Mastering Remote IoT: Connecting Raspberry Pi To AWS VPC With SSH From Windows
Getting your Internet of Things projects up and running can feel a bit like setting sail on a vast ocean, particularly when you want to manage devices from afar. Imagine having a tiny computer, like a Raspberry Pi, out in the field, collecting valuable information. You need a way to reach it securely, to update its programs, or just check on its health, all from your everyday Windows computer. This is where the magic of remote IoT, AWS Virtual Private Cloud (VPC), and SSH comes together, giving you really good control over your distant devices.
This whole idea of remote access is pretty vital for anyone working with IoT. Whether you are a hobbyist with a smart home project or a small business setting up a network of sensors, being able to connect to your devices without physically being there saves a lot of time and effort. It helps you keep things running smoothly, even when your devices are in hard-to-reach spots, which is a big plus.
So, we are going to walk through how you can get your Raspberry Pi talking to your Windows machine, all while keeping things safe and sound within the Amazon Web Services (AWS) cloud. We will cover setting up a secure network, connecting your Pi, and making sure you have the right tools on your Windows computer. It is, in a way, about building a private, protected pathway directly to your IoT device, allowing you to manage it with ease and confidence. This guide will show you how to download necessary tools for Windows, too.
- Niece In Spanish Language
- Deep Winter Color Palette
- Somber Smithing Stone 6
- How To Make Stickers
- Kimberly Guilfoyle Before And After
Table of Contents
- Understanding the Basics of Remote IoT and AWS
- Preparing Your AWS Environment
- Getting Your Raspberry Pi Ready
- Accessing Your Raspberry Pi from Windows
- Common Challenges and Solutions
- Keeping Your Setup Secure
- Frequently Asked Questions
Understanding the Basics of Remote IoT and AWS
- Nice And Slow Lyrics
- Mid Taper Textured Fringe
- Sophie Rain Spiderman Video
- Filmy Fly Com
- Can You Eat Crocs
What is Remote IoT?
Remote IoT, in essence, means you can manage and interact with your physical devices from anywhere with an internet connection. This could be a sensor in a remote farm, a smart light in your living room, or a monitoring system in a factory. The idea is to gather information, send commands, and keep an eye on things without needing to be right next to the device. It is very much about extending your reach, so to speak, across distances.
This capability opens up so many possibilities. Think about home automation, where you can turn on your heating before you even get home. Or in agriculture, where farmers can monitor soil conditions from their office. It really changes how we interact with the physical world through technology, making things more efficient and often, more convenient, too.
Why AWS VPC for Your Raspberry Pi?
Using an AWS Virtual Private Cloud (VPC) for your Raspberry Pi setup offers a lot of good things, particularly for security and organization. A VPC is like having your own private, isolated section of the AWS cloud. Inside this private space, you can launch AWS resources, like virtual servers (EC2 instances), and define your own network settings, including IP address ranges, subnets, and network gateways. This means your Raspberry Pi, when connected, is not just out on the open internet, which is rather important.
By putting your Raspberry Pi within a VPC, you create a protected network environment. This helps keep your device safe from unwanted access. You can control exactly what traffic goes in and out, setting up strict rules that only allow authorized connections. This level of control is pretty hard to achieve with a simple home network setup, and it gives you peace of mind, too it's almost a necessity for serious projects.
The Role of SSH in Secure Access
SSH, which stands for Secure Shell, is a network protocol that lets you operate network services securely over an unsecured network. It provides a strong cryptographic connection between two devices, like your Windows computer and your Raspberry Pi. When you use SSH, all the information exchanged between your computer and the Pi is encrypted, meaning it is scrambled and unreadable to anyone trying to snoop. This is a very important part of keeping your remote access safe.
Without SSH, sending commands or files to your Raspberry Pi over the internet would be like shouting secrets across a crowded room. Anyone could listen in. With SSH, it is more like having a private, coded conversation directly with your device. It is the primary tool for remote command-line access, file transfers, and even setting up secure tunnels, which we will look at a little later. So, it is, in some respects, the backbone of secure remote management.
Preparing Your AWS Environment
Setting Up Your VPC: A Private Cloud Space
The first step in building your secure remote IoT setup is to create a Virtual Private Cloud (VPC) in AWS. Think of your VPC as a private, isolated section of the AWS cloud where you can launch your resources. It is like having your own dedicated data center, but in the cloud. You get to define its IP address range, which subnets it has, and how traffic flows in and out. This isolation is a really good thing for security, as it keeps your IoT devices away from the public internet by default.
To get started, log into your AWS Management Console. Go to the VPC service. You will want to create a new VPC. Give it a name that makes sense, like "MyIoTProjectVPC." You will also need to specify a CIDR block, which is a range of IP addresses for your private network. A common choice is `10.0.0.0/16`, which gives you plenty of addresses for your devices. After creating the VPC, you will then set up at least one public subnet and one private subnet within it. The public subnet will host a "jump server" that you will use to connect to your private devices, while your Raspberry Pi will live in the private subnet, shielded from direct internet exposure. This is a bit like having a guarded entrance to your private area.
Creating an EC2 Instance: Your Jump Server
Since your Raspberry Pi will be in a private subnet, you cannot directly connect to it from the internet. This is where a "jump server" comes in. A jump server is an EC2 instance (a virtual server in AWS) that you launch in your VPC's public subnet. You will connect to this jump server from your Windows computer, and then from the jump server, you will connect to your Raspberry Pi. It acts as a secure intermediary, a kind of bridge, if you will. This setup adds an extra layer of security, as only the jump server needs a public IP address, and it can be heavily secured.
When creating your EC2 instance, pick a small, cost-effective instance type, like a `t2.micro` or `t3.micro`, which is typically eligible for the AWS Free Tier. Choose an Amazon Machine Image (AMI) that is based on Linux, such as Amazon Linux 2 or Ubuntu Server. Make sure to launch it into the public subnet of your newly created VPC. During the setup, you will also create a key pair. This key pair is absolutely vital for securely connecting to your jump server using SSH. You will download the private key file (a `.pem` file) to your Windows computer. Keep this file very safe, as it is your digital key to the server. It is basically the only way to get in.
Configuring Security Groups for Safe Connections
Security groups act as virtual firewalls that control inbound and outbound traffic for your EC2 instances and other AWS resources. They are a really important part of your security strategy. You will need to set up two main security groups for this project: one for your jump server and one for your Raspberry Pi. For the jump server's security group, you will want to allow inbound SSH traffic (port 22) from your specific public IP address. This means only your computer can initiate an SSH connection to the jump server, which is a good thing. You can find your public IP address by searching "what is my IP" on Google. For the Raspberry Pi's security group, you should only allow inbound SSH traffic (port 22) from the private IP address range of your VPC. This ensures that only your jump server can connect to the Pi, and no outside traffic can reach it directly. It is, in a way, like having a bouncer at the door, letting only specific people in. Learn more about security best practices on our site.
You might also need to configure network ACLs (Access Control Lists) for more granular control over your subnets, but for a basic setup, security groups often do the trick. The key is to be as restrictive as possible, only opening ports and allowing traffic that is absolutely necessary. This principle, sometimes called "least privilege," helps minimize potential security risks. It is a fundamental part of keeping your system safe, and honestly, it is usually a good idea to spend a little extra time on this part of the setup.
Getting Your Raspberry Pi Ready
Installing Raspberry Pi OS
Before you can connect your Raspberry Pi to your AWS VPC, you need to get its operating system installed. The most common choice is Raspberry Pi OS (formerly Raspbian), which is a version of Debian Linux optimized for the Raspberry Pi. You will need a microSD card, a computer with a card reader, and the Raspberry Pi Imager software. The Imager is pretty easy to use; you just select your Raspberry Pi model, choose the Raspberry Pi OS (Lite version is often best for headless IoT applications, as it uses fewer resources), and then select your microSD card. The software does the rest, writing the operating system image to the card. It is a straightforward process, and it usually takes just a few minutes. This is, basically, the foundation for everything else we will do.
Once the OS is written, you will need to do a couple of things to prepare it for remote access. Before you eject the microSD card, you can create an empty file named `ssh` (no extension) in the boot partition of the card. This tells the Raspberry Pi to enable SSH automatically on its first boot. You can also create a `wpa_supplicant.conf` file in the boot partition to pre-configure your Wi-Fi settings, which is incredibly handy if your Pi will be in a place without easy wired access. This file should contain your Wi-Fi network name (SSID) and password. These little steps save you from needing a keyboard and monitor for the initial setup, which is often a big convenience.
Enabling SSH on Your Pi
As mentioned, placing an empty `ssh` file in the boot partition before the first boot is the easiest way to enable SSH. If you have already booted your Raspberry Pi without doing this, you can enable SSH manually. Connect a monitor and keyboard to your Pi, log in, and open a terminal. Then, type `sudo raspi-config` and navigate to "Interface Options" -> "SSH" and enable it. This command-line tool is a pretty common way to configure various aspects of your Raspberry Pi. After enabling SSH, it is a good idea to change the default password for the `pi` user (or create a new user and disable the `pi` user) for security reasons. The default password is "raspberry," which is very well-known and not secure at all. So, you know, change it immediately. This step is, actually, a critical part of securing your device.
Once SSH is enabled, you can test it from a local computer on the same network using `ssh pi@your_pi_ip_address`. You will be prompted for the password you set. Successfully connecting locally means the SSH service is running correctly on your Pi. This preliminary test is quite useful, as it confirms that the basic SSH setup is working before you introduce the complexities of the AWS VPC. It is, in a way, a small victory before the main event.
Connecting the Pi to Your VPC
Connecting your Raspberry Pi to your AWS VPC typically involves a VPN (Virtual Private Network) connection. Since your Pi is a physical device, it cannot just "be" inside the AWS cloud like an EC2 instance. You need a secure tunnel from your Pi to your VPC. One common way to do this is by setting up an OpenVPN client on your Raspberry Pi and an OpenVPN server on an EC2 instance within your VPC. The EC2 instance acting as the OpenVPN server would be in your private subnet, and it would have a private IP address. This creates a secure, encrypted tunnel, making your Raspberry Pi appear as if it is directly on your VPC's private network. It is, in a way, extending your private cloud to your physical device. This method provides a strong security posture, as all traffic between your Pi and your VPC is encrypted and routed through the VPN tunnel. It is a slightly more advanced setup, but it offers really good protection.
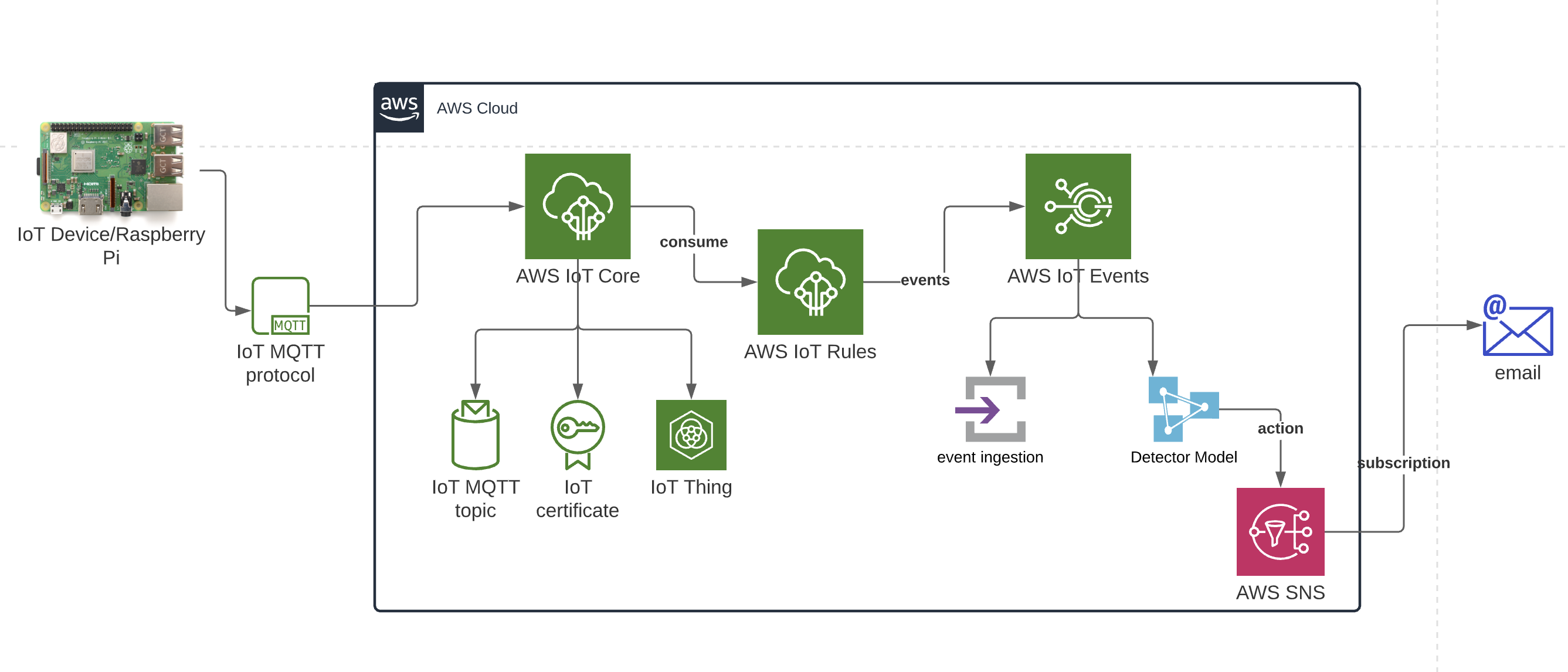
Another approach, especially for simpler setups or when you want to avoid running a full VPN server, is to use AWS IoT Core and its Device Gateway. While not directly "connecting" the Pi to the VPC in the traditional network sense, it allows your Pi to securely communicate with AWS services within your VPC (via endpoints) without needing a direct VPN tunnel. The Pi would publish and subscribe to MQTT topics, and AWS IoT Core would handle the secure routing of these messages. This can be a simpler way to get data in and out securely, especially if your primary goal is data exchange rather than full remote shell access via SSH. However, for direct SSH access, the VPN method is usually the way to go. You can also explore options like AWS Site-to-Site VPN or AWS Client VPN, but these often involve more complex configurations or costs. For a hobbyist or small project, a self-hosted OpenVPN server on an EC2 instance is often a very practical choice. We can discuss more about AWS IoT Core features on our other pages.
Accessing Your Raspberry Pi from Windows
Downloading SSH Client for Windows
To connect to your jump server and then to your Raspberry Pi from your Windows computer, you will need an SSH client. Luckily, modern versions of Windows (Windows 10 and 11) come with an OpenSSH client built-in. You can usually access it directly from PowerShell or Command Prompt. Just type `ssh` in your terminal, and if you see a list of commands, it is installed and ready to go. If not, you might need to enable it through "Optional features" in your Windows settings. This built-in client is usually enough for most needs, and it is pretty convenient, too.
For those who prefer a graphical interface or need more advanced features, popular third-party SSH clients like PuTTY are widely used. PuTTY is free, open-source software that provides a user-friendly way to manage SSH connections. You can download PuTTY from its official website. Once downloaded, it is a single executable file, so there is no complex installation process. Just run it. PuTTY also includes PuTTYgen, a tool for generating SSH key pairs and converting existing keys (like your `.pem` file from AWS) into a format that PuTTY can use (a `.ppk` file). This conversion is often necessary if you are using PuTTY with AWS EC2 key pairs. So, you know, pick the tool that feels right for you, but the built-in Windows SSH is usually a good starting point for remoteiot vpc ssh raspberry pi aws download windows.
Connecting via SSH Tunneling
Now that you have your jump server and your Raspberry Pi connected to your VPC (via VPN, as discussed), and you have an SSH client on Windows, it is time to connect. Since your Raspberry Pi is in a private subnet, you cannot directly SSH into it from your Windows machine. You will use SSH tunneling, also known as SSH port forwarding, through your jump server. This means you first SSH into your public jump server, and then from there, you establish another SSH connection to your private Raspberry Pi. It is like a two-step process, or rather, like walking through a secured lobby to get to a private office. This method is very secure because only your jump server needs to be exposed to the internet, and all traffic between your jump server and your Pi stays within your private VPC network.
Here is how you would typically do it using the built-in OpenSSH client in PowerShell:
ssh -i "C:\Path\To\Your\aws-key.pem" -L 8080:your_pi_private_ip:22 ec2-user@your_jump_server_public_ip- `-i "C:\Path\To\Your\aws-key.pem"`: This specifies the path to your private key file that you downloaded when setting up your EC2 jump server.
- `-L 8080:your_pi_private_ip:22`: This is the crucial part for tunneling. It tells your local machine to forward traffic from your local port 8080 to port 22 (SSH) on your Raspberry Pi's private IP address, *through* the jump server.
- `ec2-user@your_jump_server_public_ip`: This is the username (typically `ec2-user` for Amazon Linux AMIs or `ubuntu` for Ubuntu AMIs) and the public IP address of your jump server.
ssh pi@localhost -p 8080Common Challenges and Solutions
Setting up remote access for your Raspberry Pi in AWS can sometimes throw a few curveballs. One common issue is connectivity problems. If you cannot connect to your jump server, first check your security group rules in AWS. Make sure inbound SSH (port 22) is allowed from your current public IP address. Also, confirm that your `.pem` key file has the correct permissions (read-only for the owner on Linux/macOS, or just ensure it is not publicly writable on Windows). If you can connect to the jump server but not the Pi, double-check the Raspberry Pi's security group to ensure it allows SSH from your VPC's private IP range. Also, confirm the Pi's private IP address is correct in your SSH tunnel command. It is very easy to make a small typo, so careful checking is usually a good first step.
Another challenge can be related to the Raspberry Pi's network connection. If your Pi is using Wi-Fi, ensure the `wpa_supplicant.conf` file is correctly configured with the right SSID and password. Sometimes, the Pi might lose its Wi-Fi connection, especially after a power cycle. You might need to implement a simple script on the Pi to automatically reconnect to Wi-Fi if it drops. Also, make sure your Pi has a static private IP address within your VPC's private subnet, or at least a reserved DHCP address, so its IP does not change unexpectedly. Dynamic IPs can be a real headache for consistent remote access, so it is, in some respects, better to fix that from the start. Finally, always check your logs. On the jump server, `/var/log/auth.log` can give clues about failed SSH attempts. On the Raspberry Pi, similar logs can help diagnose issues. These logs are, basically, your best friends when troubleshooting.
Keeping Your Setup Secure
Security is not a one-time setup; it is an ongoing effort, especially with remote IoT devices. First and foremost, always use strong, unique passwords for your Raspberry Pi. Better yet, configure SSH to use key-based authentication only and disable password authentication entirely. This means you will generate an SSH key pair on your Windows machine, copy the public key to your Raspberry Pi, and then use your private key to connect. This is much more secure than passwords, which can be guessed or brute-forced. It is, in a way, like having a special, unguessable lock and key. Additionally, regularly update your Raspberry Pi's operating system and installed software. Outdated software often has security vulnerabilities that can be exploited. You can do this with `sudo apt update` and `sudo apt upgrade` commands on your Pi. This is, honestly, a simple but very important step.
Limit the number of open ports on your security groups to only what is absolutely necessary. If you are only using SSH, then only port 22 should be open. Avoid opening ports to the entire internet (`0.0.0.0/0`) unless it is truly unavoidable and you have other layers of security in place. Implement a firewall on your Raspberry Pi itself, such as `ufw` (Uncomplicated Firewall), to add another layer of protection. This can restrict what connections are allowed even if someone manages to bypass your AWS security groups. Consider setting up intrusion detection systems or monitoring tools on your jump server and Raspberry Pi to alert you to suspicious activity. Finally, regularly review your AWS security group rules and network configurations to ensure they still meet your security needs. As your project evolves, so too should your security measures. This proactive approach helps keep your remote IoT setup safe from potential threats, which is, very, very important in today's digital world.
Frequently Asked Questions
How do I make my Raspberry Pi always accessible from AWS, even if its IP changes?
To keep your Raspberry Pi always accessible, you should give it a static private IP address within your VPC's private subnet. You can configure this directly on the Raspberry Pi's network settings. If you are using DHCP, you might be able to reserve a specific IP address for your Pi's MAC address in your VPC's DHCP options set. This ensures its private IP does not change, which is pretty helpful for consistent SSH tunneling. Alternatively, for more advanced setups, you could use a service like AWS IoT Core which doesn't rely on direct IP address access for device communication, which is, you know, a different way to think about connectivity.
What is the easiest way to transfer files to my Raspberry Pi through the jump server?
The easiest way to transfer files is by using `scp` (Secure Copy Protocol) or `sftp` (SSH File Transfer Protocol), which are part of the SSH suite. With `scp`, you can use a command like this from your Windows PowerShell (after setting up the SSH tunnel): `scp -P 8080 "C:\Path\To\Your\local_file.txt" pi@localhost:/home/pi/remote_directory/`. The `-P 8080` tells `scp` to use your local forwarded port. For a more graphical approach, tools like WinSCP for Windows can be configured to use an SSH tunnel, allowing you to drag and drop files. This makes file management much simpler, which is, honestly, a real time-saver.
Can I use a VPN client directly on my Windows machine instead of a jump server?
Yes, you can. If you set up an AWS Client VPN endpoint in your VPC, or if you run a VPN server (like OpenVPN) on an EC2 instance in your VPC, you can install the corresponding VPN client directly on your Windows machine. Once connected to the VPN, your Windows computer will be virtually part of your VPC network, allowing you to directly SSH into your Raspberry Pi using its private IP address. This eliminates the need for a jump server for SSH access, simplifying the connection process. It is, in a way, like bringing your computer directly into your private cloud. This method can be quite convenient, but it does require setting up and managing a VPN server or Client VPN endpoint, which can have its own complexities and costs, too it's almost a trade-off.
- How To See Deleted Sms
- Taper Fade Black Men
- Help I Accidentally Forgot How Gravity Works
- Steve Horstmeyer Dogs
- How To Get Rid Of Gnats

Mastering Remote IoT VPC SSH On Raspberry Pi AWS For Windows Users
Mastering RemoteIoT VPC SSH Raspberry Pi AWS Download Free: The

Securely Connect RemoteIoT VPC Raspberry Pi AWS Download Windows