A Comprehensive Guide To Remote IoT Device Connect Example
Connecting to your Internet of Things (IoT) devices from afar can seem like a pretty big challenge, particularly when those devices are tucked away behind a router or a sturdy firewall. Yet, the ability to manage and interact with your IoT setup, no matter where you are, is becoming incredibly important for many different kinds of projects and businesses. This guide will walk you through the process of setting up remote access for your IoT gadgets, showing you some clear ways to get connected securely.
You know, whether you are looking after a smart home system, overseeing industrial machinery, or simply tinkering with a Raspberry Pi in your garage, the need to connect remotely is definitely growing. This article will help you understand the core ideas and practical steps involved in making a secure connection to your remote IoT devices, even when they seem a bit out of reach. We will look at how a good `remoteiot device connect example` can simplify things for you.
Many folks find themselves struggling with the usual network hurdles that pop up when trying to reach devices far away. That's where solutions like `remoteiot` really shine, offering a way to skip all those common hassles. It's almost like having a direct line to your device, no matter its location, and that, is pretty useful, you know?
- Is A Fish An Animal
- Mikafans Leaks
- Baby Alien Fan Bus
- How Do I Say Goodbye Lyrics
- Jamaican Restaurants Near Me
Table of Contents
- Why Remote IoT Access Matters So Much
- The Usual Hurdles in Remote IoT Connectivity
- Foundational Techniques for Remote IoT Access
- Using a Specialized Platform: The remoteiot Way
- A Practical Remote IoT Device Connect Example
- Sorting Out Common Remote Connection Problems
- The Bigger Picture: Benefits of Smart Remote IoT Management
Why Remote IoT Access Matters So Much
The rise of IoT devices is quite something, with them popping up everywhere from our homes to big factories. With this growth, the need to connect to and control these devices from anywhere is also increasing, you know? It's not just about turning a light on from your phone; it's about making sure systems run smoothly, getting data, and fixing things without having to be right there.
Remote access gives you a lot of freedom. Imagine being able to check the CPU, memory, and network usage of your IoT devices, get alerts if something seems off, and even run batch jobs on them, all from a single dashboard. This kind of flexibility is really useful for companies, especially those with devices spread out in many different places, like construction job sites that need constant connection.
IoT devices, in a way, have the potential to truly change how we work, live, and move forward. Being able to access them remotely means you can keep things running, stay updated, and react quickly to any situation, which is pretty powerful, actually. It's about turning information into action, making things faster and easier, so to speak.
- How To Remove Acrylic Nails
- Sophiexyz Spiderman
- King Edward Love Chair
- Twin Where Have You Been
- What Is A Golden Birthday
The Usual Hurdles in Remote IoT Connectivity
Connecting IoT devices from a distance can be a bit tricky, especially when your device is sitting behind a NAT router or a firewall. These network setups are there for security, which is good, but they also make it harder for outside connections to reach your device directly. It's like trying to knock on a door that has no visible handle from the outside, you know?
NAT, or Network Address Translation, basically hides your device's specific address from the wider internet. It allows many devices on a local network to share one public IP address. While this saves IP addresses and adds a layer of security, it also means direct incoming connections are usually blocked by default. Firewalls, too, are designed to block unwanted traffic, which can include your attempts to connect remotely.
These barriers mean that a simple direct connection often just will not work. You need a clever way to get around them, a method that respects the security measures while still letting you reach your devices. Finding that method, or using a platform that provides it, is often the key to successful remote IoT management, and that's what we will talk about.
Foundational Techniques for Remote IoT Access
To get past those network hurdles, there are a couple of widely used techniques that you should know about. These methods create secure tunnels or pathways, allowing you to reach your IoT devices even when they are not directly exposed to the internet. They are pretty much the backbone of any `remoteiot device connect example` you might encounter.
SSH: Your Secure Access Point
SSH, which stands for Secure Shell, is a very common way to securely access remote computers and devices. It provides a secure channel over an unsecured network by using strong encryption. For IoT devices, especially something like a Raspberry Pi, SSH is often the first choice for remote command-line access. This guide will give you a detailed walkthrough of how to establish secure SSH connections to remote IoT devices, covering everything from setting things up to troubleshooting.
The fundamentals of SSH are pretty straightforward: you have an SSH client on your computer and an SSH server running on your IoT device. When you connect, SSH encrypts all the communication, so your commands and the device's responses are kept private. This example really highlights the simplicity and effectiveness of using SSH in IoT environments. By following these steps, you can ensure secure and reliable communication with your devices, which is quite important.
You can even use SSH to create a secure tunnel, which is sometimes called SSH port forwarding. This lets you access services on your remote IoT device that might not normally be exposed to the internet, like a web interface or a specific application. It's a very flexible tool, and learning how to use it for your IoT projects is a smart move, you know?
Reverse Proxy: Getting Past Network Barriers
Another powerful technique for remote access, especially for web interfaces on IoT devices, is setting up a secure SSL/TLS-based reverse proxy connection. This is a bit more involved than just SSH, but it is incredibly useful when you want to access a web-based control panel or an API running on your device, even if it is behind a NAT router or firewall.
So, how does it work? Instead of you trying to connect directly to your IoT device, which the firewall would likely block, the IoT device itself makes an outgoing connection to a publicly accessible server (the reverse proxy). This outgoing connection is usually allowed by firewalls. Once that connection is made, the reverse proxy then acts as an intermediary. When you want to access your IoT device, you connect to the reverse proxy server, and it forwards your requests securely through that established outgoing connection to your device.
The same technique can be used for various kinds of remote access, making it a very versatile solution. Web interfaces are now standard in IoT edge devices as well as connected embedded systems. They let users configure, control, and monitor hardware via a computer, and a reverse proxy makes these interfaces accessible from anywhere, which is really handy, actually. It's a way to get around those tricky network blockades while keeping everything secure with SSL/TLS encryption.
Using a Specialized Platform: The remoteiot Way
While understanding SSH and reverse proxies is great, setting them up can sometimes be a bit of a headache, especially for those who are not network experts. This is where dedicated platforms like `remoteiot` come into play. They provide a way to skip all the hassles, making remote connectivity much simpler and faster. It's a bit like having a ready-made bridge over those network rivers, you know?
Making Things Simple with remoteiot
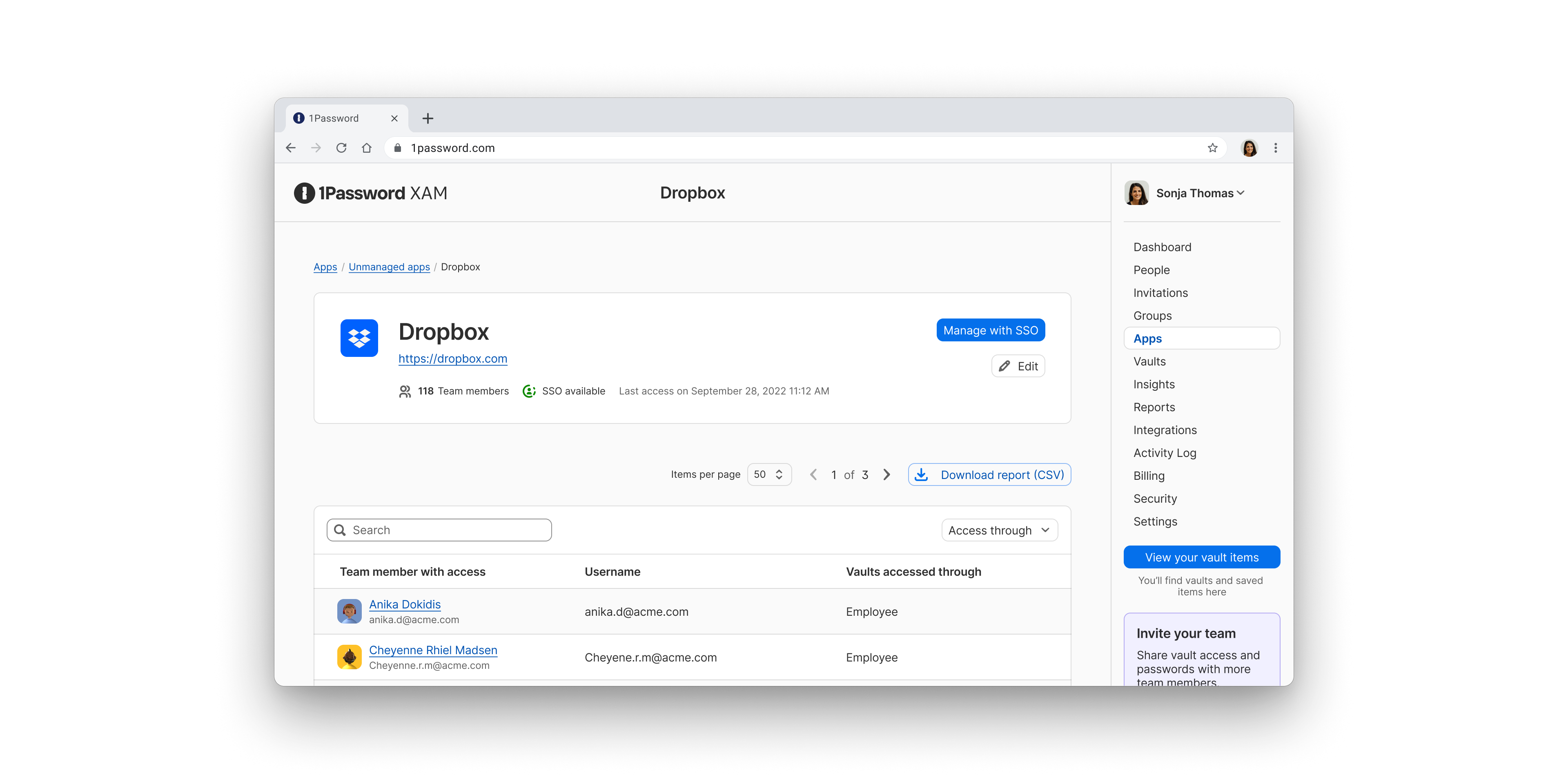
`remoteiot` is designed to streamline the process of connecting to your IoT devices from anywhere. The platform basically handles all the tricky parts of secure connections, like managing SSL/TLS certificates, setting up tunnels, and dealing with NAT and firewalls. You can use the `remoteiot` secure IoT cloud platform to quickly connect to networked Raspberry Pi devices from anywhere, even if they are behind a firewall. This makes the whole `remoteiot device connect example` much easier to follow.
It means you do not have to spend hours configuring complex network settings or worrying about dynamic IP addresses. The platform takes care of that, allowing you to focus on what your IoT devices are actually doing. This kind of simplification is really helpful for anyone who wants to get their devices online quickly and securely, without a lot of fuss.
Secure Cloud Platform for Raspberry Pi
Raspberry Pi devices are incredibly popular for IoT projects due to their versatility and low cost. `remoteiot` is particularly good at helping you connect these devices. The platform lets you manage and connect Raspberry Pi or other IoT devices securely from anywhere. You can connect to any device or machine behind firewalls, which is a common scenario for many Raspberry Pi setups in homes or small offices.
This secure cloud platform ensures that your connection is encrypted and safe from prying eyes. It provides the infrastructure needed to establish and maintain those connections, so you do not have to build it all yourself. It's a pretty complete solution for Raspberry Pi users looking for reliable remote access, actually.
Direct Connections with remoteiot VPC
`remoteiot` also offers a Virtual Private Cloud (VPC) feature. With `remoteiot` VPC, you can securely and directly connect Raspberry Pi and other IoT devices. A VPC creates a private, isolated network within a public cloud, giving you more control and security over your connections. This means your devices can communicate as if they are on the same local network, even if they are geographically separated.
This direct connection capability is very useful for scenarios where you need low latency or more granular control over network traffic. It adds another layer of security and privacy, ensuring that your IoT communications are protected. It's a slightly more advanced option, but it provides a lot of benefits for certain applications, you know?
Centralized Monitoring and Control
Beyond just connecting, `remoteiot` also provides a complete overview of all your IoT devices in one single dashboard. This is a huge benefit for managing a fleet of devices. You can remotely monitor CPU, memory, and network usage for each device. This kind of oversight is vital for maintaining device health and performance.
The platform also allows you to receive alerts based on monitored IoT data. If a device's CPU usage spikes, or its network connection drops, you can be notified immediately. Plus, you can run batch jobs across multiple devices, which saves a lot of time and effort. This centralized control makes managing large IoT networks much more efficient, which is really something to consider.
A Practical Remote IoT Device Connect Example
Let's put some of these ideas into a practical `remoteiot device connect example`. While the exact steps might vary slightly depending on your specific device and chosen platform, this general outline should give you a good idea of the process. This example will focus on using a platform like `remoteiot` for simplicity, as it handles many of the underlying complexities.
Preparing Your IoT Device
First things first, your IoT device needs to be ready. This usually means it is powered on, connected to the internet (even if behind a router), and has the necessary operating system or firmware installed. For a Raspberry Pi, this would mean having Raspberry Pi OS set up and ensuring it can access the internet.
You will also need to make sure any necessary software or agents for the `remoteiot` platform are installed on your device. This agent is what allows your device to securely connect to the `remoteiot` cloud platform, establishing that outgoing connection that bypasses firewalls. This step is usually pretty well documented by the platform provider, so you can follow their specific instructions, which is nice.
Setting Up Secure Remote Access
Once your device is ready, you will typically log into your `remoteiot` account on their web platform. Here, you would register your device, usually by following a simple setup wizard. This process often involves generating a unique key or token on the platform and then using that key on your IoT device to authenticate it with the `remoteiot` service.
After your device is registered and connected to the platform, you can then configure the type of remote access you need. This might involve setting up an SSH connection, configuring access to a web interface via a secure URL, or establishing a VPC connection. The platform takes care of creating the secure tunnels (like SSL/TLS based reverse proxy connections or SSH tunnels) automatically, so you do not have to deal with port forwarding or complex firewall rules yourself. This is where `remoteiot` helps you avoid those hassles, you know?
Checking Your Connection
With the setup complete, it is time to test your `remoteiot device connect example`. From your `remoteiot` dashboard, you should be able to see your device listed and its status. You can then try to initiate an SSH session directly from the dashboard, or click on the provided URL to access its web interface. If everything is set up correctly, you should now have secure, remote access to your IoT device from anywhere.
You can also check the device's metrics like CPU and memory usage to confirm that data is flowing correctly. This simple test confirms that the secure connection is working and that you have full control over your remote IoT device. It's a pretty satisfying moment when it all clicks, actually.
Sorting Out Common Remote Connection Problems
Even with the best tools, you might run into a snag or two when trying to connect remotely. It happens to everyone, really. If your `remoteiot device connect example` is not working as expected, here are a few things you can check to sort out common issues.
First, always check your internet connection on both ends: your device and your remote access point. A simple network hiccup is often the culprit. Make sure your IoT device is actually powered on and has a stable internet connection. Sometimes, it is just a loose cable or a Wi-Fi issue, you know?
Next, confirm that the `remoteiot` agent or client software on your IoT device is running correctly and is up to date. An outdated or stopped agent can prevent the device from connecting to the cloud platform. Also, double-check your credentials or authentication tokens within the `remoteiot` platform; a small typo can cause big problems.
If the issue persists, try using a different browser or even a different computer to access the `remoteiot` dashboard. Sometimes, browser caches or local network settings can interfere. If you cannot find a method to achieve your objective or are struggling to use the API, please contact the support team for the platform you are using. They are usually very helpful, and that's a good thing.
The Bigger Picture: Benefits of Smart Remote IoT Management
Establishing a successful `remoteiot device connect example` is just the beginning. The real value comes from the ongoing management and the benefits it brings. Being able to access and control your IoT devices from anywhere means you can maintain them more efficiently, react to problems quickly, and collect valuable data without having to travel to each device's location.
This capability helps you avoid pitfalls in managing large IoT device networks and ensures efficient remote control. You can monitor system health, deploy updates, and troubleshoot issues, all from a centralized location. This saves time, reduces operational costs, and increases the reliability of your IoT deployments. It's a pretty significant advantage for any organization using IoT on a larger scale.
Ultimately, remote IoT management, whether through secure SSH, reverse proxies, or dedicated platforms like `remoteiot`, is about giving you more control and flexibility. It lets you turn information into action, making it faster and easier to go from searching to doing. Learn more about secure IoT connections on our site, and you might also find useful information on IoT security best practices.
- Point Of View Skin Care
- Abbey Love On The Spectrum
- Ball Up Top Meaning
- Camarones A La Diabla
- Two Babies One Fox Comic
Device, Connect, Connection Icon Graphic by 121icons · Creative Fabrica

Manage Remote IoT Device Example: Comprehensive Guide For Efficient
Manage Remote IoT Device Example: Comprehensive Guide For Efficient