Securely Connect Remote IoT Devices: P2P SSH Download Free Solutions For Today
Are you feeling a bit worried about your smart gadgets and devices out there? You know, the ones that are supposed to make life easier, but sometimes they just feel a little… exposed? Many folks find their remote equipment, like those smart home sensors or even industrial monitors, are sometimes at risk. This happens because they might be a bit behind on important security updates. You might even see warnings pop up, like "This connection is untrusted," or maybe your browser just can't confirm things are safe. It's a common worry, really, and it means your data might not be as protected as you'd like it to be.
It's honestly a bit frustrating when you're trying to connect to something important, and then you get that message saying, "There is a problem connecting securely to this website." It makes you wonder, doesn't it? Especially when you've tried different web browsers, like MS Edge, Firefox, or Chrome, and still, nothing seems to work. That feeling of not having any other option when these warnings appear can be quite unsettling, so it's almost time to find a better way.
Thankfully, there are ways to get your devices back on track. We can make sure they run more securely, and that your connections are trustworthy. This article will look at how you can securely connect remote IoT devices using P2P SSH, and yes, we'll even talk about options you can download for free. We'll help you understand why this matters and what steps you can take to keep your remote gadgets safe, which is a big help.
- Timothee Chalamet Net Worth
- How Do You Spell
- Remoteiot Monitoring Ssh Download Android
- What Is A Femboy
- Jackerman Mother Warmth
Table of Contents
- The Need for Secure IoT Connections
- What is SSH and Why It Matters
- Peer-to-Peer (P2P) Connections Explained
- Combining P2P and SSH for IoT Security
- How to Securely Connect RemoteIoT P2P SSH (Download Free)
- Common Connection Issues and How to Fix Them
- Frequently Asked Questions (FAQs)
- Taking the Next Steps for Better Security
The Need for Secure IoT Connections
You know, it’s a bit like leaving your front door unlocked when you have a lot of valuable things inside. Your IoT devices, whether they are smart cameras, environmental sensors, or even just a smart thermostat, are little computers that connect to the internet. If these connections aren't secure, then it's almost like anyone could peek in, or worse, mess with them. We've heard stories about devices being out of date and missing important security fixes, which is a real worry.
When your system, like Windows, is not up-to-date, it just can't run as securely as it should. This can lead to those scary messages that say, "Your device is at risk because it's out of date and missing important security and quality updates." It’s a clear sign that things need a bit of attention, you know? Keeping everything current is a pretty big part of staying safe online, and that includes your remote gadgets.
Think about it: an untrusted connection is like trying to talk to someone through a wall, and you can't be sure who is listening on the other side. When Firefox, or any browser, tells you it "can't confirm that your connection is secure," it's a big red flag. This applies to your remote IoT devices too, especially if you're trying to get information from them or send commands. You really want to make sure that the path between you and your device is private and protected, so that's a good goal.
- How Do I Say Goodbye Lyrics
- Shasha Prasad
- Securely Connect Remoteiot Vpc Raspberry Pi Aws Server
- Yes Yes Yes Meme
- What Happened To Jessica Tarlov
What is SSH and Why It Matters
SSH stands for Secure Shell. It's a way to connect to a computer over an unsecured network, but it does so in a very safe manner. Think of it like a secret tunnel for your data. When you use SSH, all the information you send and receive is wrapped up in a strong code. This code makes it very hard for anyone else to understand what's going on, even if they somehow manage to grab your data. It’s pretty much the gold standard for remote access security, and it’s been around for a while, too.
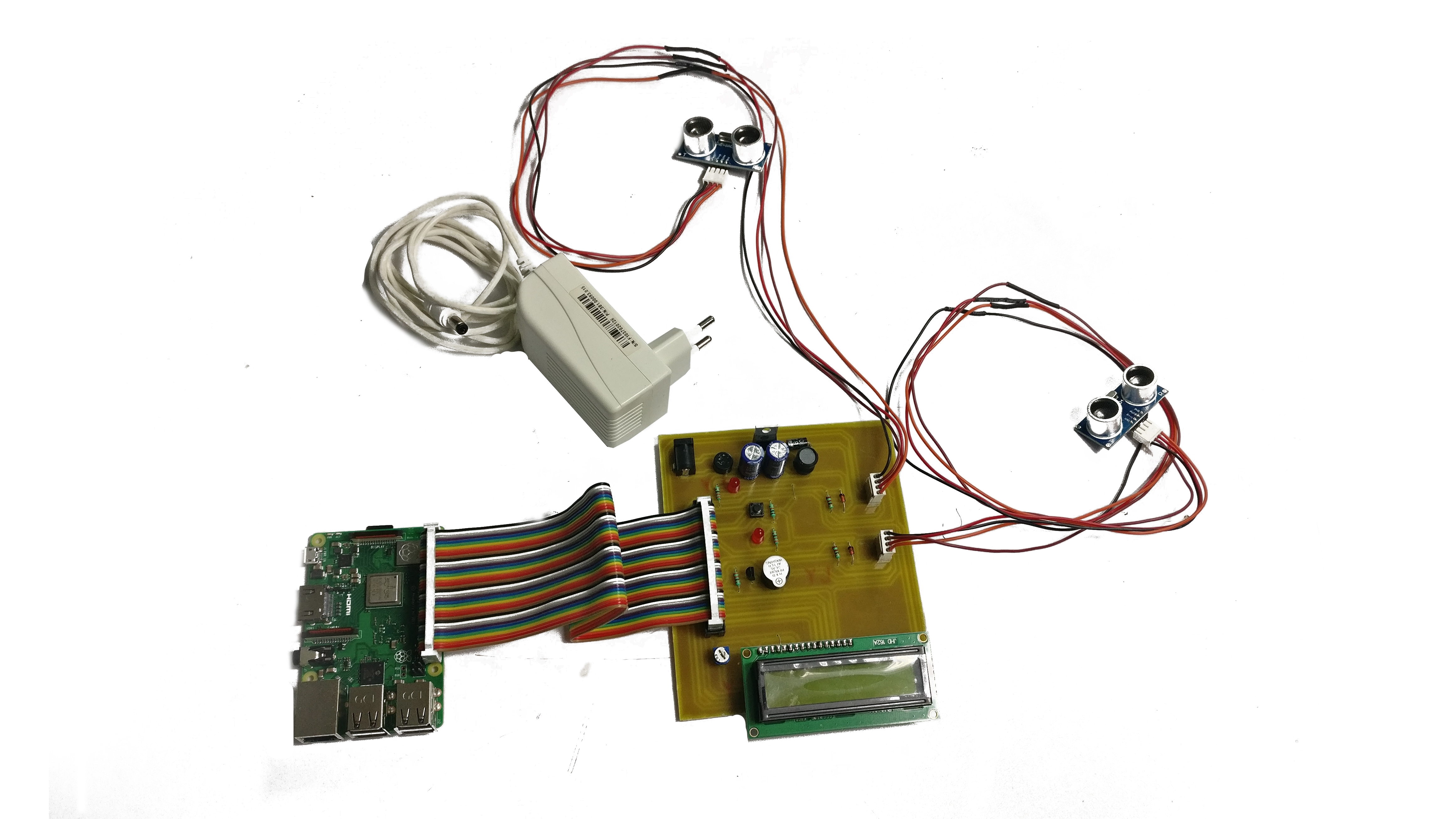
The main reason SSH is so important for IoT devices is that these small gadgets often sit in places that are not physically secure. Maybe your smart garden sensor is out in the yard, or your industrial monitor is in a remote facility. You need a way to talk to them, update them, or get data from them without exposing them to bad actors. SSH provides that safe pathway. It helps you manage these devices from afar, keeping everything private and sound, which is really helpful.
Without SSH, your connection might be like an open book. Anyone with a bit of know-how could potentially see what you're doing, or even take control of your device. This is why when you get warnings about untrusted connections, it's a serious matter. SSH fixes that by making sure your communication is encrypted from start to finish. It gives you peace of mind, knowing that your remote commands and data are traveling through a secure channel, you know, which is rather comforting.
Peer-to-Peer (P2P) Connections Explained
So, what exactly is a peer-to-peer, or P2P, connection? Well, it's a bit different from how most internet connections work. Usually, when you go to a website, your computer talks to a central server, and that server then sends you the website's information. That's a client-server setup, so it's a common way things happen.
With P2P, there isn't one central server in the middle. Instead, your computer talks directly to another computer. Imagine two friends talking on walkie-talkies without needing a big radio tower in between them. That's more or less what P2P is. For IoT, this can be really useful because it means your devices can talk to each other, or to your control station, without relying on a third-party server that might go down or cost money. It’s a very direct way to communicate, you know.
The beauty of P2P for IoT is its efficiency and sometimes its ability to bypass certain network hurdles. For instance, if your IoT device is behind a tricky home router, a P2P setup might help it "find" your control computer more easily. It reduces reliance on external services, which can be a good thing for privacy and cost. It's a rather clever way to make devices communicate directly, and that's a big plus for many situations.
Combining P2P and SSH for IoT Security
When you put P2P and SSH together, you get a pretty powerful combination for IoT security. Imagine that direct, friend-to-friend walkie-talkie connection from P2P, but now, everything you say over that walkie-talkie is in a secret code that only your friend can understand. That's P2P SSH for you. It means your IoT device and your control computer are talking directly, but their conversation is completely private and protected. This is a big deal, you know.
This setup is especially good for remote IoT devices because it offers a few benefits. First, it makes the connection very secure due to SSH's encryption. Second, the P2P aspect can make it easier to connect to devices that might be behind tricky firewalls or routers, which is often the case with home IoT setups. You don't always need complex network configurations or expensive cloud services to get things working. It’s a pretty neat way to get around common problems, in a way.
Also, this approach can help you avoid those "untrusted connection" warnings. Because you're setting up a direct, encrypted link, your system is more likely to trust the connection. It gives you a lot more control over your device's access. This means you can manage your smart home gadgets, or even more serious industrial sensors, with confidence, knowing your data is safe. It's a rather smart way to keep your digital life private, you know, and very secure.
How to Securely Connect RemoteIoT P2P SSH (Download Free)
Getting your remote IoT devices connected securely with P2P SSH, especially using free tools, is quite doable. It does take a few steps, but it's worth the effort for the peace of mind you'll gain. Remember, we want to avoid those frustrating messages about untrusted connections and make sure your systems are up to date. This approach helps with all that, so it's a good path to take.
Choosing Your Free SSH Client
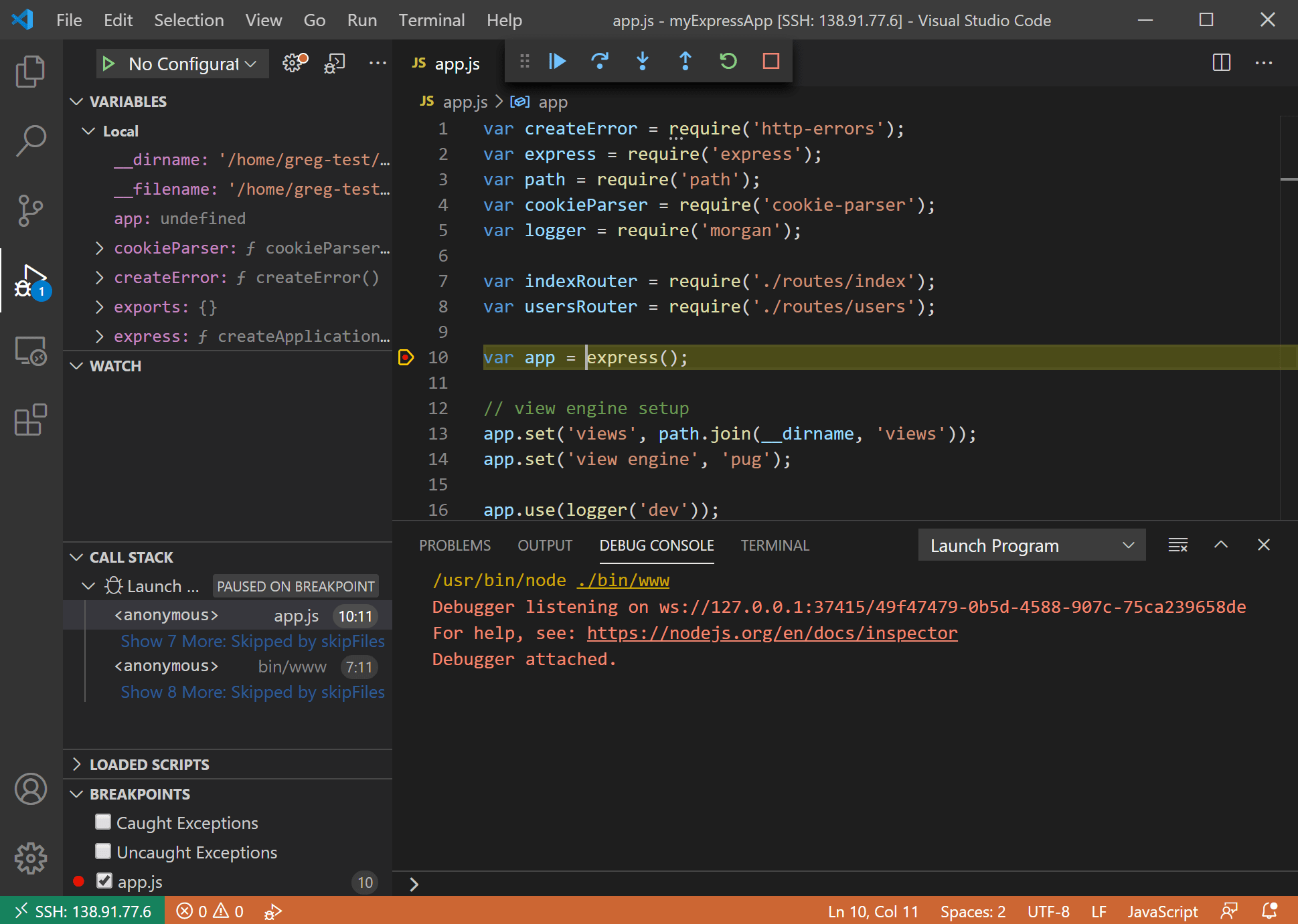
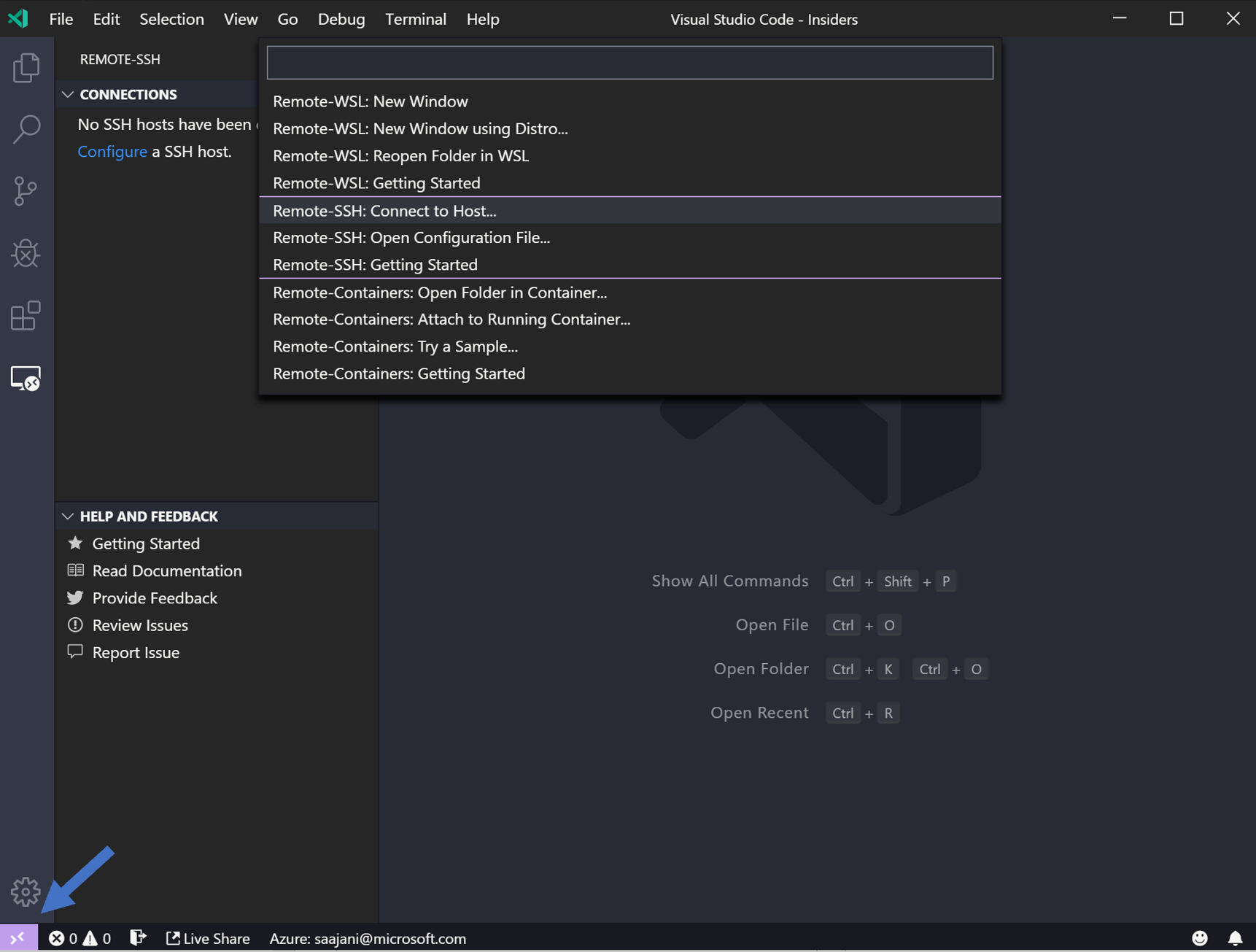
The first step is to pick a good, free SSH client for your computer. This is the program you'll use to talk to your IoT device. For Windows users, a very popular choice is PuTTY. It's free, pretty easy to use, and you can download it directly from its official website. For Mac or Linux users, SSH is often built right into the terminal, so you don't even need to download anything extra. It's just there, ready to go, which is quite convenient, you know.
When you're looking to download, make sure you get it from a trusted source. For PuTTY, always go to the official PuTTY website. Be careful of other sites offering "free downloads" that might bundle extra, unwanted software. You want the clean version, you know, the one that won't cause more problems. Getting the right tool from the right place is pretty important for a smooth start.
Setting Up SSH on Your IoT Device
Most modern IoT devices, especially those running a version of Linux like Raspberry Pi or similar microcontrollers, have SSH built in or can have it easily added. You'll usually need to access your device locally first, perhaps by plugging it into a monitor and keyboard, or by connecting to its local network. From there, you can enable the SSH service. For example, on a Raspberry Pi, it's often as simple as running a command like sudo raspi-config and then selecting the SSH option. This just turns it on, you know.
It's really important to change the default password on your IoT device right away. Many devices come with a standard username and password, like "pi" and "raspberry" for a Raspberry Pi. These are widely known and a huge security risk. Pick a strong, unique password for your device. This single step makes a very big difference in keeping your device safe from unwanted visitors. It's honestly one of the most basic, yet most powerful, things you can do.
Establishing a P2P Connection
Now, for the P2P part. This is where it can get a little bit tricky, but there are free tools that can help. One common way to create a P2P-like connection for remote devices is by using a VPN (Virtual Private Network) service that allows direct device-to-device tunneling, or by using specific P2P networking tools. Some services, like ZeroTier or Tailscale, offer free tiers that help you create a secure, direct network between your computer and your IoT device, no matter where they are in the world. They essentially make your devices act like they are on the same local network, which is very handy.
These P2P networking tools usually involve installing a small piece of software on both your computer and your IoT device. Once installed, you link them together using a unique network ID. This creates that direct, peer-to-peer pathway. Then, you can use your SSH client (like PuTTY) to connect to your IoT device's IP address within that virtual P2P network. It's a clever way to get around typical router problems, you know, and makes things much simpler.
For example, with ZeroTier, once your devices are part of the same virtual network, you can just SSH to the IP address ZeroTier assigns to your IoT device. It’s like magic, almost. This avoids the need for complex port forwarding on your router, which can be a security headache in itself. It’s a very clean and direct way to get that secure connection going, which is rather nice.
Keeping Your System Updated
Remember those warnings about "Your device is at risk because it's out of date and missing important security and quality updates"? This applies to your IoT devices just as much as your computer. Once you have your SSH connection working, make it a regular habit to log in and update your device's software. For Linux-based IoT devices, this often means running commands like sudo apt update and sudo apt upgrade. This keeps everything fresh, you know.
These updates bring important security fixes that patch up any newly discovered weaknesses. Ignoring them is like leaving a window open after you've locked the front door. It just undoes all your good work. So, make sure you schedule regular check-ins to update your IoT devices. It's a pretty straightforward step, but it's incredibly important for ongoing security. This really helps keep things running smoothly and safely.
Common Connection Issues and How to Fix Them
Sometimes, even with the best intentions, you might run into problems. You might get messages like "This connection is untrusted" or "There is a problem connecting securely to this website." These usually point to an issue with how your connection is being verified, or perhaps an outdated security certificate. For SSH, this often means the SSH key fingerprint isn't recognized or has changed. If you see a warning about a host key, and you know you're connecting to the right device, you might need to accept the new key. Just be very sure it's your device, you know.
If you're having trouble connecting at all, first, check your network connection. Is your IoT device powered on and connected to the internet? Is your computer also online? Simple things can sometimes be the biggest hurdles. Next, double-check the IP address of your IoT device within the P2P network. Sometimes these addresses can change, so it's a good idea to confirm. A small typo can stop everything, you know.
Also, make sure the SSH service is actually running on your IoT device. Sometimes it might get turned off after an update, or if the device restarts. A quick login (if you can) or a reboot of the device might fix it. If you're using a P2P networking tool, check its status on both your computer and the IoT device to make sure they are both connected to the virtual network. These little checks can save you a lot of frustration, honestly, and are pretty much the first things to look at.
Frequently Asked Questions (FAQs)
Q1: Why do I keep getting "untrusted connection" warnings when I try to connect to my remote devices?
A1: You know, those warnings often pop up because your device's security certificates are old, or perhaps your browser can't confirm the connection's safety. It can also mean your device's software is out of date. Making sure your device has the latest updates and using secure methods like SSH can often clear these up. It's a pretty common issue, honestly, that just needs a bit of attention.
Q2: Can I really securely connect remote IoT devices using P2P SSH without paying for software?
A2: Yes, absolutely! There are many excellent free and open-source tools available for both SSH clients and P2P networking. Tools like PuTTY for SSH and services like ZeroTier or Tailscale (with their free tiers) let you set up secure, direct connections without spending any money. It just takes a little bit of setup, you know, but the tools themselves are freely available.
Q3: My Windows 11 PIN isn't working to log in. Is this related to device security updates?
A3: While a PIN issue on your Windows login screen isn't directly tied to remote IoT device connections, it does point to a general system health concern. Outdated systems can cause all sorts of strange problems, including login glitches. Making sure your Windows operating system is fully updated is a very good first step to fix many issues, including login problems. It's like giving your computer a fresh start, you know, and helps it run better overall.
Taking the Next Steps for Better Security
Getting your remote IoT devices connected securely with P2P SSH is a very smart move for anyone with smart gadgets. It helps you avoid those annoying "untrusted connection" messages and keeps your data safe from prying eyes. Remember, the digital world changes quickly, so staying on top of security updates for all your devices is really important. It’s an ongoing process, you know, not a one-time fix.
By using free SSH clients and P2P networking tools, you can build a robust, secure link to your remote gadgets without breaking the bank. It gives you direct control and a lot more confidence in your remote operations. So, go ahead, give it a try. Your devices, and your peace of mind, will thank you for it. It's a pretty good step to take for your overall digital safety, you know, and it's quite empowering.
For more detailed technical guides and community support, you might find helpful resources on the OpenSSH project website. It's a great place to learn more about how SSH works and how it can protect your connections. Jerrywoods2 and marcelo_p, who have shared their experiences and insights, remind us that community knowledge is a valuable thing, so it's worth checking out.
- Two Person Yoga Poses
- Abbey Love On The Spectrum
- Somber Smithing Stone 6
- Grab The Mic Game
- Jamaican Restaurants Near Me
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide