Connecting Your Remote IoT Devices Securely: A Windows 10 Guide To VPC SSH
Getting your Internet of Things (IoT) gadgets to talk to you from afar, especially in a safe way, is something many folks think about these days. It is, you know, quite important to make sure those connections are solid and private. Whether you're a developer working on a big project or just someone with smart home devices, figuring out how to reach them securely can feel a bit like solving a puzzle. This is where a Virtual Private Cloud (VPC) and SSH (Secure Shell) truly step in to help.
Many people find themselves wondering how to bridge the gap between their Windows 10 computer and those small, often distant IoT devices. The good news is that with the right approach, it's not nearly as complicated as it might first appear. We're talking about creating a protected pathway, a kind of digital tunnel, that keeps your device interactions just between you and your things. This guide will walk you through the steps, making sure you have a clear picture of how to get everything linked up.
This article will show you how to use a VPC for a private network space and SSH for a secure connection right from your Windows 10 machine. We'll cover everything from getting your network ready to setting up your IoT device and making that first secure link. So, you might find, this really helps you keep your remote IoT projects running smoothly and safely, which is, you know, pretty good.
- How To See Deleted Sms
- Timothee Chalamet Net Worth
- How To Make Birria Tacos
- 4 Guard Buzz Cut
- How To Make Stickers
Table of Contents
- Understanding the Basics: IoT, VPC, and SSH
- Why Security Matters for Remote IoT Access
- Getting Ready: What You'll Need
- Setting Up Your VPC for IoT Devices
- Configuring SSH Access on Your IoT Device
- Connecting from Windows 10: The SSH Client
- Tips for a Smooth and Safe Connection
- Troubleshooting Common Connection Issues
- Looking Ahead: The Future of Remote IoT Security
- Frequently Asked Questions
- Conclusion
Understanding the Basics: IoT, VPC, and SSH
Before we get into the actual setup steps, it helps a lot to have a good idea of what these terms mean. You see, knowing the basics makes the whole process feel much less intimidating. It's almost like learning the rules of a game before you start playing, which is, you know, pretty helpful.
What are IoT Devices, Really?
IoT devices are, simply put, everyday objects that have sensors, software, and other technologies embedded within them. These devices connect and exchange data with other devices and systems over the internet or other communication networks. Think of smart thermostats, security cameras, or even tiny sensors monitoring soil moisture in a garden. They're basically small computers that do one or a few jobs, often sending back data. This data, too, might be something like a temperature reading, a door opening, or a machine's operational status.
These devices often collect different kinds of information. For example, some might send back simple "yes" or "no" signals, which is like a boolean value. Others might report temperatures or humidity levels, which are numeric types of data. Then there are devices that send back text messages or unique identifiers, which, you know, are string data. This variety means that when you connect to them, you're often looking at or processing these different data forms, much like how a query might execute over data where each column of data can only hold boolean, numeric, or string information.
- King Edward Love Chair
- Yes Yes Yes Meme
- Who Won The Voice 2025
- What Does Yeet Mean
- Mid Taper Textured Fringe
Virtual Private Clouds (VPCs): Your Secure Network Space
A Virtual Private Cloud, or VPC, is like having your own private, isolated section within a larger public cloud. Imagine a huge apartment building, and your VPC is your own apartment, complete with its own walls and doors. It gives you a dedicated space where you can launch your resources, like virtual servers or, in our case, connect your IoT devices. This separation means your devices are not just out on the open internet, which, you know, is a really good thing for safety. It provides a secure environment for your devices to communicate.
Inside your VPC, you have full control over your network settings. You can define IP address ranges, create subnets, and configure network gateways. This level of control is pretty important for managing traffic and making sure only authorized connections can reach your IoT devices. It's a fundamental layer of security that helps keep unwanted visitors out, so, in some respects, it's like setting up a very specific set of rules for who gets to come to your party.
SSH: Your Secure Remote Doorway
SSH, or Secure Shell, is a network protocol that gives you a secure way to access a computer over an unsecured network. Think of it as a super-strong, encrypted tunnel between your Windows 10 computer and your IoT device. When you use SSH, all the information you send back and forth, like commands or data, gets scrambled up so no one else can read it. This is, you know, absolutely vital for keeping your device control and data private. It’s a standard tool for remote administration.
It typically uses public-key cryptography for authentication, which is a much safer method than just using passwords alone. This means you have a pair of keys: a public key that lives on your IoT device and a private key that stays safely on your Windows 10 machine. When you try to connect, these keys work together to prove who you are without sending your secret private key over the network. It's a pretty smart system, and very effective at keeping things secure, you know.
Why Security Matters for Remote IoT Access
Leaving your IoT devices exposed on the internet is, quite frankly, a really bad idea. These small devices can become easy targets for malicious actors. If someone gains control of your IoT device, they could use it to spy on you, launch attacks on other networks, or even mess with the data it collects. Imagine a smart camera being turned against you, or a sensor feeding false information; it's a very real concern. So, too, securing these connections is not just a technical step; it's a protective measure for your privacy and digital well-being.
A private, encrypted pathway, like the one a VPC and SSH create, provides a strong defense against these threats. It ensures that only authorized users can communicate with your devices, and that all communication is scrambled and unreadable to outsiders. This significantly reduces the risk of data breaches, unauthorized access, and other cyber incidents. It’s about building a digital fortress around your little gadgets, which is, you know, pretty smart in today's connected world.
Getting Ready: What You'll Need
Before we start the actual setup, let's gather all the tools and accounts you'll need. Having everything ready beforehand makes the process much smoother. It's like preparing your ingredients before you start cooking; it just makes sense. You'll want to have these items handy, you know, to make things easier.
A Windows 10 PC: This is your control center, the machine you'll use to connect to your IoT devices. Make sure it's updated to the latest version, as this often includes important security patches and features like the built-in OpenSSH client.
An IoT Device: This could be anything from a Raspberry Pi running Linux to a specialized industrial sensor. The key is that it needs to be able to run an SSH server and be configurable for network access. You might have one already, or you could be setting up a new one. It's pretty common for these devices to run some form of Linux, which makes SSH setup quite straightforward.
A Cloud Provider Account: You'll need an account with a major cloud provider like Amazon Web Services (AWS), Microsoft Azure, or Google Cloud Platform (GCP). These providers offer the VPC services we'll be using. If you don't have one, most offer free tiers or trials that are perfect for getting started. You know, these platforms are very powerful.
SSH Client for Windows: Windows 10 actually has a built-in OpenSSH client, which is what we'll mostly focus on. However, if you prefer, you can still use third-party clients like PuTTY. We'll touch on both options, so you have choices, you know.
Basic Network Knowledge: While this guide tries to explain everything clearly, a little familiarity with network concepts like IP addresses, subnets, and firewalls will certainly help. It's not strictly necessary to be an expert, but it helps to grasp the concepts, which is, you know, a good thing.
Setting Up Your VPC for IoT Devices
Setting up your VPC is the first big step in creating that secure network space for your IoT devices. This part involves defining your private network and setting up rules for how traffic can flow in and out. It's a bit like designing the layout of your private apartment within that large building we talked about earlier. You want to make sure everything is in its right place, so, you know, things work well.
Creating Your VPC
Log into your chosen cloud provider's management console. Look for the "VPC" service. You'll typically find an option to "Create VPC" or "Launch VPC Wizard." When creating it, you'll define a CIDR block, which is a range of private IP addresses for your network. For example, 10.0.0.0/16 is a common choice. This range will be used by all the resources within your VPC, including your IoT devices. It's a pretty important foundational step, you know.
Give your VPC a meaningful name, something that helps you remember what it's for, like "MyIoTProjectVPC." You might also have options for DNS support and hostnames; usually, keeping the defaults for these is fine to start with. This initial setup establishes the boundaries of your private network, and it's where all your secure IoT activity will take place. So, you know, get this part right.
Subnets and Route Tables
Inside your VPC, you'll create subnets. Subnets are smaller divisions of your VPC's IP address range. You might create one public subnet (for resources that need internet access, like a bastion host) and one or more private subnets (where your IoT devices will live). Your IoT devices should be in a private subnet, so they are not directly exposed to the public internet. This arrangement adds another layer of security, you know, keeping things tucked away.
Route tables tell your network traffic where to go. For your private subnets, you'll typically have a route table that directs traffic within the VPC and perhaps through a NAT Gateway if your IoT devices need to initiate outbound connections to the internet (e.g., to send data to a cloud service). For your public subnet, the route table will have a route to an Internet Gateway. This ensures that only necessary traffic can flow in and out, which is, you know, a really smart way to manage things.
Security Groups and Network ACLs
Security Groups act like virtual firewalls for your individual instances (like your IoT device). You'll create a security group for your IoT devices that only allows incoming SSH traffic (port 22) from specific IP addresses – ideally, the public IP address of your Windows 10 machine or a bastion host within your VPC. This is a very granular level of control. You might also allow outbound traffic to necessary services. It's a pretty effective way to limit who can talk to your device, you know.
Network Access Control Lists (NACLs) are stateless firewalls that operate at the subnet level. While Security Groups are more common for instance-level control, NACLs can provide an additional layer of security by defining rules for all traffic entering or leaving a subnet. You typically set up NACLs to be quite permissive and rely more on Security Groups for specific instance rules, but it's good to know they exist for broader network control. They are, you know, another tool in your security toolbox.
VPN or Direct Connect (for advanced setups)
For more advanced setups, or if you have many IoT devices and a dedicated network infrastructure, you might consider setting up a Virtual Private Network (VPN) connection between your on-premises network and your VPC. This creates a secure tunnel over the internet, allowing your Windows 10 machine to act as if it's directly inside the VPC. For very high-bandwidth or critical applications, a Direct Connect service provides a dedicated network connection between your premises and the cloud provider, bypassing the public internet entirely. These are, you know, for bigger projects.
While a VPN or Direct Connect offers superior security and performance, they are more complex to set up and usually come with higher costs. For connecting a few remote IoT devices from your Windows 10 machine, using a public IP for SSH access (through a bastion host or directly to a device in a public subnet, with very strict security group rules) is often sufficient and simpler. You know, start simple and scale up if needed.
Configuring SSH Access on Your IoT Device
Once your VPC is ready, the next step is to prepare your IoT device to accept secure SSH connections. This involves installing the SSH server software and setting up key-based authentication. This is, you know, a really important part of the whole process, making sure your device is ready to listen for your secure connection.
Installing SSH Server
Most Linux-based IoT devices, like a Raspberry Pi, come with an SSH server pre-installed or it's very easy to add. If it's not there, you can usually install it with a simple command. For Debian/Ubuntu-based systems, you'd typically run sudo apt update && sudo apt install openssh-server. This command fetches the latest package information and then installs the SSH server. After installation, the SSH service usually starts automatically. You know, it's pretty straightforward for many devices.
It's a good idea to make sure the SSH service is running and configured to start on boot. You can check its status with sudo systemctl status ssh. If it's not running, you can start it with sudo systemctl start ssh. This ensures your device is always ready to accept your secure connection when it's powered on. So, too, this step is quite fundamental for remote access.
Generating SSH Keys (Public/Private Pair)
On your Windows 10 machine, you'll generate an SSH key pair. This pair consists of a private key (which you keep secret and secure) and a public key (which you can share). Open PowerShell or Command Prompt and type ssh-keygen. Press Enter for the default file location and passphrase (though adding a passphrase for your private key is highly recommended for extra security). This command creates two files, typically id_rsa (your private key) and id_rsa.pub (your public key), in your user's .ssh directory (e.g., C:\Users\YourUser\.ssh\). This is, you know, a very secure way to authenticate.
The passphrase adds an extra layer of protection to your private key. Even if someone gets hold of your private key file, they still won't be able to use it without the passphrase. This is a very good practice for keeping your connections safe. Remember to keep your private key absolutely secure and never share it with anyone. It's the key to your digital door, after all, and you wouldn't just give that out, would you?
Placing the Public Key on Your IoT Device
Now, you need to copy the public key (the .pub file) to your IoT device. The public key needs to go into a special file called authorized_keys within the .ssh directory of the user you'll be connecting as on the IoT device. For example, if you're connecting as the 'pi' user on a Raspberry Pi, the path would be /home/pi/.ssh/authorized_keys. If the .ssh directory or authorized_keys file doesn't exist, you'll need to create them and set the correct permissions. This is, you know, a pretty common step.
You can use the ssh-copy-id command from your Windows 10 machine (if you have Git Bash or WSL installed) or manually copy the content of your public key. To manually copy, open your id_rsa.pub file in a text editor, copy its entire content, then SSH into your IoT device using its password (just this once, for setup). Create the .ssh directory (mkdir -p ~/.ssh), set permissions (chmod 700 ~/.ssh), and then append your public key to authorized_keys (echo "your_public_key_content" >> ~/.ssh/authorized_keys). Finally, set permissions for the authorized_keys file (chmod 600 ~/.ssh/authorized_keys). These permissions are very important for security, you know.
Disabling Password Authentication (for better security)
Once you've confirmed that key-based authentication works, it's a very good idea to disable password authentication for SSH on your IoT device. This significantly improves security because it means no one can guess or brute-force their way into your device using just a password. They would need your private key and its passphrase. To do this, edit the SSH daemon configuration file, typically located at /etc/ssh/sshd_config. You'll need root privileges to edit this file, so use sudo nano /etc/ssh/sshd_config. You know, it's a critical security step.
Find the line that says #PasswordAuthentication yes or PasswordAuthentication yes. Uncomment it if it's commented out (remove the #) and change yes to no. Also, make sure PermitRootLogin is set to no and PubkeyAuthentication is set to yes. Save the file and then restart the SSH service (sudo systemctl restart ssh). After this, you will only be able to connect using your SSH key, which is, you know, much safer.
Connecting from Windows 10: The SSH Client
With your VPC set up and your IoT device configured, it's time to make that secure connection from your Windows 10 computer. We'll look at using the built-in OpenSSH client, which is very convenient, and also mention PuTTY for those who prefer it. It's pretty exciting when you make that first successful link, you know.
Using Windows 10's Built-in OpenSSH
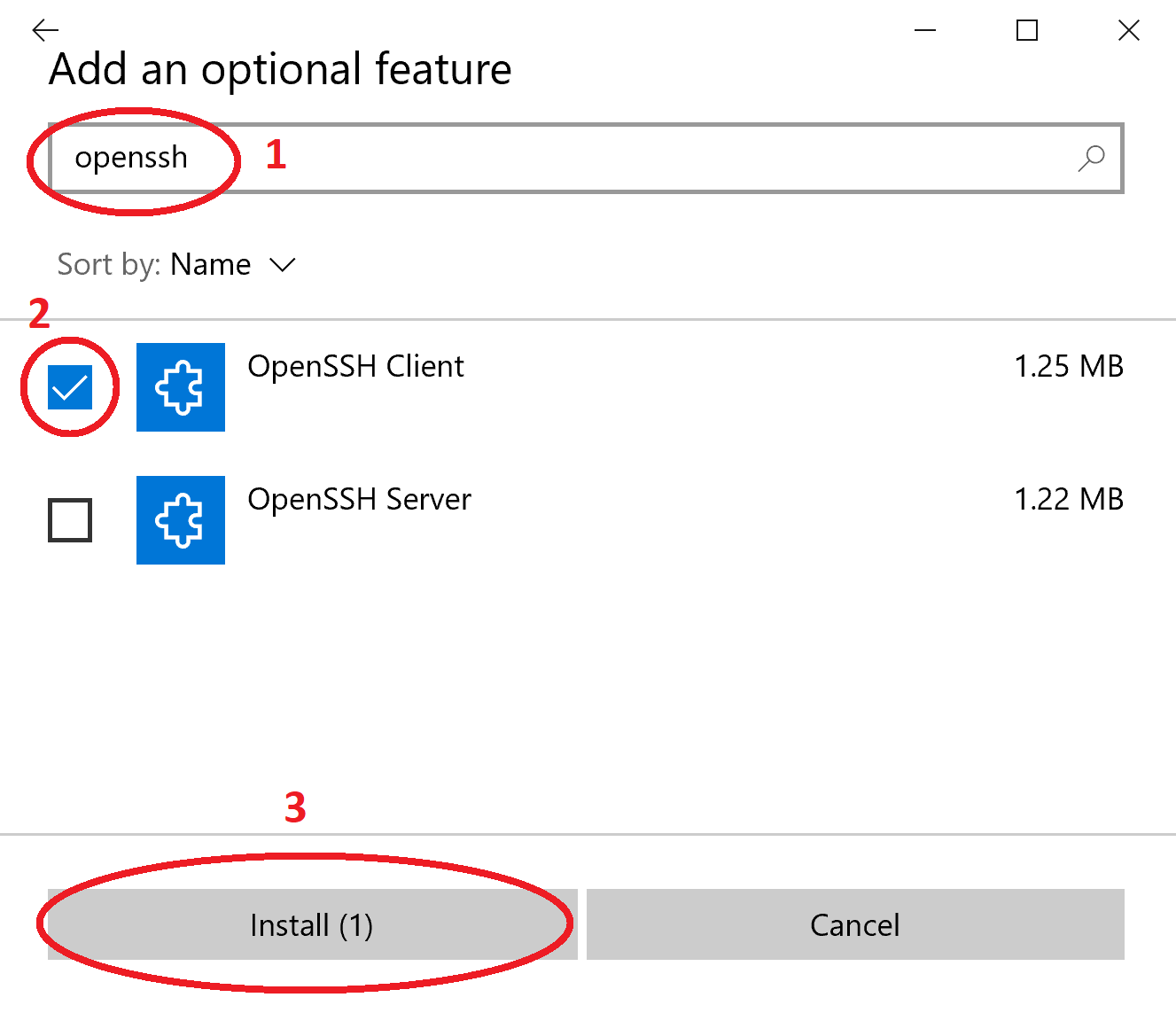
Windows 10 includes an OpenSSH client by default, which means you don't need to install any extra software for basic SSH
- Kimberly Guilfoyle Before And After
- Jasmine Crockett Husband
- Boo Did I Scare You Im A Job Application
- Jackerman Mother Warmth
- Who Won The Voice 2025

Remote IoT: Setup VPC SSH For Raspberry Pi & Windows 10 Access

Securely Connecting To IoT Devices Via VPC With SSH On Windows 10
Securely Connecting To IoT Devices Via VPC With SSH On Windows 10