Securely Connect Remote IoT P2P SSH: A Free Download Guide For Your Devices
Connecting to your remote devices, especially those little IoT gadgets, can feel like a real puzzle, can't it? You want to check on your smart home sensors, maybe adjust something on your Raspberry Pi that's far away, or perhaps manage an industrial IoT setup without being right there. This is where the idea of securely connecting remote IoT devices using P2P SSH comes into play, and the good news is, you can often do it with free tools. It's about getting that important access while keeping everything safe from prying eyes, so that's pretty neat, isn't it?
For many people, the thought of reaching out to a device that isn't on their immediate network brings up worries about security. How do you make sure only you can get in? How do you avoid leaving a digital door wide open for others? This article guides you through the process of securely connecting remote IoT devices using P2P SSH on Windows, specifically focusing on free tools and resources, so you can feel good about your connections.
This comprehensive guide dives deep into the concept of securely connecting your gadgets, showing you how P2P SSH works and exploring its many benefits. Whether you're an experienced network administrator or a novice IoT enthusiast, this guide will provide you with the necessary information and resources to secure your remote connections, offering a comprehensive overview of the necessary steps and tools to safely connect your Raspberry Pi in a remote IoT P2P environment, too. It's really quite helpful, you know.
- Sophie Rain Spiderman Video
- What Is Boba Made Of
- Caramel Highlights On Brown Hair
- Moth Grow A Garden
- Business Class Vs First Class
Table of Contents
- What is Remote IoT and P2P SSH?
- Getting Started: Securely Connect Remote IoT P2P SSH Free Download
- Step-by-Step Guide to Secure Connection
- Best Practices for Ongoing Security
- Common Questions About Secure IoT Connections
- Conclusion
What is Remote IoT and P2P SSH?
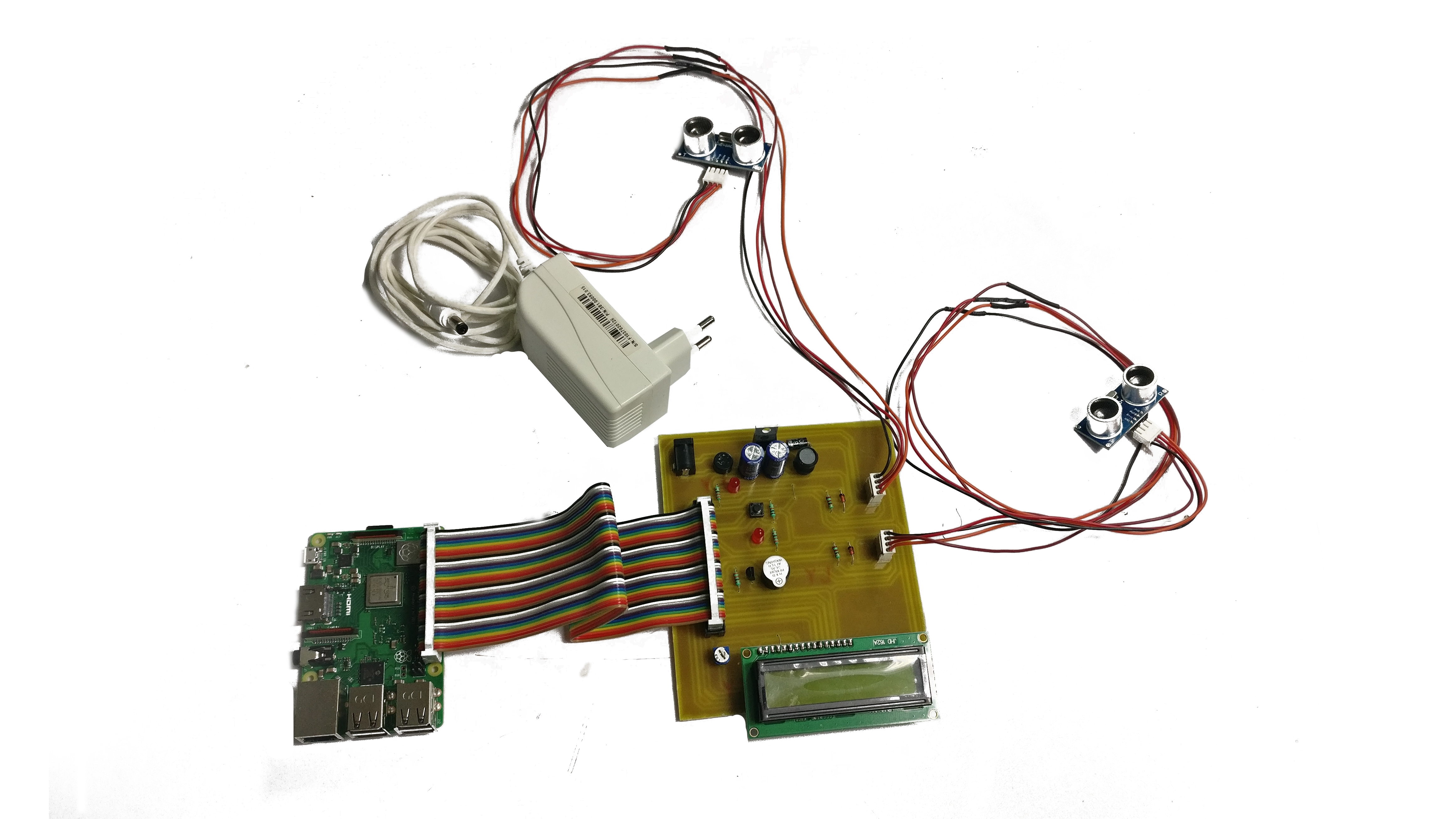
Remote IoT, in simple terms, means having your internet-connected things, like sensors or small computers, placed somewhere far away from you. You might have a weather station in your garden, or a security camera at a vacation home, or even a network of industrial sensors in a factory. These are all examples of remote IoT devices. You need a way to reach them, to get their data, or to send them commands, without physically being there, so that's what we're talking about, really.
P2P SSH, which stands for Peer-to-Peer Secure Shell, is a method that lets two devices talk directly to each other over a secure, encrypted channel. Think of it like a private, secret tunnel built just for your devices to communicate. Instead of going through a central server that might cost money or add extra steps, P2P SSH lets your device at home connect straight to your remote IoT device. This guide will walk you through everything you need to know about securely connecting to your Raspberry Pi using remote IoT P2P SSH, including the download process, so it's very helpful.
How P2P SSH Works
SSH, by itself, creates a secure connection for command-line access. It's like having a secure remote control for your computer. When you add the "P2P" part, it means the connection tries to go directly from your computer to the remote IoT device. This can be a bit tricky because of things like firewalls or different network setups, but special tools help make this direct link happen. The process involves creating a safe and direct pathway between your local machine and the distant device, which is quite clever, you know.
- Surrealism Dress To Impress
- Wasmo Somali Channel Telegram 2025
- Is Clarke From Love Island Trans
- What Does Nvm Mean
- Costco Dinner Kit Chicken Taco
This approach often uses a technique called "hole punching" or a small, lightweight relay to help the two devices find each other and establish that direct link. Once the connection is made, all the data that travels between them is encrypted, meaning it's scrambled and unreadable to anyone else. This keeps your information private and your commands safe. As we delve deeper into the topic of securely connecting remote IoT devices using P2P SSH downloads, we will explore the intricacies of setting up secure connections, so it's a good thing to learn.
Why Security Matters for IoT
Security for IoT devices is super important, honestly. These devices are often connected to your home network, or even to critical systems in businesses. If someone who shouldn't have access gets into one of your IoT devices, they could potentially spy on you, mess with your settings, or even use your device to launch attacks on other parts of the internet. That's a pretty big deal, you know.
Using a secure method like P2P SSH helps protect against these risks. It ensures that only authorized people can access your devices and that the information exchanged is kept private. A comprehensive guide to securely connecting your Raspberry Pi to a remote IoT network using P2P SSH necessitates robust SSH configuration, so learning how to implement SSH for better security is key. It's about peace of mind, really, knowing your devices are safe.
Getting Started: Securely Connect Remote IoT P2P SSH Free Download
If you're determined to securely connect remote IoT P2P downloads on Windows 10, this guide will walk you through the entire process, step by step. The first thing you'll want to do is figure out what tools you'll use. There are many free options out there that can help you get this done without spending a dime. It's pretty cool how much is available, actually.
This article guides you through the process of securely connecting remote IoT devices using P2P SSH on Windows, specifically focusing on free tools and resources. You don't need expensive software to make this work. A bit of know-how and some freely available programs are usually all you need to get started. So, that's a good place to begin, isn't it?
Choosing Your Tools
For securely connecting remote IoT devices using P2P SSH, you'll need a few pieces of software. On your local computer, you'll likely use an SSH client. PuTTY is a very popular free choice for Windows users, and it's been around for a long time. For the P2P part, you might look into tools that help with direct connections through firewalls, like ZeroTier or ngrok, which often have free tiers for personal use. This guide will walk you through the process of securely connecting your Raspberry Pi in a remote IoT P2P environment, complete with a free download option for the essential tools, so it's all covered.
When choosing, think about what operating system your remote IoT device uses. If it's a Raspberry Pi running Linux, then OpenSSH is usually built right in, which makes things a bit simpler. For Windows IoT Core, you might need to enable an SSH server. The key is finding tools that are well-supported and have good documentation, so you know how to use them, you know.
Preparing Your Devices
Before you can securely connect remote IoT P2P SSH free download, you need to get both your local computer and your remote IoT device ready. For your IoT device, this often means making sure it's powered on, connected to the internet, and has an SSH server running. For a Raspberry Pi, this is usually a simple command to enable SSH, which is very handy.
On your local computer, you'll need to install your chosen SSH client, like PuTTY, if you don't already have it. You'll also want to make sure your network settings aren't blocking outgoing SSH connections, though this is less common for home users. This guide is designed to offer a comprehensive overview of the necessary steps and tools to safely connect your Raspberry Pi in a remote IoT P2P environment, so you'll be well-prepared, honestly.
Step-by-Step Guide to Secure Connection
This article has served as your guide, steering you through the process of securely connecting remote IoT devices via P2P SSH on Windows, encompassing all the necessary steps. We'll go through the general steps here, but remember that specific details might vary a little depending on your exact devices and chosen tools. It's usually pretty similar, though, so that's good.
The main idea is to get your remote device ready to accept an SSH connection, then set up a way for your local computer to find and connect to it directly. This might involve setting up a P2P network overlay or using a service that helps bridge the connection. It's a fairly logical sequence of actions, you know.
Setting Up SSH on Your IoT Device
For most Linux-based IoT devices, like a Raspberry Pi, setting up SSH is quite simple. You'll typically log into the device locally (with a keyboard and screen, or over your local network) and run a command to enable the SSH server. You might also want to change the default password for the 'pi' user, or even create a new user, which is a very good security practice, by the way.
If your device is running Windows IoT Core, you'll need to enable the SSH feature through its settings or command line. It's about making sure the SSH service is active and listening for incoming connections. This guide will walk you through everything you need to know about securely connecting to your Raspberry Pi using remote IoT P2P SSH, including the download process, so you'll find the specific instructions there, too.
Configuring P2P Connection
This is where the "P2P" part really comes into play. If you're using a tool like ZeroTier, you'll install the ZeroTier client on both your local computer and your remote IoT device. Then, you'll join both devices to the same virtual network. ZeroTier helps them find each other and communicate as if they were on the same local network, even if they're miles apart. It's pretty clever how it works, honestly.
Once they're on the same virtual network, your IoT device will get a virtual IP address. You can then use your SSH client on your local computer to connect to that virtual IP address. This bypasses many of the traditional network hurdles, making it much easier to securely connect remote IoT devices using P2P SSH. It's surprisingly straightforward once you get the hang of it, you know.
Testing Your Secure Link
After you've set up SSH on your IoT device and configured your P2P connection, it's time to test it out. From your local computer, open your SSH client (like PuTTY). Enter the virtual IP address of your remote IoT device and the SSH port (usually 22). Then, try to connect. If everything is set up correctly, you should be prompted for a username and password, which is a very good sign.
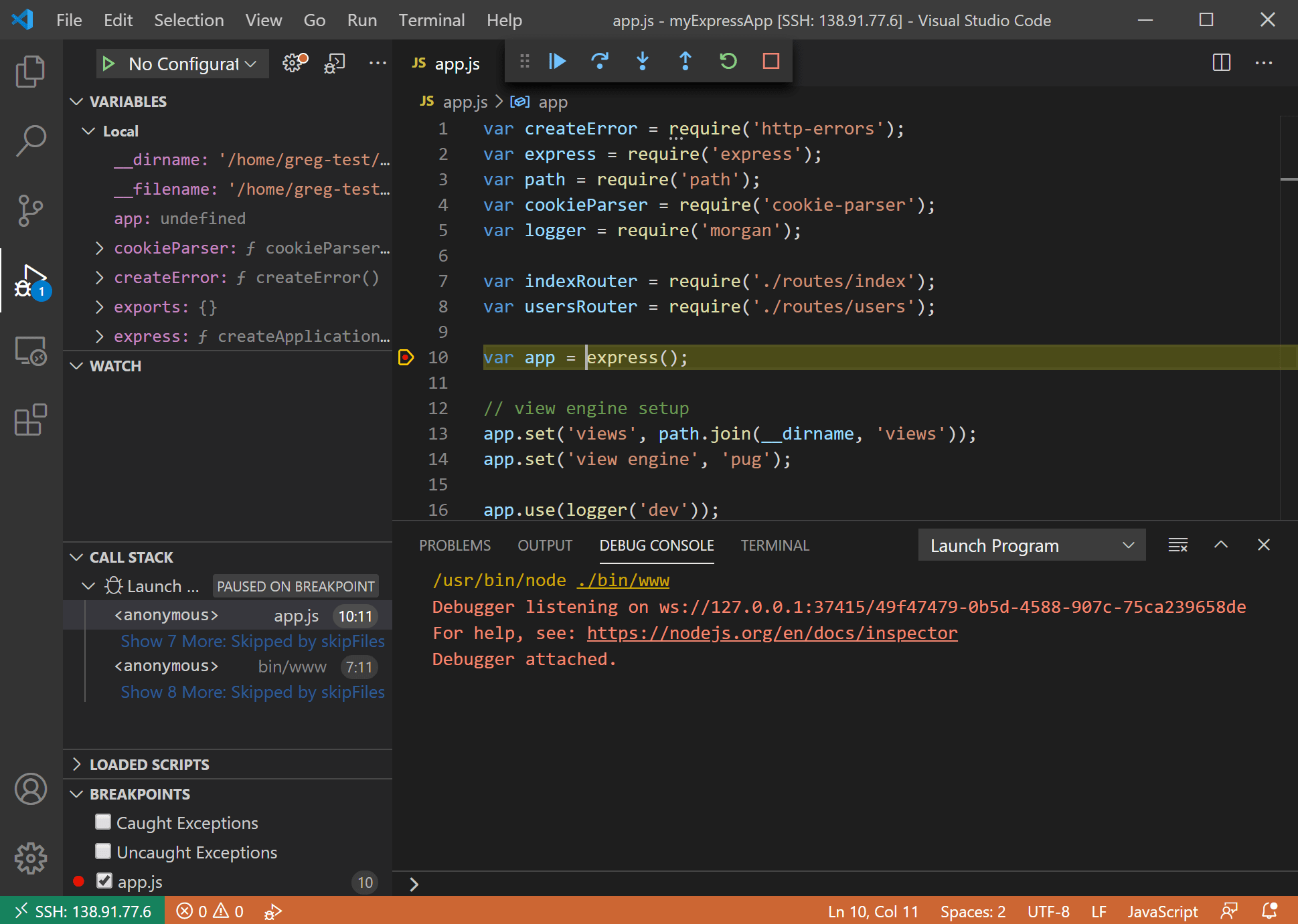
Once you log in, you'll have a secure command-line interface to your remote IoT device. You can run commands, check files, or manage services, all from afar. This article explores the best methods to securely connect remote IoT devices via P2P SSH, and testing is a critical step to ensure your setup is working as it should, so make sure you do it.
Best Practices for Ongoing Security
Securely connecting remote IoT devices using P2P SSH is not only possible but also incredibly beneficial. By following the steps outlined in this guide, you can set up a secure, cost-effective way to manage your devices. But security isn't a one-time thing; it needs ongoing attention. Keeping your connections safe means staying vigilant, you know.
Even with a good initial setup, new threats appear all the time. So, it's a good idea to regularly check your settings and make sure your software is up to date. This proactive approach helps keep your remote IoT devices protected against potential risks, which is pretty important, actually.
Keeping Software Current
One of the simplest and most effective ways to maintain security is to keep all your software updated. This includes the operating system on your IoT device (like Raspbian for Raspberry Pi), your SSH client on your local computer, and any P2P networking tools you're using. Software updates often include security patches that fix newly discovered weaknesses, so that's really important, you know.
Make it a habit to check for updates regularly. For Linux-based systems, a simple `sudo apt update && sudo apt upgrade` command can often do the trick. For Windows, make sure your system updates are enabled. This little bit of effort goes a long way in keeping your connections secure, so it's worth the time, honestly.
Strong Passwords and Keys
When you set up SSH, you'll use either a password or SSH keys for authentication. Passwords should always be long, complex, and unique. Avoid using easy-to-guess words or common phrases. A better approach, however, is to use SSH key pairs. This involves creating a public key on your IoT device and a private key on your local computer. The private key never leaves your local machine, and it's much harder for someone to guess than a password, so it's a very good idea to use them.
If you do use SSH keys, make sure your private key is protected with a strong passphrase. This adds an extra layer of security, meaning even if someone gets hold of your private key, they still can't use it without the passphrase. It's a bit like having two locks on a door, which is pretty smart, you know.
Monitoring Your Connections
It's a good idea to occasionally check who is connecting to your remote IoT devices. Most operating systems keep logs of SSH login attempts. You can review these logs to look for any suspicious activity or failed login attempts that might suggest someone is trying to gain unauthorized access. This guide will walk you through everything you need to know about securely connecting remote IoT P2P SSH on Windows 10, ensuring you can manage your devices with a good sense of security, so checking logs is part of that.
If you see anything unusual, it's a sign to change your passwords or SSH keys immediately. Being aware of who is accessing your devices helps you stay on top of your security. Learn how to securely connect remote IoT P2P SSH free download and enhance your remote device management by including monitoring in your routine, too. It's a simple step that can make a big difference, honestly.
Common Questions About Secure IoT Connections
Is it really safe to use P2P SSH for my IoT devices?
Yes, when set up correctly, P2P SSH can be very safe for your IoT devices. The "SSH" part means the connection is encrypted, making it hard for others to snoop on your data. The "P2P" part means you're often connecting directly, which can sometimes reduce reliance on third-party servers. It's about using strong passwords or, better yet, SSH keys, and keeping your software updated, you know. That's how you keep it safe.
Do I need a special router or network setup for P2P SSH?
Not usually for the P2P SSH part itself. Traditional SSH often needs port forwarding on your router, which can be tricky. However, P2P tools like ZeroTier create a virtual network that bypasses most router configurations. This means your devices can find each other without you needing to change complicated router settings, which is pretty convenient, actually. You just need an internet connection for both devices.
Can I use this method for any type of IoT device?
Generally, yes, if the IoT device can run an SSH server and the P2P client software. This is very common for devices like Raspberry Pi, Arduino boards running Linux, or even some industrial controllers. Smaller, very simple IoT devices that don't have a full operating system might not be able to support SSH directly. But for most programmable IoT devices, it's a very viable option, so that's good.
Conclusion
Connecting remote IoT devices securely using P2P SSH is incredibly beneficial. This article has served as your guide, steering you through the process of securely connecting remote IoT devices via P2P SSH on Windows, encompassing all the necessary steps. You've seen that it's not only possible but also surprisingly straightforward to get your remote gadgets talking to you safely, often with free tools. It really opens up a lot of possibilities for managing your devices from anywhere, which is pretty cool, you know.
Whether you're an experienced network administrator or a novice IoT enthusiast, this comprehensive guide will provide you with the necessary information and resources to secure your remote connections. By following the advice about choosing the right
- How Tall Is The Rock
- How To Make Birria Tacos
- Jasmine Crockett Husband
- Help I Accidentally Summoned Mahoraga
- Can You Eat Crocs
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide

Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide