Securely Connect Remote IoT: P2P SSH For Safe Downloads Explained
Connecting to devices that are far away, especially those little IoT gadgets, can feel a bit like trying to talk to someone across a really big room. You want to make sure your message gets there clearly and, perhaps more importantly, that no one else is listening in. When you're dealing with sensitive information, or maybe just trying to grab a file from your smart sensor, keeping that connection private and sound is, you know, absolutely essential.
Many folks have run into frustrating issues when trying to get things done online, like when a browser, say Microsoft Edge, acts up while you're trying to download an important file from a shared space. Or perhaps you've seen those unsettling messages pop up, telling you your device is at risk because it's missing vital security updates. That kind of thing can really throw a wrench in your day, and it makes you wonder about the safety of your digital interactions, doesn't it?
So, we're here to talk about a pretty neat way to get your remote IoT devices talking securely, especially when you need to move files back and forth. We'll explore how something called P2P SSH can help you avoid those "untrusted connection" warnings and make sure your downloads are, actually, totally safe. It's about getting you back on track so your connections can run more securely, which is a good thing.
- What Does Yeet Mean
- 6 Guard Buzz Cut
- Do Female Cats Spray
- Remoteiot Monitoring Ssh Download Android
- What Is A Torta
Table of Contents
- What is P2P SSH for IoT?
- Why Secure IoT Connections Matter
- Getting Started with P2P SSH for Your IoT Devices
- Best Practices for Secure Downloads and Data Transfer
- Troubleshooting Common Secure Connection Issues
- The Benefits of a Secure P2P SSH Approach
- Frequently Asked Questions About Secure IoT Connections
What is P2P SSH for IoT?
When we talk about P2P SSH for IoT, we're basically discussing a way for your little smart devices, like sensors or smart home gadgets, to talk directly to your computer or another device without needing to go through a big central server. SSH, or Secure Shell, is a method for connecting to a computer over an unsecured network. It's designed to be very secure, which is, you know, really important. So, in a way, it's like having a private, encrypted phone line directly between your laptop and your remote weather station, for instance.
Traditionally, many IoT setups rely on cloud services. Your device sends data to a cloud server, and then your phone or computer pulls that data from the cloud. That works, but it means your data travels through a third party. P2P, which stands for peer-to-peer, cuts out that middleman. It allows the devices to connect directly, making the path for your data, well, a lot shorter and, arguably, more private. This direct link, especially when using SSH, means you get a strong layer of protection for any information moving between your devices. It's a pretty neat concept, honestly, for keeping things tight.
The "download" part in "securely connect remoteiot p2p ssh download" points to getting files or data from these remote devices. Maybe your IoT sensor collects data logs, or perhaps you need to update its software. Using P2P SSH for this means that when you initiate a download, the data travels over that secure, direct channel. This helps prevent anyone from snooping on your files or, perhaps even worse, changing them while they're on their way to you. It's about peace of mind, really, when you're pulling information from far-off places.
- Whispers Of Manifestation On Borlest
- Business Class Vs First Class
- Randy Travis Jackson Mall Investment
- Sophie Rain Spiderman Vid
- How To Say I Love You In French
Why Secure IoT Connections Matter
You know, in our everyday lives, we often bump into situations where security just isn't quite right. Think about those messages that pop up, saying something like, "This connection is untrusted you have asked firefox to connect securely to www.xxxxxxxxxxxx.com, but we can't confirm that your connection is secure." That's a big red flag, isn't it? It means the path your information is taking might not be as safe as you think. For IoT devices, where data can be very personal or even critical, ignoring these warnings is, actually, a very risky move.
Then there are the times when your own system tells you, "Your device is at risk because it's out of date and missing important security and quality updates." This isn't just a minor inconvenience; it's a direct warning. An outdated system is like a house with an open door. For IoT, where devices are often left running for long periods without much attention, keeping them updated is, quite simply, vital. These kinds of real-world issues show us why putting security first for our connected gadgets is not just a good idea, but a necessity, in some respects.
The Risks of Unsecured Connections
When you leave your IoT connections unprotected, you're basically inviting trouble. Without proper security, things like your smart home camera feed could be seen by unauthorized people, or your industrial sensors could have their data tampered with. This could lead to serious privacy problems, or even operational failures. Imagine someone getting access to your home's temperature controls, or, you know, worse, your security system. It's a pretty scary thought, isn't it?
Data breaches are another big concern. If you're downloading sensitive information from a remote IoT device, say, patient data from a healthcare monitor, and the connection isn't secure, that data could be intercepted. This isn't just a hypothetical problem; it happens. The fallout from such an event can be, really, quite devastating, leading to financial losses, damage to reputation, and even legal trouble. So, putting in the effort to secure these connections is, honestly, a form of self-protection.
Beyond data, there's the risk of device takeover. An unsecured IoT device can become a target for cybercriminals who want to use it for their own purposes, like launching attacks on other networks. Your little smart light bulb could, theoretically, become part of a botnet. This is why making sure your IoT connections are strong and dependable, with something like SSH, is so important. It protects not just your data, but the device itself and, you know, the wider internet, too.
Lessons from Common Connection Problems
We've all been there, haven't we? Trying to download a file, maybe an .msg file from SharePoint Online, and it just won't work in a particular browser, like Microsoft Edge. Or perhaps you're trying to password protect a file in SharePoint, but the option seems to have vanished. These are not just minor glitches; they point to deeper issues around how our systems handle security and permissions. When you can't even protect a file you own, it makes you wonder about the bigger picture of data safety, doesn't it?
Then there's the frustration of getting "This connection is untrusted" messages, whether it's for mail services like bay173.mail.live.com or just a regular website. And it's not just one browser; sometimes you try multiple platforms – MS Edge, Firefox, Chrome – and still, no luck. This suggests that the problem isn't just with the browser, but with the underlying trust relationship or certificates. For IoT, this means we can't just hope things work; we need to proactively build trust into the connection itself, which is where SSH comes in handy, like your own private security guard.
The experience of Jerrywoods2, who faced persistent untrusted connection issues across browsers, really highlights the need for fundamental security solutions. It's not about finding a hidden option or a quick fix; it's about establishing a connection that is, basically, inherently secure from the ground up. This is why understanding and implementing solutions like P2P SSH for your remote IoT devices is so valuable. It helps you bypass those frustrating, untrusted warnings by building a secure path from the start, which is, you know, a very good thing.
Getting Started with P2P SSH for Your IoT Devices
Setting up P2P SSH for your IoT devices might sound a bit technical, but it's really about creating a direct, secure line between your computer and your remote gadget. Think of it like giving your devices a secret handshake that only they understand. This method helps bypass some of the common connection problems you might face, like those untrusted warnings, by establishing trust right from the start. It's a way to take more control over your data's journey, which is, actually, pretty empowering.
The core idea is to let your devices talk directly to each other, rather than routing everything through a cloud server or a central hub. This can be particularly useful for devices that are in remote locations or on networks where direct internet access is limited. It's about creating a dedicated tunnel for your data, ensuring that when you need to, say, download a log file from a sensor in your garden, it travels safely and directly to your laptop. This approach, you know, gives you a lot more peace of mind.
While we won't go into every single command here, understanding the basic steps can help you get started. It's a bit like learning to ride a bike; once you get the hang of the basics, you can, like, go pretty far. The goal is to make sure that when you're connecting to your remote IoT device, you're doing it in a way that's dependable and, most importantly, secure. This helps prevent those frustrating moments where your connection just feels, well, a bit shaky.
Basic SSH Setup for IoT
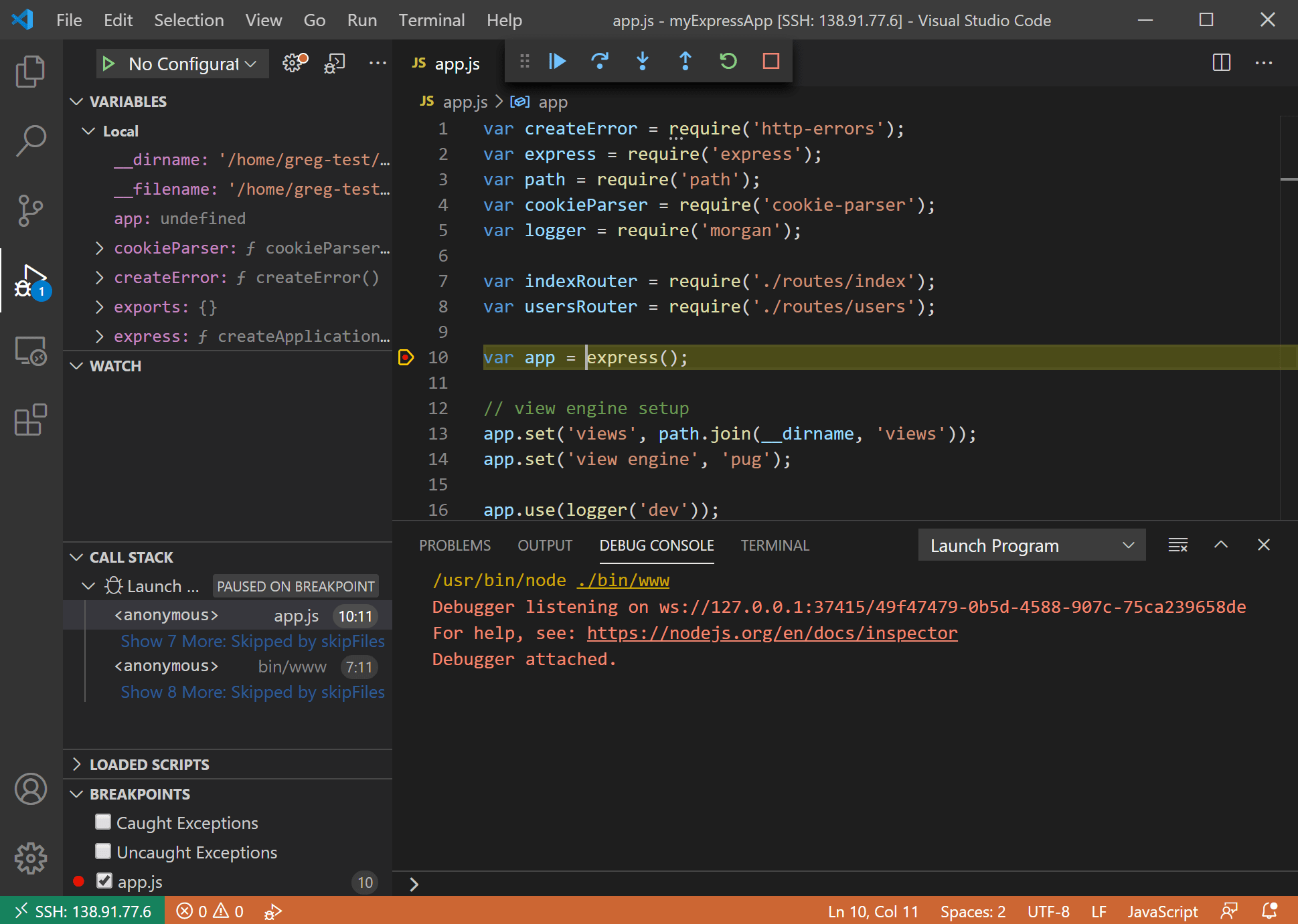
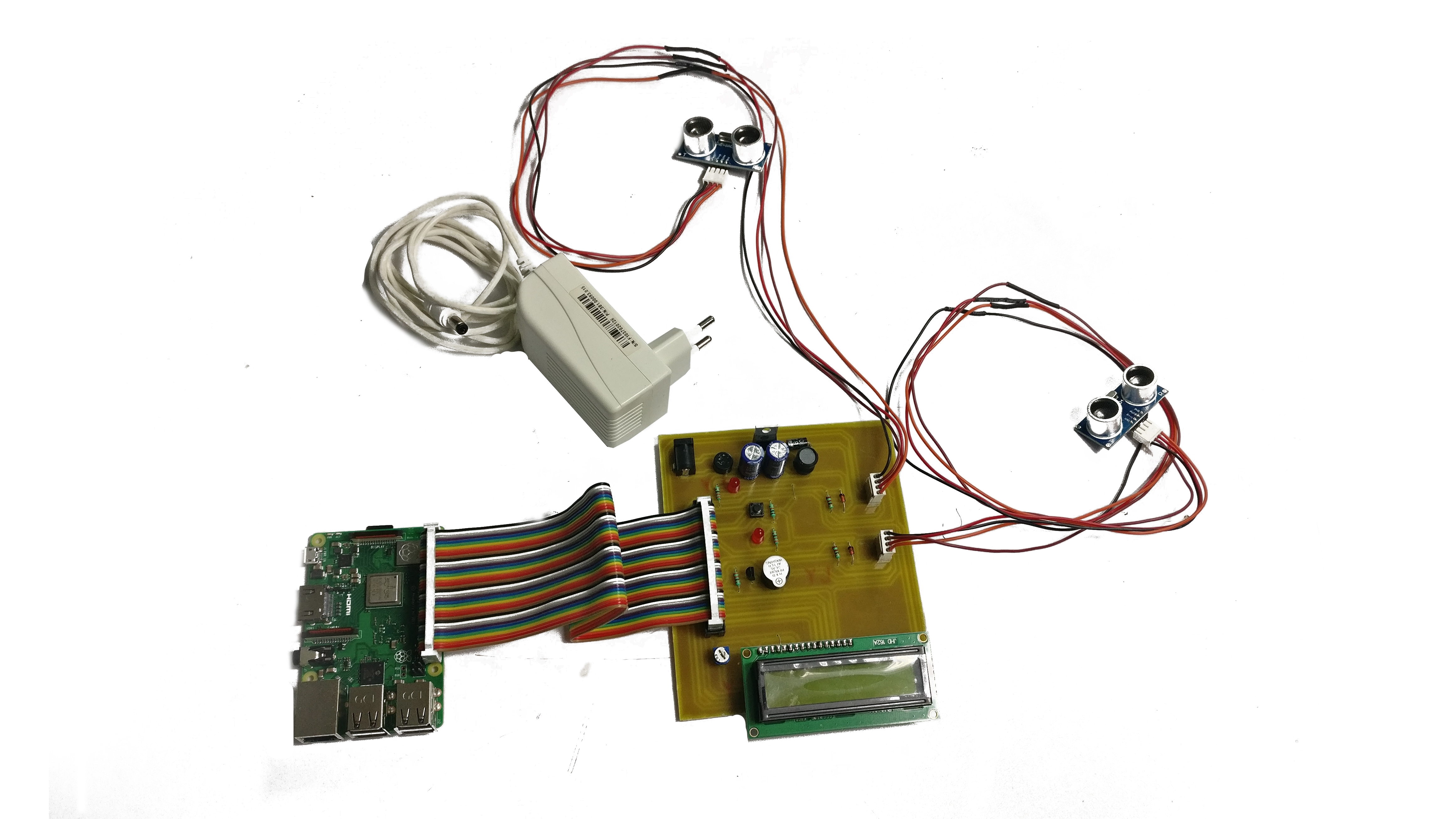
The first step usually involves making sure your IoT device has SSH enabled and that you can access it. Many small computing devices, like Raspberry Pis, come with SSH capabilities built-in, or you can add them easily. You'll typically need to connect a keyboard and screen to the device initially, or access it over your local network, to turn on the SSH service. This is, basically, like setting up the doorbell for your secure connection, so you can knock on its digital door.
Next, you'll generate SSH keys. This is a pair of digital keys: one public and one private. You put the public key on your IoT device, and you keep the private key safe on your computer. When you try to connect, your computer uses its private key to prove its identity to the IoT device, which then checks it against the public key. This method is, honestly, much more secure than using just a password, which can sometimes be guessed or stolen. It's a much stronger form of identification, in some respects.
Once the keys are in place, you can try a simple SSH connection from your computer to the IoT device. This is often done using a command-line tool. If it connects successfully, you've established a basic secure channel. This means you can run commands on the remote device, or, importantly, start moving files back and forth. It's a fundamental step towards having a truly secure way to interact with your remote gadgets, which is, you know, really helpful for managing them.
Making it P2P
To make the SSH connection truly P2P, especially if your IoT device is behind a firewall or on a private network, you might need to use techniques like reverse SSH tunnels or services that help with NAT traversal. A reverse SSH tunnel, for example, allows the IoT device to initiate an outgoing connection to a publicly accessible server (which you control), and then your computer can connect to that server to reach the IoT device. It's a bit like the IoT device calling home and leaving a message for you to pick up, so you can call it back securely.
Another approach involves using specialized P2P networking tools or libraries that are designed to help devices find and connect to each other directly, even when they're on different networks. These tools often handle the complex parts of establishing a direct link, making it easier for you. The goal is always to create that direct, encrypted pathway without relying on third-party cloud services for the actual data transfer. This keeps your data path, well, very direct and private, which is, actually, a huge benefit for sensitive applications.
When you have this P2P setup, downloading files becomes a direct transfer over the secure SSH tunnel. Whether you're using `scp` (Secure Copy Protocol) or `sftp` (SSH File Transfer Protocol), the data flows straight from your IoT device to your computer, or vice versa, completely encrypted. This means that even if someone were to intercept the data stream, they wouldn't be able to read it. It's a very dependable way to handle your remote IoT downloads, ensuring your information stays private, which is, you know, a top priority for many people.
Best Practices for Secure Downloads and Data Transfer
Just setting up a secure connection isn't the whole story; you also need to follow some good habits to keep your downloads and data transfers safe. Think of it like locking your front door; having a good lock is one thing, but actually remembering to use it every time is another. These practices help make sure that even with SSH, you're not leaving any little gaps for trouble to sneak in. It's about being consistently careful, which is, honestly, a very smart approach.
One of the biggest lessons we learn from common online issues, like those untrusted connection warnings, is that trust needs to be established and maintained. It's not a one-time thing. For your IoT devices, this means regularly checking on their security status and making sure everything is as it should be. It's a bit like checking your car's tires before a long trip; you want to make sure everything is in good working order for the journey ahead, which is, you know, a pretty sensible idea.
These practices are designed to help you avoid the kinds of problems that lead to "Your device is at risk" messages or difficulties downloading files securely. By being proactive, you can prevent many headaches before they even start. It's about building a strong foundation for your remote IoT interactions, so you can focus on what your devices are doing, rather than worrying about how safe their connections are. That's, basically, the goal, isn't it?
Always Verify Your Connection
Before you start downloading anything important, or sending commands to your remote IoT device, always take a moment to verify that your SSH connection is, in fact, secure. When you first connect to a new SSH server, you'll often get a message asking you to confirm the server's fingerprint. This fingerprint is a unique identifier for that specific server. It's really important to check that this fingerprint matches what you expect. If it doesn't, it could mean you're connecting to the wrong device, or, perhaps worse, someone is trying to trick you into connecting to a malicious server. This is, you know, a very critical step.
Think about those "untrusted connection" warnings you sometimes see in browsers. They pop up precisely because the browser can't verify the identity of the server it's trying to talk to. With SSH, you have a direct way to do that verification yourself. Once you've confirmed the fingerprint the first time, your SSH client will usually remember it. If it ever changes unexpectedly, your client will warn you. This is your cue to investigate immediately. Don't just click through; take the time to figure out why the fingerprint changed. It's about being vigilant, which is, honestly, a very good habit to develop.
Regularly reviewing your SSH client's known hosts file, where these fingerprints are stored, can also be a good practice. If you've decommissioned an old IoT device or changed its setup, it's wise to remove its old fingerprint. This helps keep your system clean and reduces the chance of accidentally connecting to an old, perhaps compromised, device. This little bit of upkeep can go a long way in maintaining a truly secure remote connection environment, which is, basically, what we're aiming for.
Keep Your Systems Updated
This point cannot be stressed enough: always keep both your remote IoT devices and the computer you're connecting from updated. Remember that warning about your device being at risk because it's out of date? That applies directly here. Software updates often include important security fixes that patch up newly discovered weaknesses. If you're running old software, you're essentially leaving known vulnerabilities open for attackers to exploit. It's like having a really strong lock but leaving the key under the doormat, isn't it?
For your IoT devices, this means regularly checking for firmware updates or operating system updates. Many small devices running Linux-based systems, like Raspberry Pis, can be updated with a few simple commands. For other proprietary IoT devices, you might need to check the manufacturer's website for update instructions. It's a bit of a chore sometimes, but the security benefits are, actually, immense. An unpatched vulnerability on a remote device could give an attacker a way in, even if your SSH connection itself is strong.
Similarly, make sure the SSH client on your computer is also up to date. Software developers are constantly working to improve security and fix bugs. Using an old version of your SSH client could mean you're missing out on these improvements, potentially exposing you to risks. It's a simple step, but a very important one, to ensure that your entire connection chain is as strong as it can be. This consistent updating helps maintain a high level of security, which is, you know, what we're really after.
Managing Access and Permissions
When you set up SSH for your IoT devices, it's really important to think about who can access them and what they can do. This is about setting up proper permissions. For instance, you should avoid using the "root" user for everyday SSH access. The root user has complete control over the device, and if that account is compromised, an attacker has full reign. Instead, create a separate, less privileged user account for SSH access, and only switch to root when absolutely necessary. This is, basically, a principle of "least privilege," which is a very good security practice.
Also, make sure the files and directories on your IoT device have the correct permissions. For example, your SSH private key on your local machine should have very strict permissions, typically readable only by you. If others can read your private key, they could use it to impersonate you and access your IoT devices. This is similar to how you wouldn't want to leave your house keys lying around for anyone to pick up. It's about keeping your sensitive credentials truly private, which is, you know, paramount.
If multiple people need to access the IoT device, each person should have their own SSH key pair. Avoid sharing private keys. This makes it easier to track who is doing what and to revoke access for specific individuals if needed, without affecting others. It's about accountability and control. By carefully managing who has access and what they can do, you add another strong layer of security to your remote IoT setup. This kind of careful planning helps prevent unauthorized access, which is, actually, a common source of trouble.
Troubleshooting Common Secure Connection Issues
Even with the best intentions and careful setup, you might still run into a snag or two when trying to connect securely to your remote IoT devices. It's a bit like trying to fix a leaky faucet; sometimes you just need to know where to look. Many of these issues echo the problems people face with general web connections, like those frustrating "untrusted" messages or browser download glitches. Knowing how to approach these can save you a lot of headaches, which is, you know, pretty valuable.
Remember how some users, like Jerrywoods2, tried multiple browsers and still couldn't get a secure connection? That tells us the problem often goes deeper than just the application you're using. For IoT, it means we need to look at the network, the device itself, and the security certificates or keys involved. It's about systematically checking things, rather than just hoping for a quick fix. This systematic approach can, actually, help you pinpoint the real source of the trouble, which is a good thing.
The goal here is to give you some pointers for when things don't quite go as planned. It's about getting you back on track so your windows can run more securely, or, in this case, so your IoT connections can. These tips are based on common experiences and can help you diagnose and fix many of the typical problems you might encounter when trying to securely connect remote IoT devices for, say, a P2P SSH download. It's about being prepared, which is, you know, always a smart move.
Dealing with "Untrusted Connection" Messages
If you're getting "This connection is untrusted" messages when trying to SSH into your IoT device, or even when trying to download something via a secure channel, it usually means there's a problem with how your computer trusts the remote device's identity. This is very similar to what happens when you see such a warning in Firefox for a website like bay173.mail.live.com. The core issue is that your client (your computer) can't confirm the identity of the server (your IoT device) in a way it expects. This is, basically, a trust breakdown.
First, double-check the SSH host key fingerprint. As mentioned earlier, when you first connect to an SSH server, your client asks you to verify its fingerprint. If you're getting an untrusted message on subsequent connections, it might mean the fingerprint stored on your computer no longer matches what the server is presenting. This can happen if the IoT device was reinstalled, or, very rarely, if someone is trying to perform a "man-in-the-middle" attack. If the fingerprint has changed legitimately, you'll need to update your client's known hosts file. If it's suspicious, stop and investigate immediately. It's, you know, a very important check.
Another reason for untrusted warnings can be network issues or firewalls blocking the connection. Sometimes, a firewall on either your side or the IoT device's network might be interfering with the SSH handshake. Make sure the correct ports (usually port 22 for SSH) are open. Also, if you're using a complex P2P setup with reverse tunnels or proxy servers, ensure all parts of that chain are correctly configured and trusted. A simple network test, like pinging the IoT device if possible, can sometimes reveal basic connectivity problems. It's about checking all the pieces, which is, actually, pretty sensible.
Browser and Download Challenges
Sometimes, the issue isn't directly with SSH but with how your browser or operating system handles secure downloads, especially when you're pulling files from a remote source. Remember the problem with downloading an .msg file from SharePoint Online in Microsoft Edge? While P2P SSH bypasses the browser for the core connection, the downloaded file still ends up on your local
- Chris Jones 40 Yard Dash
- Bianca Censori Before Kanye
- Whispers Of Manifestation On Borlest
- Help I Accidentally Summoned Mahoraga
- Eminence In Shadow Season 3

Securely Connect Remote IoT P2P SSH: The Ultimate Guide
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide