Securely Connect Remote IoT: Raspberry Pi, AWS VPC, And Trusted Downloads
It's a common worry, you know, when your devices feel a bit exposed, perhaps even a little out of date. Maybe you've seen those unsettling messages, like "Your device is at risk because it's out of date and missing important security and quality updates." Or, perhaps, you've tried to connect to something, only to be told, "This connection is untrusted you have asked firefox to connect securely... but we can't confirm that your connection is secure." These warnings are, in a way, a wake-up call, showing just how important it is to make sure your remote systems are truly safe and sound.
So, too it's almost, when you're working with remote IoT setups, especially something like a Raspberry Pi out in the field, connecting back to your central cloud brain in AWS. The very idea of an untrusted connection, or a system that's not getting its vital security updates, can really keep you up at night. It's not just about getting things to work; it's about making sure they work reliably and, perhaps most importantly, securely. After all, a connection that isn't trusted can lead to all sorts of problems, like the ones Jerrywoods2 mentioned, where browsers just won't cooperate.
This article, then, is about getting you back on track, helping Windows – or rather, your entire IoT ecosystem – run more securely. We'll look at how to securely connect your remote Raspberry Pi devices to AWS, using a Virtual Private Cloud (VPC) for that extra layer of protection, and making sure all your software downloads and updates are completely trustworthy. We're talking about building a setup where you won't have to worry about those "connection is untrusted" messages ever again, in a way.
- Bianca Censori Before Kanye
- Do Female Cats Spray
- Burger King Crown Guy
- Jon Gruden Past Teams Coached
- Julesari Leaks
Table of Contents
- The Challenge of Remote IoT Security
- Understanding the Core Components
- Building a Secure Connection: Step-by-Step
- Best Practices for Ongoing Security
- Addressing Common Connection Issues
- Frequently Asked Questions
- Conclusion
The Challenge of Remote IoT Security
When you have devices scattered far and wide, maybe in different buildings or even across continents, keeping them safe becomes a big job. Traditional ways of securing computers, like firewalls at an office, don't quite fit. These remote IoT devices, like a Raspberry Pi, are often out there on their own, needing to talk to a central brain, which for many, is in the cloud, like AWS. This connection, you know, is where things can get a bit risky if not handled carefully.
Unsecured connections are a real problem, actually. It's like leaving your front door wide open. Bad actors could slip in, mess with your device, or even steal data. Remember those warnings about "Your device is at risk because it's out of date"? That's not just for your laptop. An old, unpatched Raspberry Pi is a target. The need for trust in these connections is, therefore, very, very important. If your system can't confirm the connection is secure, as Firefox sometimes tells you, then you have a big problem on your hands.
Getting your systems to run more securely is the goal. We need to build a setup where every piece, from the little Raspberry Pi to the big AWS cloud, trusts each other completely. This means making sure all communications are encrypted and that only authorized devices can talk. It also means, quite simply, that any software or updates going to your remote devices are truly from you and haven't been tampered with. This is what we mean by a secure connection, after all.
- Securely Connect Remoteiot Vpc Raspberry Pi Aws Server
- In The Clurb We All Fam
- Highest Block Blast Score
- Whispers Of Manifestation On Borlest
- Dress To Impress Creator Gigi
Understanding the Core Components
To really get a grip on securely connecting remote IoT, we need to look at the main players. Each one has a specific job, and understanding them helps us build a safer system. So, we'll talk about the Raspberry Pi, AWS VPC, and AWS IoT Core. They all work together, you know, to make things happen.
Raspberry Pi: Your Edge Device
The Raspberry Pi is a tiny, affordable computer that's very popular for IoT projects. It's small enough to fit almost anywhere, but powerful enough to collect data, run programs, and talk to the internet. People use them for all sorts of things, from smart home gadgets to industrial sensors. Its popularity, however, also makes it a target, so securing it is a must, basically.
While the Raspberry Pi is amazing, it doesn't come with built-in, foolproof security for remote operations. You have to add that yourself. This means making sure its operating system is up-to-date, and that it only talks to trusted sources. It's like having a little guard dog; you still need to train it and give it proper protection, you know.
AWS VPC: Your Private Cloud Network
Think of an AWS VPC, or Virtual Private Cloud, as your own private, isolated section of the AWS cloud. It's like having your own dedicated network space where you can launch AWS resources. This isolation is very, very important for IoT. It means your devices and their data are kept separate from the public internet, or from other people's AWS stuff, for instance.
Using a VPC for your IoT setup adds a strong layer of security. You control the network environment, setting up firewalls and rules for who can access what. This helps prevent unauthorized access to your IoT data and control systems. It's a bit like having a gated community for your digital assets, with strict rules about who gets in and out, you know.
AWS IoT Core: The Orchestrator
AWS IoT Core is the central hub for managing your IoT devices. It helps them connect, communicate, and process data. It's designed to handle millions of devices and messages, making it very scalable. This service, in a way, handles the heavy lifting of device management and messaging, so you don't have to build it all from scratch.
A key part of IoT Core is its focus on secure communication. It uses strong authentication and encryption protocols, like mutual TLS, to make sure only authenticated devices can send and receive messages. This means your Raspberry Pi and AWS IoT Core both verify each other's identity before they start talking. It's a bit like a secret handshake, making sure everyone is who they say they are, you know.
Building a Secure Connection: Step-by-Step
Now, let's get down to the practical steps of building this secure connection. It might seem like a lot at first, but breaking it down makes it much more manageable. We'll go through setting up your AWS environment, getting your Raspberry Pi ready, and making sure they can talk to each other safely. This is where the rubber meets the road, so to speak.
Prerequisites and Setup
Before we start, you'll need a few things ready. First, an AWS account, of course. If you don't have one, setting it up is pretty straightforward. Second, you'll need a Raspberry Pi, powered on and connected to the internet, with its operating system installed. Some basic familiarity with Linux commands and networking concepts will also be helpful, you know, just to make things a little easier.
Make sure your Raspberry Pi's operating system is up to date, too. You can usually do this with commands like `sudo apt update` and `sudo apt upgrade`. This is a very basic, but very important, security step. An outdated system is just asking for trouble, in a way.
Setting Up Your AWS VPC
First, log into your AWS Management Console. Go to the VPC service. You'll want to create a new VPC, which is your isolated network. Give it a name and choose an IP address range. Then, create at least one public subnet within this VPC. This subnet will be where your internet gateway lives, allowing your devices to talk to the internet, but in a controlled way, you know.
Next, create an Internet Gateway and attach it to your VPC. This allows traffic to flow in and out of your VPC. After that, set up a Route Table for your subnet, making sure traffic destined for the internet goes through your Internet Gateway. Finally, and this is very important, configure Security Groups and Network Access Control Lists (NACLs). These act as firewalls, controlling what traffic can enter and leave your subnet and your specific devices. You want to be very, very strict here, allowing only the necessary connections, in fact.
Configuring AWS IoT Core
Head over to the AWS IoT Core service in your console. You'll need to "register" your Raspberry Pi as a "thing." This gives it an identity within AWS IoT. When you register a thing, you'll generate certificates and private keys. These are like digital passports and keys for your Raspberry Pi, allowing it to prove its identity to AWS IoT Core. Keep these files very, very safe; they are critical for secure communication, you know.
After generating certificates, you'll create an AWS IoT policy. This policy defines what your Raspberry Pi is allowed to do within AWS IoT. For example, it might allow it to publish messages to a specific topic or subscribe to another. You should follow the principle of least privilege here: only grant the permissions absolutely necessary for your device to function. This helps prevent a compromised device from doing too much damage, you know, just in case.
Connecting Raspberry Pi to AWS IoT
Now, on your Raspberry Pi, you'll need the AWS IoT Device SDK. This SDK provides libraries that make it easier for your Pi to communicate with AWS IoT Core. You can usually install it using Python's pip package manager. Once installed, you'll place the certificates and private keys you generated earlier onto your Raspberry Pi. These files are what your device will use to authenticate itself to AWS IoT Core.
Your Raspberry Pi will communicate with AWS IoT Core using MQTT, a lightweight messaging protocol perfect for IoT. The SDK helps you set up this connection, using the certificates for mutual authentication. This means both your Pi and AWS IoT Core verify each other's identity before any data is exchanged. It's a pretty secure way to talk, ensuring that the connection is trusted, and not like those "untrusted" warnings you might have seen, you know.
Ensuring Secure Downloads and Updates
One of the biggest security risks for remote devices is getting untrusted software or updates. Remember "Your device is at risk because it's out of date"? We want to fix that safely. AWS IoT Device Management offers Over-the-Air (OTA) updates. This service lets you securely send firmware and software updates to your remote Raspberry Pi devices. It ensures the updates are delivered reliably and, most importantly, are authentic. This is a big step towards keeping your systems up-to-date and secure, you know.
When you prepare updates, you should use code signing. This involves digitally signing your update files. Your Raspberry Pi can then verify this signature before installing the update. This check confirms that the update truly came from you and hasn't been tampered with. It helps avoid situations where you have "a probler connecting securely to this website" because the source isn't trusted. By signing your code, you build in that trust right from the start, you know, just like a trusted certificate for a website.
Using services like AWS IoT Device Management for updates means you avoid the dangers of downloading from untrusted sources. It's not like going to a random website and hoping for the best. Instead, you have a controlled, secure pipeline for delivering new software and patches. This is how you prevent your device from being at risk due to missing important security updates, actually.
Best Practices for Ongoing Security
Building a secure connection is a great start, but security is an ongoing effort. You can't just set it and forget it. Regular patching is, for instance, extremely important. Just like your Windows PC needs updates to run more securely, your Raspberry Pi and AWS services need constant attention. Always apply security patches and updates as soon as they become available. This helps close known vulnerabilities before attackers can exploit them, you know.
Always follow the principle of least privilege. This means giving your devices and users only the permissions they absolutely need to do their job, and no more. If a device only needs to publish data to a specific topic, don't give it permission to delete things or access other parts of your AWS account. This limits the damage if a device is ever compromised, you know, just in case.
Monitoring and logging are also very, very important. Use AWS CloudWatch and CloudTrail to monitor your IoT activity and log all actions. This allows you to detect unusual behavior or potential security incidents quickly. If something looks off, you'll know about it. For your Raspberry Pi, you can set up local logging and send those logs to CloudWatch for centralized monitoring. It's like having a security camera watching everything, in a way.
Consider implementing secure boot for your Raspberry Pi devices. This feature helps ensure that only trusted software can run when the device starts up. It prevents malicious code from running before the operating system even loads. This adds another layer of defense, making it much harder for attackers to gain a foothold on your remote devices, you know.
Addressing Common Connection Issues
Even with the best planning, sometimes things don't go perfectly. You might run into issues like "This connection is untrusted" or "There is a problem connecting securely to this website," but for your IoT setup. Troubleshooting these problems usually comes down to a few key areas, actually.
If you're getting untrusted connection warnings, the first place to check is your certificates and keys. Are they correctly installed on the Raspberry Pi? Are they valid and not expired? Is the policy in AWS IoT Core correctly attached to the certificate? A mismatch or an expired certificate is a common culprit for connection failures. It's like trying to get into a building with the wrong key, you know.
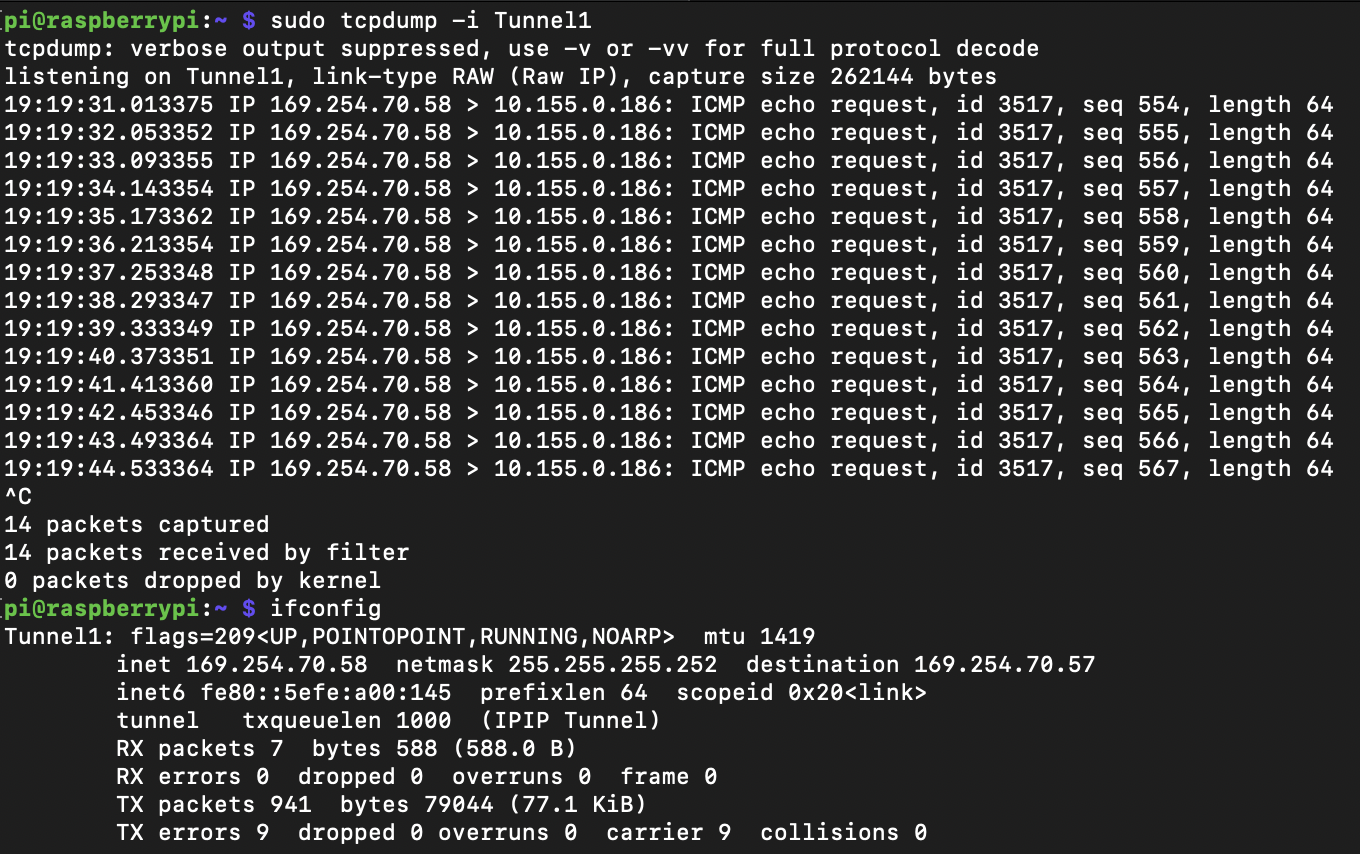
Firewall rules are another common source of headaches. Double-check your AWS VPC Security Groups and NACLs. Are they allowing the necessary traffic on the correct ports (usually MQTT ports like 8883 for secure connections)? Is your Raspberry Pi's local firewall (like `ufw` on Linux) configured to allow outgoing connections to AWS IoT Core? A blocked port is a very simple reason for a connection problem, you know.
Network connectivity itself can also be an issue. Is your Raspberry Pi actually connected to the internet? Can it resolve AWS IoT Core endpoints? Sometimes, a simple network hiccup can cause connection problems. You can use tools like `ping` or `traceroute` from your Raspberry Pi to diagnose network path issues. It's worth checking, you know, just to be sure.
Frequently Asked Questions
Here are some common questions people often ask about securely connecting remote IoT devices:
1. Why is secure connection important for IoT devices?
A secure connection is very important for IoT devices because it protects your data from being stolen or tampered with. It also prevents unauthorized people from taking control of your devices. Without security, your device could be at risk, like when your computer tells you it's missing important updates, you know. It keeps your operations private and reliable, basically.
2. Can I use other cloud providers instead of AWS for this setup?
Yes, you can, actually. While this article focuses on AWS, other cloud providers like Google Cloud Platform (GCP) and Microsoft Azure offer similar services for IoT device management and secure connectivity. The general principles of using private networks, device identities, and secure messaging remain similar across platforms, you know. You would just use their specific services instead.
3. How do I update my Raspberry Pi's software securely when it's remote?
To update your remote Raspberry Pi securely, you should use a trusted Over-the-Air (OTA) update mechanism. Services like AWS IoT Device Management allow you to send signed firmware updates to your devices. This ensures that the updates are authentic and haven't been tampered with. It's a very reliable way to keep your devices up-to-date and secure, unlike trying to download from untrusted sources, you know.
Conclusion
Building a secure connection for your remote IoT devices, like a Raspberry Pi, to AWS is not just a good idea; it's a necessity in today's world. We've talked about how using an AWS VPC creates a private, safe space for your devices, and how AWS IoT Core helps manage and communicate with them securely. We also covered the very important aspect of ensuring secure downloads and updates, making sure your devices are always running trusted software. It's about preventing those unsettling "untrusted connection" warnings and keeping your systems running smoothly and safely, you know.
By following these steps and best practices, you can create a robust and secure IoT ecosystem. This approach helps protect your data, your devices, and your peace of mind. It allows you to confidently deploy and manage your Raspberry Pi devices from anywhere, knowing they are connected in a way that is both powerful and secure. To learn more about IoT security best practices on our site, and link to this page .
For more detailed information on AWS IoT Core and its capabilities, you can always refer to the official AWS IoT Documentation. It's a great resource for going deeper into the technical aspects, you know.
- Remoteiot P2p Download
- Whispers Of Manifestation On Borlest
- Shut Up In Spanish
- Emily Compagno Husband
- Eminence In Shadow Season 3

Securely Connect Remote IoT VPC Raspberry Pi AWS: A Comprehensive Guide
Securely Connect Remote IoT VPC Raspberry Pi AWS Free: A Comprehensive

Securely Connect Your IoT Devices Using Raspberry Pi And AWS VPC