices send and receive information, which is quite handy.
What is an Amazon VPC?
An Amazon Virtual Private Cloud (VPC) is your own private, isolated network section within the AWS cloud. Think of it as your own private office building inside a very large campus. You get to choose your IP address range, create subnets, and configure network gateways. This gives you full control over your network environment. It's a bit like having your own dedicated space.
Inside your VPC, you can launch AWS resources, such as EC2 instances, databases, and other applications. These resources are protected by your own security settings, like network access control lists (ACLs) and security groups. This isolation is key for keeping your sensitive data and applications safe from the public internet. It's a very good way to keep things separate and secure.
The Bridge: Connecting IoT to Your Private Network
The main challenge is getting your remote IoT devices, which might be out in the world, to talk securely to services running inside your private AWS VPC. Typically, IoT Core handles the device connections, but what if the services processing that data are deep inside your private network? You do not want to expose your private services directly to the internet. This is where the "securely connect remoteiot vpc aws" part becomes really important.
You need a reliable and safe way for data to flow from IoT Core into your VPC. This bridge must ensure that only authorized data gets through and that it stays private. It's about building a trusted path, so your data does not have to go through the open internet to reach your private applications. This is a very crucial step for overall security.
Key Strategies to Securely Connect Remote IoT to AWS VPC
PrivateLink for Direct, Secure Access
AWS PrivateLink is a fantastic way to connect your IoT Core to services within your VPC without using the public internet. It creates a private endpoint within your VPC for AWS services. This means your IoT devices can send data to IoT Core, and then IoT Core can send it directly into your VPC using this private connection. It's almost like having a secret tunnel.
Specifically, you can use a VPC Endpoint for AWS IoT Core. This makes sure that all traffic between your devices (via IoT Core) and your VPC stays on the AWS network. It never touches the public internet. This significantly reduces the risk of data breaches and makes your connection much more secure. It is a really strong option for privacy.
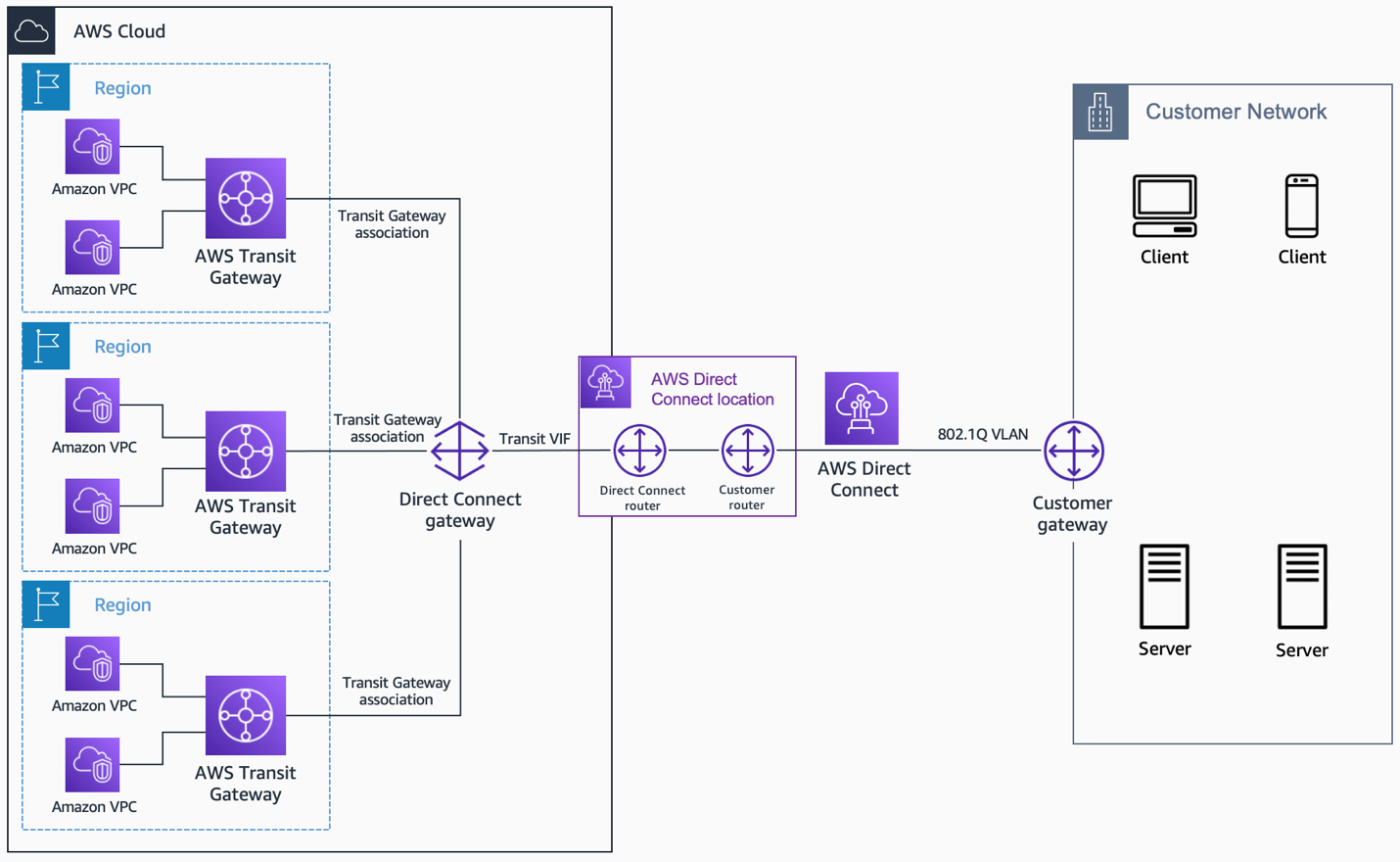
VPN or Direct Connect for Hybrid Setups
For situations where your IoT devices or gateways are on-premises and need to talk to your AWS VPC, a Virtual Private Network (VPN) or AWS Direct Connect can be useful. A VPN creates an encrypted tunnel over the public internet. This makes sure your data is scrambled and safe as it travels. It's a pretty common way to link networks securely.
AWS Direct Connect offers a dedicated, private network connection from your premises directly to AWS. This provides even greater security, reliability, and usually better performance than a VPN. It bypasses the public internet entirely. So, if you have a lot of data or very strict security needs, Direct Connect might be a very good choice. It's like having your own private highway to the cloud.
Device Identity and Authentication
Before any device can send data, you need to know who it is. This is called authentication. For IoT devices, X.509 certificates are a common and very strong method. Each device gets a unique certificate. When a device tries to connect to AWS IoT Core, it presents its certificate. IoT Core then checks if the certificate is valid and issued by a trusted source. This is a bit like showing your ID card at a secure building entrance.
AWS IoT also supports custom authenticators. This means you can use your own systems to verify device identities. This gives you a lot of flexibility if you have specific security needs or existing identity systems. It ensures that only known and approved devices can even begin to communicate with your cloud resources. This is, you know, a fundamental security step.
Authorization with AWS IoT Policies
Once a device is authenticated, you need to decide what it is allowed to do. This is authorization, and AWS IoT Policies handle this. These policies are like rulebooks for your devices. You can specify which topics a device can publish messages to, or subscribe to receive messages from. You can also control which AWS services a device can interact with.
For example, you can say that a temperature sensor can only publish data to the "temperature/readings" topic and nothing else. It cannot, say, try to control a motor. This principle of "least privilege" is very important. It means giving devices only the permissions they absolutely need to do their job. This significantly limits what a compromised device could do. It is, basically, a smart way to limit risk.
Data Encryption In Transit and At Rest
Encryption is about scrambling your data so that only authorized people or systems can read it. When data moves from your IoT device to AWS IoT Core and then into your VPC, it should be encrypted "in transit." This usually happens automatically with secure protocols like TLS (Transport Layer Security). This is the same technology that secures your web browsing. It makes sure that even if someone intercepts your data, they cannot understand it. It's a very good layer of protection.
Data should also be encrypted "at rest," meaning when it's stored in services like Amazon S3 or databases within your VPC. AWS provides various encryption options for data storage. This means if someone somehow gets access to your storage, the data is still unreadable without the correct decryption key. This is, you know, a double layer of security, which is pretty good.
Network Segmentation and Firewall Rules
Within your AWS VPC, you should divide your network into smaller, isolated sections called subnets. This is called network segmentation. For instance, you might have one subnet for your IoT data processing applications and another for your databases. Then, you use firewall rules (like AWS Security Groups and Network ACLs) to control what traffic can flow between these subnets. This is a bit like putting internal walls in your office building.
This approach helps contain potential security breaches. If one part of your network is compromised, the damage is limited to that segment. It prevents an attacker from easily moving to other, more sensitive parts of your VPC. This is a very practical way to limit exposure. It's almost like having separate secure rooms for different tasks.
Regular Updates and Patching
Remember those warnings about "Your device is at risk because it's out of date and missing important security and quality updates"? This applies to IoT devices just as much as your computer. Software on IoT devices, gateways, and even the operating systems on your AWS instances need regular updates. These updates often fix security flaws that attackers could exploit. So, it's very important to keep everything current.
Having a process for applying these updates is essential. This might involve over-the-air (OTA) updates for your remote devices. For your AWS resources, it means regularly patching your operating systems and applications. Neglecting updates is one of the easiest ways to leave your systems vulnerable. It's just a simple, but crucial, step.
Monitoring and Logging for Anomaly Detection
You can't protect what you don't see. Monitoring and logging are your eyes and ears in your IoT and VPC environment. AWS services like CloudWatch and CloudTrail collect logs of activity. CloudWatch can track metrics and set alarms for unusual behavior. CloudTrail records every API call made in your AWS account, showing who did what, when, and where. This is a very powerful tool.
By regularly reviewing these logs and setting up alerts for suspicious activities, you can quickly spot potential security issues. For example, if a device suddenly tries to connect from an unusual location, or attempts to access resources it shouldn't, you can be notified immediately. This allows you to react quickly and stop a problem before it gets too big. It's basically about staying vigilant.
Real-World Scenarios and Best Practices
Think about a smart factory with hundreds of sensors and robots. These devices generate a huge amount of data about production lines, machine health, and inventory. Securely connecting them to an AWS VPC, using PrivateLink for instance, means this sensitive operational data stays private. It helps prevent industrial espionage or disruptions. So, that's a pretty clear benefit.
Another example is remote health monitoring devices. These collect very personal health data. Using strong authentication like X.509 certificates and strict IoT policies ensures that only the patient's authorized device can send data. Encrypting data both in transit and at rest protects patient privacy. This is, you know, absolutely critical for trust and compliance.
For smart city applications, like traffic sensors or environmental monitors, ensuring data integrity is key. You want to be sure the data is accurate and hasn't been tampered with. Regular updates for these devices are also very important, as Marcela_p might agree, to close any security gaps that appear over time. These practices help build a reliable and safe connected environment for everyone.
Frequently Asked Questions (FAQs)
How do I secure my IoT devices in AWS?
Securing your IoT devices in AWS involves several steps. You should use strong authentication methods, like X.509 certificates, to verify device identity. Also, set up strict AWS IoT policies to control what each device can do. Make sure to encrypt data when it moves and when it's stored. Keep your device software and firmware up to date to patch security holes. Monitoring device activity for anything unusual is also very important. These steps help keep your devices safe.
Can IoT devices connect directly to a VPC?
IoT devices usually connect to AWS IoT Core first, which acts as a central hub. From IoT Core, you can then establish a secure, private connection to your VPC using services like AWS PrivateLink. This creates a VPC endpoint for IoT Core, so traffic stays within the AWS network and does not go over the public internet. While not a direct device-to-VPC connection in the traditional sense, it achieves the goal of private communication. It's almost like a secure relay.
What is AWS IoT Core's role in secure connections?
AWS IoT Core plays a really big part in secure connections. It handles the initial secure connection from your devices, supporting various authentication methods. It enforces the rules you set with AWS IoT Policies, deciding what each device is allowed to do. IoT Core also manages device certificates and can integrate with other AWS security services. It basically acts as the secure front door for all your IoT devices entering the AWS cloud. It's pretty much essential for secure setups.
Conclusion
Connecting your remote IoT devices to an AWS VPC securely is a big deal for protecting your data and keeping your operations running smoothly. It is about building trust in your system. By using tools like PrivateLink, strong authentication, and smart policies, you can create a really safe environment. Keep your systems updated and monitor everything closely. This helps avoid those frustrating "untrusted connection" problems. Start making your IoT connections safe today. Learn more about IoT security best practices on our site, and link to this page AWS IoT Core features for more details.
- More Than A Married Couple
- Just Give Me My Money
- Lagu Waiting For You
- Emily Compagno Husband
- What Does Nvm Mean

AWS VPC Tutorial - Part I Introduction - StudyTrails

Securely Connect Remote IoT VPC Raspberry Pi AWS: A Comprehensive Guide
Securely Connect Remote IoT VPC AWS Not Working Windows: Comprehensive