SSH Into IoT Device Example: Your Guide To Secure Remote Access
Connecting to your Internet of Things (IoT) devices from afar is a pretty big deal these days. Picture this: you have smart gadgets scattered around, maybe at home, or perhaps in an industrial setting, and you need to keep an eye on them, maybe even change how they work. Typically, a person overseeing these devices uses some kind of software or an app to check on each one from a central spot. From that control center, administrators can tweak machine settings, which is rather convenient.
This kind of remote surveillance of smart technology as it operates together is what we call IoT remote monitoring. It helps people see the status of devices and make adjustments without having to be right there with them. You know, it's just a practical way to keep things running smoothly, even if you are not physically present, which can be a real time-saver, so to speak.
For truly secure oversight and management of these gadgets from a distance, an IoT remote SSH connection is a perfect choice. This guide will help you learn how to set up this kind of connection. We will go over how to safely connect to an IoT device using SSH, giving you a way to reach its functions and settings. You'll gain good control and be able to fix things with a bit more ease, honestly.
- Do Female Cats Spray
- Camarones A La Diabla
- Boo Did I Scare You Im A Job Application
- What Does Body Count Mean
- Mikafans Leaks
Table of Contents
- What is SSH and Why It Matters for IoT?
- The Basics of Remote IoT Monitoring
- Preparing Your IoT Device for SSH Access
- A Practical SSH into IoT Device Example: Raspberry Pi
- Securely Connecting to Your IoT Device
- Managing and Troubleshooting with SSH
- When SSH Might Not Be Enough: Scalable Alternatives
- Advanced SSH Techniques for IoT
- Important Security Considerations
- Frequently Asked Questions
- Wrapping Things Up
What is SSH and Why It Matters for IoT?
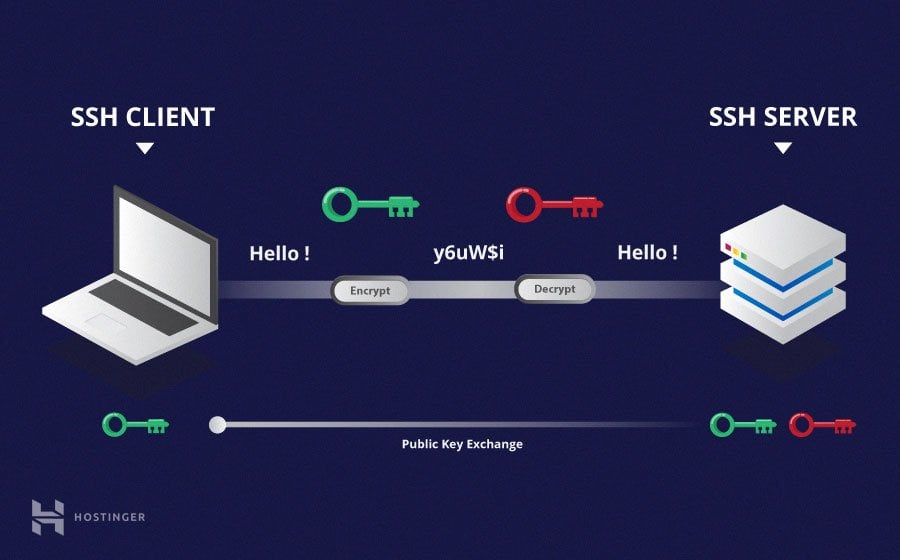
Secure Shell, or SSH, is a network protocol that gives you a secure way to operate network services over an unsecured network. Think of it as a secret tunnel for your data, keeping it safe from prying eyes. For IoT devices, this means you can get to the device's command line from far away. This is incredibly helpful for managing settings, updating software, or just keeping an eye on things, you know, from anywhere.
SSH provides a solid way to deal with the challenge of remote access, setting up encrypted communication paths between devices. This guide will explain what you need to know about SSH, which is pretty much everything for this topic. It shows how Secure Shell can be used to keep sensitive information safe when it travels across networks. This article will look at why this is so important, too it's almost a necessity for modern setups.
The ability to use SSH with IoT devices, from smart home gadgets to big industrial sensors, makes sure you keep control and security. In this article, we'll look at an example of how to set up SSH for an IoT device, going into some of the finer points. This helps you maintain a strong hold on your device's functions, which is really what you want, in a way.
- What Is A Torta
- Is Clarke From Love Island Trans
- Jamaican Restaurants Near Me
- Morty And Rick Cast
- Deep Winter Color Palette
The Basics of Remote IoT Monitoring
IoT remote monitoring, as we discussed, means watching smart technology work together. An administrator usually uses a software program or an application to see the status of each IoT device from a central digital control center. From this spot, administrators can change machine settings. This centralized view is pretty handy, as a matter of fact, for keeping track of many devices.
This kind of oversight is key for monitoring, checking, and even fixing industrial machinery, vehicle fleets, and home automation devices from distant spots. It's especially useful when people can't easily get to the devices themselves. Remote access for IoT, or something like Raspberry Pi remote SSH access, is what makes this kind of management possible, you know.
The Internet of Things has changed how people interact with objects in connected environments; IoT devices seem to be everywhere now. Being able to remotely SSH and manage these devices over the internet has made interacting with IoT devices much easier. It's a fundamental shift, allowing for more flexible operations, which is quite useful, honestly.
Preparing Your IoT Device for SSH Access
Before you can connect to your IoT device using SSH, you need to make sure it's ready. This usually means the device needs to be running a suitable operating system, like a version of Linux, and it needs to be connected to a network. Often, you'll need to enable the SSH service on the device itself. This is typically a straightforward process, but it varies slightly depending on the device you're using, so be prepared for a little bit of variation.
For instance, if you're using a Raspberry Pi, which is a very common IoT device for these kinds of projects, enabling SSH is usually just a few commands away or a quick setting change in its configuration tools. This initial setup is a very important step because without SSH enabled, you simply won't be able to make that secure connection from your computer. It's kind of like making sure the door is unlocked before you try to walk through it, you know.
You might also need to think about network settings, like ensuring your device has a stable IP address or that your router allows incoming connections if you plan to access it from outside your local network. These network considerations are pretty important for a reliable connection. This guide will walk you through the basics of SSH, how it applies to IoT, and provide real examples of setting up remote SSH for IoT devices, showing why free IoT access is so valuable, actually.
A Practical SSH into IoT Device Example: Raspberry Pi
Let's walk through an example using a Raspberry Pi, a popular choice for many IoT projects. First, make sure your Raspberry Pi has its operating system installed, like Raspberry Pi OS. You can enable SSH either by creating an empty file named `ssh` (no extension) in the boot partition of the SD card before you even start the Pi, or by using the `raspi-config` tool once the Pi is running, which is pretty simple to do.
Once SSH is enabled on your Raspberry Pi, and it's connected to your local network, you'll need its IP address. You can find this by logging into your router's administration page or by running a command like `hostname -I` directly on the Raspberry Pi. Knowing this IP address is really important because it's how your computer will find the Pi on the network, as a matter of fact.
From your computer, you'll open a terminal (on Linux/macOS) or use a program like PuTTY (on Windows). The command to connect is typically `ssh username@ip_address_of_pi`. For a new Raspberry Pi, the default username is often `pi`. So, you might type `ssh pi@192.168.1.100` (replacing the IP with your Pi's actual address). You'll then be asked for the password, which is usually `raspberry` by default. And just like that, you're in! You can now type commands directly into your Pi, which is quite useful, honestly.
Securely Connecting to Your IoT Device
After you get the basic connection working, making sure it's secure is the next big step. Using strong passwords is a good start, but key-based authentication is much safer. With key-based authentication, you generate a pair of keys: a public key that goes on your IoT device and a private key that stays on your computer. When you try to connect, your computer uses the private key to prove its identity to the device, and the device verifies it with the public key. This method is far more secure than just a password, you know.
To set this up, you'd typically use a command like `ssh-keygen` on your computer to create the keys. Then, you'd copy the public key to your IoT device using `ssh-copy-id`. This process removes the need to type a password every time you connect, making it faster and much more secure. It's a pretty standard practice for serious remote access, and it helps a lot with keeping things safe, in a way.
Also, think about firewalls. Using firewalls is a common way to protect and secure access to IoT devices. Yet, it's challenging to get to and manage devices that are deployed in distant places, behind firewalls that block connections. You might need to set up port forwarding on your router or use more advanced techniques like reverse SSH tunnels if your device is behind a strict firewall or NAT. This is a very important consideration for reliable and safe access, obviously.
Managing and Troubleshooting with SSH
Once you're connected to your IoT device via SSH, you have pretty much full control over its command line. This means you can do a lot of things. For example, you can change settings by editing configuration files, update the device's software by running package manager commands (like `sudo apt update` and `sudo apt upgrade` on a Linux-based device), or install new applications. It's a very direct way to interact with your device, you know.
Monitoring the device's health and performance is also straightforward. You can check resource usage (like CPU, memory, and disk space) with commands such as `top` or `df -h`. You can also view system logs to troubleshoot issues or see what the device has been doing. If a sensor isn't reporting data correctly, or if an application crashes, the logs can give you clues. This ability to get right into the device's core is incredibly useful for keeping things running smoothly, honestly.
Troubleshooting becomes much simpler too. If a device isn't responding or acting strangely, you can use SSH to restart services, check network connectivity, or even reboot the device remotely. This saves you from having to physically go to the device, which can be a huge benefit, especially if your IoT devices are spread out or in hard-to-reach places. It's a very practical tool for administrators and developers, really.
When SSH Might Not Be Enough: Scalable Alternatives
While SSH is a fantastic tool for connecting to individual IoT devices, especially for beginners or small setups, it has its limits when you start to grow. For small and medium-sized businesses (SMBs), relying solely on direct SSH connections for many devices can quickly become tricky to manage. It's just not built for managing hundreds or thousands of devices at once, you know.
When you have a lot of devices, keeping track of all their IP addresses, managing SSH keys for each one, and ensuring consistent security policies across the board can get complicated fast. This is why many organizations, particularly SMBs, often outgrow simple SSH setups for remote access. They need something more scalable and centralized, which is pretty much the next step for larger operations.
For bigger deployments, cloud-based IoT platforms offer more advanced solutions. Services like AWS IoT or Azure IoT Hub Device Streams provide ways to securely access IoT devices, offering features like centralized device management, identity services, and even secure tunnels without needing direct SSH connections from your local machine. These platforms help manage security and access on a much larger scale, which is quite different from individual SSH, as a matter of fact. Learn more about on our site.
Advanced SSH Techniques for IoT
Beyond basic direct connections, SSH offers some more advanced techniques that are very useful for IoT devices, especially when dealing with tricky network setups. One powerful method is reverse SSH tunneling. This technique helps you access devices that are behind a NAT router or a firewall, which often block incoming connections. With a reverse tunnel, the IoT device itself initiates an outgoing connection to a publicly accessible server, creating a tunnel that you can then use to connect back to the device. This is a very clever way to get around network restrictions, you know.
For example, SocketXP provides SSH-based reverse proxy tunnels to remotely access and control Raspberry Pi and IoT devices behind NAT routers or firewalls. This means even if your device is on a private network, you can still get to it from anywhere. This guide will walk you through everything you need to know about remotely SSHing into an IoT device using AWS, complete with practical examples and actionable insights. It's a pretty comprehensive approach, honestly.
Another advanced use involves integrating SSH access with cloud services. For instance, in this article, we’ll look closely at how you can SSH into an IoT device from anywhere using AWS. We'll cover everything from setting up your environment to keeping it secure. Using AWS IoT, you can set up secure connections and manage your devices through a cloud console, which adds another layer of control and scalability. This is a very powerful combination for large-scale IoT projects, as a matter of fact.
Important Security Considerations
Security is a very big deal when it comes to IoT devices and remote access. Hackers often look for weak security in IoT gadgets to create large networks of compromised devices, known as botnets. These botnets can then be used to launch powerful attacks, like Distributed Denial of Service (DDoS) attacks. So, making sure your SSH connections are secure is not just about protecting your device, but also about protecting the wider internet, you know.
Always change default passwords on your IoT devices immediately after setting them up. Default credentials are a very common entry point for attackers. Using strong, unique passwords for each device is a must, but as mentioned earlier, moving to SSH key-based authentication is even better. It significantly reduces the risk of unauthorized access. This is a pretty fundamental security practice, honestly.
Keeping your device's software up to date is another critical security measure. Software updates often include patches for known vulnerabilities. Regularly updating your IoT device's operating system and any applications running on it helps close potential security holes that hackers might try to exploit. By following these steps and best practices, you can make sure your SSH into IoT devices is a powerful tool that enables secure and efficient remote management, which is quite important, you know. You can learn more about Secure Shell (SSH) in Internet of Things (IoT) devices and how it ensures secure communication and remote access by checking out this page .
Frequently Asked Questions
How can I make my SSH connection to an IoT device more secure?
To make your SSH connection safer, you should absolutely change the default password right away. Even better, switch to using SSH key-based authentication instead of passwords. This involves creating a pair of cryptographic keys, putting the public key on your device and keeping the private key secure on your computer. It’s a much stronger way to prove who you are, as a matter of fact.
What if my IoT device is behind a firewall or NAT? Can I still SSH into it?
Yes, you can often still connect, but it might need a few extra steps. If your device is behind a firewall or a NAT (Network Address Translation) router, direct incoming SSH connections might be blocked. In these cases, you can set up port forwarding on your router or use a technique called reverse SSH tunneling. Reverse tunnels have the IoT device make an outgoing connection to a public server, creating a path back for you to connect through, which is pretty clever, honestly.
Are there alternatives to SSH for remote IoT device management, especially for many devices?
Yes, there are. While SSH is great for individual devices, managing a large number of them this way can get tricky. For bigger setups, cloud-based IoT platforms like AWS IoT or Azure IoT Hub offer more scalable solutions. These platforms provide centralized ways to manage devices, handle security, and even offer secure remote access features without needing direct SSH connections to each device. They are pretty much designed for larger scale operations, you know.
Wrapping Things Up
This comprehensive guide was put together to help beginners get started with connecting to IoT devices using SSH. We covered the basic ideas, how to set things up, good practices, and important security points. Thanks to SSH, administrators and developers can get to an IoT device’s command line from far away. This can be needed to handle settings, update software, or keep an eye on things, which is very useful, really.
From smart home devices to industrial sensors, the ability to SSH into IoT devices helps you keep control and security. In this article, we explored an example of SSH into IoT device setups, looking closely at how it works. With this guide, you now have the basic knowledge to start connecting to your IoT devices safely using SSH and to make your projects bigger effectively, you know.
SSH offers a strong way to handle this challenge, giving encrypted ways for devices to talk to each other. This guide covered everything you need to know about SSH in this context. It showed practical examples of putting remote SSH to use for IoT devices. This kind of remote access over the internet has made interacting with IoT devices much easier, which is pretty much a big step forward, honestly. For more general information on SSH, you can visit the official SSH Academy.
- Jon Gruden Past Teams Coached
- What Is Boba Made Of
- Who Won The Voice 2025
- What Does Body Count Mean
- Jackerman Mother Warmth
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

Windows SSH Server | Learning, Secure shell, Software engineer