RemoteIoT SSH AWS Example: Connecting Your Devices Safely
Have you ever thought about how devices out in the world, far from your office, stay connected and safe? Maybe you have heard about remote IoT setups, AWS, and SSH connections. It can seem like a puzzle to put it all together, but actually, it's a very practical way to keep things running smoothly. This way of doing things helps you reach your internet-connected gadgets no matter where they are, keeping them secure.
Picture this: you have a tiny computer, like a Raspberry Pi, sitting in a remote location. It might be checking the weather or managing some machinery. How do you get to it if it is behind a strict firewall? How do you give it new instructions or fix something if it goes wrong? This is where the idea of a remote IoT SSH AWS example truly shines, offering a way to talk to these devices without physical presence. It's about making your computer talk safe and secure when dealing with those remote gadgets, you know?
This article will go into how a remoteIoT SSH AWS example works. We will look at why it is so helpful for managing devices that are out of reach. We will also see how different parts of AWS, like IoT Core and EC2, play a part. By the end, you will have a clearer picture of how to set up such a system, ensuring your IoT things are both accessible and protected, more or less.
- How To See Deleted Sms
- A Court Of Shaded Truths
- How Do I Say Goodbye Lyrics
- Business Class Vs First Class
- Kay And Tay Abuse Allegations
Table of Contents
- What is RemoteIoT SSH AWS Example?
- Why Secure Remote Access is So Important
- Key AWS Services for IoT Connectivity
- Setting Up Your Secure Connection: A Conceptual Guide
- Benefits of This Approach
- Frequently Asked Questions about RemoteIoT SSH AWS Example
What is RemoteIoT SSH AWS Example?
A remoteIoT SSH AWS example is, in a way, a blueprint. It helps folks set up a safe communication path between internet-connected gadgets and Amazon Web Services servers. It is a powerful method to look after and protect your IoT devices using AWS services. Whether you are just starting or have lots of experience, this setup offers a clear path.
Think of it like this: you have a device far away, perhaps a sensor in a field or a smart home gadget. You need to talk to it, maybe to get data or send it new instructions. SSH, which stands for Secure Shell, is a method for secure communication. AWS, which is Amazon Web Services, provides the tools and space in the cloud for all this to happen. So, you know, it's about making a secure tunnel from your computer to that far-off device, using AWS as the bridge.
The phrase "remoteiot vpc ssh raspberry pi aws example" might sound like a lot of words, but it is simpler than you might think. It really means creating a protected link between your Raspberry Pi, or any IoT device, and a virtual network in AWS. This allows you to manage and interact with your devices as if they were right next to you, which is very useful for operations that span wide areas.
- Caitlin Clark Rookie Card
- Jon Gruden Past Teams Coached
- Yes Yes Yes Meme
- B Cup Breast Size
- Filmy Fly Com
Essentially, this approach lets you reach any remote device on any cloud service. You can even get a Visual Studio Code instance going with no fuss at all. This kind of setup can be used to run a configuration management tool or to get a group of devices ready for action, which is pretty neat.
Why Secure Remote Access is So Important
The need for secure ways to reach devices that are not close by is growing. As more and more gadgets connect to the internet, keeping them safe from unwanted access becomes a big deal. A remoteIoT SSH AWS example tackles this head-on. It gives you peace of mind that your data and devices are guarded, more or less.
When devices are placed behind strict firewalls at far-off places, you absolutely need a way to get to them. This is true for checking on them, making updates, or fixing problems. Without a secure path, these devices can become isolated, or worse, vulnerable to threats. That is why a well-thought-out remote access plan is so important for any IoT project.
It is not just about getting access, though. It is also about making sure that access is safe. Just like with yeast leavening, the presence of certain elements changes things. In this case, the presence of strong security measures changes the game for IoT. You want to make sure only authorized people can talk to your devices, and that the conversation itself cannot be listened to by others. This is a big part of why this particular setup is so valued.
Devices Behind Restricted Firewalls
Imagine your IoT devices are like little outposts, each behind its own protective wall, a firewall. These walls are there for a good reason, to stop bad things from getting in. But, you know, they also stop you from getting in easily when you need to. This is a common situation for devices in factories, retail stores, or even smart homes. They are often on private networks with strict rules about who can connect from the outside.
This is where the remoteIoT SSH AWS example truly helps. It provides a clever way to bypass these restrictions safely. Instead of trying to open up holes in every firewall, you use AWS as a central, secure meeting point. Your devices can talk out to AWS, and you can talk into AWS, and then AWS helps them talk to each other. It is a bit like having a secure post office box in the cloud that both you and your device can use, which is very handy.
This method means you do not have to mess with complicated network setups at each remote spot. You do not need to ask network administrators to open specific ports, which can be a security risk anyway. Instead, your devices simply connect out to AWS, which is usually allowed by firewalls. This simplifies things quite a lot, actually.
Keeping Your IoT Network Safe
Security is a huge concern for anything connected to the internet. An insecure IoT setup can be a weak spot for a whole network. This is why making sure your remote IoT connections are solid is so important. The remoteIoT SSH AWS example focuses heavily on this, building security right into the way it works.
Using SSH means that all communication between your computer and the remote device is encrypted. This is like putting your messages in a secret code that only the sender and receiver can read. It stops anyone trying to snoop on your connection from understanding what you are doing or sending. This is a fundamental layer of protection, which is quite reassuring.
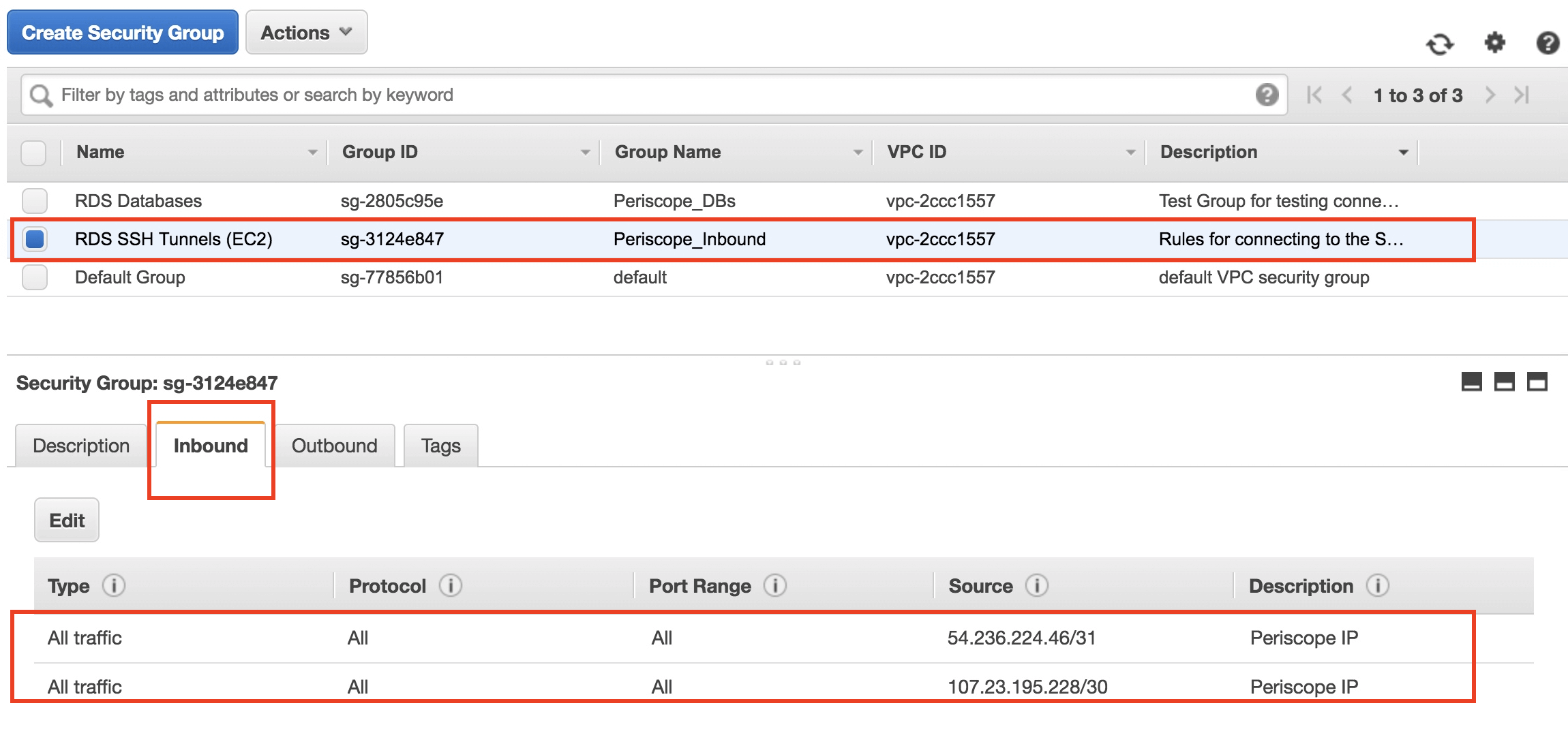
Also, AWS provides many tools to control who can access what. You can set up very specific rules, like only allowing certain users to connect to certain devices at certain times. This is called "least privilege," and it is a very good security practice. It means if someone's access is ever compromised, the damage they can do is limited. This is a key part of keeping your entire IoT network safe and sound, you know?
Key AWS Services for IoT Connectivity
If you are hoping to set up a secure, growing, and dependable IoT environment, AWS offers some pretty useful tools. But setting up a virtual private cloud and connecting everything can seem like a lot. The remoteIoT SSH AWS example relies on several key AWS services working together. Each one plays a distinct part in making the whole system function smoothly and safely.
These services help establish secure communication channels for different organizations. They let you manage your devices, set up private networks, run virtual computers, and even trigger code without having to manage servers. Knowing what each service does helps you see the bigger picture of how this remote access system comes together, you know, sort of like fitting puzzle pieces.
AWS IoT Core
AWS IoT Core is the central hub for connecting your IoT devices to the AWS cloud. It is designed to let billions of devices and trillions of messages connect easily and securely. Think of it as the main meeting place where all your devices report in and get their instructions. It handles the difficult work of making sure messages get from your devices to other AWS services and back again.
IoT Core also manages device identities and authenticates them, making sure only trusted devices can connect. It has rules that decide what messages go where, and it can even keep track of the state of your devices. This means you can know if a device is online or offline, and what its last reported status was, which is quite helpful for managing a large number of devices. It is a very robust service for managing device communication, you see.
For a remoteIoT SSH AWS example, IoT Core can be used to trigger actions when a device needs attention. For instance, a device could send a message to IoT Core saying it needs a software update. IoT Core could then, in turn, trigger another AWS service to make that update happen, without you having to manually connect to the device. It is a fundamental part of a responsive IoT setup, too it's almost.
Amazon VPC (Virtual Private Cloud)
An Amazon VPC is like having your own private, isolated section of the AWS cloud. It is a virtual network where you can launch AWS resources in a way that is separate from other AWS customers. This gives you complete control over your virtual networking environment, including your IP address ranges, subnets, route tables, and network gateways. It is your own secure space, basically.
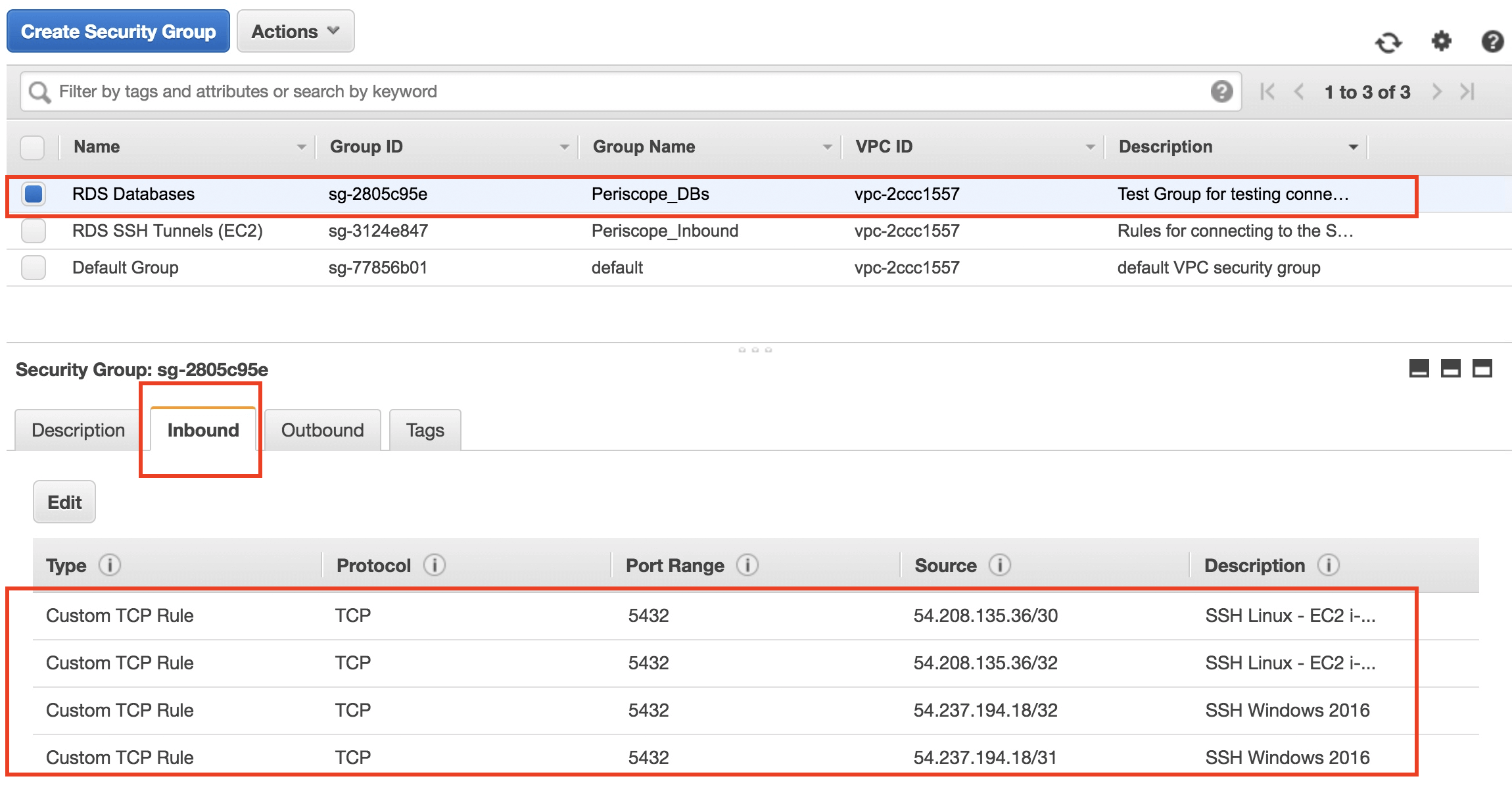
For a remoteIoT SSH AWS example, a VPC is super important for security. It means your IoT devices, or the servers that manage them, can exist within a private network that you control. You can set up strict rules about what traffic can come in and out of this network. This helps create a very protected environment for your sensitive IoT data and operations, which is quite reassuring.
The phrase "remoteiot vpc ssh raspberry pi aws example" highlights the VPC's importance. It is all about creating a secure connection between your Raspberry Pi and an AWS virtual private cloud. This ensures that when your Raspberry Pi communicates, it does so within a controlled and isolated network space, reducing the chances of unauthorized access. It is a foundational element for secure remote operations, in some respects.
Amazon EC2 (Elastic Compute Cloud)
Amazon EC2 provides resizable computing capacity in the cloud. It is like having virtual computers that you can create and use whenever you need them. You can pick the size, operating system, and software you want on these virtual machines. They are very flexible and can be started or stopped as needed, which is pretty efficient.
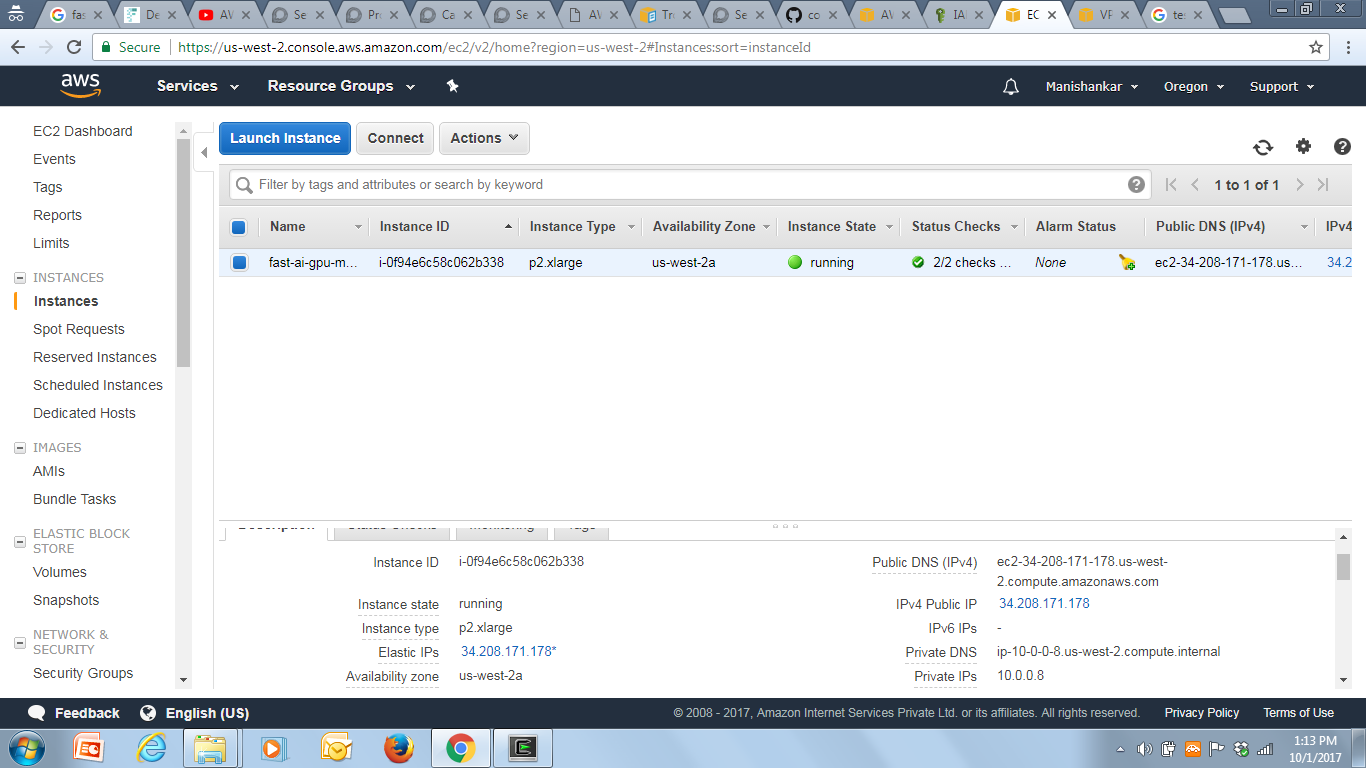
In a remoteIoT SSH AWS example, an EC2 instance often acts as a jump box or a central management server. This is a secure server within your VPC that you can SSH into. From this EC2 instance, you can then securely connect to your remote IoT devices. It acts as a secure intermediary, a kind of staging post for your remote access, you know?
Learning how to set up remote development on an AWS EC2 instance using Visual Studio Code and SSH is a common use case. This guide provides detailed steps to connect via SSH and start coding remotely. This means you can work on your IoT device's software from anywhere, using a powerful cloud-based development environment, which is quite convenient, actually.
AWS Lambda
AWS Lambda is a service that lets you run code without needing to manage servers. You just upload your code, and Lambda takes care of everything needed to run and scale it. It is often called "serverless computing" because you do not have to worry about the underlying infrastructure. It is very efficient for tasks that only need to run sometimes, or in response to an event.
For a remoteIoT SSH AWS example, Lambda can be used to automate parts of your remote access process. For instance, if an IoT device reports a certain status through IoT Core, a Lambda function could be triggered. This function could then, perhaps, automatically open an SSH tunnel for a short time, or send you an alert, or even restart a service on the remote device. It adds a layer of automation that can make managing many devices much simpler, very, very simple.
By using AWS services such as IoT Core, AWS Lambda, and Amazon EC2, organizations can set up secure communication channels for their devices. Lambda helps stitch these services together, allowing for event-driven actions that make your remote IoT setup more dynamic and responsive. It is a powerful tool for adding intelligence and automation to your system, in a way.
Setting Up Your Secure Connection: A Conceptual Guide
Setting up a remoteIoT VPC SSH Raspberry Pi AWS example is a powerful way to make your IoT infrastructure better. It helps ensure safe communication between devices. This process involves a few steps that link your physical device to the cloud and then allow you to reach it securely. It is not just about connecting; it is about connecting with confidence, you know?
The secret lies in a clever combination of chemical reactions, carefully balanced to create the perfect rise. Oh, wait, that's for baking powder! My apologies! For IoT, the secret lies in a clever combination of network configurations and security protocols, carefully balanced to create the perfect remote access. It is a bit like setting up a secure pathway that only you and your devices can use. This post will go into the scientific principles that govern baking powder’s performance, exploring its composition, activation mechanisms, and the factors that influence. No, no, again, my apologies! This post will go into the technical principles that govern secure remote access, exploring its components, connection mechanisms, and the factors that influence its safety. It is a truly fascinating area, arguably.
To be effective, all remote IoT setups rely on secure connections to produce reliable data and control. Just as with yeast leavening, the presence of proper conditions is key. Here, the proper conditions mean strong encryption and controlled access. Understanding the science behind remote access, including its connection mechanism and components, is important for managing devices successfully. By mastering the role of network settings, security keys, and cloud services, you can achieve great things, you know?
The Role of SSH in Remote Access
SSH, or Secure Shell, is the backbone of this remote access strategy. It provides a secure channel over an unsecured network by using strong encryption. When you use SSH, your data is scrambled before it leaves your computer and unscrambled only when it reaches the correct destination. This makes it very difficult for anyone to intercept and read your communications, which is pretty good.
To use SSH, you typically use SSH keys. These are like a very secure username and password, but much longer and more complex. You have a public key that you put on the remote device, and a private key that stays on your computer. When you try to connect, the two keys "talk" to each other to confirm your identity. If they match, you get access. If not, you are denied. This system is much safer than using simple passwords, which can be guessed, you know?
The process often involves setting up an SSH tunnel. This is a way to route other network traffic securely through an SSH connection. For instance, you might use an SSH tunnel to securely access a web interface on your Raspberry Pi that is not directly exposed to the internet. It is like creating a secret, protected passageway through a busy public space, which is rather clever.
Connecting Your Raspberry Pi
The Raspberry Pi is a very popular device for IoT projects. It is small, affordable, and powerful enough for many tasks. Connecting a Raspberry Pi in a remoteIoT SSH AWS example involves a few steps. First, your Raspberry Pi needs to be able to connect to the internet and communicate with AWS IoT Core, which it usually does over standard internet connections, you know?
You would configure your Raspberry Pi to register with AWS IoT Core. This involves installing the necessary software and providing it with credentials so IoT Core knows it is a legitimate device. Once registered, the Raspberry Pi can send messages to IoT Core and receive commands from it. This sets the stage for remote management, basically.
Then, to allow SSH access, you would typically set up a secure proxy or a VPN connection through your AWS VPC. The Raspberry Pi might initiate a connection outwards to an EC2 instance in your VPC, or use a service like AWS IoT Device Shadow to maintain its state and receive instructions. This way, you do not need to open inbound ports on the Raspberry Pi's local network, which is a big security plus, you know?
The connection setup is all about creating a secure connection between your Raspberry Pi and an AWS virtual private cloud. This might involve using a service like AWS IoT Secure Tunneling, which creates an on-demand, secure tunnel to a device without needing to open inbound ports on the device's network. It is a very effective way to get to your devices safely, apparently.
Getting VSCode Up and Running Remotely
One of the really cool things about this setup is the ability to do remote development. This basically means you can SSH into any remote instance on any cloud service and get a VSCode instance up and running with absolutely no fuss. This is incredibly useful for developers working on IoT projects, as it lets them code as if they were directly on the device, even when it is miles away.
Visual Studio Code has extensions that allow you to connect to a remote SSH host. Once connected, VSCode runs its backend on the remote machine (like your EC2 instance or even directly on your Raspberry Pi if it has enough resources). Your local VSCode then acts as a lightweight client, giving you a full development experience. You can browse files, edit code, run terminals, and debug, all remotely, which is very, very handy.
This capability means you do not need a powerful computer at the remote site. The heavy lifting of compiling code or running tests can happen on the EC2 instance in the cloud. You just need your local machine to run the VSCode interface. This makes development much more flexible and efficient, allowing you to work from anywhere with an internet connection. It is a real game-changer for remote teams, you know?
Benefits of This Approach
The remoteIoT SSH AWS example brings a lot of good things to the table for anyone dealing with IoT devices. It is more than just a mouthful; it really helps make things better. One big benefit is the improved security. By using SSH and AWS services, you are building a system that is designed to be tough against unwanted access. All your communications are encrypted, and you have fine-grained control over who can connect to what, which is pretty important.
Another great thing is the scalability. AWS is built to handle huge numbers of devices and massive amounts of data
- In The Clerb We All Fam
- Who Won The Voice 2025
- Mikafans Leaks
- How To Say I Love You In French
- Timothee Chalamet Net Worth
AWS SSH Security Group Configuration | Sisense for Cloud Data Teams
AWS SSH Security Group Configuration | Sisense for Cloud Data Teams
SSH into your AWS instance? - Part 1 (2017) - fast.ai Course Forums