Connect Your Raspberry Pi Securely: SSH Remote IoT Access, Free And Simple
Are you looking to manage your Raspberry Pi from anywhere, perhaps even across the globe, without worrying about prying eyes? So, securing your remote connections is a really big deal, especially when dealing with tiny computers like the Raspberry Pi that might be running your smart home or a cool science project. Many people want to access their devices from afar, and doing that safely is, you know, a very important part of the whole setup. This piece is all about making those remote connections safe and, what's more, showing you how SSH, a widely used tool, can give you that secure link for your IoT devices, including your Raspberry Pi, all without any cost.
The idea of controlling a device that is not right in front of you, a device like a Raspberry Pi, is quite appealing to many. You might have your Pi set up in a different room, or even in another building, and still want to send it instructions or get information from it. This kind of remote control is a cornerstone of many modern systems, and it helps people do a lot of interesting things with their technology, that is for sure. We will look at how SSH helps with this, providing a solid way to connect.
This discussion will walk you through what SSH is, why it matters for your Raspberry Pi and other internet-connected gadgets, and how it gives you a free path to keeping your data private. We will explore its history a little bit, too, and then talk about its practical uses for those working with small computers. You will also get some ideas on how to get started with this secure connection method, so, it is going to be helpful.
Table of Contents
- Understanding SSH: The Secure Connection Protocol
- Why SSH is Your Best Friend for Raspberry Pi and IoT
- Getting SSH for Your Raspberry Pi: It's Free
- Setting Up Secure Remote Access: A Basic Approach
- Keeping Your Remote IoT Connections Safe
- Common Questions About SSH and Raspberry Pi
- Conclusion: Secure Your IoT World
Understanding SSH: The Secure Connection Protocol
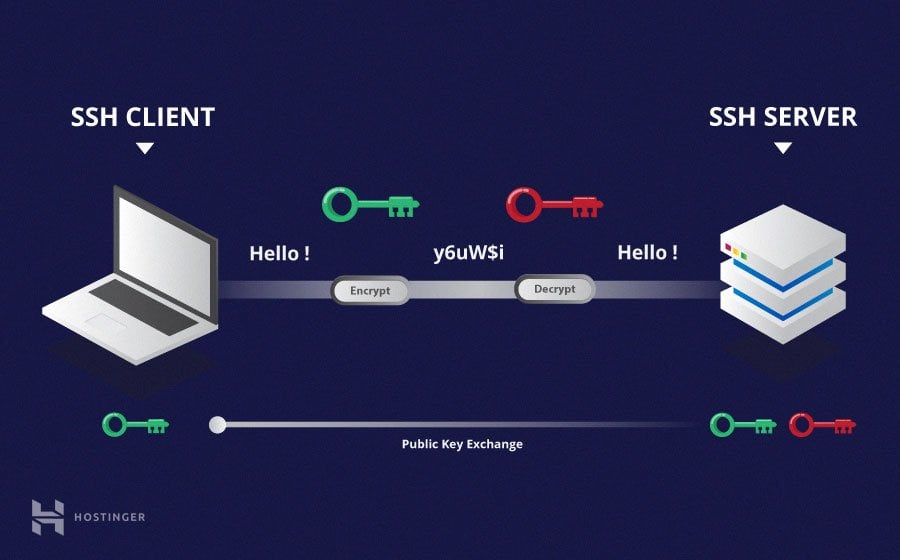
SSH, which stands for Secure Shell, is a kind of network language, you know, a protocol that helps two computer systems talk to each other in a safe way, even if the network they are using is not so safe itself. Back in 1995, a Finnish computer scientist named Tatu Ylönen came up with SSH. He made it to replace older, less secure ways of connecting, like Telnet and Rlogin, which were, in a way, quite open to problems. SSH changed how people thought about secure remote computing, providing an encrypted way to communicate.
This software package, SSH, helps with managing computer systems and moving files around, all over networks that might not be secure on their own. It is, basically, a tool you find in almost every big data center and in nearly every large company. The main goal of SSH is to set up connections that are encrypted, meaning all the information sent back and forth is scrambled, so, it is hard for anyone else to read it. This helps stop people from listening in, taking over your connection, or trying other bad things.
OpenSSH, in fact, is the main tool people use for logging in remotely with the SSH protocol. It makes sure all your communication is private. SSH can use different ways to check who you are, too, before it lets you connect securely to a server. These ways include using special digital keys, regular passwords, or even host keys, so, there are many options. It truly provides a secure path between computers, making sure your remote interactions are protected.
- Randy Travis Jackson Mall Investment
- Deep Winter Color Palette
- How To Say I Love You In French
- Pam Bondi Have Children
- How Old Is Harper Zilmer
Why SSH is Your Best Friend for Raspberry Pi and IoT
The Raspberry Pi, a small and powerful computer, has become very popular for all sorts of projects, especially those involving the Internet of Things, or IoT. These are devices that connect to the internet to send and receive data, maybe controlling lights, monitoring temperatures, or even running robots. Because these devices are often placed in different spots, and you want to check on them or change things, remote access is, you know, a pretty big need. This is where SSH truly shines for Raspberry Pi users and anyone working with IoT.
Using SSH means you can connect to your Raspberry Pi from another computer, perhaps your laptop at home, or even your phone, and do things like run commands, change settings, or move files. You can do all of this as if you were sitting right in front of your Pi, typing on its keyboard. The really good part is that SSH makes sure this connection is safe. It wraps all your communication in a secure channel, which is very important for devices that might be outside your direct control or on a public network.
Without SSH, if you were to use older, insecure methods, anyone with a bit of know-how could potentially see what you are doing, including your passwords or any sensitive information you are sending. This could lead to someone taking over your device or getting access to your home network, which is a big worry for many. SSH helps avoid these problems by encrypting everything, making it a very reliable way to manage your remote IoT projects. It is, in a way, a shield for your digital interactions.
For example, if you have a Raspberry Pi acting as a weather station in your garden, you might want to check its readings or update its software without having to go outside and plug in a screen and keyboard. SSH lets you do just that, securely, from the comfort of your living room, or, perhaps, even when you are far away. This kind of freedom and security makes SSH an absolutely vital tool for anyone serious about their Raspberry Pi or IoT setups. It really makes things simpler and safer.
Getting SSH for Your Raspberry Pi: It's Free
When people hear "download free" in the context of software, they often think about going to a website and getting a file. With SSH for your Raspberry Pi, the situation is a bit different, and actually, quite convenient. The good news is that SSH, specifically OpenSSH, is typically included as part of the operating system that runs on your Raspberry Pi, usually Raspberry Pi OS. So, you do not really need to go and "download" a separate program in the traditional sense, which is pretty neat.
Most versions of Raspberry Pi OS, which is the most common system for these small computers, come with the OpenSSH client and server already available. This means that the parts you need to both connect *from* your Pi and connect *to* your Pi are usually there from the start. This makes getting started with secure remote access very straightforward, as a matter of fact. You just need to make sure it is enabled, which is often a simple setting change or a quick command.
Because SSH is an open-source protocol, the tools that implement it, like OpenSSH, are free to use, distribute, and even change. This open nature means there are no licensing fees or costs involved in using SSH for your personal projects or even for commercial applications. This "free" aspect is a huge benefit, especially for hobbyists and students who are building IoT devices with Raspberry Pi, so, it is very accessible. It helps keep project costs down while still providing top-notch security.
Think about it: you get a powerful security tool that is used by huge companies and data centers, and it is available to you without any charge. This is a big win for anyone looking to build secure, connected systems on a budget. It means you can focus your resources on the actual hardware or other parts of your project, rather than worrying about software costs for secure connections. It truly democratizes secure remote computing for everyone.
Setting Up Secure Remote Access: A Basic Approach
Getting SSH ready on your Raspberry Pi usually involves a few simple steps. First, you need to make sure the SSH server component is active on your Pi. When you first set up a Raspberry Pi, especially with a fresh install of Raspberry Pi OS, SSH might be turned off by default for security reasons. This is a good thing, as it means your device is not open to connections until you explicitly allow it, which is, in a way, a thoughtful design choice.
To turn on SSH, you can often use a graphical tool within the Raspberry Pi OS desktop environment, or you can do it from the command line if you are more comfortable with that. There is a specific command that lets you enable it, and once you run it, your Pi will be ready to accept SSH connections. This initial step is quite important because it opens the door for you to control your Pi without needing a screen or keyboard directly connected to it, which is very useful.
After enabling SSH on your Pi, you will need an SSH client on the computer you are connecting from. For most Linux or macOS systems, an SSH client is already built in, and you can just open a terminal window and type a command. For Windows users, there are free tools available, like PuTTY, that provide an SSH client, or you can use the built-in SSH client in newer versions of Windows. Connecting to your Pi involves knowing its network address, which is like its unique street number on your local network.
Once you have the address, you use the SSH client to try and connect. The first time you connect, your client will probably ask you to confirm the Pi's identity, which is a security measure to prevent connecting to the wrong device. After that, you will be asked for your username and password for the Raspberry Pi. Once you enter those correctly, you will have a secure command line connection to your Pi, ready to issue commands. It is, basically, like having a direct line to your device, no matter where you are.
For even better security, many people choose to set up SSH key-based authentication instead of using passwords. This involves creating a pair of digital keys: a public key that goes on your Raspberry Pi, and a private key that stays on your connecting computer. When you try to connect, these keys are used to verify your identity, which is much harder for someone to guess or steal than a password. This method provides a very high level of security for your remote access, and is, arguably, the preferred way for serious users.
Keeping Your Remote IoT Connections Safe
While SSH itself provides a strong layer of security through encryption, there are still things you can do to make your remote IoT connections even safer. One of the most important steps is to change the default password on your Raspberry Pi right away. Many Pis come with a standard username and password, and if you leave those unchanged, anyone who knows them could potentially get into your device, which is a big risk. Picking a strong, unique password is a very good start.
Another key step is to consider using SSH key-based authentication, as mentioned earlier. This method is much more secure than relying solely on passwords. If someone somehow gets your private key, it is still protected by a passphrase, adding another layer of defense. It means you are not sending your password over the network, which, in a way, removes a common point of weakness. Setting this up takes a little bit of effort, but the peace of mind it offers is truly worth it.
You should also think about limiting who can connect to your Raspberry Pi via SSH. For example, you might configure your network router to only allow SSH connections from specific IP addresses, perhaps only from your home network or a known location. This is often called port forwarding, and when you set it up, you can be quite specific about who gets in. This helps reduce the chances of unwanted visitors trying to access your device from anywhere on the internet, so, it adds a good boundary.
Keeping your Raspberry Pi's operating system and all its software up to date is also really important for security. Developers regularly release updates that fix security weaknesses. If you do not apply these updates, your Pi could be vulnerable to known attacks, even if you are using SSH. Regularly checking for and installing these updates helps keep your system patched and protected against new threats, which is, basically, ongoing maintenance for security.
Finally, consider using a VPN (Virtual Private Network) if you need to access your Raspberry Pi from outside your home network. A VPN creates a secure tunnel for all your internet traffic, adding another layer of encryption and making it harder for others to see your activities. This is especially useful if you are connecting from public Wi-Fi networks, which are often not very secure. For more information on network security, you can learn more about network security generally. It is a good idea to explore these extra measures to keep your IoT projects safe and sound.
Common Questions About SSH and Raspberry Pi
Many people have questions when they first start using SSH with their Raspberry Pi. Here are some common ones that might come up, providing some quick answers to help you along.
Is SSH already on my Raspberry Pi when I get it?
Typically, the SSH client and server components, especially OpenSSH, are included with the Raspberry Pi OS. However, the SSH server, which lets you connect *to* your Pi, might be turned off by default for security reasons. You usually need to enable it manually after the initial setup. This means it is there, but you just need to flip a switch, so, it is more about activation than a fresh download.
Can I really use SSH for free on my Raspberry Pi?
Yes, absolutely. SSH itself is a protocol, and the most common implementation, OpenSSH, is open-source software. This means it is free to use for personal projects, educational purposes, and even commercial applications. There are no fees or subscriptions required to use SSH on your Raspberry Pi, which is, in a way, a great benefit for many users.
What if I forget my Raspberry Pi's password when using SSH?
If you forget the password for your Raspberry Pi and cannot log in via SSH, you will typically need to connect a keyboard and monitor directly to your Pi. From there, you can usually reset the password for your user account. It is a bit like getting locked out of your house and needing to use a spare key, you know, a physical connection is often the way back in. Learn more about password recovery on our site, and link to this page troubleshooting Raspberry Pi access for more tips.
Conclusion: Secure Your IoT World
Using SSH for your Raspberry Pi and other IoT devices is, basically, a smart move for anyone who wants to manage their technology remotely. It provides a strong, encrypted connection that helps keep your data safe from prying eyes and unauthorized access. As we have seen, this powerful tool, created by Tatu Ylönen, is widely adopted in many professional settings, and the best part is that it is freely available to you through OpenSSH, which is usually part of your Raspberry Pi's operating system.
The ability to securely access your Raspberry Pi from anywhere means you have greater control over your projects, whether they are for home automation, learning, or more complex applications. By understanding the basics of SSH, enabling it on your Pi, and taking a few simple security steps like using strong passwords or SSH keys, you can truly protect your remote connections. It is a very effective way to make sure your internet-connected devices are both accessible and safe, giving you peace of mind.
- Costco Dinner Kit Chicken Taco
- Jon Gruden Past Teams Coached
- Ap Classroom Unit 6 Progress Check Mcq Answers Ap Lang
- Remoteiot Monitoring Ssh Download Android
- What Does Ig Mean
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

Windows SSH Server | Learning, Secure shell, Software engineer