RemoteIoT VPC SSH Raspberry Pi AWS: Your Guide To Secure Cloud Connections
Introduction: Bringing Your Raspberry Pi into the Cloud's Secure Embrace
Connecting small, clever devices like the Raspberry Pi to the vastness of the cloud can seem like a big puzzle, but it's actually quite achievable with the right approach. Many organizations, you know, are finding ways to extend their reach, putting computing power closer to where things happen, right at the edge. This setup, with devices talking to cloud services, opens up all sorts of possibilities for gathering information and making things happen remotely, more or less automatically.
For those looking to manage devices that are far away, keeping things safe and sound is a top concern. We often hear about the worries people have when their valuable data travels across the internet or when devices need a little tweak from a distance. It's about making sure only the right people can get in and that the information stays private. That's why figuring out a solid, protected connection is, like, a really big deal for anyone working with remote gadgets.
This article will walk you through how to use a private section of the cloud, known as an AWS VPC, to create a very secure tunnel for your Raspberry Pi using SSH. We'll talk about how this all fits together, why it's a smart move for your projects, and how you can get started. Think of it as building a private, secure road for your little computers to talk to their cloud home, so you can keep tabs on them and make changes from anywhere, basically. We help organizations, you see, make these kinds of transformations happen, giving them the proper tools for their new systems.
- What Does Asl Mean
- 16 Guard Buzz Cut
- Somber Smithing Stone 6
- Sophie Rain Spiderman Vid
- Hannah Love Is Blind
Table of Contents
- Understanding the Core Components
- Why Secure Remote Access Matters for IoT
- Setting Up Your AWS VPC for IoT Devices
- Connecting Raspberry Pi via SSH to VPC
- Managing Multiple Devices and Scaling
- Common Questions About Remote IoT Security
- Moving Forward with Your Secure IoT Setup
Understanding the Core Components
To really get a grip on setting up a secure remote system, it helps to know the main pieces involved. Each part plays a specific role, and when they work together, they create a pretty reliable way to manage your devices. It's like building something with different kinds of blocks, where each block has its own job, you know.
Raspberry Pi: The Edge Device
The Raspberry Pi is a small, affordable computer that's become a favorite for many projects. It's powerful enough to do a lot of tasks, from collecting information to controlling other bits of equipment. People often call it an "edge device" because it sits at the edge of a network, close to where data is created or where actions need to happen, like in a factory or a home. It's quite versatile, actually.
AWS VPC: Your Private Cloud Space
AWS VPC stands for Amazon Web Services Virtual Private Cloud. Think of it as your own isolated section within the larger AWS cloud. You get to define your own network settings, including IP addresses, subnets, and network gateways. This private space means your devices can talk to your cloud resources without being exposed to the public internet, which is a very good thing for security, obviously.
- Remoteiot Monitoring Ssh Download Android
- Kay And Tay Abuse Allegations
- Sophie Rain Height In Feet
- Nice And Slow Lyrics
- Help I Accidentally Forgot How Gravity Works
SSH: The Secure Connection
SSH, or Secure Shell, is a network protocol that allows you to connect to a remote computer over an unsecured network in a very secure way. It provides a strong layer of protection for the communication channel, meaning that anyone trying to listen in won't be able to understand what's being sent. It's basically like having a secret, coded conversation that only you and your device can understand, you know.
RemoteIoT: The Big Picture
When we talk about "RemoteIoT," we're looking at the broader idea of managing and interacting with internet-connected things from a distance. This could be anything from checking the temperature in a remote sensor to updating the software on a fleet of devices spread across different locations. The goal is to have control and visibility without needing to be physically present, which is pretty convenient, really.
Why Secure Remote Access Matters for IoT
Having a secure way to reach your IoT devices isn't just a nice extra; it's truly important. Without proper security, your devices and the information they handle could be at risk. This could mean unauthorized people gaining access, data being stolen, or even devices being taken over for harmful purposes. So, it's something you really need to think about from the start, you know.
Data protection: Many IoT devices collect sensitive information, whether it's personal data, business secrets, or operational readings. Keeping this information safe from prying eyes is, like, absolutely critical. A secure connection makes sure that data stays private as it travels.
Device integrity: If someone can get into your device, they might change its settings, load bad software, or make it stop working altogether. Secure access helps protect the device itself from tampering, ensuring it does what it's supposed to do, consistently, more or less.
Operational continuity: For businesses that rely on IoT devices for their daily operations, any disruption can mean lost money or services. Secure remote access helps you fix issues quickly and perform necessary updates without putting your system at risk of downtime, which is pretty vital, obviously.
Setting Up Your AWS VPC for IoT Devices
Building your own private network in AWS is a fundamental step for secure remote IoT. It gives you a controlled environment where your devices can talk to your cloud services without being exposed to the wider internet. It's like building a walled garden for your devices within the huge AWS cloud, so they can operate safely, you know.
Creating Your VPC
The first thing you'll do is create the VPC itself. You'll pick a range of IP addresses for your network, which is like deciding how many houses can be on your private street. AWS provides a simple way to do this through its management console or by using code. It's a straightforward process, honestly, to get that initial private space ready.
Subnets and Security Groups
Inside your VPC, you'll create subnets. These are smaller sections of your network, and you might have one for your Raspberry Pis and another for your cloud servers. Then there are security groups, which act like firewalls for your individual devices, controlling what kind of network traffic can come in and go out. This granular control is very powerful for security, actually.
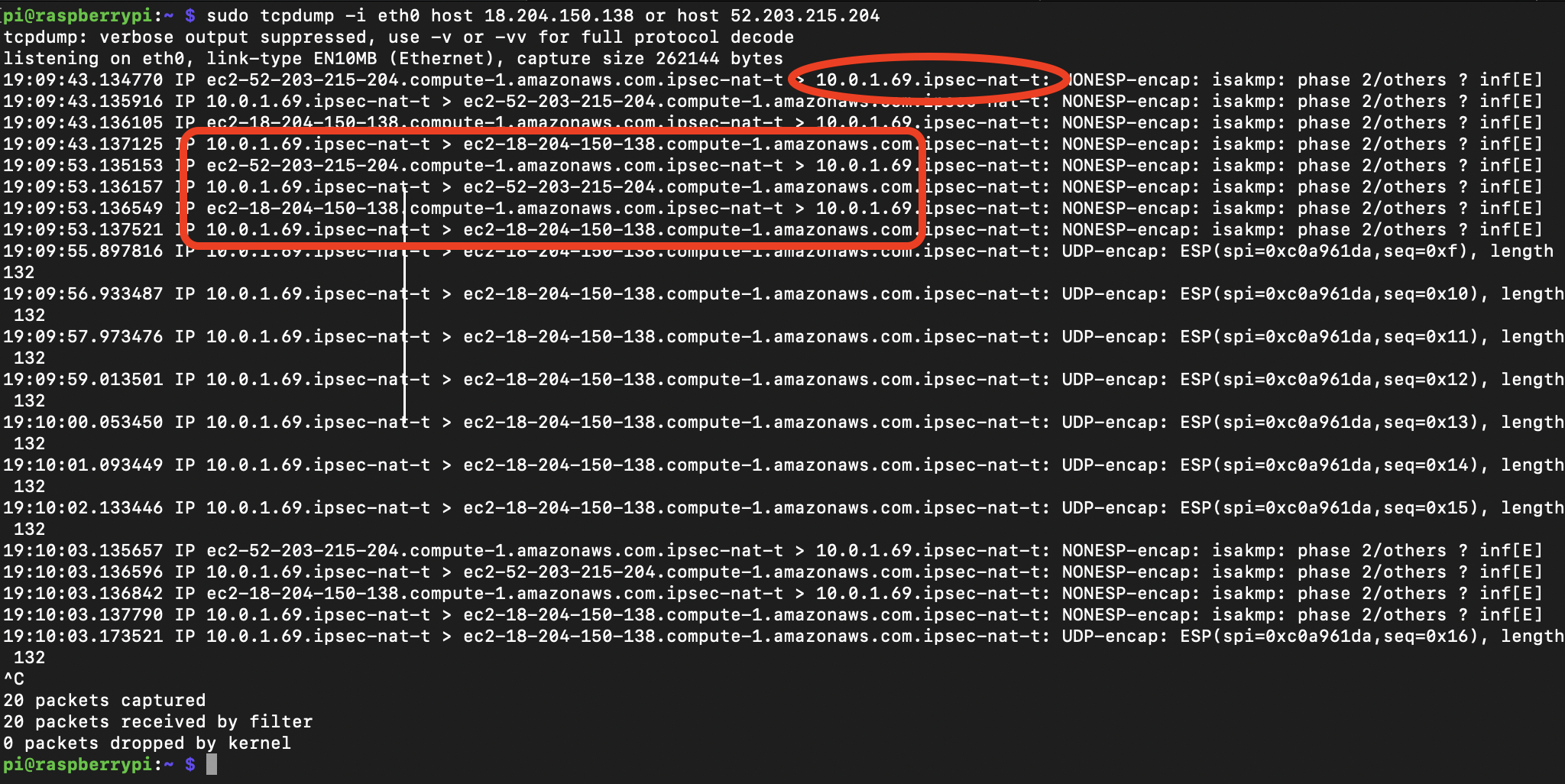
VPN or Direct Connect Options
To connect your on-site Raspberry Pis to your AWS VPC, you'll typically use a VPN (Virtual Private Network) connection or, for larger setups, AWS Direct Connect. A VPN creates an encrypted tunnel over the public internet, making it seem like your devices are right inside your VPC. Direct Connect offers a dedicated, private network connection, which is even more secure and faster for very demanding needs, you know. It's a choice based on your specific requirements.
Connecting Raspberry Pi via SSH to VPC
Once your VPC is ready, the next step is getting your Raspberry Pi to talk to it securely using SSH. This involves a few key preparations on your Pi and then setting up the connection. It's like preparing a special key and then using it to open a very secure door to your private cloud space, you know.
Preparing Your Raspberry Pi
Before connecting, your Raspberry Pi needs some basic setup. Make sure it has the latest software updates and that SSH is enabled. You'll also generate an SSH key pair: a private key that stays on your computer and a public key that goes onto the Raspberry Pi. This key pair is what makes the SSH connection so secure, essentially.
Establishing the SSH Tunnel
With your Pi ready, you'll use an SSH client on your local computer to connect to it. This connection will go through your VPN or Direct Connect link into your AWS VPC, then directly to your Raspberry Pi's private IP address. The command typically involves specifying your private key and the Pi's user and IP address. It's a direct, encrypted line, so, like, everything you send back and forth is protected.
Maintaining the Connection
For long-running tasks or continuous monitoring, you might want to keep the SSH connection alive. There are settings you can use in your SSH client to send "keepalive" messages, which prevent the connection from timing out. You can also automate the connection process using scripts, so your Pi is always ready for remote access without manual steps. This makes things much smoother for ongoing management, you know.
Managing Multiple Devices and Scaling
Setting up one Raspberry Pi is a good start, but what if you have ten, a hundred, or even more? Managing many devices requires a more structured approach, especially when it comes to keeping them secure and up-to-date. Automation becomes your very good friend here, honestly, making the whole process much less of a headache.
You can use tools that help you manage configurations across all your devices. This means you can push out software updates, change settings, or deploy new applications to many Raspberry Pis at once, rather than doing each one individually. It saves a lot of time and makes sure all your devices are consistent, which is pretty important for a big setup, you know.
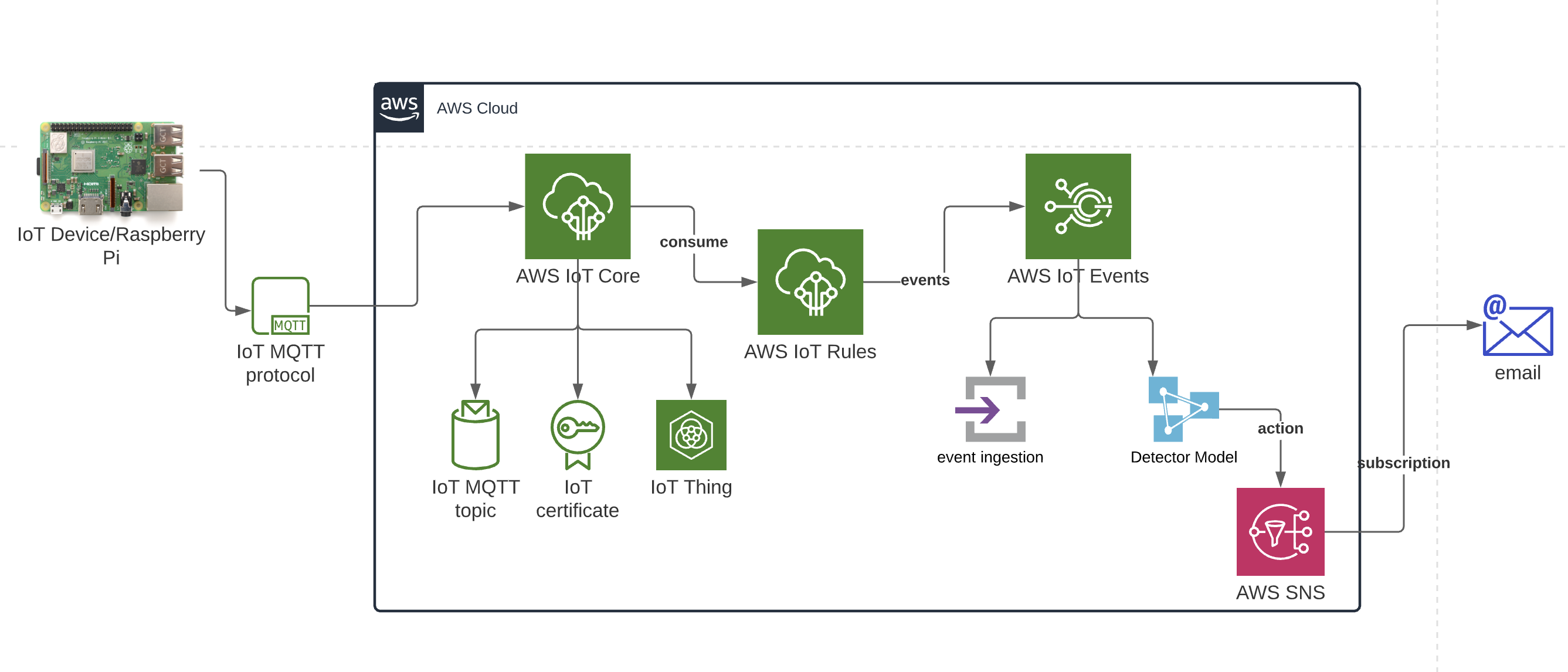
AWS IoT Core Integration
For even more advanced management, you can integrate your Raspberry Pis with AWS IoT Core. This service is designed to help you connect billions of IoT devices and manage them centrally. It provides features for device authentication, message routing, and even device shadows, which are virtual representations of your devices in the cloud. It helps you keep track of everything and interact with your devices in a very organized way, you know.
Centralized Management Tools
Beyond AWS IoT Core, there are other tools that can help with centralized management. Configuration management systems can automate the setup and ongoing care of your Raspberry Pis. These tools let you define the desired state for your devices, and they work to ensure all your Pis match that state. This means less manual work and fewer chances for mistakes, which is a big plus for a growing fleet of devices, honestly.
Common Questions About Remote IoT Security
People often have similar questions when they start thinking about secure remote access for their IoT devices. It's natural to wonder about the best practices and how to keep everything safe. Let's look at a few common ones, you know.
How do I securely connect my Raspberry Pi to AWS VPC?
You connect your Raspberry Pi to an AWS VPC primarily by setting up a secure tunnel, usually a VPN connection, between your local network (where the Pi sits) and your VPC. Once that tunnel is active, you can use SSH to connect directly to your Raspberry Pi's private IP address within the VPC. This method keeps your Pi off the public internet while still allowing you remote access, which is pretty smart, honestly.
What are the benefits of using SSH for remote IoT devices?
Using SSH for remote IoT devices offers several important benefits. First, it provides strong encryption for all communications, keeping your data private. Second, it uses authentication methods like key pairs, making it very difficult for unauthorized users to gain access. This means you can manage your devices from afar with a good deal of confidence, knowing your connection is protected, you know.
Can I manage multiple Raspberry Pis in an AWS VPC?
Yes, you absolutely can manage many Raspberry Pis within a single AWS VPC. You'd typically assign each Pi a private IP address within your VPC's subnets and use security groups to control their network access. For larger numbers, you might use automation tools or AWS IoT Core to handle configuration, updates, and monitoring for all your devices from a central point. It's quite scalable, actually, once you have the basic setup down.
Moving Forward with Your Secure IoT Setup
Building a secure remote IoT system with Raspberry Pi and AWS VPC is a very smart move for anyone looking to manage devices from a distance. It brings together the flexibility of edge computing with the security and scalability of cloud infrastructure. By using SSH within a private cloud network, you create a protected environment for your devices to operate and communicate, which is pretty much what everyone wants, right?
As a trusted collaborator, we help organizations make these kinds of technological advancements with confidence. We support business transformation and success, from the first ideas through to getting everything set up and making sure people know how to use it. You can learn more about secure cloud connections on our site.
This approach allows you to extend your operations, gather valuable information, and maintain control over your distributed devices without compromising on security. It's a way to truly revolutionize how you work with remote technology. For more details on AWS VPC, you can check out the official AWS Virtual Private Cloud documentation. And if you're curious about other ways we can support your tech needs, feel free to visit this page .
- What Does Asl Mean
- A Court Of Shaded Truths
- Help I Accidentally Summoned Mahoraga
- Space City Home Network
- Wasmo Somali Channel Telegram 2025
Secure Connection between AWS VPC and a Raspberry Pi | Tales of a
How To Master RemoteIoT VPC SSH Raspberry Pi AWS Download: A

Mastering RemoteIoT VPC SSH On Raspberry Pi With AWS Free Tier: A