Your Guide To SSH Access For IoT: A Real-World Example
Getting your smart devices, those little internet-connected gadgets, to listen to your commands from afar can feel a bit like magic, can't it? It’s a truly useful skill, especially when you need to fix something or check on a tiny computer far away without actually being there. This idea of reaching out and managing things remotely, using something called SSH, is a pretty big deal for anyone working with IoT, or the Internet of Things. It helps you keep an eye on your devices, maybe even update them, all from the comfort of your desk. So, knowing how to set this up properly, and what to watch out for, is very important for keeping your smart setups running smoothly.
Think about a small sensor tucked away in a remote spot, perhaps gathering data about the weather or monitoring a machine. What happens if it stops sending information? You can't just drive out there every time something goes wrong, can you? That's where SSH, or Secure Shell, comes into play. It gives you a safe, encrypted way to connect to that device, just as if you were sitting right in front of it, typing commands directly. This method is, you know, a cornerstone of managing these devices when they are spread out.
This article will walk you through a practical look at using SSH for your IoT projects, touching on some common hiccups and how to sort them out. We'll share some real-world experiences, like setting up a specific server and dealing with a few tricky errors that often pop up. Our aim is to give you a clearer picture of how this works, and perhaps help you avoid some of the little frustrations that can come with remote device control. You might find it surprisingly straightforward, actually, once you get the hang of it.
- Blowout Taper Straight Hair
- Steve Horstmeyer Dogs
- How Tall Is The Rock
- Jamaican Restaurants Near Me
- Sophie Rain Spiderman Video
Table of Contents
- Understanding SSH for IoT Devices
- Setting Up Your IoT Server for SSH
- Tackling Common SSH Configuration Mix-Ups
- Troubleshooting SSH Access Issues
- Securing Your IoT SSH Connections
- Frequently Asked Questions About SSH IoT Access
- Final Thoughts on Remote IoT Management
Understanding SSH for IoT Devices
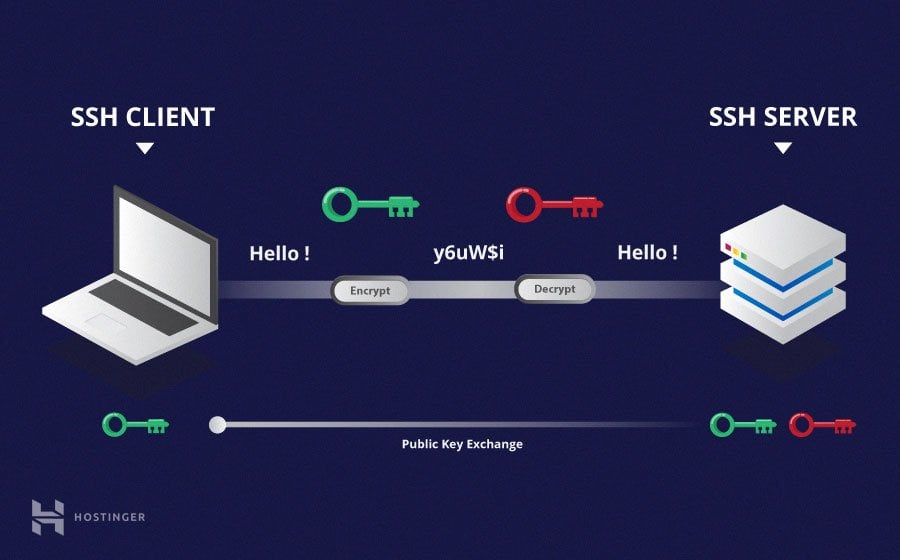
SSH, or Secure Shell, is a network protocol that gives computer users a secure way to access a computer over an unsecured network. It's a bit like having a secret, coded conversation that no one else can listen in on. For IoT devices, which are often out in the open or on public networks, this security is, you know, absolutely vital. Without it, anyone could potentially peek at your data or even take control of your devices, which would be a pretty big problem.
Why SSH Is a Good Fit for IoT
IoT devices are, in many cases, small computers that don't have a screen or a keyboard attached. They might be running a stripped-down version of Linux, which is very common. So, how do you talk to them? SSH provides that text-based interface, allowing you to send commands, transfer files, and even run programs directly on the device. It's a very efficient way to work with these devices, especially when they are physically far away. That's why it's a popular choice, really, among developers and hobbyists.
The security aspect of SSH is another huge plus. Every bit of data sent between your computer and the IoT device is encrypted. This means that even if someone manages to intercept the data, they won't be able to read it. This is, you know, a core reason why people choose SSH over older, less secure methods. It helps keep your information private and safe from prying eyes, which is quite important for any connected device, especially those handling sensitive information.
- Yes Yes Yes Meme
- Ap Classroom Unit 6 Progress Check Mcq Answers Ap Lang
- Can You Eat Crocs
- How To Erase Gel Nail Polish
- How Did Technoblade Die
Common IoT Scenarios for SSH
Think about some everyday uses. You might have a Raspberry Pi acting as a home automation hub, controlling lights and thermostats. If you want to add a new feature or fix a bug, you can SSH into it from your laptop, no need to unplug it or connect a monitor. Or, consider a network of environmental sensors in a greenhouse. If one sensor needs a software update, you can use SSH to push the new code to it, saving you a trip. It's a very flexible tool, that.
Another common use is for data collection. Many IoT devices gather information and store it locally. With SSH, you can securely copy those data files from the device to your main computer for analysis. This is, you know, incredibly helpful for long-term monitoring projects where data is collected over time. It makes managing all that information much simpler, and it's a pretty standard procedure in many setups.
Setting Up Your IoT Server for SSH
Getting your IoT device ready for SSH access usually starts with installing the right software on it. Many small devices, like single-board computers, run a version of Linux. For our example, we'll talk about setting up an Ubuntu server, which is a very popular choice for these kinds of tasks. It’s a pretty straightforward process, generally speaking, but getting the details right can save you a lot of trouble later on.
Ubuntu Server and OpenSSH: A Solid Start
Our team, as a matter of fact, recently got an Ubuntu server 22.04.3 LTS up and running. This particular version of Ubuntu is a long-term support release, meaning it gets updates for a good while, which is great for stability. When we installed it, the OpenSSH server package was already included, which made things a little easier right from the start. This package is the heart of allowing secure remote connections to your device. It’s what makes the whole SSH thing work, you know?
Having OpenSSH pre-installed is a real convenience, as it means one less step to worry about. If it's not there, you can usually add it with a simple command, something like `sudo apt install openssh-server`. This command fetches the necessary files and sets them up for you. It's a pretty common first step for many IoT projects that need remote access, and it just works, typically, without much fuss.
Initial Server Configuration Tips
Once OpenSSH is on your device, there are a few basic things you might want to check or adjust. Making sure the server is listening on the right port, usually port 22, is one. Also, you might want to think about who can log in and how. For security, it's often a good idea to disable direct root login and only allow specific users to connect. These small adjustments can make a big difference in how secure your setup is. It's almost like putting a stronger lock on your front door, really.
Another tip is to make sure your device has a static IP address, or at least a way to find it easily on your network. If its IP address keeps changing, you'll have a hard time connecting to it consistently. You know, you could use a tool like `ifconfig` or `ip a` to check the current address. Getting this right early on can prevent a lot of head-scratching later when you try to connect and can't find your device.
Tackling Common SSH Configuration Mix-Ups
When you're setting up SSH, it's easy to get a little mixed up between the different configuration files. This is a very common point of confusion, even for people who have been doing this for a while. Knowing which file controls what is pretty key to making sure your SSH connections work as they should. It’s a bit like trying to adjust the volume on your TV, but you’re actually holding the remote for the DVD player. You know, it just won't work.
Client vs. Server Settings: Knowing the Difference
One of the biggest sources of confusion comes from two files: `/etc/ssh/ssh_config` and `/etc/ssh/sshd_config`. The first one, `ssh_config`, is for the SSH client. This is the program on *your* computer that you use to connect *out* to other devices. The second one, `sshd_config`, is for the SSH *server*, which runs on the device you want to connect *to*. Our team, for instance, learned this the hard way, as I was saying, when we were trying to sort out some issues.
It's important to remember this distinction. If you want to change how your IoT device accepts incoming SSH connections, you need to edit the server's configuration file. If you want to change how your computer connects to other SSH servers, then you'd edit your client's file. Mixing them up can lead to a lot of frustration and connections that just don't work, which is pretty much what happened to us.
What to Do with /etc/ssh/ssh_config
In our experience, we found that we had some options listed in our `/etc/ssh/ssh_config` file that really didn't belong there. These were settings meant for the server, not for the client. The advice we got, and what worked for us, was to remove all those listed options from the `ssh_config` file. They are, you know, supposed to be part of the `sshd_config` file, which is the server's configuration. It's a simple fix, but it can clear up a lot of odd behavior.
When you're dealing with `ssh_config`, it's generally best to keep it pretty minimal unless you have a specific reason to change client-side behaviors. Things like default usernames for certain hosts, or specific port numbers for your outgoing connections, might go here. But for settings that control how a device *receives* connections, that's definitely the server's job. So, if you see server-like options in your client config, just take them out. It's a good practice, actually.
The Importance of /etc/ssh/sshd_config
The `/etc/ssh/sshd_config` file is where you truly control how your IoT device behaves as an SSH server. This is where you can set things like which port SSH listens on, whether password authentication is allowed, if root can log in directly, and which users are permitted. These are all very important security settings. For instance, you might want to disable password logins and only allow connections using SSH keys, which are much more secure. This file is, in a way, the control panel for your device's remote access.
After you make any changes to `sshd_config`, you must restart the SSH service for those changes to take effect. On Ubuntu, you would typically do this with a command like `sudo systemctl restart ssh`. If you don't restart the service, your changes won't be active, and you might still be scratching your head wondering why things aren't working. It's a pretty easy step to forget, but it's vital for sure.
Troubleshooting SSH Access Issues
Even with everything set up correctly, you might run into problems. SSH connections can be a bit finicky sometimes, and errors can pop up that seem confusing at first. Knowing what these common error messages mean can save you a lot of time and frustration. We've certainly had our share of head-scratching moments, you know, when trying to get things just right.
Error: Invalid Host for SSH Forwarding
One error we encountered was "Error invalid host for ssh forwarding." This message usually means there's a problem with how you're trying to set up what's called "SSH forwarding." SSH forwarding lets you send network traffic through your SSH connection, which can be useful for accessing services on a remote network that aren't directly exposed to the internet. For instance, you might use it to connect to a web server running only on your IoT device's local network.
This error often happens when the hostname or IP address you've specified for the forwarding isn't correct, or the SSH server on the IoT device isn't set up to allow forwarding. You might need to check your SSH command carefully to make sure the host details are spot on. Also, look at the `sshd_config` file on your IoT device to ensure options like `AllowTcpForwarding` are enabled. It’s a specific setting, but it's pretty important for this kind of connection, as a matter of fact.
Could Not Resolve Hostname node01
Another common message is "Could not resolve hostname node01." This one is pretty straightforward, actually. It means your computer doesn't know what "node01" refers to. It's like trying to call a friend by a nickname, but your phone doesn't have their number stored under that name. Your computer needs to translate "node01" into an actual IP address, like 192.168.1.100, to know where to send the connection request. This is, you know, a very typical network issue.
To fix this, you have a few options. You could try using the IoT device's actual IP address instead of its hostname in your SSH command. Or, you could add "node01" and its IP address to your computer's `hosts` file. On Linux or macOS, this file is usually at `/etc/hosts`. For example, you might add a line like `192.168.1.100 node01`. If you're using a DNS server, make sure it's properly configured to know about your IoT device's hostname. It's just about making sure the name matches the address, basically.
General Connection Checks
If you're still having trouble, there are some general things to check. First, make sure your IoT device is actually turned on and connected to the network. Sounds obvious, but sometimes it's the simplest things. Then, check if there's a firewall blocking the connection, either on your computer, on the IoT device, or somewhere in between, like your router. Firewalls are, you know, designed to stop unwanted connections, so they can sometimes stop wanted ones too. You might need to open port 22 on your firewall.
You can also try using the `ping` command from your computer to the IoT device's IP address. If `ping` works, it means there's at least basic network connectivity. If it doesn't, then your problem is probably more about network setup than SSH itself. Also, check the SSH server logs on the IoT device for more detailed error messages. These logs, typically found in `/var/log/auth.log` or `/var/log/syslog` on Ubuntu, can give you clues about why connections are failing. It's a pretty good place to start looking for hints, really.
Securing Your IoT SSH Connections
Once you have SSH access working, the next big step is to make sure it's as secure as possible. IoT devices can be targets for attackers, so taking extra precautions is very wise. There are a few key practices that can significantly improve the safety of your remote connections. It's not just about getting it to work, you know, it's about making sure it stays safe and sound.
Using SSH Keys for Better Security
The most important security measure for SSH is to use SSH keys instead of passwords. SSH keys come in pairs: a private key that stays on your computer and a public key that you put on the IoT device. When you try to connect, the server checks if your private key matches the public key it has. This method is much more secure than passwords because keys are very long and complex, making them nearly impossible to guess. Plus, you don't have to type a password, which is a nice convenience, too.
To set this up, you'd typically generate a key pair on your computer using a tool like `ssh-keygen`. Then, you copy the public key to the `~/.ssh/authorized_keys` file on your IoT device. After that, you can disable password authentication in your `sshd_config` file on the IoT device. This means no one can log in with just a password, forcing them to use a key. It's a very strong security improvement, basically, and widely recommended for all SSH setups.
Firewall Rules: A Necessary Layer
Even with strong SSH keys, a firewall adds another layer of protection. A firewall controls which network traffic is allowed in and out of your IoT device. You can configure it to only allow SSH connections from specific IP addresses, perhaps just your home network's IP, or from a VPN you use. This significantly reduces the attack surface, meaning fewer opportunities for bad actors to try and connect. It's a pretty simple step, but it makes a big difference in keeping things safe, you know.
On Ubuntu, you can use `ufw` (Uncomplicated Firewall) to manage your firewall rules. For example, `sudo ufw allow ssh` would allow SSH connections from anywhere. But for better security, you might use `sudo ufw allow from 192.168.1.0/24 to any port 22` to only allow connections from your local network. Remember to enable the firewall after setting your rules. It's a bit like having a guard at the door, only letting in people you recognize, which is a good thing for security.
Frequently Asked Questions About SSH IoT Access
People often have similar questions when they're getting started with SSH for their IoT devices. Here are a few common ones that come up, you know, quite a lot.
How do I find my IoT device's IP address for SSH?
You can often find your IoT device's IP address by logging into your router's administration page and looking at the list of connected devices. On the device itself, if you have a way to access its command line, you can type `ip a` or `ifconfig` to see its network details. Sometimes, tools like network scanners on your computer can also help discover devices on your local network. It's usually not too hard to find, really.
Is it safe to expose my IoT device's SSH port to the internet?
Directly exposing SSH to the internet without proper security measures is generally not a good idea. If you must, always use SSH keys for authentication, disable password logins, and consider changing the default SSH port (though this is more for obscurity than true security). A better approach is to use a VPN or a service like Tailscale to create a secure tunnel to your device, so it's not directly open to the world. It adds a layer of protection, you know, that is very valuable.
What if I forget my SSH password or lose my SSH key?
If you forget your password and don't have SSH key access, or if you lose your SSH key, you might need to physically access your IoT device. This could involve connecting a monitor and keyboard directly to it, or even reflashing its operating system if you can't log in locally. That's why having a backup method or a recovery plan is, you know, pretty important. Always keep your private SSH keys safe and backed up in a secure place.
Final Thoughts on Remote IoT Management
Getting comfortable with SSH for your IoT devices truly opens up a world of possibilities for managing them from anywhere. It means you can keep your smart home running, monitor remote sensors, or update tiny computers without ever needing to be right next to them. This ability to connect securely and reliably is, you know, a cornerstone of effective IoT deployment. It gives you a lot of control and peace of mind, which is very helpful.
Remember that learning to troubleshoot common issues, like those related to hostname resolution or incorrect configuration files, is part of the journey. Our team's experience with Ubuntu Server 22.04.3 LTS and the specific SSH configuration challenges highlights that even experienced folks run into these things. The key is to understand the differences between client and server settings and to know where to look when things go wrong. For more helpful information, learn more about IoT security on our site, and link to this page for remote device management tips. Keeping your connections secure with SSH keys and smart firewall rules is also a step you should always take. You can find more general advice on securing remote access on sites like the SSH.com Academy, which is a good
- How To Ripen Avocados
- How Many Legs Does A Spider Have
- How Long Is A Fortnight
- Mid Taper Textured Fringe
- Securely Connect Remote Iot Vpc Raspberry Pi Download Windows Free
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

Windows SSH Server | Learning, Secure shell, Software engineer