Securely Connect Remote IoT: P2P SSH For Raspberry Pi From Windows
Are you feeling that familiar worry about your gadgets being exposed online? It's a common feeling, especially when your device seems to tell you it's "out of date and missing important security and quality updates." That message, or perhaps seeing a warning like "This connection is untrusted" when you try to reach something important, can really make you think about how safe your digital life actually is. We all want our connections to be solid and trustworthy, yet it feels like there's often "a problem connecting securely to this website," doesn't it?
It's a bit like trying to get somewhere new, but the map is old and some roads are just gone. You want to sign in faster and more securely, but then you hit a snag, perhaps your usual login pin isn't working on Windows 11, or you are asked to enter your password to set up something like Windows Hello. These moments, quite honestly, show us just how much we rely on secure ways to interact with our technology, especially when it's not right next to us, you know?
This article is here to help you get a handle on how to securely connect your remote IoT devices, like a Raspberry Pi, right from your Windows computer. We will talk about peer-to-peer (P2P) SSH, a really good way to make sure your connection is safe and sound. It's about getting you back on track so your systems can run more securely, without those frustrating "untrusted connection" warnings popping up. So, let's just get going, shall we?
- King Edward Love Chair
- Lagu Waiting For You
- All You Can Eat Wings Buffalo Wild Wings
- Two Person Yoga Poses
- Securely Connect Remoteiot Vpc Raspberry Pi Aws Server
Table of Contents
- Understanding the Need for Secure Connections
- Why Raspberry Pi and IoT Devices?
- The Power of P2P SSH for Remote Access
- Preparing Your Raspberry Pi for Secure P2P SSH Access
- Connecting from Your Windows Computer
- Troubleshooting Common Secure Connection Problems
- Maintaining Ongoing Security for Your IoT Setup
- Frequently Asked Questions
- Wrapping Things Up
Understanding the Need for Secure Connections
In our modern world, where everything seems to be linked, keeping your devices safe is a really big deal. You might have seen messages that say "Your device is at risk because it's out of date and missing important security and quality updates." This kind of alert is a clear sign that your system needs some attention. It's almost like leaving your front door unlocked; you would not want to do that, would you?
Think about how often you see warnings like "This connection is untrusted." Whether it's Firefox telling you it "can't confirm that your connection is secure" to a website, or just a general "problem connecting securely," these messages point to a core issue. They mean that the identity of the thing you are trying to connect to cannot be verified, which is a bit unsettling. A secure connection is basically a handshake that both sides trust, and without that, things can go wrong, so.
The risks are pretty real. Unsecured connections can let unwanted people snoop on your data, or even take control of your devices. This is especially true for IoT gadgets, which might not always have the strongest built-in defenses. Making sure your connections are secure means protecting your information, keeping your devices working as they should, and giving yourself some peace of mind, too it's almost.
- What Does Nvm Mean
- Space City Home Network
- Wasmo Somali Chanel
- What Does Ig Mean
- How To Erase Gel Nail Polish
Why Raspberry Pi and IoT Devices?
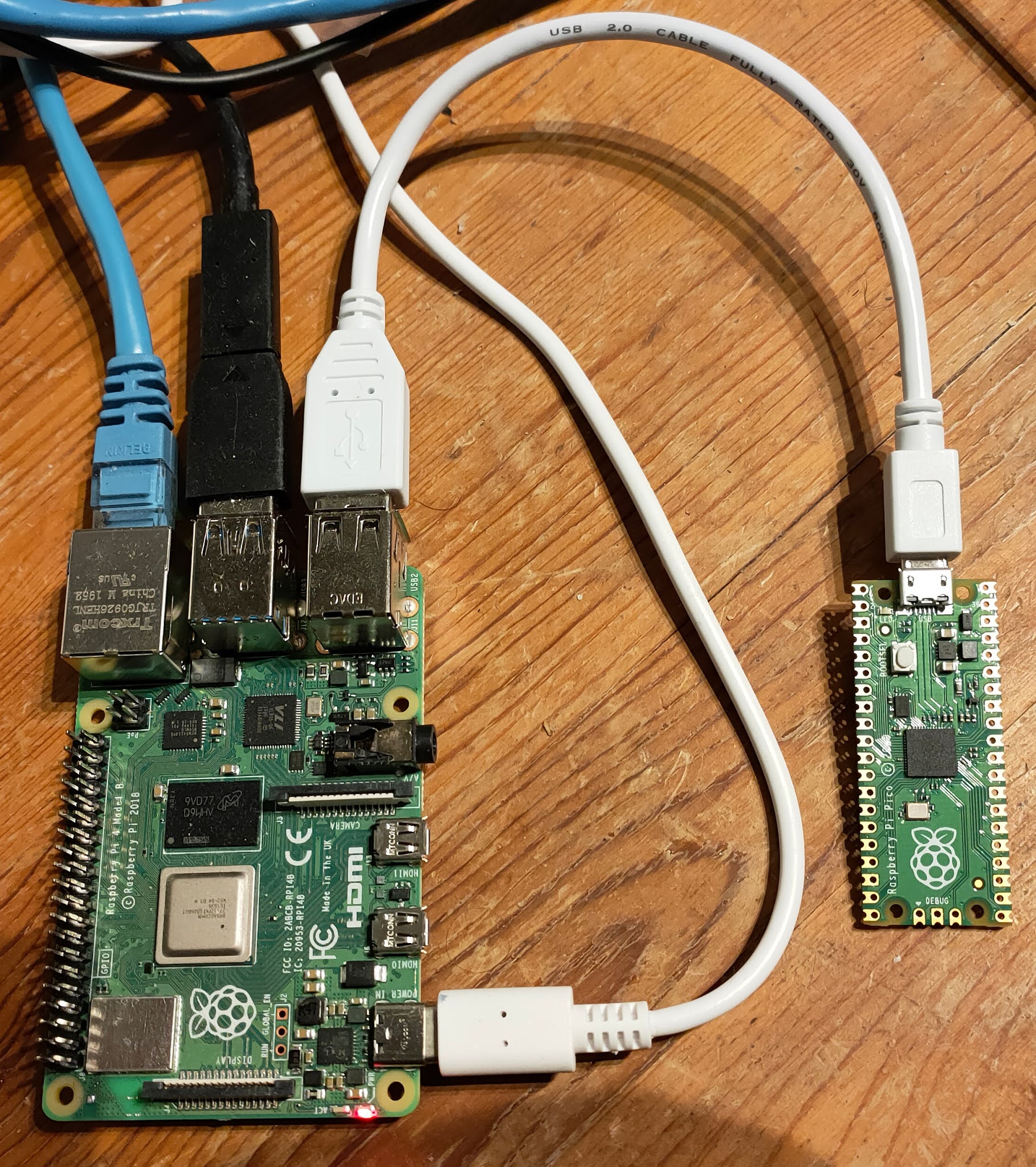
Raspberry Pi boards are, in a way, tiny, affordable computers that are very popular for all sorts of projects. People use them for home automation, custom servers, environmental monitors, and so much more. They are a big part of the Internet of Things (IoT) movement, which is about connecting everyday objects to the internet. This allows them to send and receive data, and you can control them from far away, that is.
IoT devices, including the Raspberry Pi, are becoming more common in homes and businesses. They collect all sorts of data, from temperature readings to video feeds. Because they often sit outside traditional network defenses, they can be easy targets if not set up with care. So, connecting to them securely, especially when they are somewhere remote, is absolutely vital, you know?
The flexibility of a Raspberry Pi means it can be placed almost anywhere, perhaps monitoring a garden or a remote cabin. But this also means you need a good way to reach it without physically being there. That is where a secure remote connection comes into play, making sure your tiny computer is safe from prying eyes, or rather, digital intruders, sort of.
The Power of P2P SSH for Remote Access
SSH, or Secure Shell, is a network protocol that lets you access a computer over an unsecured network in a very secure way. It provides a strong, encrypted channel for data exchange. When we talk about P2P SSH, it means setting up a direct, secure connection between your Windows computer and your Raspberry Pi, without needing a middle server or complex network setups, typically.
This direct approach helps avoid some of the common security problems that arise with older, less secure methods. It's a bit like having a private, coded conversation instead of shouting your plans across a crowded room. P2P SSH helps protect against eavesdropping and tampering, which is pretty important for sensitive IoT data, you know?
Using SSH keys instead of passwords adds another layer of security. Passwords can be guessed or stolen, but SSH keys are much harder to compromise. This method also helps address issues where a "site's identity can't be verified," because the key acts as a trusted form of identification. It means you can be much more confident that you are connecting to the right device, not some imposter, that.
Preparing Your Raspberry Pi for Secure P2P SSH Access
Getting your Raspberry Pi ready for a secure connection takes a few careful steps. It is not too hard, but each part is important for keeping things safe. We want to make sure your tiny computer is a tough nut to crack, in a way, even when it's out there on its own, so.
Initial Raspberry Pi Setup and SSH Activation
First things first, you need to get your Raspberry Pi up and running with its operating system, usually Raspberry Pi OS. Make sure you download the latest version from the official Raspberry Pi website. Using an older version is like leaving yourself open to those "out of date and missing important security" warnings, which you definitely want to avoid, you know?
Once the OS is on your SD card and the Pi boots up, you will need to enable SSH. This is a crucial step. You can do this through the Raspberry Pi Configuration tool under "Interfaces," or by creating an empty file named `ssh` (no extension) in the boot directory of the SD card before you even start the Pi. This just turns on the service that lets you connect remotely, that.
After enabling SSH, it is a very good idea to change the default password for the 'pi' user immediately. The default is widely known, and keeping it is a huge security risk. Pick a strong, unique password. This simple action can prevent a lot of potential headaches, honestly, so.
Network Considerations for P2P Connections
For a true P2P connection, your Raspberry Pi and your Windows computer need to be able to "see" each other on the network. If they are on the same local network, this is usually straightforward. You will just need the Pi's local IP address. You can find this by typing `hostname -I` into the Pi's terminal, you know.
If your Pi is in a different location, connecting P2P can get a little more complex. This often involves setting up port forwarding on the router where the Pi is located, or using a VPN (Virtual Private Network) to create a secure tunnel. Port forwarding means directing specific traffic from the internet to your Pi, but it needs to be done with care to avoid opening up other vulnerabilities, so.
For a truly direct P2P connection without port forwarding, solutions like reverse SSH tunnels or services that help establish direct connections through firewalls might be considered. These are a bit more advanced, but they essentially help your Windows machine and your Pi find a way to talk directly, even if they are far apart, apparently.
Hardening Your Pi for Top-Notch Security
This part is really important for making your Pi secure. The first step is to use SSH keys for authentication instead of passwords. SSH keys are a pair of cryptographic keys: a public key that you put on your Raspberry Pi, and a private key that stays on your Windows computer. When you try to connect, the two keys talk to each other to confirm your identity, which is much safer than typing a password, you know?
To set this up, you will generate the key pair on your Windows machine. Then, you copy the public key to your Raspberry Pi's `~/.ssh/authorized_keys` file. After that, you should disable password authentication for SSH on your Pi. This means only someone with the correct private key can log in, which is a very strong defense, that is.
Another good step is to change the default SSH port (which is 22) to a different, less common port. This does not make it truly secure on its own, but it does help reduce the amount of automated scanning from bots looking for easy targets. Also, consider setting up a basic firewall, like `ufw` (Uncomplicated Firewall) on your Pi, to allow only necessary connections. This just adds another layer of protection, sort of.
Connecting from Your Windows Computer
Now that your Raspberry Pi is ready and secure, it is time to connect from your Windows machine. This part is pretty straightforward once you have the right tools in place. It is almost like getting the right key for a very special lock, you know?
Getting the Right Tools on Windows
For Windows users, there are a few good options for connecting via SSH. The classic choice has long been PuTTY, which is a free SSH client. You can easily download PuTTY from its official website. It is a very reliable tool for making these kinds of connections, so.
More recently, Windows 10 and 11 come with OpenSSH client built-in. This means you might not even need to download extra software, which is pretty convenient. You can usually access it right from PowerShell or Command Prompt. This built-in option can make things a little smoother for many users, you know?
If you are using SSH keys, you will also need a way to generate them on Windows. PuTTY comes with PuTTYgen for this purpose, or you can use `ssh-keygen` if you are using the built-in OpenSSH client. Just make sure you keep your private key safe and sound, as it is the key to your secure connection, literally.
Step-by-Step SSH Connection Guide
Here is a basic rundown of how to connect, assuming you have your Pi's IP address and your SSH key (if you are using one):
Open your SSH client: If using PuTTY, open the PuTTY application. If using OpenSSH, open PowerShell or Command Prompt.
Enter connection details:
For PuTTY: In the "Session" category, type your Raspberry Pi's IP address (or hostname) in the "Host Name (or IP address)" field. Make sure the "Port" is set to your SSH port (default is 22, or whatever you changed it to). Select "SSH" as the connection type. If using an SSH key, go to "Connection" > "SSH" > "Auth" and browse for your private key file (usually a `.ppk` file for PuTTY).
For OpenSSH (PowerShell/CMD): Type `ssh pi@YOUR_PI_IP_ADDRESS` (replace `YOUR_PI_IP_ADDRESS` with your Pi's actual IP). If your private key is not in the default location, you might need to specify it with `-i C:\path\to\your\private_key`.
Connect: Click "Open" in PuTTY or press Enter in PowerShell/CMD. The first time you connect, you might see a warning about the host key not being cached. This is normal; just confirm you want to proceed. This is part of the trust building process, you know?
Authenticate: If you are still using a password, you will be prompted to enter it. If using SSH keys, and everything is set up correctly, you should be logged in automatically without needing a password. You are now securely connected to your Raspberry Pi, that is.
Troubleshooting Common Secure Connection Problems
Even with the best intentions, you might run into a "problem connecting securely" sometimes. It is a bit frustrating when you are trying to get something done and it just does not seem to work. Remember that "This connection is untrusted" message? We want to avoid that, so.
One common issue is network visibility. Can your Windows computer actually "see" the Raspberry Pi? Make sure they are on the same network segment, or that your port forwarding (if used) is set up correctly. A quick `ping YOUR_PI_IP_ADDRESS` from your Windows CMD can tell you if there is basic network communication, you know?
Another common problem is SSH not being enabled or running on the Pi. Double-check the SSH service status on your Pi. Sometimes, firewall settings on either the Pi or your router can block the connection. Make sure the SSH port is open and allowed through any firewalls. It is almost like a digital gatekeeper, and you need to tell it to let your connection through, you know?
If you are using SSH keys and cannot connect, verify that your public key is correctly placed in the `~/.ssh/authorized_keys` file on your Pi, and that the file permissions are correct (usually 600 for the file and 700 for the `.ssh` directory). Also, make sure you are pointing your SSH client to the correct private key on your Windows machine. These little details can really trip you up, that is.
Finally, always check for system updates. Just like your "out of date" Windows message, an outdated Raspberry Pi OS or SSH client can have bugs or security flaws that prevent proper connections. Keeping everything current can solve a lot of mysterious issues, honestly.
Maintaining Ongoing Security for Your IoT Setup
Setting up a secure connection is a really good start, but security is not a one-time thing. It is more like an ongoing process, a bit like keeping your house tidy; you have to keep at it, you know?
Regularly update your Raspberry Pi's operating system and all installed software. This includes running `sudo apt update && sudo apt upgrade` often. These updates often include important security patches that fix vulnerabilities, helping to prevent those "device is at risk" situations. It is probably the most straightforward way to stay safe, so.
Periodically review your SSH configurations on the Pi. Ensure password authentication remains disabled and that your SSH keys are still secure. If you ever suspect a private key might have been compromised, generate a new key pair and update your Pi immediately. This kind of vigilance can save you a lot of trouble, honestly.
Consider implementing additional security measures, like fail2ban, on your Raspberry Pi. Fail2ban automatically blocks IP addresses that show signs of malicious activity, like too many failed login attempts. This just adds another layer of defense against brute-force attacks, which is pretty clever, really.
For your Windows machine, keep your operating system updated, and make sure your SSH client (PuTTY or OpenSSH) is also the latest version. Just like the "missing important security and quality updates" warning, keeping your Windows system current helps protect your end of the secure connection. It is about making sure both ends of the connection are strong, you know?
Frequently Asked Questions
How do I securely access my Raspberry Pi from Windows?
You can securely access your Raspberry Pi from Windows using SSH (Secure Shell). This involves enabling SSH on your Raspberry Pi, then using an SSH client on your Windows computer, like PuTTY or the built-in OpenSSH client in PowerShell. For the best security, you should set up SSH key-based authentication instead of using passwords, you know?
What is P2P SSH and how does it help with IoT?
P2P SSH means establishing a direct, secure, encrypted connection between your Windows computer and your Raspberry Pi without relying on intermediate servers. This helps with IoT devices by providing a very secure way to manage and interact with them remotely. It reduces the risk of data interception and unauthorized access, making your IoT setup much safer, that is.
Why is my connection to a remote device untrusted?
A connection might be untrusted because the identity of the remote device cannot be verified, or the connection itself is not encrypted. When you connect to a Raspberry Pi, if you see an "untrusted" warning, it might mean the SSH host key is new or has changed, or that someone is trying to impersonate your Pi. Using SSH keys and verifying host keys helps establish trust, so.
Wrapping Things Up
Getting your remote IoT devices, especially your Raspberry Pi, to connect securely from your Windows computer does not have to be a source of worry. By using P2P SSH and following some good security practices, you can really make sure your connections are strong and trustworthy. We talked about why those "untrusted connection" warnings pop up and how keeping your systems updated helps a lot. It is almost like giving your devices a protective shield, so.
Setting up SSH keys, keeping your software current, and being mindful of network configurations are really important steps. This approach helps you avoid those frustrating moments where you cannot connect securely, or when your device feels at risk. You can learn more about secure network practices on our site, and for more specific details on setting up SSH keys, you might want to link to this page our SSH key guide. Making these small efforts means you can manage your remote IoT projects with a lot more confidence and peace of mind, you know?
- Tun Tun Tun Sahur
- Dress To Impress Creator Gigi
- How Long Is A Fortnight
- Lirik Heart Will Go On
- Lily Phillips 101 Challenge Video
Securely Connect RemoteIoT VPC Raspberry Pi: Free Download For Windows
Securely Connect Remote IoT VPC Raspberry Pi Download Windows Free

Securely Connect Remote IoT VPC Raspberry Pi: Free Download For Windows