Remote Access For IoT Devices: An SSH AWS Example
Do you ever wonder how to check on your distant smart devices, maybe a sensor in a far-off location or a little computer doing important work somewhere else? Well, getting to these devices when you are not right next to them is a big deal for anyone working with connected things. It means you can fix problems, update software, or just see what's going on, all from your own comfortable spot. This kind of access is pretty much essential for keeping everything running smoothly in today's world of smart gadgets and systems, so it's a very practical thing to know about.
The internet of things, or IoT, is a huge network of physical items that have sensors and software built into them. These items can talk to each other and also send information to the cloud, as Lewis explains. Think about your smart home gadgets or even industrial machines; they are all part of this connected web. These devices collect information from their surroundings and then share it, which helps us monitor things digitally, you know, from afar.
Having a way to reach these gadgets remotely is a common need, especially as more and more things get connected. This article will show you how to set up remote access for an IoT device using SSH, which is a secure way to connect, with a little help from AWS. We will walk through an iot remote access ssh aws example, so you can see how it works in practice, and perhaps try it yourself.
- 6 Guard Buzz Cut
- Somber Smithing Stone 6
- What Does Yeet Mean
- Securely Connect Remote Iot Vpc Raspberry Pi Download Windows Free
- Blowout Taper Straight Hair
Table of Contents
- What is IoT Remote Access and Why Does it Matter?
- SSH: A Secure Way to Connect
- AWS for IoT Connections
- Getting Ready: Your IoT Device and AWS Setup
- The SSH AWS Example: Step-by-Step
- Keeping Things Safe: Best Practices
- Common Questions About IoT Remote Access
- Wrapping Things Up
What is IoT Remote Access and Why Does it Matter?
IoT remote access is simply the ability to reach and control your connected devices from somewhere else, not directly next to them. This could be from your home computer, a different office, or even your phone. It means you can check on a sensor in a factory or a smart thermostat in a vacation home without needing to be there in person, which is quite convenient, honestly.
Why is this so important, you might ask? Well, imagine you have hundreds or thousands of devices spread out over a large area, perhaps across different cities or even countries. If one of them has a problem, or if you need to update its programming, you can't just drive to each one. Remote access lets you handle these things efficiently, saving a lot of time and effort. It is that kind of thing that makes a big difference for many businesses and even for people at home.
Also, remote access helps with keeping things running smoothly. You can monitor how devices are doing, see if they are collecting data correctly, and even restart them if they get stuck. This continuous oversight helps prevent bigger issues from happening and keeps your IoT system working as it should, you know, all the time.
- Two Babies One Fox Comic
- Whispers Of Manifestation On Borlest
- Camarones A La Diabla
- The Voice Winner 2025
- Jamaican Restaurants Near Me
SSH: A Secure Way to Connect
SSH stands for Secure Shell. It is a way of connecting to a computer over an unsecured network, like the internet, but in a very safe manner. Think of it like sending a secret message in a locked box; only the person with the right key can open it and read what is inside. This makes it a really good choice for something like iot remote access ssh aws example setups.
When you use SSH, all the information you send back and forth is encrypted. This means that if someone tries to listen in, they will only see a jumble of unreadable characters, not your actual commands or data. This protection is super important, especially when you are dealing with devices that might be in public places or handling sensitive information. So, it's pretty much a standard for remote control.
Another nice thing about SSH is that it uses key pairs for authentication. Instead of just a password, you have two special digital keys: a public key and a private key. You put the public key on the device you want to connect to, and you keep the private key safe on your own computer. When you try to connect, these keys talk to each other to prove who you are, making it much harder for someone else to pretend to be you. This setup is, in a way, more secure than just using a password alone.
AWS for IoT Connections
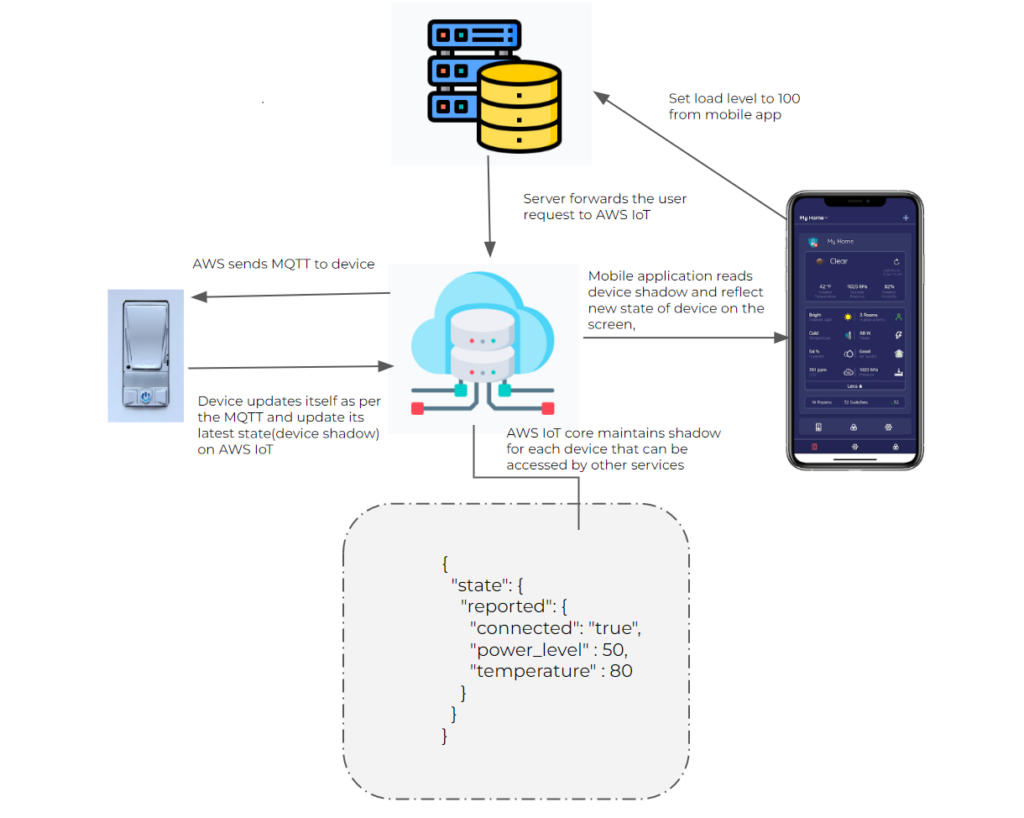
Amazon Web Services, or AWS, offers a wide range of services that are really helpful for IoT projects. For our iot remote access ssh aws example, we will look at a few of these. AWS IoT Core, for instance, is a service that lets billions of IoT devices connect to the cloud and talk to other AWS services without much trouble. It is like a central hub for all your smart gadgets.
AWS also provides compute services, like EC2 instances, which are virtual servers you can use in the cloud. These are quite useful because you can set them up to act as a kind of middleman or "jump host" for your IoT devices. This means your IoT device does not need to be directly exposed to the internet, which adds an extra layer of protection. It is a bit like having a guarded entrance to your device, which is rather clever.
Using AWS for your IoT setup also means you get the benefit of its big infrastructure and security features. AWS has many tools to help you manage your devices, keep them secure, and scale your operations as you add more and more gadgets. This makes it a very strong platform for building and managing IoT systems, so it's a popular choice for many folks.
Getting Ready: Your IoT Device and AWS Setup
Before we can connect remotely, we need to make sure our IoT device and our AWS environment are prepared. This involves a few steps to get everything in order. It is a bit like getting all your ingredients ready before you start cooking, you know, so everything goes smoothly.
Preparing Your IoT Device
First, your IoT device needs to be ready for SSH connections. This typically means it is running a Linux-based operating system, like a Raspberry Pi, for example. You will want to make sure SSH is enabled on the device itself. For many small computers, this is a setting you can turn on, or a piece of software you can install, which is pretty straightforward.
You will also need to make sure your device has internet access. It needs to be able to reach AWS and receive commands. This might involve setting up Wi-Fi or an Ethernet connection. Having a stable network connection is, of course, very important for any remote work, so you want to check that first. You will also need to know your device's local IP address for some of the initial setup, too it's almost a given.
It is a good idea to update your device's software to the latest version. This helps with security and makes sure everything works as it should. Keeping your device up-to-date is a basic step that helps prevent problems down the line. This preparation makes sure your device is ready for the next steps in our iot remote access ssh aws example, so you can connect with confidence.
Setting Up AWS IoT Core
Next, we will set up some things in AWS. While we are using SSH directly, AWS IoT Core can still be helpful for managing device identities and certificates. You will typically register your IoT device as a "thing" in AWS IoT Core. This gives it a unique identity within your AWS account, which is quite handy.
You will also create a certificate and policy for your device in AWS IoT Core. The certificate helps your device prove who it is when it talks to AWS, and the policy defines what actions it is allowed to perform. Even if we are using SSH for remote access, having this identity helps with overall device management and security within the AWS ecosystem, you know, for a complete picture.
This setup in AWS IoT Core is a foundational step for many IoT projects. It helps keep track of your devices and gives you a way to manage their permissions. For our iot remote access ssh aws example, it provides a solid base, even if the direct SSH connection does not always go through IoT Core itself. It is a good practice to follow, anyway.
The SSH AWS Example: Step-by-Step
Now, let us get into the practical steps for setting up remote access. This part of our iot remote access ssh aws example shows you how to connect to your device securely using SSH, with AWS as part of the picture. We will use a "jump host" method, which is a common and secure way to do this, as a matter of fact.
Creating an EC2 Instance as a Jump Host
A jump host is like a secure stepping stone. Instead of connecting directly to your IoT device, you first connect to a small, secure server in AWS, called an EC2 instance. From there, you then connect to your IoT device. This adds a layer of protection because your IoT device does not need to be directly exposed to the public internet, which is a very good thing for security.
To set this up, you will launch a small EC2 instance in your AWS account. Choose a basic Linux image, like Amazon Linux 2 or Ubuntu. When you create it, you will also create a key pair. This key pair is what you will use to connect to the EC2 instance itself. Make sure to download the private key file and keep it safe on your computer, as you will need it later, obviously.
This EC2 instance will act as our secure gateway. It is a simple setup, but it makes a big difference in how secure your remote access is. It is a pretty common strategy for those who need to manage many devices, you know, without putting them all out in the open. This jump host is a key part of our iot remote access ssh aws example setup.
Configuring SSH on Your IoT Device
Your IoT device needs to be set up to accept SSH connections from your jump host. This means making sure the SSH server software is running on your device. Most Linux-based IoT devices, like a Raspberry Pi, come with this capability, or you can install it easily. You will also need to generate an SSH key pair on your IoT device itself, which is a separate set of keys from the one you used for the EC2 instance.
Once you have generated the key pair on your IoT device, you will take the public key from that pair and add it to the `authorized_keys` file on your IoT device. This file tells the SSH server which public keys are allowed to connect. You will then take the private key from this pair and put it on your EC2 jump host. This way, the jump host can use that private key to connect to your IoT device, which is a bit of a dance, but it works.
This setup ensures that only your jump host, with the correct private key, can initiate an SSH connection to your IoT device. It is a very specific way of granting access, which helps keep things locked down. This step is pretty important for the security of your iot remote access ssh aws example, so you want to get it right.
Setting Up Security Groups and Network Rules
Security groups in AWS are like virtual firewalls that control what network traffic can reach your EC2 instances. For your EC2 jump host, you will need to set up a security group that allows incoming SSH traffic (on port 22) from your own IP address. This means only you, from your specific location, can connect to the jump host, which is a good safety measure, really.
For your IoT device, you will need to ensure it can be reached by the EC2 jump host. If your IoT device is also in AWS (perhaps in a private subnet), you would configure its security group to allow SSH traffic from the security group of your EC2 jump host. If your IoT device is outside of AWS, you would need to make sure your network allows the jump host to connect to it, perhaps through a VPN or a direct connect, or by allowing traffic from the jump host's public IP, which is less ideal but sometimes necessary, you know, depending on your setup.
These network rules are vital for keeping your system safe. They make sure that only authorized connections can happen. Getting these security groups and network settings right is a very big part of a secure iot remote access ssh aws example, so pay close attention to them.
Connecting Through the Jump Host
With everything set up, you can now connect to your IoT device. First, you will SSH into your EC2 jump host from your local computer. You will use the private key you downloaded when you created the EC2 instance. The command will look something like `ssh -i /path/to/your/ec2-key.pem ec2-user@your-ec2-public-ip`, which is pretty standard.
Once you are logged into the EC2 jump host, you will then SSH from the jump host to your IoT device. Remember, you put the private key for your IoT device on the jump host. So, the command on the jump host will be something like `ssh -i /path/to/your/iot-device-key.pem iot-user@your-iot-device-ip`. This two-step connection is what makes the jump host method so secure, actually.
You can also set up your local SSH configuration file (often `~/.ssh/config`) to make this a single command from your local machine, using SSH's `ProxyJump` feature. This makes the whole process feel much smoother, even though it is still doing the two steps in the background. It is a very neat trick for frequent access, you know, to save time.
Keeping Things Safe: Best Practices
Security is a very big concern when it comes to remote access for IoT devices. There are a few things you should always do to keep your setup safe. Following these tips will help protect your devices and your data from unwanted access, which is something you really want to avoid.
Use Strong Passwords and Keys: If you use passwords, make them long and complex. For SSH keys, always use strong, unique key pairs. Never share your private keys with anyone. Keeping your keys safe is like protecting the keys to your house, so it is pretty important.
Limit Access: Only allow SSH connections from specific IP addresses that you trust, like your office or home network. This is done through security groups in AWS. Do not leave your devices open to the whole internet, as that is asking for trouble, you know.
Regularly Update Software: Keep your IoT device's operating system and all its software up-to-date. Software updates often include security fixes that patch vulnerabilities. This is a basic but very effective way to stay safe, as a matter of fact.
Monitor Activity: Keep an eye on the logs of your IoT devices and your EC2 jump host. Look for any unusual login attempts or strange activity. Catching problems early can prevent bigger issues later, which is something you should always do.
Use a Jump Host: As we showed in our iot remote access ssh aws example, using a jump host adds a significant layer of security. It means your IoT device does not have to face the internet directly, which is a very good thing.
Least Privilege Principle: Give your IoT devices and users only the permissions they absolutely need, and no more. If a device only needs to send data, do not give it permission to delete things. This limits the damage if something goes wrong, you know, just in case.
Consider VPNs: For even more security, you might consider setting up a Virtual Private Network (VPN) between your network and your IoT devices. A VPN creates a secure, encrypted tunnel for all your traffic, which is another great way to keep things private.
Backup Your Data: Make sure you regularly back up any important data from your IoT devices. If something does go wrong, you will have a copy of your information, which is a very sensible thing to do.
These practices help build a strong defense for your IoT setup. Security is an ongoing process, not a one-time task, so you should always be thinking about it, honestly.
Common Questions About IoT Remote Access
People often have questions when they are thinking about how to get to their IoT devices from afar. Here are some common ones that come up, especially when talking about things like an iot remote access ssh aws example.
Can I use a VPN instead of a jump host for IoT remote access?
Yes, you can use a VPN for IoT remote access, and it is a very good option for security. A VPN creates a secure, encrypted tunnel between your network and your IoT devices. This means all the traffic between them is protected. It can be a simpler setup for some, especially if you have many devices in one location. A jump host is still a great choice, particularly if you need to access devices spread across different networks or if you want a very specific control point, you know, for certain situations.
What if my IoT device doesn't have a public IP address?
Most IoT devices do not have a public IP address, and that is actually a good thing for security. They are usually on a private network behind a router. This is where methods like using a jump host or a VPN become very useful. Your IoT device connects outbound to the jump host or VPN server, and then you connect to that server. This way, your device does not need to be directly exposed to the internet, which is much safer, honestly. It is a common setup for many connected gadgets, as a matter of fact.
Are there other ways to get remote access besides SSH?
Yes, there are other ways to get remote access to IoT devices. Some devices might have web interfaces you can access, or they might use specific protocols for remote management. AWS IoT also offers services like AWS IoT Device Shadow or AWS IoT Jobs that let you send commands and manage devices without a direct SSH connection. These are often used for things like updating software or changing settings on many devices at once. SSH is very popular for direct command-line access, which is often what people need for detailed troubleshooting, you know, for a more hands-on approach.
Wrapping Things Up
Setting up remote access for your IoT devices using SSH and AWS gives you a lot of control and peace of mind. It means you can manage your connected gadgets from anywhere, keeping them running smoothly and securely. We have walked through an iot remote access ssh aws example, showing you the steps involved in getting a jump host ready and configuring your devices for secure connections. This kind of setup is really important for anyone working with IoT, as it allows for flexible and safe management.
Remember that keeping your remote access secure is an ongoing effort. Regularly updating your devices, using strong security practices, and monitoring your connections are all very important steps. By taking these precautions, you can be confident that your IoT system is protected and accessible when you need it. You can learn more about IoT security practices on our site, and perhaps even link to this page for more detailed AWS IoT guides, so you can keep learning and building.
- Taper Fade Black Men
- 405 Howard Street San Francisco
- Caitlin Clark Rookie Card
- Drew Pritchard Divorce
- Whats Jon Gruden Doing Now

IoT SSH Remote Access - SocketXP Documentation
Understanding AWS IoT With An Example - Home Automation - Beyond App

Remote Monitoring of IoT Devices | Implementations | AWS Solutions