SSH RemoteIoT Tutorial: Securely Accessing Your Devices From Anywhere
It feels like devices are connecting to the internet more and more every day, doesn't it? So, it's almost a given that you'd want to keep an eye on them, even when you're not right there. This is where a really helpful tool called SSH comes into play, making it possible to manage your internet of things (IoT) gadgets from almost anywhere.
This SSH RemoteIoT tutorial is all about helping you get comfortable with securely reaching your smart devices. As IoT keeps growing in popularity across so many areas, having a safe way to check on things from afar becomes super important. Whether you're someone who creates new things with technology, an IT person, or just someone who loves tech and wants to see how things work, this guide will show you the way.
You see, SSH, or Secure Shell, has been around for a while, but using it with IoT is somewhat new. With more and more devices getting connected, the need for safe ways to talk to them just keeps getting bigger. This tutorial, you know, will guide you through setting up and using SSH for your remote IoT devices, making sure your connections are private and sound.
- How Old Is Harper Zilmer
- Goob From Meet The Robinsons
- What Is Boba Made Of
- How To Make Stickers
- Abbey Love On The Spectrum
Table of Contents
- What is SSH and Why It Matters for IoT?
- Getting Your IoT Device Ready for SSH
- Setting Up SSH on Your IoT Device
- Accessing Your IoT Device Remotely
- Common Issues and Simple Fixes
- Best Security Practices for SSH IoT
- Conclusion
- Frequently Asked Questions (FAQs)
What is SSH and Why It Matters for IoT?
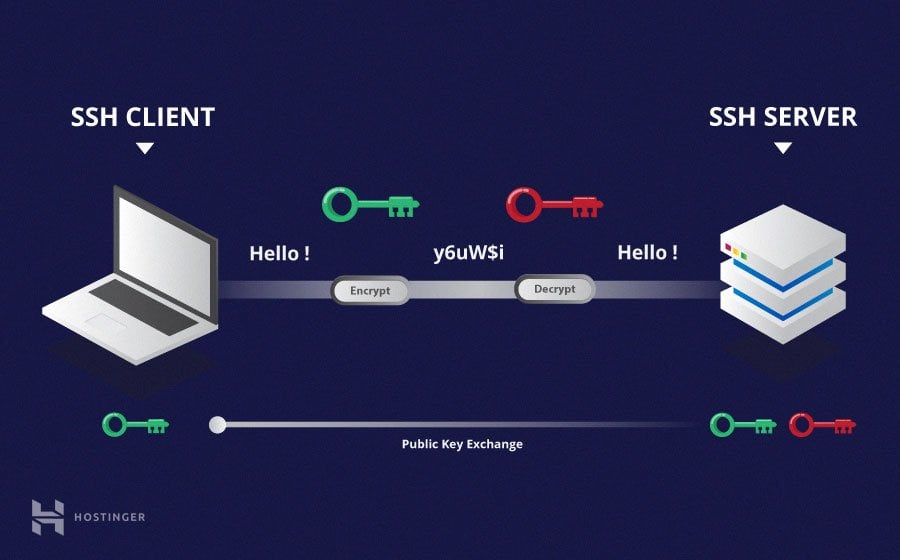
So, you might be wondering, what exactly is SSH? Well, SSH, which stands for Secure Shell, is a way to get into another computer over a network, but it does it in a really safe way. It creates a secure tunnel, you know, making sure that anything you send back and forth is kept private and can't be spied on. This is super important for things like managing servers, and it turns out, it's just as good for your little IoT gadgets.
The Foundation of Secure Remote Access
Think of SSH as a secret handshake between your computer and your IoT device. It's the very basis of secure remote access, providing an encrypted way for them to talk. This means that when you're giving commands to your smart light or checking on your remote sensor, those messages are scrambled, so only your device and your computer can truly understand them. It's, like, a fundamental building block for keeping your digital life safe.
This tutorial is designed to walk you through every step, from getting SSH ready on your IoT device to sorting out common little problems that might pop up. Whether you're a tech fan, a hobbyist, or just curious about IoT, this article will help you get a good grip on things. It truly offers a robust solution for accessing and controlling IoT devices from anywhere in the world, which is quite handy.
- Baby Alien Fan Bus
- 6 Guard Buzz Cut
- How Did Mr Beast Get Rich
- Steve Horstmeyer Dogs
- Emily Compagno Husband
Why SSH is Perfect for IoT
IoT devices, you know, are often out there in the real world, maybe in your home, a garden, or even a factory. They need a reliable and safe way to be managed from afar. SSH provides a strong and encrypted way to get into and control these devices. It's pretty much essential for developers, network administrators, and IoT enthusiasts who want to keep their devices secure.
The remoteIoT web SSH tutorial is here to change how you interact with your devices, making it seamless and secure. When you use SSH with IoT platforms, it gives you a safe path for remote access, letting you tell your devices what to do, even if you're miles away. This is, arguably, a big deal for peace of mind.
Getting Your IoT Device Ready for SSH
Before we jump into setting up SSH, we need to make sure your IoT device is ready for the task. This usually means having the right kind of device and getting it set up with its basic operating system. It's a bit like preparing the ground before you plant something, you know, making sure everything is just right.
Choosing the Right IoT Device
For this SSH RemoteIoT tutorial, we'll often talk about devices like the Raspberry Pi, which is a very popular choice for IoT projects. These small computers are pretty good because they're flexible and can run a full operating system, which makes setting up SSH much easier. You could use other devices too, but a Raspberry Pi is a great place to start, as a matter of fact.
Many platforms allow you to remotely SSH into IoT devices, but the core ideas remain similar. The goal is to have a device that can run a version of Linux or a similar system, where you can install and manage software. So, picking a device that supports this is, like, the first big step.
Initial Setup on Your IoT Device
Once you have your IoT device, you'll need to get its operating system up and running. For a Raspberry Pi, this typically involves putting the operating system onto a memory card and then booting up the device. You'll want to make sure it's connected to your local network, perhaps with a cable or Wi-Fi, you know, so it can talk to other devices.
You might need to open the terminal on your Raspberry Pi, or access it using SSH on your local network if you've already done some basic setup. This initial connection lets you start installing the necessary services for remote access. It's pretty much the starting point for everything else we'll do.
Setting Up SSH on Your IoT Device
Now comes the main part: getting SSH ready on your IoT device. This involves installing the right software and then making a few changes to how it works to make it more secure. It's not too hard, honestly, but paying attention to the details here will save you headaches later.
Installing the SSH Server
The first thing you'll need to do is install the SSH server software on your IoT device. For most Linux-based devices, this is a straightforward command in the terminal. You'll usually use a package manager, like 'apt' on Debian-based systems (like Raspberry Pi OS), to fetch and install the software. So, you might type something like `sudo apt update` and then `sudo apt install openssh-server`.
After the installation, the SSH server should start running automatically. You can usually check its status to make sure it's active. This step, you know, makes your IoT device ready to listen for incoming SSH connections from your computer. It's basically opening a secure door.
Configuring SSH for Better Security
While SSH is secure by default, there are some changes you can make to make it even safer. One common suggestion is to change the default port that SSH listens on, which is typically port 22. Changing it to a different, less common port can help avoid automated attacks that look for SSH on its usual spot. You'll edit a configuration file, often located at `/etc/ssh/sshd_config`, to make these adjustments, you know.
Another really important security measure is to disable password logins and only allow access using SSH keys. This is a much stronger way to authenticate, as keys are much harder to guess or crack than passwords. This guide will walk you through configuring SSH on your remote IoT devices, sorting out common issues, and putting in place the best security steps. By the end of this, you'll have a much safer setup.
User Accounts and Permissions
It's a good idea to create a separate user account on your IoT device for SSH access, rather than using the default 'pi' user or 'root' user. This helps limit what someone can do if they somehow get access. You'll also want to make sure that the permissions on your SSH configuration files and keys are set correctly, so only the right people can read or change them. This is, you know, a basic but very important security step.
Making sure your user has just enough access to do what's needed, and no more, is called the principle of least privilege. It's a pretty good rule to live by when it comes to security. This tutorial is designed for anyone looking to understand and put into practice SSH for remote IoT access, whether you're a developer, IT professional, or hobbyist.
Accessing Your IoT Device Remotely
Once SSH is all set up on your IoT device, the exciting part begins: connecting to it from your computer, wherever you are. This is where the magic of remote management truly happens. You'll find it's surprisingly simple, you know, once you have the right pieces in place.
Connecting From Your Computer
To connect to your IoT device, you'll open a terminal or command prompt on your computer. The basic command is `ssh username@ip_address`. So, if your username on the Raspberry Pi is 'myiotuser' and its IP address is '192.168.1.100', you'd type `ssh myiotuser@192.168.1.100`. If you changed the SSH port, you'd add `-p` followed by the new port number.
After you type this, if you have set up your keys correctly (more on that next), SSH will use your private key to prove it's you, and you should get a command prompt on your remote IoT device. This means you're connected and can start giving commands, which is pretty cool. This SSH RemoteIoT tutorial is here to help you get the hang of the basics and even more.
Using SSH Keys for Extra Security
SSH keys are a much safer way to connect than passwords. They come in pairs: a public key that goes on your IoT device, and a private key that stays on your computer. When you try to connect, your computer uses the private key to prove its identity to the IoT device, which checks it against the public key. This method is, like, way more secure than just typing a password.
To set this up, you'll typically generate a key pair on your computer and then copy the public key to your IoT device. There are specific commands for this, like `ssh-keygen` and `ssh-copy-id`. If you've ever wondered how to connect your IoT devices securely using SSH, this is, arguably, the ultimate guide for it.
Web SSH for IoT: A Convenient Option
For those who prefer a web browser interface, there are tools and services that offer "web SSH for IoT." These services let you connect to your IoT devices through a web page, which can be very handy if you're on a computer where you can't install SSH client software, or if you just like a visual interface. The remoteIoT web SSH tutorial is your way to seamless and secure remote access to your devices.
RemoteIoT web SSH is an incredible tool that brings together the good things about IoT and SSH to give you safe and efficient remote access. By following the steps outlined in this tutorial, you'll be able to use these handy web-based options. It's, you know, a really nice alternative for many people.
Common Issues and Simple Fixes
Sometimes, things don't go exactly as planned, and you might run into a few bumps when trying to connect via SSH. Don't worry, that's perfectly normal! Most common problems have pretty simple solutions, honestly. We'll go over some of them here.
Connection Problems
If you can't connect, the first thing to check is if your IoT device is actually on and connected to the network. Is it getting power? Is its Wi-Fi connected? You might also want to double-check the IP address of your IoT device; it can sometimes change if your router assigns them dynamically. A quick ping command from your computer to the IoT device's IP address can tell you if they can even see each other, which is a good first step.
Another thing to look at is your firewall settings, both on your computer and on the IoT device itself. Sometimes, a firewall might be blocking the SSH connection. Make sure the SSH port (default 22, or whatever you changed it to) is open. This is, you know, a very common reason for connection troubles.
Authentication Challenges
If you can connect but can't log in, it's usually an authentication issue. This means either your password is wrong, or there's a problem with your SSH keys. If you're using passwords, double-check your typing. If you're using keys, make sure your private key is in the right place on your computer and that the public key is correctly installed on your IoT device in the `~/.ssh/authorized_keys` file.
Also, permissions on the `~/.ssh` directory and the `authorized_keys` file on your IoT device are very important. They need to be set just right, or SSH will refuse to use them for security reasons. This SSH RemoteIoT tutorial a comprehensive guide to secure remote access, will help you sort through these sorts of things.
Performance Tips
Sometimes, SSH connections can feel a bit slow, especially over a less-than-perfect network. You can try a few things to make them snappier. Using SSH keys instead of passwords can speed up the login process. Also, making sure your network connection is stable and has good signal strength can make a big difference.
For more advanced users, looking into SSH client settings like `Compression` or `ControlMaster` can sometimes help with performance for repeated connections. These are, you know, little tweaks that can make your remote management experience feel much smoother.
Best Security Practices for SSH IoT
While SSH is inherently secure, keeping your IoT devices safe means following some smart practices. It's not just about setting it up; it's also about maintaining that security over time. Being a bit careful here can really protect your devices from unwanted visitors.
Strong Passwords and Key Management
If you absolutely must use passwords, make them long, complex, and unique for each device. However, as mentioned, SSH keys are much better. When using keys, protect your private key very carefully; it's like the key to your digital home. Never share it, and consider protecting it with a strong passphrase. This is, you know, a really important step.
Regularly review your SSH keys and remove any that are no longer needed. It's also a good idea to rotate your keys every so often, meaning you generate new ones and remove the old ones. This helps keep your access credentials fresh and harder for anyone to compromise over time. It's a bit like changing the locks on your house every few years.
Firewall Rules and Network Protection
Configure firewalls on your IoT device to only allow SSH connections from specific, trusted IP addresses if possible. This significantly reduces the attack surface. Also, make sure your home or office router's firewall is set up to only forward the SSH port if absolutely necessary, and ideally, use a VPN for remote access instead of directly exposing SSH to the internet. This is, you know, a much safer way to go about it.
Think about segmenting your network, too. Putting your IoT devices on a separate network segment from your main computers can help contain any potential security issues. This SSH IoT remotely tutorial has covered the basics of using SSH for secure remote access to IoT devices, from setting up an SSH server to putting in place advanced security steps.
Regular Updates and Monitoring
Keep your IoT device's operating system and all installed software, including SSH, up to date. Software updates often include security fixes for newly discovered weaknesses. Regularly check the logs on your IoT device for any unusual activity related to SSH logins. Unusual login attempts could mean someone is trying to get in.
Consider setting up automated alerts for failed login attempts or other suspicious events. Being proactive about updates and monitoring is, you know, key to long-term security. This comprehensive guide will walk you through everything you need to know about SSH remote IoT device tutorials, from the basics of SSH to advanced techniques for managing IoT devices. As of today, , these practices remain very relevant.
Conclusion
In short, SSH RemoteIoT is a very powerful tool that gives you secure and efficient ways to manage your IoT devices. By following the steps outlined in this tutorial, you can set up and maintain a safe connection to your gadgets, no matter where you are. The increasing number of connected devices means that tools like SSH RemoteIoT are becoming, you know, truly essential.
This guide has covered everything from the basics of SSH to more advanced techniques and good security habits. Understanding remote IoT SSH is, like, a fundamental skill for anyone involved with smart devices. To learn more about secure remote access on our site, and to explore further details, you can also link to this page IoT Security Best Practices. Secure Shell (SSH) provides a robust and encrypted method to access and control these devices, making your IoT experience much safer.
So, if you're ready to take control of your IoT devices with confidence, start putting these steps into practice. It's a step towards a more secure and manageable smart environment. For more general information about SSH, you might want to check out the SSH Academy for a good reference.
Frequently Asked Questions (FAQs)
What is the main benefit of using SSH for IoT devices? The main benefit is getting a secure and encrypted way to access and control your IoT devices from afar. It keeps your communication private and safe from people who shouldn't see it, which is, you know, very important for security.
Can I use SSH to manage my Raspberry Pi remotely? Yes, absolutely! The Raspberry Pi is a very popular choice for this kind of setup, and this SSH RemoteIoT tutorial covers exactly how to get SSH working on it. It's a pretty common way to manage those little computers.
Is it safe to expose my IoT device's SSH port directly to the internet? It's generally not the safest thing to do. It's much better to use SSH keys instead of passwords, change the default port, and ideally, use a Virtual Private Network (VPN) or a secure web SSH service to connect. This adds extra layers of protection, you know, making things much more secure.
- Securely Connect Remoteiot Vpc Raspberry Pi Aws Server
- 405 Howard Street San Francisco
- Drew Pritchard Divorce
- Tun Tun Tun Sahur
- B Cup Breast Size
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

Windows SSH Server | Learning, Secure shell, Software engineer