Fixing Your Remote IoT To AWS VPC Connection: When Securely Connecting Isn't Working
It can feel pretty frustrating when you're trying to get your remote IoT devices to talk to your AWS Virtual Private Cloud, and, well, it's just not happening. You've set things up, you expect a smooth, secure pathway, yet the connection remains elusive. This situation, where you're aiming to securely connect remote IoT to your AWS VPC but it's just not working, is a common puzzle for many folks working with connected things. It's like trying to get a message to someone across a big, busy city, and the messenger keeps getting lost or stopped along the way. Your valuable device data needs to arrive safely, and when it doesn't, it really stops things cold.
You put in the effort to make sure everything is free from danger, like securely fastening a door or guarding an important office. You want that same kind of assurance for your IoT setup, knowing that everything is securely attached because anything that falls could cause a traffic accident below, and sudden weather can change everything. It's about making sure your data stream is steady, protected, and reliable. This piece will walk you through why these connections sometimes fail and, more importantly, what you can do to get them back on track, so you get that peace of mind.
This challenge often comes up because there are many parts that need to line up perfectly, from the device itself to the far reaches of your cloud setup. Just like trying to log into an account and finding your pin not working, or seeing a message that your connection is untrusted, these issues can stop you cold. We'll look at the usual suspects that cause these connection hiccups, and then we'll share some straightforward steps to help you sort things out, so your windows can run more securely, and your IoT system can too. It's about regaining control over your privacy and making sure sensitive information stays just that: sensitive.
- Whats Jon Gruden Doing Now
- Jon Gruden Past Teams Coached
- Sophie Rain Height In Feet
- How To See Deleted Sms
- Is A Fish An Animal
Table of Contents
- Understanding the "Securely Not Working" Puzzle
- Initial Checks: Laying the Groundwork
- Diving Deeper: AWS VPC and IoT Core Setup
- Troubleshooting Common Glitches
- Advanced Strategies for Strong Connections
- Frequently Asked Questions
- Wrapping Things Up
Understanding the "Securely Not Working" Puzzle
When you're dealing with remote IoT devices, getting them to securely connect to your AWS VPC can feel like a bit of a mystery, can't it? You've got these little devices out there, perhaps in a factory or on a farm, and they need to send their information back to a central brain in the cloud. When that secure connection isn't working, it's a real head-scratcher. It's a bit like when you try to connect securely to a website and your browser says, "This connection is untrusted." That's a sign something isn't quite right with how the trust is being established. We want to avoid that kind of message for our IoT devices, too, so they can send their information without any worries.
Why Security Matters So Much
Security isn't just a nice-to-have; it's absolutely vital, actually. For IoT, it means keeping your information free from danger, making sure it gets where it needs to go without anyone else seeing it or changing it. Think of it like securely guarding an office or keeping an important document securely tucked away so it cannot be lost or stolen. If your device information isn't securely attached, it could cause big problems, like traffic accidents below if something falls, or sudden weather changes ruining everything. Your device might be at risk because it's out of date and missing important security updates, so it's really important to keep everything current. That's why we put so much effort into making these connections solid.
Common Sticking Points
So, why does a secure connection to your remote IoT VPC in AWS sometimes just not work? There are many reasons, you know. It often comes down to a few usual suspects. Sometimes it's about how the device proves who it is, or maybe the network isn't set up quite right. It could be that the rules for what traffic is allowed are too strict, or perhaps not strict enough. These are the kinds of things that can stop your connection in its tracks, leaving you wondering why you've tried multiple platforms and still to no avail. It’s about finding that hidden option or way to get past the block, a bit like trying to password protect a file and not finding the option.
- Space City Home Network
- Kendrick Lamar Mustard Song
- How Long Is A Fortnight
- What Happened To Jessica Tarlov
- All You Can Eat Wings Buffalo Wild Wings
Initial Checks: Laying the Groundwork
Before you start digging into the deeper parts of AWS, it's often a good idea to check the very basics. Sometimes, the simplest things are the ones that cause the biggest headaches. It's like when you're trying to figure out why your internet isn't working, and it turns out the cable just came loose. These first steps are about making sure the foundation is solid before you build on it, so you're not wasting time on more complex issues when a simpler fix is available, basically.
Network Configuration Basics
Is your remote IoT device actually connected to the internet? That sounds silly, but it's a real first step. Check its local network settings. Is it getting an IP address? Can it reach other places on the internet, like a simple website? Sometimes, the device might be behind a local firewall that's blocking its outgoing connection attempts. You might need to open specific ports on that local network to allow the device to talk to the outside world. It's about making sure the door is securely fastened for outgoing messages, not just incoming ones, you see.
Device Credentials and Certificates
This is a big one, perhaps one of the biggest. For a secure connection, your IoT device needs to prove its identity, just like you select your identity provider when signing in with Google or Microsoft Azure AD. It typically does this using certificates. Is the device's certificate correctly installed? Is it still valid, or has it expired? Is the private key on the device matching the public key in the certificate? If there's any mismatch or issue here, the connection will be untrusted. It's like having an important document that's not quite right, and because of that, no one will accept it. This is really about making sure everything stays under your control, from securing passwords to files.
Diving Deeper: AWS VPC and IoT Core Setup
Once you've checked the basics on the device side, it's time to look closely at your AWS setup. This is where a lot of the magic happens, but also where many little things can go wrong. It's about making sure your cloud environment is ready to receive and process information from your remote devices securely. This part of the puzzle is where the AWS side of the connection comes into play, and it's quite detailed, you know.
VPC Endpoints: Are They Right?
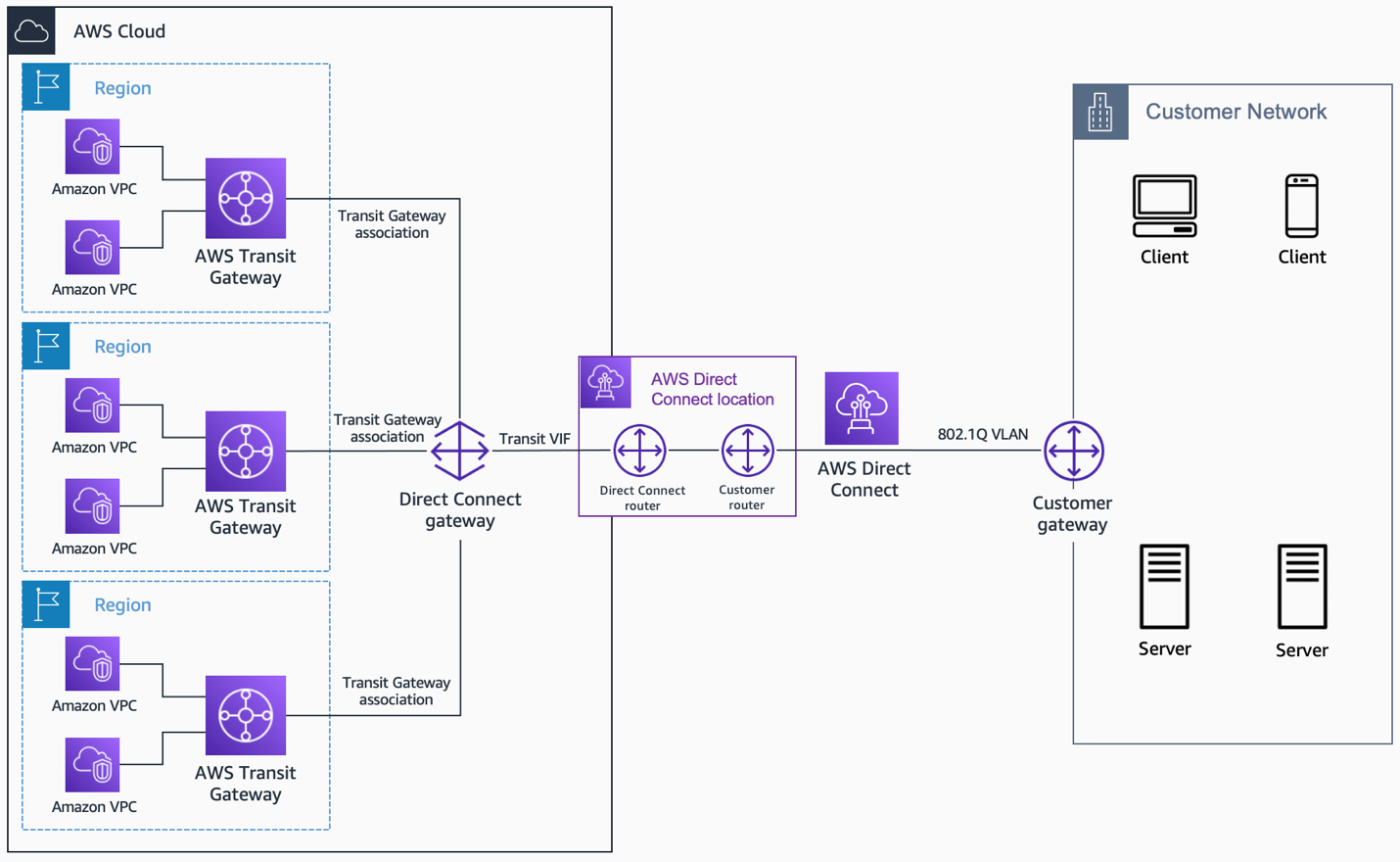
Many people want to connect their IoT devices directly to their VPC without going over the public internet. This is where VPC endpoints come in. Did you set up the correct type of VPC endpoint for AWS IoT Core? There are interface endpoints and gateway endpoints, and for IoT Core, you typically want an interface endpoint. Is the endpoint in the right subnets? Is it associated with the correct security groups? If the endpoint itself isn't set up correctly, the connection won't even have a place to land, so it's almost like building a road that leads nowhere.
Security Groups and Network ACLs: The Gatekeepers
These are your network's bouncers, deciding what traffic gets in and out. For your IoT connection to work, the security groups attached to your VPC endpoint, and potentially to your IoT Core resources, must allow incoming traffic from your IoT devices. This usually means allowing MQTT traffic (port 8883 for secure MQTT) from the IP addresses or ranges where your devices are located. Network Access Control Lists (NACLs) also need to permit this traffic. If these gatekeepers are too strict, they'll block your connection, and then you're stuck, as a matter of fact. It's like the offices were securely guarded, but they won't let your legitimate visitors in.
Routing Tables: Guiding the Traffic
Your VPC's routing tables tell network traffic where to go. If you're using a VPC endpoint, the routing table in the subnets where your endpoint resides needs to have a route for the IoT Core service. If your devices are coming in from outside AWS, you also need routes that direct their traffic into your VPC, perhaps through a VPN or Direct Connect gateway. Incorrect routing is like a map with wrong directions; your data just won't find its way home, anyway. It's about ensuring every bit of information knows exactly where it's supposed to go.
IoT Core Policies and Rules
Beyond network connectivity, AWS IoT Core has its own set of permissions. Each IoT device or "thing" needs an attached policy that grants it permission to connect, publish messages, and subscribe to topics. Are these policies specific enough but also broad enough to allow the necessary actions? Do they match the topics your device is trying to use? If the policy is too restrictive, even if the network connection is fine, IoT Core will reject the device's actions. This is like not having the right identity provider selected, so you can't sign in, even if your internet is working, you know.
Troubleshooting Common Glitches
When you've gone through the setup and something is still not working, it's time to put on your detective hat. Many common issues pop up again and again, and knowing what to look for can save you a lot of time and frustration. It's often about finding that one little thing that's out of place, kind of like when you're looking for a hidden option or way to do something. These are the usual suspects that trip up connections, so we'll cover them here.
Certificate Woes
Certificates are the digital handshake for secure connections. A common problem is an incorrect certificate on the device, or the certificate not being registered with AWS IoT Core. Make sure the certificate chain is complete on the device – that includes the device certificate, any intermediate certificates, and the root CA certificate from Amazon. Also, confirm the certificate is "ACTIVE" in your AWS IoT console. If your device is at risk because it's out of date and missing important security updates, its certificates might also be compromised or simply too old to be trusted. This connection is untrusted because we can't confirm your connection is secure, just like that Firefox message, so check those certificates thoroughly.
Policy Permissions
Even with a good certificate, if the AWS IoT policy attached to your device isn't right, it won't connect or publish. Double-check that the policy allows the `iot:Connect` action. Then, ensure it allows `iot:Publish` and `iot:Receive` on the specific MQTT topics your device uses. A common mistake is using a wildcard topic (`#` or `+`) in the policy but the device trying to publish to a more specific topic not covered, or vice-versa. It's like having the right key but the wrong door, you know. The policy needs to match the device's intended actions exactly.
Firewall Blocks
Both on the device side and within AWS, firewalls can block connections. On the device's local network, make sure outbound port 8883 (for MQTT over TLS) is open. Within AWS, check your VPC security groups and NACLs. Are they allowing inbound traffic on port 8883 from the IP addresses or CIDR blocks of your remote devices? Sometimes, a default "deny all" rule can silently block everything, so you have to explicitly allow the traffic. It's about ensuring that the offices were securely guarded, but they also have a clear path for authorized visitors, if you get what I mean.
DNS Resolution
Your IoT device needs to be able to find the AWS IoT Core endpoint by its hostname. This means DNS resolution must be working correctly. If your device is configured with a static IP for its DNS server, make sure that server can resolve AWS public hostnames. If you're using a VPC endpoint, ensure your VPC DNS settings are correct and that the endpoint's private DNS name is being resolved properly by your devices, especially if they are within the VPC or connected via VPN. A DNS problem is like trying to call someone but having the wrong phone number; the call just won't go through, you know.
Time Sync Issues
This one is a bit sneaky, but it's actually quite common. Secure connections that use TLS (which AWS IoT Core does) rely on accurate time synchronization between the client device and the server. If your IoT device's clock is significantly out of sync with real-world time, the TLS handshake will fail, and the connection will be rejected. This is because certificates have validity periods, and if the device's time is off, it might think the certificate is expired or not yet valid. Make sure your devices use Network Time Protocol (NTP) to keep their clocks accurate. It's like trying to get into a building when your ID says the wrong date; it just won't work, will it?
Advanced Strategies for Strong Connections
Once you've got the basics down and are troubleshooting the common glitches, there are also some more advanced ways to make your IoT connections even more robust and reliable. These are typically for situations where you need extra layers of security, local processing, or very stable network links. It's about building a system that's designed to address the unique challenges of modern learning, on any device, in any classroom, so it can handle more, basically.
Using AWS IoT Greengrass
For devices that need local processing or more consistent connectivity even when the internet is spotty, AWS IoT Greengrass is a powerful tool. Greengrass extends AWS cloud capabilities to edge devices, allowing them to run AWS Lambda functions, perform local data processing, and communicate with other devices locally. It can also manage secure connections to AWS IoT Core, buffering messages and sending them when connectivity is available. This can reduce the burden on individual devices to maintain constant cloud connections and provide a more resilient setup. It's like having a local branch office that handles a lot of the day-to-day work, only sending the important summaries to headquarters, you know.
VPN or Direct Connect for Remote Sites
For larger remote sites with many IoT devices, or where data privacy and network performance are paramount, establishing a VPN (Virtual Private Network) connection or an AWS Direct Connect link between your remote site and your AWS VPC can be a really good option. A VPN creates a secure tunnel over the public internet, while Direct Connect provides a dedicated private network connection. These methods ensure that all traffic from your remote devices to your VPC stays private and doesn't traverse the public internet, adding a significant layer of security and often improving reliability. It's like having a private, securely guarded road straight to your cloud, rather than sending everything through busy public streets, so you get peace of mind.
Monitoring and Logging
You can't fix what you can't see, right? Setting up robust monitoring and logging for your IoT devices and your AWS environment is absolutely vital. Use AWS CloudWatch Logs for IoT Core and VPC Flow Logs to see exactly what traffic is coming in and what's being rejected. CloudWatch metrics can show you connection attempts and failures. On the device side, make sure your IoT device logs its connection attempts, certificate errors, and any network issues. This information is like quickly accounting for students in an emergency; it helps you pinpoint exactly where the problem is occurring. This connection is untrusted because you can't confirm that your connection is secure, but logs help you figure out why, you see.
You can find more general information about securing IoT devices by checking out resources like the NIST IoT Security Guidelines, which can offer helpful insights for any system that needs to operate securely.
Frequently Asked Questions
Here are some common questions people ask when their remote IoT to AWS VPC connection isn't working:
How do I securely connect IoT devices to AWS VPC?
You typically use AWS IoT Core with VPC Endpoints. Your devices connect to the endpoint using MQTT over TLS, authenticating with X.509 certificates and policies. This setup creates a private path for your device data into your VPC, keeping it off the public internet. It's about setting up the right identity provider for your devices, so they can sign in with proper credentials.
What are common reasons for AWS IoT VPC connection failures?
Often, it comes down to incorrect device certificates, restrictive AWS IoT policies, misconfigured security groups or Network ACLs in your VPC, or issues with DNS resolution. Time synchronization problems on the device can also cause TLS handshakes to fail. It's like having a problem connecting securely to a website because something is untrusted; the reasons are often similar.
Can I connect remote IoT devices to a private VPC without a VPN?
Yes, you can use AWS IoT Core VPC Endpoints. These endpoints allow your devices to connect directly to your VPC using private IP addresses, even if the devices are remote, without needing a full VPN tunnel for each device. This is a very common way to achieve private connectivity for IoT. It helps you take full control over your privacy, keeping sensitive information within your private network, you know.
Wrapping Things Up
Getting your remote IoT devices to securely connect to your AWS VPC when things aren't working can feel like a real uphill climb, as a matter of fact. It involves checking many different pieces, from the tiny device itself to the big cloud infrastructure. But by systematically going through the network settings, device credentials, AWS VPC configurations, and troubleshooting common issues like certificate woes or policy permissions, you can usually pinpoint the problem. It's about understanding that a device at risk because it's out of date needs attention, just like an untrusted connection needs to be fixed. The goal is always to get you back on track so your system can run more securely, giving you that peace of mind, just like Securly classroom aims to do for learning environments.
Remember, the path to a smoothly running IoT system is often about making sure every piece is securely attached and properly identified. Whether it's making sure your device's identity provider is recognized or that the door is securely fastened for its data, every step matters. For more about keeping things safe and connected, you can learn more about secure connections on our site, and also find helpful information on troubleshooting network issues right here.
- Jasmine Crockett Husband
- Boo Did I Scare You Im A Job Application
- Shasha Prasad
- Goob From Meet The Robinsons
- Moth Grow A Garden
Securely Connect Remote IoT VPC AWS Not Working Windows: Comprehensive
Securely Connect Remote IoT VPC AWS Not Working Windows: A

Troubleshooting: Securely Connect Remote IoT VPC AWS Not Working On Windows