Securely Connect Remote IoT Devices With P2P SSH On Ubuntu: A Practical Example For Today
Connecting to your remote Internet of Things (IoT) devices can feel a bit like trying to talk to someone across a very busy room, especially when you need to make sure your conversation is private. You want to send commands or get information from your little gadgets, but you also need to keep things safe from prying eyes. This is where learning to securely connect remote IoT devices with P2P SSH on Ubuntu becomes really useful, and it's something many folks are looking into as more and more things get connected, so it's a timely topic.
Think about it, you have these small computers or sensors out there, maybe in your garden, a workshop, or even a different building. Getting to them without opening up your entire network to the world can seem a little tricky. We often hear about "untrusted connections" or devices being "at risk" because they are not up to date, and that really highlights the need for better ways to manage these connections, you know?
This guide will show you how to set up a direct, private link using Peer-to-Peer (P2P) SSH, specifically on Ubuntu systems. We'll go through the steps for a practical example, making it easier for you to manage your remote IoT setup with a good feeling of safety. You'll learn how to get around common network hurdles and keep your data private, which is pretty important, as a matter of fact.
- Goob From Meet The Robinsons
- Twin Where Have You Been
- Kay And Tay Abuse Allegations
- How To Cook Scallops
- What Does Wap Mean
Table of Contents
- Why Secure IoT Connections Matter
- Getting Ready: Your Ubuntu Devices
- Setting Up SSH Keys for Strong Security
- Creating the P2P Connection with SSH Tunnels
- Accessing Your IoT Device Through the Tunnel
- Security Tips for Your IoT Setup
- Troubleshooting Common Issues
- Frequently Asked Questions
- Conclusion: Secure Remote IoT Connections
Why Secure IoT Connections Matter
In our increasingly connected world, having devices that talk to each other is pretty common. From smart home gadgets to industrial sensors, these IoT devices gather and send a lot of information. Ensuring that this information travels safely and that only authorized people can access your devices is, in a way, very important. You wouldn't want someone else messing with your settings or, you know, seeing your private data, would you?
The Challenge of Remote IoT Access
Accessing IoT devices that are not on your local network can be a bit of a headache. Most home or small office networks use something called NAT (Network Address Translation), which acts like a bouncer, letting traffic out but not easily letting outside traffic in unless you tell it exactly what to do. This means directly connecting to a device behind a router is often not straightforward, and that's a real thing people struggle with.
Opening up ports on your router, a process called port forwarding, can seem like an easy fix, but it comes with its own set of risks. It's like leaving a door open in your house; while convenient, it might invite unwanted visitors. For IoT devices, which might not always get regular security updates, this can be a serious concern, too it's almost a given that you need to be careful.
- Do Female Cats Spray
- Tun Tun Tun Sahur
- Nice And Slow Lyrics
- 4 Guard Buzz Cut
- How To Get Nail Glue Off Skin
Why P2P SSH is a Good Fit
P2P SSH, especially when using SSH tunnels, offers a much safer way to connect. Instead of opening a permanent door, you create a temporary, secure tunnel from your remote IoT device back to a trusted control station. This "reverse tunnel" approach means the connection is initiated from the IoT device, which usually has an easier time connecting out than accepting incoming connections. It's a bit like your IoT device calling you, rather than you trying to call it when it's behind a locked gate, which is a pretty neat trick, honestly.
SSH itself (Secure Shell) is a very reliable and widely used way to get command-line access to remote Linux systems. It encrypts all traffic, protecting your data from eavesdropping. When you combine this with a P2P approach, you get a direct, encrypted link that bypasses many common network hurdles without exposing your network unnecessarily. This is, you know, a very good thing for security.
Getting Ready: Your Ubuntu Devices
Before we jump into the setup, let's make sure both your control station (the computer you'll use to connect from) and your remote IoT device are ready. For this example, we'll assume both are running some version of Ubuntu, which is a popular choice for IoT projects due to its flexibility and community support, and that's usually a solid bet.
What You Will Need
- Two Ubuntu-based devices:
- **Control Station:** Your laptop or desktop, which will initiate the final connection. This device needs a public IP address or be accessible from the internet (e.g., a VPS or a home network with port forwarding for the SSH server). For most home users, a small, inexpensive cloud server (VPS) makes a good control station because it always has a public IP.
- **IoT Device:** Your remote IoT gadget (e.g., a Raspberry Pi running Ubuntu Server, an old NUC, etc.). This device will initiate the reverse tunnel connection.
- Basic command-line knowledge.
- Internet access for both devices.
- SSH client installed on your control station (usually pre-installed on Ubuntu).
- SSH server installed on both devices (OpenSSH server).
Initial Setup on Both Devices
First things first, let's make sure SSH is running and updated on both your control station and your IoT device. This is a pretty basic step, but it's essential, you know.
On both your **Control Station** and your **IoT Device**, open a terminal and run these commands:
sudo apt update sudo apt upgrade -y sudo apt install openssh-server -y The `sudo apt update` command refreshes the list of available software packages. `sudo apt upgrade -y` then installs any available updates, and the `-y` just means "yes" to all prompts, which is pretty convenient. Finally, `sudo apt install openssh-server -y` makes sure the SSH server software is on your system. After this, the SSH server should be running automatically. You can check its status with `sudo systemctl status ssh`, and it should say "active (running)", that's the goal.
Make sure you know the username and IP address of both your control station and your IoT device. For your IoT device, you'll need its *local* IP address for initial setup, and for your control station, you'll need its *public* IP address if it's a VPS. If your control station is at home, you'll need to set up port forwarding on your router for SSH (port 22) to point to your control station's local IP, which is something to consider, obviously.
Setting Up SSH Keys for Strong Security
Using SSH keys is much safer than relying on passwords alone. Keys are like very long, complex passwords that are nearly impossible to guess. You'll have a pair of keys: a private key (which stays secret on your control station) and a public key (which you place on your IoT device). When you try to connect, the two keys work together to prove your identity, which is, you know, a very secure way to do things.
Generating SSH Keys on Your Control Station
On your **Control Station**, open a terminal and run:
ssh-keygen -t rsa -b 4096 This command starts the key generation process. The `-t rsa` specifies the type of key, and `-b 4096` sets the key length, making it very strong. When it asks you where to save the key, just press Enter to accept the default location (`~/.ssh/id_rsa`). It will also ask for a passphrase. **It's highly recommended to set a strong passphrase for your private key.** This adds an extra layer of security, so if someone gets your private key, they still can't use it without the passphrase. Remember this passphrase, as you'll need it when you use your key, basically.
After generation, you'll have two files in your `~/.ssh/` directory: `id_rsa` (your private key) and `id_rsa.pub` (your public key). Keep `id_rsa` safe and never share it, that's a pretty important rule.
Copying the Public Key to Your IoT Device
Now, you need to get your public key onto your IoT device. The `ssh-copy-id` command makes this super easy. From your **Control Station**, run:
ssh-copy-id username@iot_device_ip Replace `username` with the actual username on your IoT device and `iot_device_ip` with its local IP address (or public IP if it has one and is directly accessible). You'll be asked for the IoT device's password for this one-time transfer. Once done, your public key is added to the `~/.ssh/authorized_keys` file on the IoT device, which is where SSH looks for trusted keys, so that's where it goes.
Testing the Basic SSH Connection
Before setting up tunnels, let's make sure you can connect to your IoT device using SSH keys. From your **Control Station**, try:
ssh username@iot_device_ip If you set a passphrase for your key, you'll be prompted for it. If everything worked, you should be logged into your IoT device's command line. This confirms your keys are set up correctly, and that's a good sign, naturally.
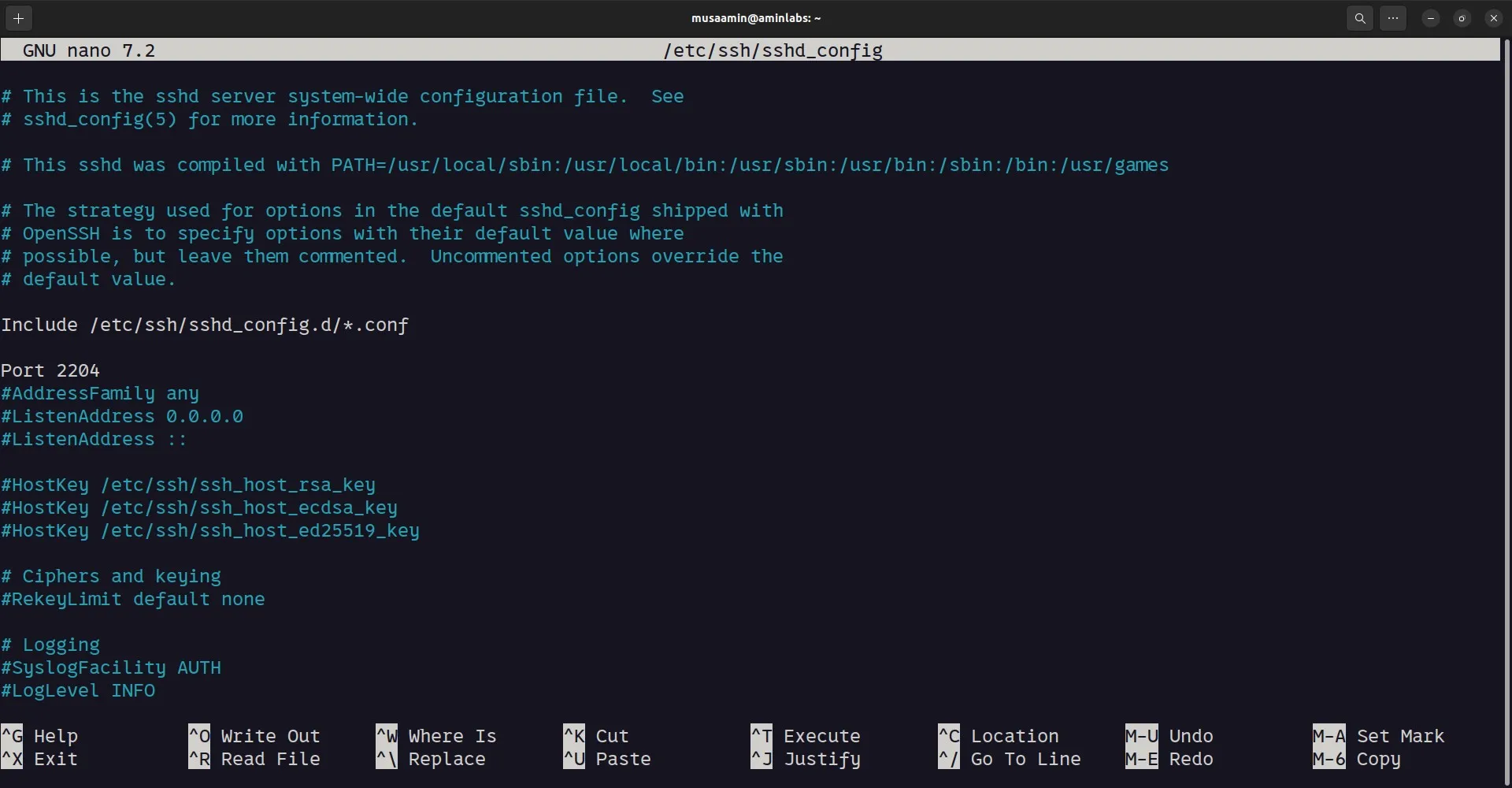
You might want to disable password authentication on your IoT device's SSH server for even better security. Edit the SSH server configuration file:
sudo nano /etc/ssh/sshd_config Find the line `PasswordAuthentication yes` and change it to `PasswordAuthentication no`. Also, find `PermitRootLogin` and make sure it's set to `no`. After making changes, restart the SSH service:
sudo systemctl restart ssh This means only users with SSH keys can log in, which is a much more secure setup, as a matter of fact.
Creating the P2P Connection with SSH Tunnels
This is where the "P2P" magic really happens. We'll set up a reverse SSH tunnel, allowing your IoT device to connect *out* to your control station, and then you can connect *in* to your IoT device *through* that established tunnel. This bypasses the need for complex port forwarding on the IoT device's network, which is a common hurdle, you know.
Understanding SSH Tunnels
An SSH tunnel creates a secure pathway between two machines over an SSH connection. A **reverse SSH tunnel** is special because the "server" for the tunnel (your control station) is the one that listens for connections, but the "client" (your IoT device) is the one that initiates the connection to create the tunnel. It's like your IoT device builds a secret, secure bridge back to your control station, and then you can walk across that bridge to get to your IoT device, which is a pretty clever way to do things.
Setting Up a Reverse SSH Tunnel
On your **IoT Device**, you will initiate the reverse tunnel. This command tells the IoT device to connect to your control station and create a tunnel:
ssh -N -R 2222:localhost:22 username@control_station_ip Let's break down this command:
- `ssh`: The SSH client.
- `-N`: This tells SSH not to execute a remote command. It's just for port forwarding.
- `-R 2222:localhost:22`: This is the crucial part for the reverse tunnel.
- `2222`: This is the port on your **Control Station** that will listen for connections. When you connect to `localhost:2222` on your control station, it will forward that traffic through the tunnel.
- `localhost:22`: This refers to the SSH server on the **IoT Device** itself. So, any traffic hitting `control_station_ip:2222` will be sent to `localhost:22` on the IoT device.
- `username@control_station_ip`: The username and public IP address of your **Control Station**.
When you run this command on your IoT device, it will prompt you for the passphrase for the SSH key that allows it to connect to your control station. Once entered, the tunnel is established, and the terminal will seem to hang, which is normal because it's keeping the connection open, so that's okay.
Keeping the Tunnel Alive
The tunnel created above will close if the SSH session ends. For a persistent connection, you'll want to run this command in the background and potentially have it restart if it drops. A simple way is to use `nohup` or a tool like `autossh`.
Using `nohup` (on your **IoT Device**):
nohup ssh -N -R 2222:localhost:22 username@control_station_ip & The `nohup` command ensures that the `ssh` process continues to run even if you close the terminal session on the IoT device. The `&` puts the command in the background. You'll still need to enter the passphrase, so this is better for manual setup or if you use an SSH agent. This is, you know, a pretty common way to keep things running.
For more robust persistence and automatic reconnection, `autossh` is a better tool. Install it on your **IoT Device**:
sudo apt install autossh -y Then, you can use `autossh` to manage your tunnel (on your **IoT Device**):
autossh -M 20000 -N -R 2222:localhost:22 username@control_station_ip -f Here's what's different:
- `-M 20000`: `autossh` uses port 20000 (and 20001) for monitoring the connection. Make sure these ports are not in use on your control station.
- `-f`: This tells `autossh` to go into the background before executing the SSH command.
`autossh` will automatically restart the SSH tunnel if it detects it has dropped, which is very helpful for remote devices that might have intermittent network access. You might want to set this up as a systemd service for truly automatic startup on boot, which is a bit more advanced but very good for long-term use, apparently.
Accessing Your IoT Device Through the Tunnel
Once the reverse tunnel is active from your IoT device to your control station, you can connect to your IoT device from your **Control Station** by simply connecting to a local port on your control station.
On your **Control Station**, open a new terminal and run:
ssh -p 2222 username@localhost Let's break this down:
- `ssh`: The SSH client.
- `-p 2222`: This tells SSH to connect to port 2222 instead of the default port 22. This is the port on your control station that the reverse tunnel is listening on.
- `username@localhost`: You're connecting to your own control station (localhost) using the username for your IoT device. The traffic will then be forwarded through the tunnel to the IoT device's SSH server.
You should now be logged into your remote IoT device, just as if it were directly accessible on your local network. This connection is fully encrypted and travels securely through the tunnel, which is, you know, exactly what we wanted to achieve. This is a pretty straightforward way to get to your device.
Security Tips for Your IoT Setup
While SSH tunnels provide a strong layer of security, keeping your overall IoT setup safe involves a few more steps. These are, you know, pretty important things to keep in mind.
- **Use Strong Passphrases for SSH Keys:** As mentioned, a passphrase adds a vital layer of protection to your private key.
- **Disable Password Authentication for SSH:** Once SSH keys are working, turn off password logins on both your control station (if it's a public-facing server) and your IoT device. This greatly reduces the risk of brute-force attacks, which are pretty common.
- **Keep Systems Updated:** Regularly run `sudo apt update && sudo apt upgrade -y` on both your control station and your IoT device. Software updates often include security patches, which are very important, as a matter of fact.
- **Use a Dedicated User for IoT Operations:** Instead of using the `root` user or your main user account for IoT tasks, create a separate, less privileged user on your IoT device. This limits potential damage if that account is ever compromised.
- **Firewall Rules:** Configure a firewall (like UFW on Ubuntu) on both your control station and your IoT device.
- On your **Control Station**: Allow incoming SSH connections only from trusted IPs if possible, or at least limit access to the SSH port (default 22, or 2222 if you changed it for the tunnel endpoint) to specific sources.
- On your **IoT Device**: Allow outgoing connections for SSH (port 22) to your control station's IP, and block all other unnecessary incoming connections.
- **Monitor Logs:** Regularly check SSH logs (`/var/log/auth.log`) on both devices for any unusual activity.
- **Physical Security:** If your IoT device is in an accessible location, consider its physical security. Someone with physical access can potentially bypass software security measures.
Troubleshooting Common Issues
Sometimes things don't go exactly as planned. Here are a few common problems you might run into and how to fix them, you know, just in case.
- **"Permission denied (publickey)."**
- **Check Key Permissions:** Your private key (`id_rsa`) on your control station must have very strict permissions: `chmod 400 ~/.ssh/id_rsa`.
- **Public Key on IoT Device:** Make sure your public key is correctly placed in `~/.ssh/authorized_keys` on the IoT device. Also, check permissions for the `.ssh` directory (`chmod 700 ~/.ssh`) and `authorized_keys` file (`chmod 600 ~/.ssh/authorized_keys`).
- **SSH Agent:** If you're using a passphrase and it keeps asking for it, consider using `ssh-agent` to manage your keys.
- **Tunnel drops frequently.**
- **Network Stability:** Check the internet connection on your IoT device. Intermittent connectivity will cause the tunnel to drop.
- **`autossh`:** Make sure `autossh` is running correctly on the IoT device and that its monitoring ports (e.g., 20000) are not blocked by a firewall.
- **Server Timeout:** The SSH server on your control station might be timing out idle connections. You can adjust `ClientAliveInterval` and `ClientAliveCountMax` in `/etc/ssh/sshd_config` on your **Control Station** to keep connections alive longer.
- **"Connection refused" when trying to connect to `localhost:2222` on control station.**
- **Is the Tunnel Active?** Check the IoT device to see if the reverse tunnel command is still running. If it exited, restart it.
- **Port Conflict:** Ensure port 2222 on your control station isn't already in use by another application. You can check with `sudo lsof -i :2222`. If it is, choose a different port for the tunnel.
- **Firewall on Control Station:** Make sure your control station's firewall isn't blocking connections to port 2222 from `localhost`.
- **Slow connection.**
- **Network Latency:** This could be due to the distance or quality of the internet connection between your IoT device and your control station.
- **Device Resources:** If your IoT device is very low-powered, it might struggle with the encryption overhead.
Frequently Asked Questions
Here are some common questions people often have
- B Cup Breast Size
- More Than A Married Couple
- The Voice Winner 2025
- Jasmine Crockett Husband
- Sophie Rain Spiderman Vid

Securely Connect Remote IoT P2P SSH Ubuntu Example: A Comprehensive Guide

How To Securely Connect Remote IoT P2P SSH Ubuntu
How to Change SSH Port in Ubuntu 24.04 • Linux & Open Source