Securely Connecting Your Remote IoT Devices With SSH And AWS
Do you ever feel a little stuck when trying to reach your remote gadgets? It's almost like they're out there, doing their thing, but getting a good connection can be a real puzzle. Well, when it comes to managing your internet-connected things from far away, keeping them safe and easy to work with is super important. This is where combining secure shell, often called SSH, with Amazon Web Services, or AWS, and your remote IoT devices truly shines. It gives you a really solid way to connect and manage things, so you can actually get work done, you know?
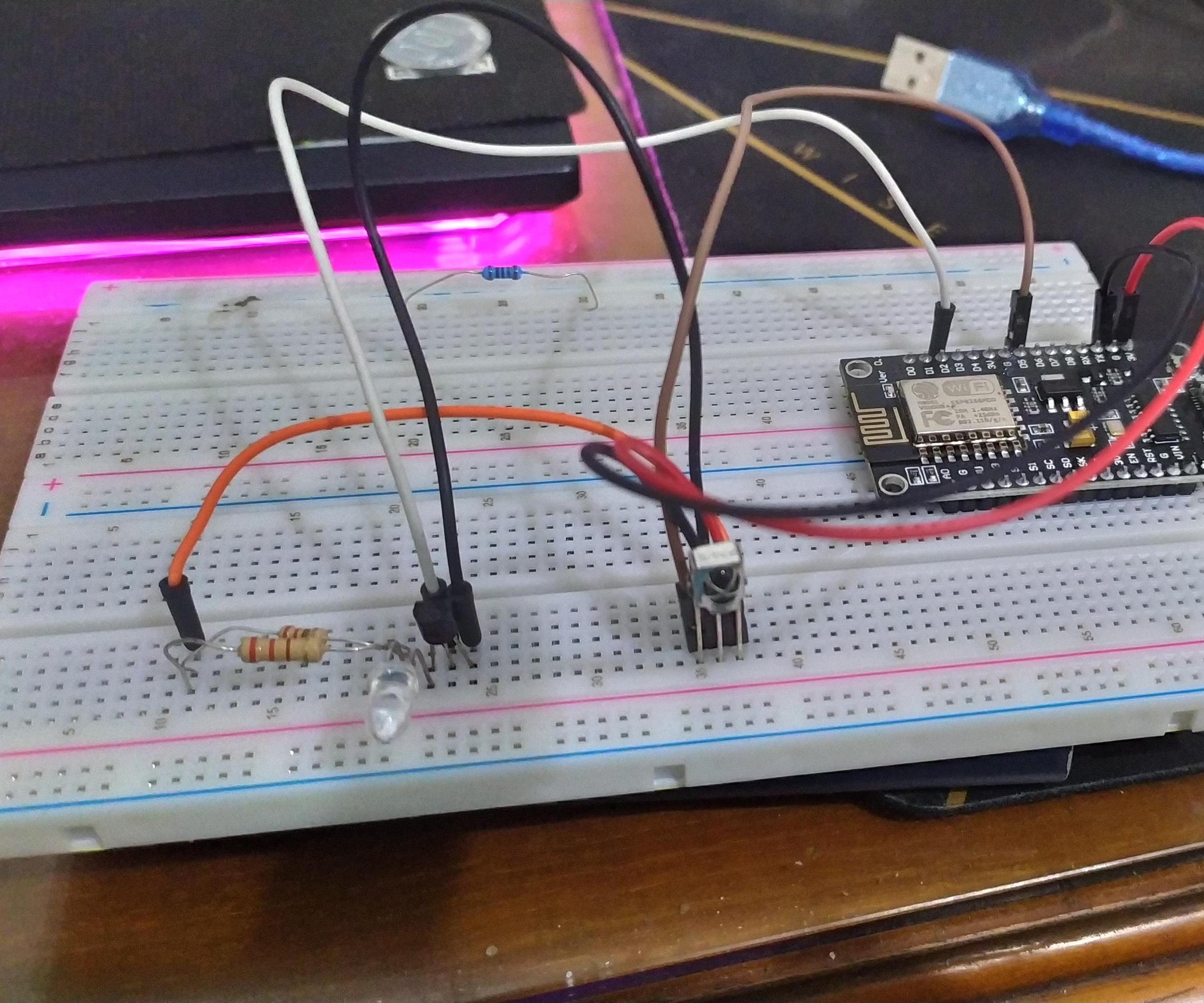
Think about all those small devices, perhaps a Raspberry Pi, sitting somewhere distant, maybe collecting data or running a tiny application. How do you check on it, update its software, or even just see if it's still working without having to physically go there? That's where the magic of SSH comes in, providing a secure pathway. And when you mix that with the powerful cloud services from AWS, you get a setup that's not just convenient but also very reliable, so that's a big plus.
This article will help you understand how `remoteiot ssh aws` works together. We will look at how to set up secure connections to your devices, whether they are small IoT sensors or larger cloud servers. We will also talk about the tools that make this possible, like VSCode's remote features and AWS's own secure tunneling options. It's really about making your remote work life a lot smoother, more or less, and keeping everything safe while you're at it.
- How To Remove Acrylic Nails
- Sophie Rain Spiderman Vid
- Yes Yes Yes Meme
- Costco Dinner Kit Chicken Taco
- Caitlin Clark Rookie Card
Table of Contents
- Why Remote IoT, SSH, and AWS Matter
- Connecting to AWS EC2 Instances with SSH
- Managing Your Connections and Security
- Common Questions About Remote IoT, SSH, and AWS
- Final Thoughts on Remote IoT, SSH, and AWS
Why Remote IoT, SSH, and AWS Matter
When you have devices spread out, perhaps in different buildings or even different cities, getting to them can be a challenge. That's where the idea of `remoteiot ssh aws` becomes so helpful. It's about making sure you can reach your devices from anywhere, keeping them running smoothly, and doing it all in a way that feels safe. This combination is, actually, a very strong way to work with all sorts of things, from tiny sensors to bigger machines.
The Basics of Secure Remote Access
SSH, or Secure Shell, is a network protocol that gives you a secure way to operate network services over an unsecured network. It's what lets you open a command line on a remote computer and type commands as if you were sitting right in front of it. This is really useful for managing Linux machines, like those running on AWS. The "My text" talks about using SSH to get into Linux instances, and that's exactly what it's for, so that's pretty clear.
For IoT devices, especially those that might be behind firewalls or on private networks, direct SSH can be tricky. This is where AWS steps in with some clever tools. They offer ways to create secure paths to your devices without needing to open up your entire network. It's kind of like having a secret, safe tunnel directly to your device, which is really handy, you know?
- Filmy Fly Com
- 6 Guard Buzz Cut
- More Than A Married Couple
- Randy Travis Jackson Mall Investment
- Julesari Leaks
AWS IoT Secure Tunneling: A Closer Look
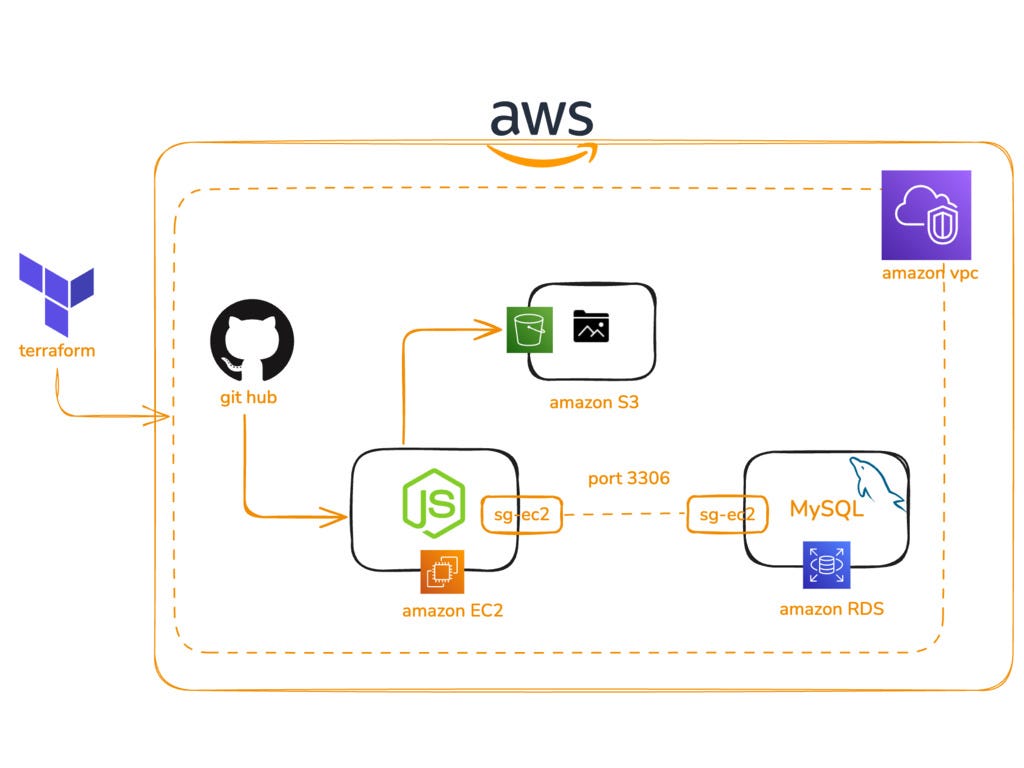
AWS IoT Device Management has a feature called secure tunneling. This is a big deal for `remoteiot ssh aws` setups. It helps customers get to remote devices over a secure connection that AWS IoT manages. You can create these tunnels right from the AWS IoT console, either from a special "tunnels hub" or from the details page of an IoT thing you've already set up. This means you don't need a local proxy to connect, which simplifies things quite a bit, honestly.
This secure tunneling is especially good for devices that are difficult to reach directly, like those on a private network or behind a strict firewall. It essentially creates a temporary, secure link between your computer and the remote device. So, you can, for example, SSH into a Raspberry Pi that's tucked away somewhere, all through AWS, which is pretty neat.
Connecting to AWS EC2 Instances with SSH
Beyond IoT devices, AWS EC2 instances are a common place where people use SSH. These are virtual servers in the cloud that you can rent and run your applications on. Connecting to them securely is a basic skill for anyone working with AWS. My text mentions guiding you through securely accessing an AWS EC2 instance using SSH on Linux, and that's a very typical use case, for instance.
Setting Up Your EC2 Instance for SSH
To connect to an EC2 instance, you first need to make sure it's set up correctly. This usually means creating a key pair, which includes a private key file (often a .pem file) that you keep safe on your computer. You also need to adjust the security group settings for your EC2 instance. This involves adding a rule to allow inbound SSH traffic, usually on port 22, from your IP address or a specific range. This step is really important for safety, as a matter of fact.
For Windows users, you might use PuTTY, which is a free SSH client. However, if you're using Windows Server 2019 or newer, OpenSSH is often recommended as it's built right in. The key is to have that .pem private key file ready, as it's what authenticates your connection to the EC2 instance. It's the digital handshake, basically, that proves you're allowed in.
Using VSCode for Remote Development on EC2
Many developers really like using Visual Studio Code (VSCode) for their work, and it has some fantastic features for remote development. My text mentions connecting VSCode with AWS Lightsail using Remote SSH, and also with EC2. This is a very popular way to work. It lets you write and run code on your remote server as if it were on your local machine, which is incredibly efficient, you know?
To do this, you'll need the Remote Development extension pack for VSCode if you don't have it already. Then, you create a remote SSH config file. In this file, you put in the details of your remote server, like its IP address and the path to your .pem key. This setup means you can deploy local source code to EC2 and then test it there, or even modify and run code directly on the EC2 instance. It really streamlines the workflow, pretty much, for many people.
Managing Your Connections and Security
Connecting to remote devices is just one part of the story; keeping those connections secure and manageable is another. With `remoteiot ssh aws`, you have powerful tools at your disposal, but using them wisely is key. It's about protecting your data and your devices from unwanted access, so that's a big thing to keep in mind.
SSH Clients and Key Management
Choosing the right SSH client is a personal preference, but ensuring your private keys are secure is universal. Whether you use PuTTY, OpenSSH, or a built-in terminal, always protect your .pem files. They are like the keys to your digital kingdom, so treating them with care is paramount. Regularly reviewing who has access to these keys and where they are stored is a good habit to get into, to be honest.
AWS Systems Manager also offers "Host Management" capabilities. This can help you manage your EC2 instances without directly SSHing into them every time, using an IAM role attached to your instance. This can add another layer of security and convenience, especially for automated tasks or larger fleets of instances. It's a different way to go about things, so that's an option too.
Security Best Practices for Remote Access
When working with `remoteiot ssh aws`, there are a few simple rules that can make a big difference for your security. Always use strong, unique passwords if you're not using key-based authentication (though keys are much better). Limit inbound SSH traffic to only the IP addresses that actually need to connect. This means not just opening it up to the whole world, which is a common mistake, you know?
Regularly update your operating systems and software on both your local machine and your remote devices. This helps patch any security weaknesses. Also, consider using multi-factor authentication (MFA) for your AWS account. It adds an extra step to logging in, but it makes it much harder for someone to get into your account, even if they have your password. It's a really good layer of protection, definitely.
Common Questions About Remote IoT, SSH, and AWS
Here are some questions people often ask about connecting remote devices using SSH and AWS:
How do I securely access my remote IoT devices with AWS?
You can use AWS IoT Device Management's secure tunneling feature. This creates a secure, temporary connection between your local machine and your remote device, even if it's behind a firewall. You manage this right from the AWS IoT console, which is quite convenient, more or less.
Can I use VSCode to develop directly on my AWS EC2 instance?
Yes, absolutely! You can install the Remote Development extension pack in VSCode. Then, by setting up an SSH config file with your EC2 instance details and private key, you can open folders and work on files located on your EC2 instance as if they were on your local computer. It's a very smooth way to develop, actually.
What's the best way to manage SSH keys for AWS connections?
The best practice is to keep your private key files (.pem) very secure on your local machine and never share them. Use strong file permissions to restrict access. For Windows, you can use OpenSSH or PuTTY. Also, consider using an SSH agent to manage your keys, so you don't have to type your passphrase every time. It just makes things a little easier, you know?
Final Thoughts on Remote IoT, SSH, and AWS
The ability to connect to and manage devices from afar is a big part of modern technology. Combining `remoteiot ssh aws` gives you a powerful set of tools to do just that, safely and efficiently. Whether you're working with a small Raspberry Pi, a fleet of IoT sensors, or robust cloud servers, these methods provide the access you need. It's about empowering you to keep your systems running, no matter where they are, so that's a big benefit. Learn more about secure remote access on our site, and link to this page for more AWS IoT solutions.
- Taper Fade Black Men
- Securely Connect Remoteiot Vpc Raspberry Pi Aws Server
- Jamaican Restaurants Near Me
- What Is Boba Made Of
- What Does Body Count Mean
Mastering Iot Ssh Download Aws A Comprehensive Guide - ACCDIS English
AWS SSH Troubleshooting. Connection Timeout Issue | by DevSecOps | Medium
How to Connect to AWS EC2 Instance Using SSH and RDP | by Laura Collins