Securely Connect Remote IoT P2P Raspberry Pi: Free Download Guide
Ever wondered how you can securely connect remote IoT devices using P2P technology for free on a Raspberry Pi? Well, you're in the right place, that is. This guide will walk you through the process of securely connecting your Raspberry Pi in a remote IoT P2P environment, complete with a free download option for essential software. We're going to talk about how you can securely connect remote IoT devices, specifically your Raspberry Pi, making sure these connections are not just working, but truly safe.
Connecting devices over long distances can seem a bit tricky, especially when you think about keeping them safe from unwanted access. Yet, for many home projects or small-scale industrial needs, having your devices talk to each other without a central server can be very helpful. This peer-to-peer (P2P) way of connecting offers a direct link, which can be faster and, in some ways, more private, actually.
This article will serve as your comprehensive guide, walking you through every step required to securely connect your Raspberry Pi in a remote IoT P2P environment. We'll delve into the importance of secure IoT connections, explore the potential of P2P technology, and provide a comprehensive guide on how to set up a secure system. By the end of this guide, you’ll know everything you need to set up a secure remote IoT P2P connection using a Raspberry Pi, all for free, so.
- More Than A Married Couple
- What Does Yeet Mean
- Dubai Strawberry Cup Near Me
- Surrealism Dress To Impress
- Sophie Rain Spiderman Vid
Table of Contents
- Why Secure IoT Connections Matter
- The Risks of Open Connections
- The Promise of P2P
- Your Raspberry Pi as an IoT Hub
- Getting Started: What You'll Need
- Basic Pi Setup for Remote Access
- Setting Up Secure P2P SSH for Remote IoT
- The P2P Advantage for IoT
- SSH: Your Secure Gateway
- Essential Software for Free Download
- Step-by-Step Guide to Secure Connection
- Preparing Your Raspberry Pi
- Installing P2P Software
- Configuring SSH for Security
- Testing Your Secure Connection
- Best Practices for Ongoing Security
- Keeping Software Updated
- Strong Passwords and Key Management
- Network Segmentation
- Troubleshooting Common Issues
- Frequently Asked Questions
- Conclusion
Why Secure IoT Connections Matter
In our modern world, we have more and more devices talking to each other. These "Internet of Things" (IoT) gadgets are everywhere, from smart home lights to industrial sensors. It's really cool to control things from far away, but it also brings up a big question: are these connections safe, you know?
The Risks of Open Connections
When your IoT devices are connected to the internet, they can be targets for people who want to do bad things. If a connection isn't properly protected, someone might sneak in. They could mess with your data, take control of your devices, or even use your system to cause trouble elsewhere. This is why making sure your connections are truly safe is so important, typically.
Think about a security camera at your home. If it's not secure, someone could watch what's happening inside your house. Or, if you have a smart lock, an unprotected connection could mean someone gets in without your permission. These are very serious concerns, and we want to help you avoid them, so.
- Pam Bondi Have Children
- Hannah Love Is Blind
- Deep Winter Color Palette
- How To Make Stickers
- Highest Block Blast Score
The Promise of P2P
P2P, or peer-to-peer, is a way for devices to talk directly to each other without needing a central server in the middle. This can be a very good thing for security. When you use P2P, your Raspberry Pi talks straight to your other device, or to your computer, for example. This direct link can reduce the number of places where someone could try to get in, which is a big plus.
P2P connections, when set up correctly, can offer a more private path for your data. It's like having a private conversation with someone, rather than shouting across a crowded room. This guide will walk you through the process of securely connecting your Raspberry Pi in a remote IoT P2P environment, providing you with the knowledge and tools necessary to make that happen, you see.
Your Raspberry Pi as an IoT Hub
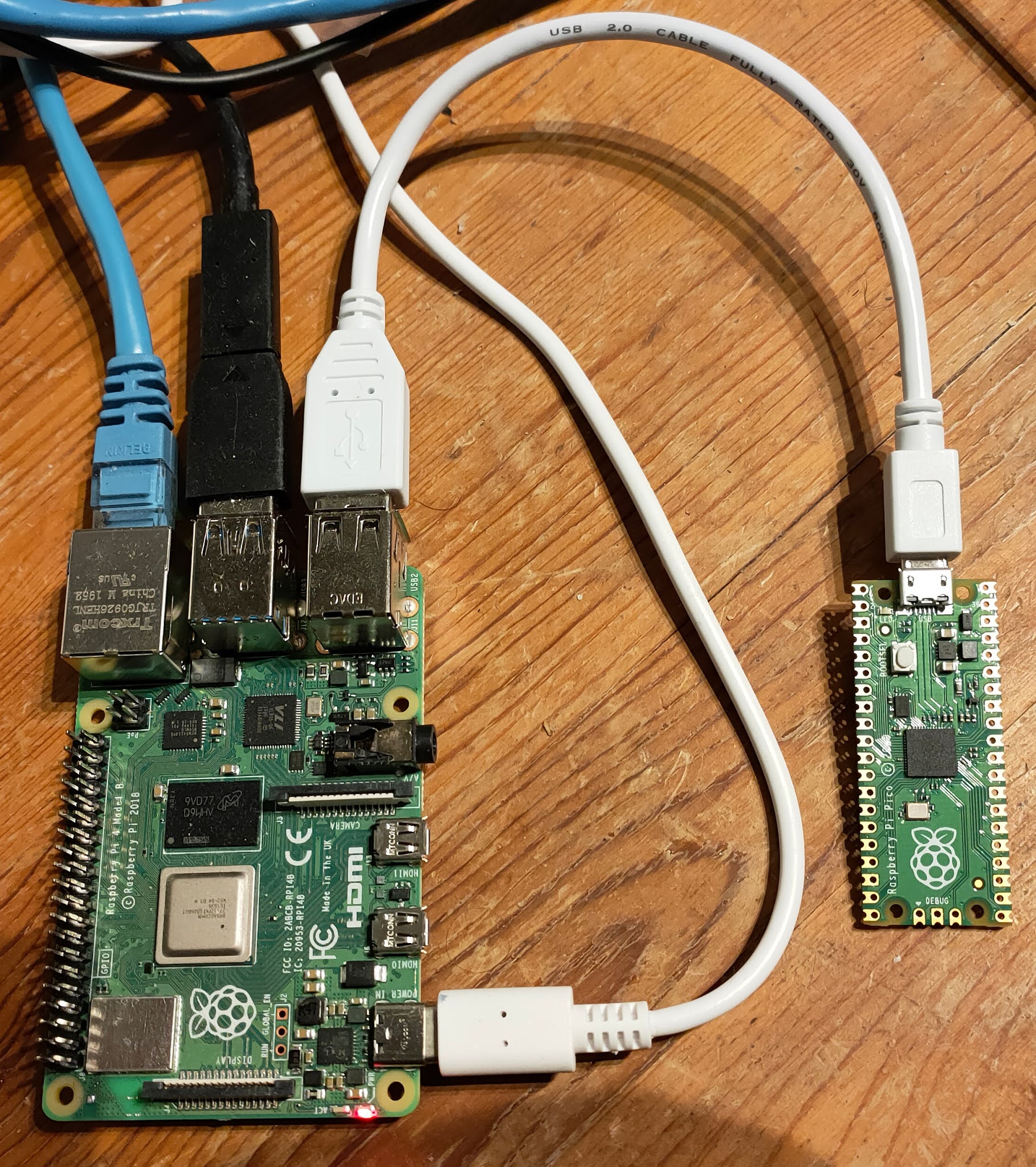
The Raspberry Pi is a small, inexpensive computer that's perfect for IoT projects. It's powerful enough to run a lot of different software, and it's very flexible. People use them for all sorts of things, from home automation to weather stations. For our purpose, it makes a great central point for your remote IoT setup, arguably.
Getting Started: What You'll Need
To begin, you'll need a few basic items. Of course, a Raspberry Pi itself is first. A Raspberry Pi 3 or 4 is usually a good choice for this kind of project. You'll also need a power supply for your Pi, a micro SD card (at least 16GB) to put the operating system on, and a way to connect it to your network, either with an Ethernet cable or Wi-Fi, generally.
You'll also want a computer to set up the SD card and to access your Pi remotely. This guide will walk you through everything you need to know about securely connecting to your Raspberry Pi using remote IoT P2P SSH, including the download process for any necessary tools, so.
Basic Pi Setup for Remote Access
Before we get into the secure P2P part, you need to get your Raspberry Pi up and running with its basic operating system. The most common choice is Raspberry Pi OS (formerly Raspbian). You'll flash this onto your SD card. Once that's done, you'll want to enable SSH (Secure Shell) on your Pi. SSH is a way to connect to your Pi from another computer using a secure, encrypted connection, which is pretty important, actually.
To enable SSH, you can do it during the initial setup process, or later through the Raspberry Pi Configuration tool. This guide will walk you through the process of securely connecting your Raspberry Pi in a remote IoT P2P environment, complete with a free download option for the essential tools you'll need for this step and beyond, you know.
Setting Up Secure P2P SSH for Remote IoT
Now we get to the heart of securely connecting your devices. We're going to combine the directness of P2P with the strong security of SSH. This combination gives you a powerful and safe way to manage your remote IoT devices, virtually.
The P2P Advantage for IoT
For IoT, P2P means your devices don't always need to go through a big cloud server. This can be quicker, and it might even save you some money on server costs. More importantly, it can give you more control over your data, as it's going directly between your chosen points. This guide delves into the intricacies of setting up a secure IoT P2P connection using Raspberry Pi, offering a comprehensive walkthrough that caters to both beginners and advanced users, a little.
When you have a P2P setup, each device acts as both a client and a server. This means they can both send and receive information directly. This setup is very useful for things like remote monitoring or controlling a device without needing a constant internet connection to a central hub, in some respects.
SSH: Your Secure Gateway
SSH, or Secure Shell, is a network protocol that lets you connect to a remote computer over an insecure network in a very safe way. It provides strong encryption, meaning that anything you send or receive is scrambled so that no one else can read it. When you use SSH with your Raspberry Pi, you're creating a secure tunnel for your commands and data, which is very good.
Using SSH is a key part of making your remote IoT connections safe. It protects your login details and any information you send back and forth. This guide will walk you through everything you need to know about securely connecting to your Raspberry Pi using remote IoT P2P SSH, including the download process for the necessary client software on your computer, you know.
Essential Software for Free Download
To get your secure P2P SSH connection going, you'll need some software. Good news: most of the tools you need are open-source and free to download. For SSH, you'll likely use a client program like PuTTY if you're on Windows, or the built-in terminal on Linux or macOS. For the P2P part, there are various open-source tools that can help establish direct connections, such as ZeroTier or OpenVPN, configured in a peer-to-peer fashion. This guide will walk you through the process of securely connecting your Raspberry Pi in a remote IoT P2P environment, complete with a free download option for essential software, so.
You can find these tools on their respective project websites. For instance, you can learn more about PuTTY if you need an SSH client for Windows. The idea is to pick reliable, well-supported open-source options that give you the control and security you need without costing anything, really.
Step-by-Step Guide to Secure Connection
Let us delve into the process of securely connecting remote IoT devices in a P2P SSH environment, offering a comprehensive guide for both beginners and experienced developers. This is where we put all the pieces together, you know.
Preparing Your Raspberry Pi
First, make sure your Raspberry Pi is updated. Open a terminal on your Pi (or connect via SSH if you've already enabled it) and run these commands:
sudo apt updatesudo apt upgrade -y
This makes sure your system has all the latest security patches and software versions. Also, it's a good idea to change the default password for the 'pi' user, or even create a new user with strong credentials. This is a basic but very important security step, arguably.
Installing P2P Software
Next, you'll install your chosen P2P networking software on your Raspberry Pi. For example, if you choose ZeroTier, you would follow their installation instructions, which usually involve a simple command line script. This software helps your Pi find and connect directly to other devices on the P2P network, even if they are behind different routers or firewalls. This guide will walk you through the process of securely connecting your Raspberry Pi in a remote IoT P2P environment, complete with a free download option for essential software, so.
Once installed, you'll typically join your Pi to a private ZeroTier network ID. This creates a virtual network where all your devices can see each other as if they were on the same local network, which is pretty neat. This is a core part of making the P2P connection work across different locations, apparently.
Configuring SSH for Security
With your P2P network in place, you can now connect to your Pi via SSH over this new virtual network. However, we want to make SSH even more secure. A very good step is to use SSH keys instead of passwords. SSH keys are much harder to guess and provide a stronger layer of security. You'll generate a pair of keys: a private key that stays on your computer, and a public key that goes on your Raspberry Pi. This guide will walk you through everything you need to know about securely connecting to your Raspberry Pi using remote IoT P2P SSH, including the download process for key generation tools, you know.
You'll also want to edit the SSH configuration file on your Raspberry Pi to disable password authentication once you have SSH keys working. This means no one can log in with just a password, only with the correct private key. This is a really important security measure, actually.
Testing Your Secure Connection
After setting everything up, it's time to test your connection. From your computer, try to SSH into your Raspberry Pi using its new P2P network address and your SSH key. If everything works, you should see the familiar command line prompt of your Raspberry Pi. This confirms you have a secure, direct connection. Securely connecting remote IoT devices using P2P SSH on a Raspberry Pi is a powerful solution that can transform how you manage your networks, by following these steps, you know.
Try sending a few commands, like checking the system status or listing files. This ensures that your connection is stable and reliable. You've basically built a private, secure tunnel for your IoT devices, which is quite an achievement, really.
Best Practices for Ongoing Security
Setting up a secure connection is a great start, but keeping it secure over time requires a bit of ongoing effort. Think of it like taking care of a garden; you plant the seeds, but you also need to water and weed regularly. These practices will help keep your remote IoT setup safe for the long haul, more or less.
Keeping Software Updated
Software gets updates for a reason: to fix bugs and, very importantly, to patch security holes. Regularly updating your Raspberry Pi's operating system and any P2P or SSH software you're using is a must. This helps protect against new threats that pop up. You can usually do this with the same `sudo apt update` and `sudo apt upgrade` commands you used earlier, so.
Make it a habit to check for updates every few weeks, or set up automatic updates if you're comfortable with that. Staying current is one of the easiest ways to maintain a strong security posture, typically.
Strong Passwords and Key Management
We talked about SSH keys, which are great. But if you still use passwords for anything, make sure they are very strong. This means long, random combinations of letters, numbers, and symbols. Never use simple words or things that are easy to guess. For your SSH keys, keep your private key very safe on your computer, and never share it with anyone, obviously.
Consider using a password manager to help you create and store strong passwords. For SSH keys, make sure they are protected with a strong passphrase. This adds another layer of protection in case your computer is ever compromised, you know.
Network Segmentation
If you have many IoT devices, consider putting them on their own separate network segment. This means they are somewhat isolated from your main home or office network. If one IoT device were to get compromised, the damage would be contained to that specific segment, rather than affecting your whole network. This can be done with a separate router or by configuring your existing router with VLANs, if it supports it, in a way.
This practice is like having separate rooms in a house; if one room gets messy, the rest of the house stays clean. It's a more advanced step, but it adds a significant layer of safety to your entire IoT setup, very.
Troubleshooting Common Issues
Sometimes things don't go perfectly on the first try, and that's completely normal. If you run into issues while trying to securely connect remote IoT devices using P2P SSH on a Raspberry Pi, here are a few common things to check, apparently.
- Can't connect via SSH: Double-check that SSH is enabled on your Raspberry Pi. Make sure your Pi is connected to the network and has an IP address. If you're using SSH keys, ensure your public key is correctly placed on the Pi and your private key is accessible on your computer.
- P2P software not connecting: Verify that the P2P service (like ZeroTier) is running on both your Raspberry Pi and the device you're connecting from. Check that both devices have successfully joined the same virtual network ID. Firewalls can sometimes block P2P connections, so check your firewall settings on both ends, too it's almost.
- Slow connection: Network speed can affect how quickly your remote IoT devices respond. Make sure your internet connection is stable. Also, check the signal strength if you're using Wi-Fi. Sometimes, a simple restart of the Raspberry Pi or your router can help clear up minor network hiccups, usually.
- Permission problems: If you're trying to run commands on the Pi and getting "permission denied" errors, you might need to use `sudo` before the command, or ensure the user you're logged in as has the right permissions for the files or actions you're trying to perform.
Don't get discouraged if you hit a snag. Most issues have straightforward solutions. Online forums and communities for Raspberry Pi and the specific P2P software you're using are great places to find help. Many people have gone through similar challenges and shared their fixes, so.
Frequently Asked Questions
Is P2P IoT truly secure?
P2P IoT can be very secure, yes, but it depends on how it's set up. The direct connection reduces some risks, but you still need strong encryption (like with SSH) and good practices for passwords and key management. It's not automatically secure just because it's P2P; you have to put in the work to make it safe. When done right, it offers a strong security model, you know.
What's the best free software for Raspberry Pi P2P remote access?
There isn't one single "best" option, as it often depends on your specific needs. However, popular and reliable free choices include ZeroTier for creating virtual P2P networks, combined with OpenSSH (which comes pre-installed on Raspberry Pi OS) for secure shell access. OpenVPN can also be configured for P2P connections. These tools are widely used and have good community support, so.
Can I control multiple Raspberry Pis with this method?
Absolutely, you can. The P2P network setup, especially with tools like ZeroTier, allows you to add multiple Raspberry Pis (and other devices) to the same virtual network. Once they are all on this network, you can securely SSH into each one individually from your computer, using the same principles outlined in this guide. This makes managing several remote IoT devices quite manageable, actually.
Conclusion
And there you have it—everything you need to know to securely connect remote IoT devices using P2P SSH on a Raspberry Pi for free. We've gone through why security is so important, how your Raspberry Pi can be a great IoT hub, and the steps to set up a truly safe P2P SSH connection. By following the steps outlined in this article, you can build a reliable and protected system for your remote devices, which is pretty cool, you know.
This guide will walk you through the process of securely connecting your Raspberry Pi in a remote IoT P2P environment, complete with a free download option for essential software. Now you have the knowledge and tools necessary to take control of your remote IoT projects with confidence. We hope this helps you get your devices talking securely, so.
Learn more about IoT security on our site, and link to this page for more Raspberry Pi IoT projects.
This guide was last updated on May 15, 2024, to reflect current best practices and available free tools.
- Lagu Waiting For You
- More Than A Married Couple
- How To Get Nail Glue Off Skin
- King Edward Love Chair
- Is A Fish An Animal
Securely Connect RemoteIoT VPC Raspberry Pi: Free Download For Windows
Securely Connect Remote IoT VPC Raspberry Pi Download Windows Free

Securely Connect Remote IoT VPC Raspberry Pi: Free Download For Windows