Securely Connect Remote IoT: Raspberry Pi To VPC From Windows Downloads
Getting your remote IoT devices, like a tiny Raspberry Pi, to talk safely with a Virtual Private Cloud (VPC) while you manage everything from your Windows computer is a big deal. It's almost like building a super-secret, very private pathway just for your devices. You really want to make sure everything is free from danger, like keeping important documents securely locked away, so no one can mess with your sensitive data or control your devices without permission. This kind of setup means you can keep an eye on things, even when devices are far away, and it gives you a lot of peace of mind, too.
When we talk about connecting things securely, it's about more than just making sure a door is securely fastened; it's about protecting information and making sure only the right people can get to it. You might have seen warnings, for example, when a connection is untrusted, and that's exactly what we want to avoid with our IoT setup. We want to be sure that every part of the connection, from your Windows machine to the cloud and then to your Raspberry Pi, is completely reliable and safe, in a way that truly matters for your operations.
This guide is here to walk you through the steps to make that happen. We'll look at how to prepare your Raspberry Pi, set up your own private section in the cloud, and then link them up safely. We'll also talk about the tools you can use on Windows and some really good habits for keeping everything secure in the long run. By the way, making sure your Windows device itself is up to date and running more securely is also a key part of this whole process.
- Can You Eat Crocs
- Burger King Crown Guy
- Is Clarke From Love Island Trans
- How Long Does It Take For Eyelashes To Grow Back
- Pam Bondi Have Children
Table of Contents
- Understanding the Need for Secure IoT Connections
- What is a VPC and Why Use It for IoT?
- Setting Up Your Raspberry Pi for Remote Access
- Preparing Your Raspberry Pi
- Essential Software for Remote Control
- Establishing Your Virtual Private Cloud (VPC)
- Choosing Your Cloud Provider
- Configuring VPC Network Isolation
- Connecting Your Raspberry Pi to the VPC
- VPN or Direct Connect?
- IP Addressing and Routing
- Managing Your Secure Connection from Windows
- Tools for Remote Access
- Ensuring Windows Device Security
- Best Practices for Ongoing IoT Security
- Regular Updates and Patching
- Identity and Access Management
- Monitoring and Alerting
- Common Questions About Secure IoT Connections
- Final Thoughts on Keeping Your IoT Safe
Understanding the Need for Secure IoT Connections
It's pretty clear that keeping remote devices safe is a really big deal these days. Think about it: anything that connects to the internet can be a target if it's not guarded properly. Your IoT devices, even something small like a Raspberry Pi, are collecting and sending data, and that data needs to be protected. For example, just like how everything should be securely attached to prevent accidents, your digital connections also need to be fastened down very tightly.
Without good security, you could face problems like someone getting unauthorized access to your devices, stealing your data, or even using your devices for bad purposes. This is similar to how "Securly is the leading solution in keeping children safe online at school," meaning we need solutions to keep our devices safe online, too. You want full control over your privacy, and that means making sure your devices and the information they handle stay under your control, basically.
We've all seen those messages saying, "Your device is at risk because it's out of date and missing important security and quality updates." That's a strong reminder that security is an ongoing effort. For remote IoT, this is even more critical. Making sure your connections are trusted and that your devices are well-protected from potential dangers is just good practice, you know?
- Highest Block Blast Score
- How To Say I Love You In French
- Nagi Hikaru
- Whats Jon Gruden Doing Now
- A Court Of Shaded Truths
What is a VPC and Why Use It for IoT?
A Virtual Private Cloud, or VPC, is like having your very own private, isolated section within a bigger public cloud. Imagine it as a special, guarded area where you can put your cloud resources, like virtual servers and databases, completely separate from everyone else's stuff. It's not just a little bit private; it's genuinely isolated. This means you have a lot more control over your network environment, which is super helpful for IoT.
For IoT devices, using a VPC offers some big advantages. First, it helps keep your devices and their data away from the general internet traffic, which reduces the chances of unwanted visitors. This separation acts like a securely guarded office, where only authorized people can enter. You can set up specific rules about what can come in and go out of your VPC, giving you a very fine-tuned way to manage access, sort of like creating transport rules to lock down an organization's email to only trusted IPs.
Secondly, a VPC lets you create a dedicated network for your IoT devices. This means they can communicate with each other and with your cloud applications without exposing themselves to the wider internet, which is a big win for security. It helps ensure that everything is securely attached, digitally speaking, because you're building a controlled environment. So, in some respects, it's about creating a safe space for your remote devices to operate.
Setting Up Your Raspberry Pi for Remote Access
Getting your Raspberry Pi ready to connect remotely is the first big step. These little computers are pretty amazing, but they need a bit of preparation to make sure they're safe and ready for action. You want to make sure your device is set up properly from the start, just like making sure a door is securely fastened before you leave.
Preparing Your Raspberry Pi
First things first, you'll want to install a fresh operating system on your Raspberry Pi, like Raspberry Pi OS. Make sure you get it from a trusted source, too. Once it's installed, change the default password right away. This is a very simple but incredibly important security step. It's like changing the locks on a new house; you just do it. You should also enable SSH (Secure Shell) on your Pi, which lets you connect to it remotely using an encrypted connection. This is a lot like having a secure phone line for talking to your device.
It's also a good idea to keep your Raspberry Pi's software updated regularly. This means running commands to get the latest security patches and bug fixes. An outdated system can be a weak point, and you really want to avoid that. Keeping things current helps your device run more securely, and it gives you a better chance of avoiding problems down the road, you know?
Essential Software for Remote Control
To control your Raspberry Pi from your Windows computer, you'll need some specific software. For secure command-line access, a program like PuTTY is a very popular choice. It lets you open an SSH connection to your Pi, so you can type commands and manage it as if you were sitting right in front of it. There are also other tools like Visual Studio Code's Remote-SSH extension that let you develop and manage files directly on your Pi, which is pretty handy.
If you prefer a graphical interface, you can set up a VNC server on your Raspberry Pi and a VNC client on your Windows machine. This allows you to see the Pi's desktop remotely, almost like you're looking at its screen. Just remember that any remote desktop solution should also be secured, perhaps by tunneling it through an SSH connection or VPN, to keep everything private and safe. It's about making sure your connection is trusted, after all.
Establishing Your Virtual Private Cloud (VPC)
Once your Raspberry Pi is ready, the next big step is setting up your VPC. This is where you create that dedicated, private network space in the cloud for your IoT devices to live and communicate. It’s a bit like building a custom, secure room within a very large building, where only your things can be. You want to make sure this space is set up just right, too.
Choosing Your Cloud Provider
There are several big cloud providers that offer VPC services, including Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Platform (GCP). Each one has its own way of doing things, but the core idea of a private network space is the same. Your choice might depend on what you're already using, your budget, or the specific features you need. For instance, if you're already familiar with Microsoft products, Azure might feel more comfortable, in a way.
When picking a provider, think about how easy it is to set up a VPC, the cost, and the security features they offer. They all have robust security protocols, but it's good to understand them. You'll want a provider that helps you keep everything securely guarded and gives you the tools to take full control over your privacy, you know?
Configuring VPC Network Isolation
Setting up your VPC involves a few key steps to ensure proper network isolation. You'll define your VPC's IP address range, which creates a logical boundary for your private network. Inside this VPC, you'll create subnets. These are smaller segments of your network, and you can use them to separate different types of devices or services. For example, you might have one subnet for your Raspberry Pi devices and another for your cloud applications, which is a bit like having separate rooms for different activities.
Security groups and network access control lists (ACLs) are also very important here. Security groups act like virtual firewalls for your individual instances (like your Raspberry Pi when it connects), controlling inbound and outbound traffic. Network ACLs operate at the subnet level, adding another layer of security. This is similar to setting up strict rules for who can enter and exit specific areas, much like restricting mail to only come from certain IP addresses, so it's a very tight system.
Connecting Your Raspberry Pi to the VPC
Now that you have your Raspberry Pi prepared and your VPC set up, it's time to bring them together. This connection needs to be solid and, most importantly, secure. We want to avoid any situation where a connection is untrusted, so we pick the right methods to ensure data travels safely, you know?
VPN or Direct Connect?
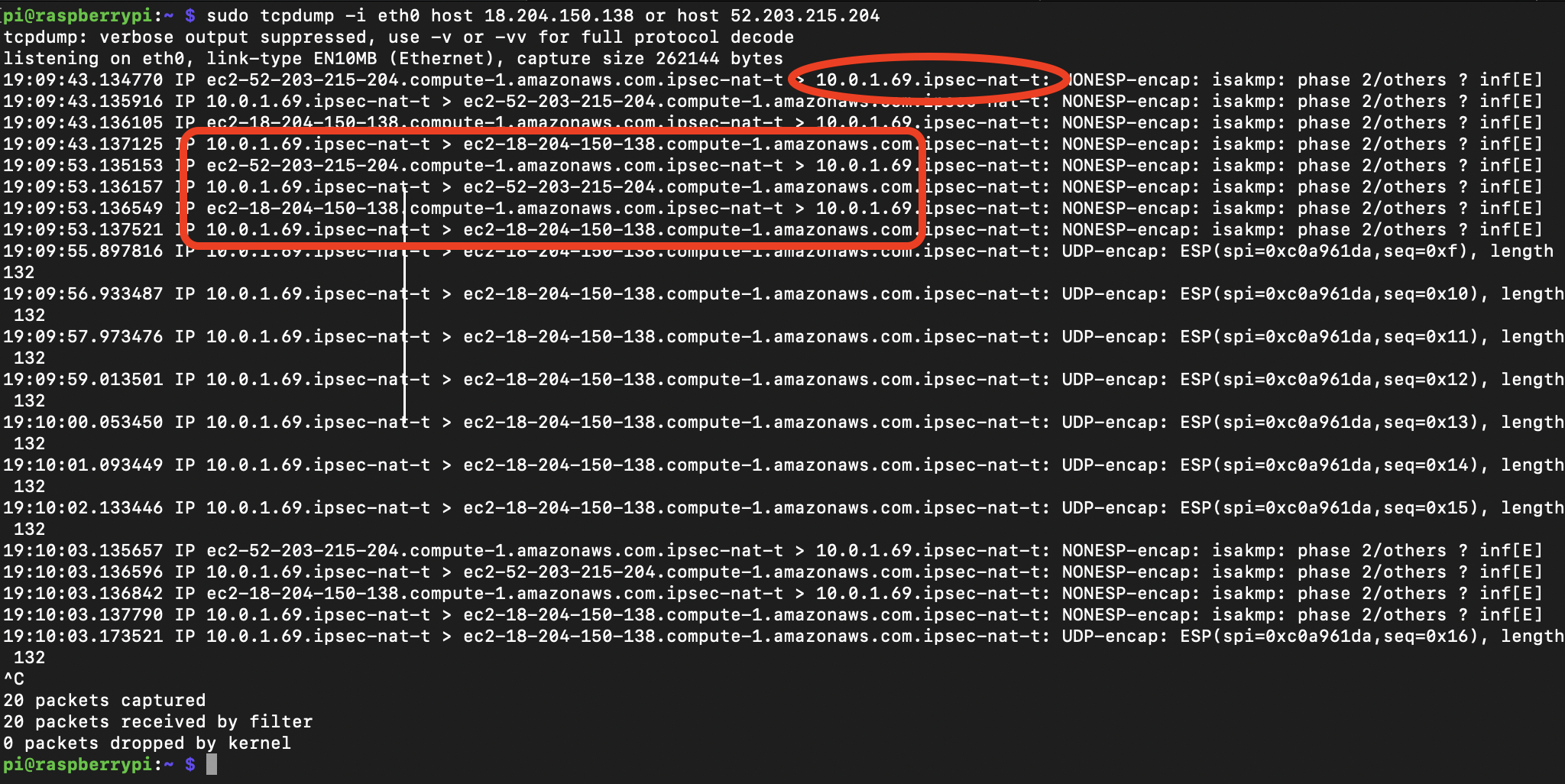
For most remote IoT setups, especially with Raspberry Pis, a Virtual Private Network (VPN) is the most common and practical way to connect to your VPC. A VPN creates an encrypted tunnel over the public internet, making it seem like your Raspberry Pi is directly inside your VPC. This means all the data flowing between your Pi and your cloud resources is protected and private, which is really important. It's like having a secret, protected pathway for your information.
Another option, though usually for much larger organizations, is Direct Connect. This provides a dedicated, private network connection from your on-premises environment directly to your cloud provider. It offers higher bandwidth and a more consistent network experience, but it's generally overkill for individual Raspberry Pi setups. For most folks, a VPN is the way to go for securely connecting remote IoT devices.
IP Addressing and Routing
Once your VPN is established, your Raspberry Pi will get a private IP address within your VPC's network range. This means it can communicate with other resources inside your VPC using those private addresses, rather than needing a public IP. This significantly boosts security because your Pi isn't directly exposed to the internet. You'll also need to configure routing tables within your VPC to make sure traffic from your Pi can reach the right cloud services, and vice versa. This ensures that data knows exactly where to go, a bit like a well-organized postal service for your network packets.
It's also worth thinking about how your Pi will find the VPN server. You might use dynamic DNS or a fixed IP if your cloud provider offers it. Making sure this part is stable is pretty key for consistent connectivity. And, of course, verifying that your connection is secure is always the goal, especially when you're connecting devices remotely.
Managing Your Secure Connection from Windows
With your Raspberry Pi connected to your VPC, you'll primarily interact with it from your Windows computer. This means having the right tools and making sure your Windows device itself is a secure gateway. It’s not just about the Pi or the VPC; your local machine plays a big role, too.
Tools for Remote Access
As mentioned before, tools like PuTTY or the SSH client built into Windows (if you're on a newer version) are great for command-line access to your Raspberry Pi over the secure VPN tunnel. For more visual tasks, a VNC client or a remote desktop protocol (RDP) client (if you've set up an RDP server on your Pi, which is a bit more involved) can give you a graphical view. These tools allow you to manage your Pi as if it were right there, which is very convenient.
When you're downloading any software or configurations related to your IoT setup onto your Windows machine, always make sure you're getting them from trusted sources. Sometimes, issues can happen, like when "downloading an .msg file from sharepoint online document library" in a specific browser, so it's good to be aware of potential quirks. Always double-check where your downloads are coming from to keep your Windows system safe, you know?
Ensuring Windows Device Security
Your Windows computer is the control center for your remote IoT setup, so its security is just as important as the Pi's. Make sure your Windows operating system is always up to date with the latest security and quality updates. If your device is out of date, it's at risk, and you want to get back on track so Windows can run more securely. This is a pretty straightforward step but one that many people sometimes overlook.
Also, use strong passwords, and consider using multi-factor authentication (MFA) for your Windows login and any cloud accounts you access. This adds an extra layer of protection, making it much harder for unauthorized people to get in. Think about how important it is to keep a certificate securely; your digital access points need the same level of care. You might also want to look into protecting specific files or folders on your Windows machine, similar to how someone might want to password protect a file in SharePoint, even if it's not the entire folder.
Best Practices for Ongoing IoT Security
Setting up your secure connection is a fantastic start, but keeping your IoT system safe is an ongoing effort. It's not a one-time task; it's something you consistently work on, like making sure your offices are securely guarded every single day. There are a few habits that will really help you maintain that strong security posture, you know?
Regular Updates and Patching
This point cannot be stressed enough: keep everything updated. This includes the operating system on your Raspberry Pi, any software running on it, your Windows operating system, and all the tools you use for remote access. Software developers constantly release updates to fix vulnerabilities and improve performance. Missing these updates leaves your devices exposed to known threats, which is a bit like leaving a door unlocked when you know there are people trying to get in. Regularly checking for and applying updates is a simple yet very effective way to keep your entire system running more securely.
Identity and Access Management
Who can access your devices and data? This is a really important question. Implement strong identity and access management (IAM) practices. This means using unique, complex passwords for every account, and enabling multi-factor authentication wherever possible. It's also about giving people only the access they absolutely need to do their job, and nothing more. This is similar to how you might "select your identity provider" for various sign-ins, like Google or Microsoft Azure AD, ensuring that only verified identities get through. It truly helps you take full control over your privacy, which is something everyone wants.
Monitoring and Alerting
Even with the best security measures, it's wise to monitor your IoT devices and network for unusual activity. Setting up logs and alerts can notify you if something out of the ordinary happens, like an unexpected login attempt or a sudden surge in data traffic. This is a bit like having a system to "quickly account for students in an emergency"; you want to know right away if something is amiss. Early detection can help you respond quickly to potential threats and prevent bigger problems. Seeing your child's online activity in real-time gives parents peace of mind, and monitoring your IoT devices offers a similar sense of security for your digital assets, you know?
Common Questions About Secure IoT Connections
People often have similar questions when they're thinking about how to securely connect remote IoT devices, especially when using a VPC and managing things from Windows. Here are a few common ones, in a way that might help clear things up.
How do I know if my Raspberry Pi connection to the VPC is truly secure?
You can check for a truly secure connection by verifying that your VPN tunnel is active and encrypted. Look for indicators like a strong cryptographic cipher being used. You should also regularly review your VPC security group and network ACL rules to ensure only necessary traffic is allowed. If you're getting messages like "this connection is untrusted," that's a sign something isn't right, and you'll want to investigate that right away. It's about making sure your connection is confirmed as secure.
What if my Windows computer gets compromised? Will my IoT devices still be safe?
If your Windows computer gets compromised, the security of your IoT devices depends on how well you've isolated them. If your Raspberry Pi is only accessible through the VPC via a VPN and strong authentication (like MFA), the risk is much lower. However, if your Windows machine holds critical credentials or keys, those could be exposed. This highlights why keeping your Windows device updated and running more securely is absolutely vital, and why strong identity protection is so important, you know?
Can I manage multiple Raspberry Pis through one VPC?
Yes, you absolutely can manage multiple Raspberry Pis within a single VPC. This is actually one of the big benefits of using a VPC. You can place all your IoT devices in the same private network space, apply consistent security policies, and manage them centrally. You can even use different subnets or security groups to logically separate groups of Pis if needed, which gives you a lot of flexibility. It's pretty efficient, too.
Final Thoughts on Keeping Your IoT Safe
Getting your Raspberry Pi to securely connect to a VPC from your Windows machine is a really smart move for managing remote IoT devices. It's all about building those strong, private pathways for your data and ensuring everything stays under your watchful eye. By taking steps to prepare your Pi, setting up a proper VPC, and using secure connection methods, you're building a very solid foundation. This helps you keep your devices free from danger, which is the main goal, after all.
Remember, security is a continuous journey. Staying on top of updates, managing who has access, and keeping an eye on your network are ongoing tasks that will help you maintain that peace of mind. It’s a bit like knowing that "Securly is designed to help you take full control over your privacy," giving you the tools to protect your valuable information and devices. For more insights on securing your connected devices, explore IoT security best practices from official sources. You can also learn more about secure remote connections on our site, and link to this page for more details on device management. Taking these steps helps ensure that your remote IoT setup runs smoothly and safely, today and in the future.
- What Is A Golden Birthday
- B Cup Breast Size
- Niece In Spanish Language
- Shut Up In Spanish
- Remoteiot P2p Download
Securely Connect Remote IoT VPC Raspberry Pi Download Windows Free: A
Securely Connect Remote IoT VPC Raspberry Pi AWS Download Windows

Securely Connect Remote IoT VPC Raspberry Pi: Free Download For Windows