Secure Your Gadgets: An SSH IoT Tutorial For Remote Access Today
Connecting your IoT devices from afar, safely and reliably, is a big deal these days. This is where a really helpful tool called SSH comes into play, making it possible to manage your internet of things (IoT) gadgets from almost anywhere, you know. With SSH, remote access to devices is safe, easy to put in place, and dependable, so it's a pretty big deal.
Many people worry about keeping their devices safe when they are out there on the internet, and that's a fair concern. Secure Shell (SSH) is a vital tool for managing remote devices securely, especially when working with IoT ecosystems. It gives you a safe way to connect to your internet of things (IoT) devices from a distance, like your own private, locked pathway.
This guide will walk you through everything you need to know about using SSH for your IoT devices, from setting things up to handling some common little bumps along the way. We'll explore the fundamentals of SSH, talk about its practical uses within the IoT world, and show you how to confidently manage your devices.
- Surrealism Dress To Impress
- B Cup Breast Size
- Julesari Leaks
- Yes Yes Yes Meme
- How Many Legs Does A Spider Have
Table of Contents
- What is SSH and Why It's Good for IoT
- Getting Your IoT Device Ready for SSH
- Turning SSH On
- Making User Accounts
- Connecting to Your IoT Device
- Using an SSH Client
- Setting Up SSH Keys
- Keeping Your SSH Connections Safe
- Keys Over Passwords
- Changing the Default Port
- Firewall Basics for IoT
- Dealing with Common SSH Issues
- More Advanced SSH Tricks for IoT
- Opening Tunnels
- Using SSH with AWS IoT
- AWS IoT Secure Tunneling
- Frequently Asked Questions About SSH for IoT
What is SSH and Why It's Good for IoT
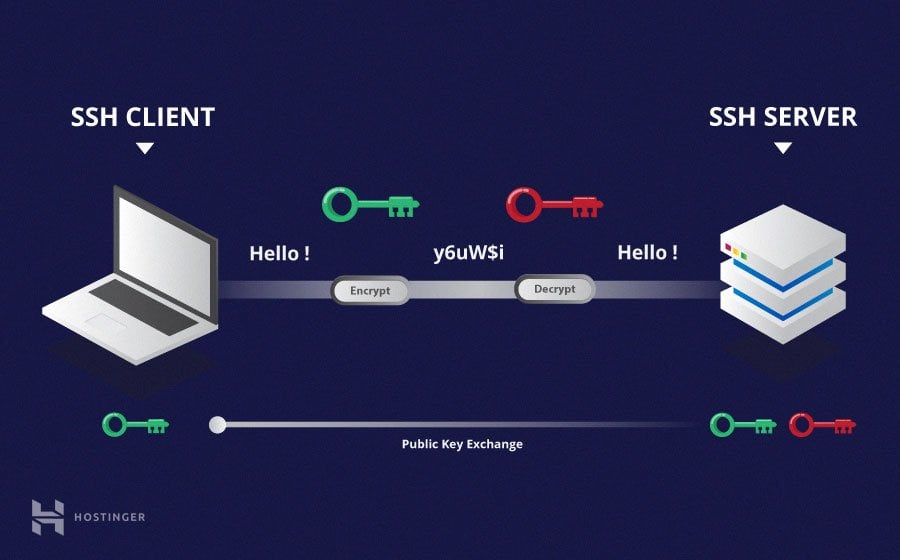
Secure Shell, or SSH, is a way to get into computers and devices from far away in a very safe manner. It makes sure that whatever information you send back and forth stays private and protected from prying eyes. This is, you know, really important for anything connected to the internet.
For IoT devices, which are often out there in the world and not sitting right next to you, SSH is a real lifesaver. It means you can check on them, update them, or fix things without having to physically go to each one. This makes managing your IoT setup so much simpler, actually.
The main reason SSH is so good for IoT is its focus on security. It encrypts all the data, so even if someone tries to listen in, they won't understand what's being said. This guide will explain how to use the SSH protocol to securely manage your devices, ensuring seamless communication and control in no time, so that's pretty helpful.
- Pam Bondi Have Children
- How To Cook Scallops
- Business Class Vs First Class
- 16 Guard Buzz Cut
- Space City Home Network
Getting Your IoT Device Ready for SSH
Before you can connect to your IoT device using SSH, you need to set it up to accept these connections. This usually involves a few simple steps, and it's something you can typically do quite easily, especially with popular devices like the Raspberry Pi.
Turning SSH On
Most IoT operating systems, especially those based on Linux, have SSH built-in, but it might not be turned on by default. For example, on a Raspberry Pi, you can often enable SSH through its configuration tool or by placing a special file on the boot partition. You know, it's a pretty straightforward process.
If you're using a different kind of IoT device, the steps might vary a little, but the idea is the same: you need to activate the SSH server software on the device. This is the part that listens for incoming connections, so it's a key first step.
Making User Accounts
Once SSH is active, you'll need to have a user account on your IoT device that you can log into. It's a good idea to create a new user account specifically for remote access, rather than using a default or "root" account, if possible. This adds an extra layer of safety, you see.
Make sure this new user has a strong, unique password to start with. We'll talk more about even safer ways to log in later, but for now, a good password is your first line of defense. It's really quite important to get this right from the beginning.
Connecting to Your IoT Device
With your IoT device ready, the next step is to actually make the connection from your computer. This is where you'll use an SSH client, which is a piece of software that talks to your device's SSH server. It's, you know, how the two sides communicate.
Using an SSH Client
On most Linux or macOS computers, an SSH client is already there, built right into the terminal. You just open a terminal window and type a simple command. For Windows, you might need to install a program like PuTTY, or use the built-in OpenSSH client that newer versions of Windows have, which is pretty handy.
The basic command to connect is usually something like ssh username@device_ip_address. You'll replace "username" with the account you made on your IoT device and "device_ip_address" with your device's network address. It's, you know, pretty much that simple to get started.
Setting Up SSH Keys
While passwords work, SSH keys are a much more secure and convenient way to log in. They involve two parts: a public key that goes on your IoT device and a private key that stays on your computer. This way, you don't have to type a password every time, and it's a lot safer, too.
To set up keys, you first generate a pair on your computer. Then, you copy the public key over to your IoT device. When you try to connect, your computer uses the private key to prove who it is, and the device checks it against the public key. This method is really recommended for all your IoT devices, honestly.
Getting comfortable with SSH for your IoT devices truly opens up a world of possibilities. We have gone through how to set up your keys, connect to your devices, and handle some common situations, which is pretty much the core of it all.
Keeping Your SSH Connections Safe
Security is not just important for IoT; it's essential. SSH is like the superhero of remote access, protecting your connections. But even superheroes need a little help to stay strong. There are several best practices you should follow to keep your IoT devices safe from unwanted access, you know.
Keys Over Passwords
As mentioned, using SSH keys for authentication is far better than relying solely on passwords. Passwords can be guessed or cracked, but SSH keys are extremely difficult to compromise. After you set up key-based login, you should, actually, disable password authentication on your IoT device.
This means that only someone with the correct private key can get in, making your device much more secure. It's a simple change that makes a very big difference, so it's worth the little bit of effort.
Changing the Default Port
By default, SSH uses port 22. Many automated attacks scan for devices listening on this port. Changing your SSH port to a different, non-standard number can help reduce the amount of unwanted attention your device gets. It's not a perfect security measure on its own, but it helps a little.
You'll need to edit the SSH server's configuration file on your IoT device to make this change. Remember to specify the new port when you connect from your SSH client, like ssh -p new_port_number username@device_ip_address. It's a small tweak that can add some quiet to your logs, honestly.
Firewall Basics for IoT
A firewall acts like a guard, controlling what kind of network traffic can reach your IoT device. Setting one up, even a simple one, can block many common attack attempts. You can configure your device's firewall to only allow SSH connections from specific IP addresses or networks, which is a good idea.
This comprehensive tutorial aims to walk you through the fundamentals of creating a firewall for IoT devices using SSH. We will talk about understanding IoT security risks and setting up your firewall to protect against them. It's a pretty essential step for keeping things safe.
Dealing with Common SSH Issues
Sometimes, things don't go perfectly, and you might run into a problem when trying to connect via SSH. Don't worry, many common issues have simple fixes. This tutorial is designed to walk you through every step, from setting up SSH on your IoT device to troubleshooting common issues that you might encounter.
One common problem is incorrect IP addresses or network settings. Always double-check that your device is on the network and that you have its correct IP. Another issue might be firewall rules blocking the connection, either on your computer or the IoT device. You know, checking these basic things first often solves the problem.
Permission errors with SSH keys can also happen. Make sure your private key file has the right permissions (usually read-only for your user). If you're still stuck, checking the SSH server logs on your IoT device can often give you clues about what's going wrong. It's, like, a pretty good way to figure things out.
More Advanced SSH Tricks for IoT
SSH can do more than just let you log in remotely. It also has features that are really useful for more complex IoT setups, especially when you need to access services on your device that aren't directly exposed to the internet. This is where things like SSH tunnels come in, so that's pretty neat.
Opening Tunnels
An SSH tunnel creates a secure pathway between your computer and your IoT device through the SSH connection. This is incredibly useful for accessing web interfaces or other services running on your IoT device that are not meant to be publicly accessible. For an example tutorial, see how to open a tunnel and start an SSH session to a remote device.
This allows you to securely forward traffic from a port on your local machine to a port on your remote IoT device. It's like having a private, secure bridge for specific applications. Mastering SSH remote IoT device connections involves exploring these foundational concepts of SSH and learning how to use them.
Using SSH with AWS IoT
For those using cloud services, AWS IoT offers a really helpful feature called Secure Tunneling that works beautifully with SSH. This allows you to establish a secure, bidirectional communication path to remote devices that might be behind a firewall. It's a pretty big deal for managing devices at scale.
AWS IoT Secure Tunneling
AWS IoT Secure Tunneling helps customers establish bidirectional communication to remote devices that are behind a firewall over a secure connection managed by AWS IoT. When you create a tunnel from the AWS IoT console, you can also specify whether you want to open a tunnel from the tunnels hub page using the quick setup method.
This feature makes it much easier to reach devices that are deep within private networks without needing complex firewall configurations or VPNs. It's a very practical way to ensure you can always reach your devices for maintenance or data collection, which is pretty much what you want.
In this detailed guide, we will explore the integration of IoT devices with SSH and AWS, talking about the technical aspects, benefits, and best practices. With AWS, you can seamlessly connect your devices, so that's a good thing to know.
Frequently Asked Questions About SSH for IoT
Here are some common questions people ask about using SSH with IoT devices.
Is SSH safe for IoT devices?
Yes, SSH is considered very safe for IoT devices when set up correctly. It uses strong encryption to protect all data exchanged, and with practices like key-based authentication, it offers a high level of security. It's, like, one of the best ways to keep your remote connections private.
Can I use SSH to manage my Raspberry Pi IoT projects?
Absolutely! Raspberry Pi IoT SSH tutorial is a powerful guide for anyone looking to explore the world of remote access and IoT projects. SSH is a very common and recommended way to manage Raspberry Pi devices, whether they are part of an IoT project or just used as a small computer. You'll learn how to get your devices set up and connected, which is pretty cool.
What if my IoT device is behind a firewall?
If your IoT device is behind a firewall, you might need to configure the firewall to allow SSH connections to pass through, or use advanced SSH features like tunneling. Services like AWS IoT Secure Tunneling are also designed to help you reach devices even when they are behind strict network barriers, so that's a good option to have.
Learn more about secure remote access on our site, and check out this page for official SSH documentation.
- Pam Bondi Have Children
- Twin Where Have You Been
- 6 Guard Buzz Cut
- Ap Classroom Unit 6 Progress Check Mcq Answers Ap Lang
- Jackerman Mother Warmth
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

Windows SSH Server | Learning, Secure shell, Software engineer