Securely Connect Remote IoT: P2P Freedom For Your Raspberry Pi Projects
Are you feeling a bit frustrated with how your smart gadgets or internet-connected devices just aren't as secure as you'd like, or maybe they're costing you too much to keep connected? It's a common worry, you know, when your system flashes warnings like, "Your device is at risk because it's out of date and missing important security and quality updates." Nobody wants to see messages about untrusted connections or problems getting to a website securely, like when Firefox tells you it "can't confirm that your connection is secure." It’s pretty unsettling, and you might feel like there's no other choice sometimes, especially when you’ve tried different browsers and nothing seems to help. We get it, and that’s why finding a reliable, private way to link up your remote internet of things (IoT) devices is, frankly, a big deal.
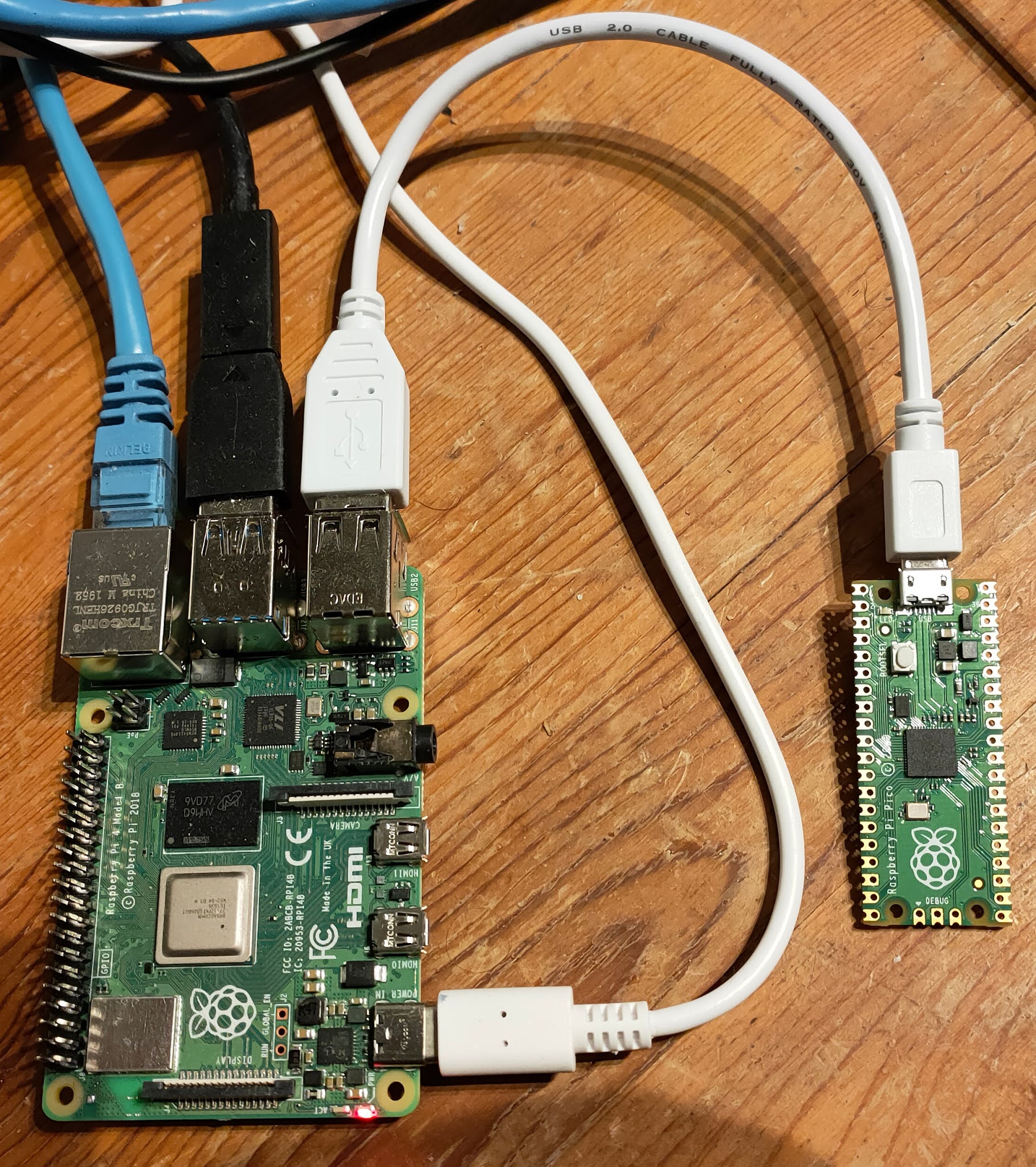
Many folks are looking for smart ways to keep their digital world safe, and that includes their tiny computers like the Raspberry Pi, which are often out there doing important jobs. The idea of securely connecting remote IoT devices using a peer-to-peer (P2P) setup on a Raspberry Pi, and doing it all without spending a dime on servers, sounds like a dream for many. This is where solutions like securely connecting remote IoT P2P SSH Raspberry Pi free become, well, incredibly helpful. It's about taking back some control, keeping things private, and avoiding those annoying security alerts that pop up when something isn't quite right.
This guide, you see, aims to show you how to securely connect your Raspberry Pi in a remote IoT P2P environment. We'll even point you towards free options for essential software, because who doesn't love saving a little money? We'll talk about how to get your systems back on track so they can run more securely, tackling those "connection untrusted" issues head-on. So, if you're keen to give your IoT projects a much-needed security boost and want to understand how P2P can help, you've come to the right spot. Let's make your Raspberry Pi IoT connections strong and private, shall we?
- Baby Alien Fan Bus
- How Do You Spell
- King Edward Love Chair
- Remoteiot P2p Download
- Boo Did I Scare You Im A Job Application
Table of Contents
- Why Secure P2P for Your Raspberry Pi IoT?
- Understanding P2P SSH: Your Free Security Gateway
- Getting Started: Preparing Your Raspberry Pi
- Step-by-Step: Securely Connecting Your Devices
- Common Challenges and Troubleshooting Tips
- Beyond the Basics: What Else Can You Do?
- Frequently Asked Questions
- Conclusion
Why Secure P2P for Your Raspberry Pi IoT?
Connecting your Raspberry Pi to other devices, especially when they are far away, can feel a bit like trying to talk across a crowded room. You want your messages to get through clearly and privately, you know? The usual ways of doing this often come with their own set of headaches, like security worries or unexpected costs. That's why figuring out how to securely connect remote IoT P2P free Raspberry Pi setups is, well, pretty important for many.
The Problem with Traditional Connections
Think about how you usually connect to things online. Often, you're going through a central server, maybe even one run by a big company. This can mean your data takes a long detour, and that central point can become a target for those who want to snoop or cause trouble. We've all seen those warnings, haven't we, about "This connection is untrusted" or messages saying your device is "missing important security and quality updates." It's a sign that relying solely on these traditional paths can leave your Raspberry Pi, and whatever it's connected to, feeling a bit exposed. Plus, some cloud-based IoT platforms can start to add up in cost, especially as your projects grow, which is, honestly, a bit of a bummer if you're trying to keep things free.
The Appeal of Peer-to-Peer
Now, P2P is a different story. Instead of going through a central hub, your Raspberry Pi talks directly to another device. It's like having a private, direct line of communication. This means less chance for someone to listen in, and it often feels more reliable because there's no single point of failure. It's a way to build a connection that feels, in a way, more personal and more controlled. This directness also helps with those tricky firewall situations that can make remote access a real headache. It's a pretty neat trick, really, to bypass some of those usual network barriers.
- No Te Duermas Morena
- Eminence In Shadow Season 3
- What Does Yeet Mean
- Taper Fade Black Men
- Lagu Waiting For You
Why Raspberry Pi is a Great Fit
The Raspberry Pi, with its small size and surprisingly good processing power, is just about perfect for this kind of work. It’s a versatile little computer that can run Linux, giving you all the tools you need to set up secure connections. Because it’s so affordable and widely available, it’s become a go-to for anyone wanting to experiment with IoT without a huge investment. Plus, there’s a massive community around it, so finding help or new ideas is, basically, never a problem. It's a really good platform for learning and for putting your ideas into action, especially when you're aiming to securely connect remote IoT P2P free Raspberry Pi setups.
Understanding P2P SSH: Your Free Security Gateway
When we talk about securely connecting remote IoT P2P free Raspberry Pi devices, a big part of that conversation involves SSH. It's a core tool, and understanding how it works, especially with a P2P twist, is pretty key to making your connections strong and private. You want to make sure your data is safe, and SSH helps a lot with that, you know?
What is SSH, Anyway?
SSH stands for Secure Shell. It's a way to access a computer remotely, but with a strong layer of encryption. Imagine you're typing commands on your home computer, but those commands are actually running on your Raspberry Pi hundreds of miles away. SSH makes that happen, and it scrambles all the information so that anyone trying to peek in just sees gibberish. This is, in fact, incredibly important because it protects your login details and any data you send back and forth. It's like having a secret, coded conversation that only you and your Raspberry Pi can understand. This means you can manage your Pi, run programs, and even transfer files, all while feeling pretty confident about your privacy.
How P2P Makes SSH Even Better
Normally, setting up SSH for remote access can involve things like port forwarding on your router, which can be a bit of a security headache. It opens up a door to your home network, and if not done carefully, it could be exploited. This is where the P2P part comes in. Instead of opening a specific port to the whole internet, P2P SSH uses clever techniques to establish a direct connection between your computer and your Raspberry Pi, even if both are behind different routers or firewalls. It's like they find a way to shake hands directly, without needing a big, public meeting place. This makes the connection much more private and, you know, a lot harder for unwanted guests to find. It's a smart way to get around some of those network barriers.
The "Free" Aspect: No Server Costs
One of the best things about using P2P SSH for your Raspberry Pi IoT projects is that it truly can be free. Unlike some commercial IoT platforms or VPN services that charge monthly fees, P2P SSH relies on direct connections. You don't need to rent a dedicated server or pay for a cloud service to act as an intermediary. Your Raspberry Pi itself, along with your other devices, does all the work. This means you can keep your project costs down, which is a pretty big win for hobbyists and small-scale deployments. It's a fantastic option if you're looking to securely connect remote IoT P2P free Raspberry Pi setups, because, well, free is good, isn't it?
Getting Started: Preparing Your Raspberry Pi
Before you can securely connect remote IoT P2P free Raspberry Pi devices, you need to get your little computer ready for action. This involves making sure it has the right software and that its basic security is in good shape. It's a bit like preparing a sturdy foundation before building a house, you know?
Essential Software and Tools
First off, you'll need a fresh installation of Raspberry Pi OS (formerly Raspbian) on your Pi. This is the operating system that makes everything run. You can download it for free from the official Raspberry Pi website. You'll also need a way to flash the OS onto an SD card; tools like Raspberry Pi Imager are, basically, perfect for this and are also free to use. For the P2P SSH part, you'll likely use a tool that helps establish those direct connections. There are several open-source, free options available, such as ZeroTier or Tailscale, which create a virtual network between your devices. These tools are pretty straightforward to install and configure on your Raspberry Pi, and they handle the complex networking stuff for you. It's really quite handy, honestly, how much they simplify things.
Initial Setup and Security Hardening
Once your Raspberry Pi OS is up and running, there are a few crucial steps to make it more secure right from the start. First, change the default password. This is, like, super important. The default username is usually 'pi' and the password 'raspberry', which is very well-known and not at all secure. Second, make sure your system is up to date. You know how your computer sometimes says, "Your device is at risk because it's out of date and missing important security and quality updates"? The same applies here. Run `sudo apt update` and `sudo apt upgrade` in the terminal regularly. This brings in the latest security patches and bug fixes. Third, disable password-based SSH login once you've set up SSH keys (we'll get to that soon). This means only devices with the correct cryptographic key can connect, which is, honestly, a much stronger security measure. Finally, consider setting up a basic firewall, like UFW, to limit incoming connections to only what's necessary. These steps might seem small, but they make a huge difference in keeping your Raspberry Pi safe from unwanted access.
Step-by-Step: Securely Connecting Your Devices
Now that your Raspberry Pi is ready, let's get down to the actual process of making those secure P2P connections. This is where the magic happens, so to speak, allowing you to securely connect remote IoT P2P free Raspberry Pi setups. It's not as hard as it might sound, really.
Setting Up SSH Keys for Trust
Instead of passwords, which can be guessed or stolen, SSH keys offer a much more secure way to log in. You'll generate a pair of keys: a private key (which stays secret on your local computer) and a public key (which you place on your Raspberry Pi). When you try to connect, your computer uses its private key to prove its identity to the Raspberry Pi, which checks it against the public key. It's a bit like having a unique digital handshake. To generate keys on your local machine, you'd typically use the `ssh-keygen` command. Then, you'd copy the public key to your Raspberry Pi using `ssh-copy-id`. This step is, frankly, foundational for a truly secure connection. It means you won't have to type a password every time, and it's much harder for someone else to break in.
Establishing the P2P Link
This is where your chosen P2P software, like ZeroTier or Tailscale, comes into play. You'll install this software on both your Raspberry Pi and the device you want to connect from (your laptop, for example). Once installed, you'll join both devices to the same virtual network provided by the P2P service. This creates a secure, encrypted tunnel between them, making them act as if they are on the same local network, even if they are miles apart. This bypasses the need for complex router configurations or public IP addresses, which is, basically, a huge convenience. It's pretty amazing how these tools can make geographically separated devices feel like they're sitting right next to each other on your home network.
Testing Your Secure Connection
After setting up the SSH keys and establishing the P2P link, it's time to test everything out. From your local computer, you should be able to SSH into your Raspberry Pi using its virtual IP address provided by the P2P network. For example, if your Pi's virtual IP is `10.147.17.123`, you would type `ssh pi@10.147.17.123` into your terminal. If everything is set up correctly, you should connect directly without any "connection untrusted" warnings or password prompts. This confirms that your securely connected remote IoT P2P free Raspberry Pi setup is working as intended. You can then try running a few commands, maybe check a sensor reading, or even transfer a small file to make sure the connection is stable and reliable. It's a pretty satisfying moment when it all just works, you know?
Common Challenges and Troubleshooting Tips
Even with the best intentions, sometimes things don't go exactly as planned when you're trying to securely connect remote IoT P2P free Raspberry Pi setups. It's completely normal to hit a snag or two. Knowing what to look for can save you a lot of frustration, you see.
Connection Untrusted Messages
Remember those annoying "This connection is untrusted" messages, like when Firefox complains it "can't confirm that your connection is secure"? These often pop up when a security certificate or a host key doesn't match what your system expects. When using SSH, if you connect to a Raspberry Pi for the first time, your client will ask you to confirm its host key. Always verify this key if you can. If you get this message on a subsequent connection, it might mean the Pi's host key has changed (maybe you reinstalled the OS), or, unfortunately, it could mean someone is trying to intercept your connection. If you're sure it's legitimate, you might need to remove the old entry from your `~/.ssh/known_hosts` file. However, if you're not sure, it's best to investigate further. Always be cautious when you see these warnings, because, well, your security depends on it.
Pin Not Working Issues
Sometimes, people run into problems where a PIN or password isn't working to log into their account, even on Windows 11 sign-in screens. While this specific issue is more about local login, it highlights a general problem: authentication failures. When connecting to your Raspberry Pi, if your SSH key isn't working, double-check that the public key is correctly installed on the Pi in the `~/.ssh/authorized_keys` file and that the permissions are correct (usually 600 for the file and 700 for the `.ssh` directory). Also, make sure your private key on your local machine is accessible and that you're using the correct one. Sometimes, it's just a simple typo or a file permission issue that can cause a lot of head-scratching. It's often the little things that trip us up, isn't it?
Keeping Your System Updated
One of the most frequent reasons for security vulnerabilities is simply having outdated software. As mentioned earlier, if your device is "out of date and missing important security and quality updates," it's at risk. This isn't just about the Raspberry Pi OS itself, but also the P2P software and any other applications you're running. Make it a regular habit to update your Raspberry Pi by running `sudo apt update && sudo apt upgrade`. For your P2P software, check their official documentation for update procedures. Staying current with updates is, frankly, one of the easiest and most effective ways to maintain the security of your securely connected remote IoT P2P free Raspberry Pi setup. It's a simple step that pays off big time in peace of mind.
Beyond the Basics: What Else Can You Do?
Once you've mastered the art of securely connecting remote IoT P2P free Raspberry Pi setups, you might find yourself wondering what other cool things you can achieve. The possibilities are, honestly, pretty vast when you have a reliable and private connection to your little computers.
Automating Connections
Manually typing SSH commands every time you want to connect can get a bit tiring, can't it? You can automate this process. For instance, you can create simple shell scripts on your local machine that connect to your Raspberry Pi with a single command. If you use SSH keys without passphrases (be cautious with this, as it reduces security if your private key is compromised), the connection can be almost instant. Some P2P services also offer client applications that automatically establish the virtual network when your devices are online, making the connection process nearly seamless. This means your IoT devices can be, basically, always ready for you to access, without any fuss. It's a really nice quality-of-life improvement.
Expanding Your IoT Network
With a secure P2P foundation, you're not limited to just one Raspberry Pi. You can add more Pis, or even other types of devices, to your virtual P2P network. Imagine having a network of sensors spread across a large area, all securely reporting data back to a central Raspberry Pi, or perhaps even directly to your laptop, without needing a costly cloud service. You could have a Pi monitoring your garden, another checking your pet's food dispenser, and yet another controlling your smart lights, all talking to each other and to you through these secure P2P tunnels. This method scales pretty well for personal projects or small-scale deployments, giving you a lot of flexibility. It's a truly powerful way to build out your own private IoT ecosystem, you know, without breaking the bank.
Frequently Asked Questions
How do I access my Raspberry Pi remotely without port forwarding?
You can access your Raspberry Pi remotely without opening ports on your router by using P2P networking solutions like ZeroTier or Tailscale. These tools create a secure virtual network that allows your devices to communicate directly, bypassing the need for traditional port forwarding, which is, honestly, a much safer approach. Once the P2P network is established, you can use SSH to connect to your Pi using its virtual IP address.
What is the most secure way to connect to a Raspberry Pi?
The most secure way to connect to a Raspberry Pi typically involves using SSH with key-based authentication (instead of passwords), disabling password login for SSH, keeping your Raspberry Pi OS and all software updated, and using a P2P network for remote access to avoid exposing SSH ports directly to the internet. This combination reduces the attack surface and relies on strong cryptographic methods, which is, basically, a very good idea for security.
Can I use a Raspberry Pi for P2P IoT communication?
Absolutely, a Raspberry Pi is an excellent choice for P2P IoT communication. Its small size, low power consumption, and ability to run a full Linux operating system make it ideal for acting as a node in a P2P network. You can install P2P software like ZeroTier or Tailscale directly on the Pi, allowing it to securely communicate with other devices on the same virtual network, which is, honestly, pretty convenient for building distributed IoT systems.
Conclusion
Getting your Raspberry Pi to connect securely, remotely, and for free using P2P methods is, frankly, a game-changer for many IoT projects. We've talked about how traditional connections can be a bit risky, with those "untrusted" warnings and the constant need for updates to keep things safe. By moving to a P2P model, especially with SSH, you create a direct, private line between your devices, cutting out the middleman and often saving you money on server costs. It’s about making your connections strong and giving you more control over your data, which is, you know, a pretty big deal in today's digital world.
We covered getting your Raspberry Pi ready, setting up those important SSH keys for a truly secure handshake, and using P2P software to bridge the distances. We even touched on how to handle those common hiccups, like connection issues or making sure your system stays fresh with updates. This approach means you can keep your projects private and protected, avoiding those
- How Long Does It Take For Eyelashes To Grow Back
- Dress To Impress Creator Gigi
- Lagu Waiting For You
- How To Cook Scallops
- Two Babies One Fox Comic
Securely Connect RemoteIoT VPC Raspberry Pi: Free Download For Windows

Securely Connect Remote IoT VPC Raspberry Pi: Free Download For Windows

Securely Connect Remote IoT P2P Raspberry Pi Download Mac Free: A