Securely Connect Remote IoT P2P SSH Free: Your Guide To Hassle-Free Access
Connecting your Internet of Things (IoT) devices from afar, well, it's a big deal these days, isn't it? If you're looking to securely connect remote IoT devices using P2P SSH for free, then you've come to the right place. This really is a vital step for so many reasons, especially when you think about keeping your data safe and your devices working as they should.
You know, in the rapidly changing digital world, getting your remote IoT devices linked up through P2P SSH has become a real must for both businesses and folks at home. It’s not just about convenience; it's very much about making sure everything stays protected. There are, actually, quite a few challenges that can pop up, like those tricky connection warnings you might see in browsers or when your device just isn't up to date.
So, if you're hoping to securely connect remote IoT devices using P2P SSH on a Raspberry Pi without spending a dime on servers, you're, like, on the right track. This streamlined process is part of why securely connect remote IoT P2P SSH Raspberry Pi free is such an appealing option. It removes much of the guesswork and, frankly, a lot of the cost, too.
- Yes Yes Yes Meme
- How To Get Nail Glue Off Skin
- How To See Deleted Sms
- What Is A Torta
- Caramel Highlights On Brown Hair
Table of Contents
- What is Remote IoT P2P SSH?
- Why Secure Remote IoT Connections Matter
- The Appeal of Free P2P SSH for IoT
- Getting Started: Tools You'll Need
- A Step-by-Step Approach to Secure P2P SSH
- Common Challenges and How to Overcome Them
- Frequently Asked Questions
What is Remote IoT P2P SSH?
So, what exactly is remote IoT P2P SSH, you might wonder? Basically, it's a way to connect your Internet of Things (IoT) devices securely over the internet using a protocol called SSH. This isn't just any connection; it's a direct, peer-to-peer link, which is rather unique.
Typically, when you connect to a remote device, you might go through a central server or use complex network configurations. P2P, though, means your device talks straight to another device, cutting out the middleman. This can make things a little more efficient, and, in some respects, simpler to set up for individual users.
This approach is especially helpful for IoT gadgets that might be in different locations, perhaps in your home, a remote cabin, or a small business. It lets you manage them without needing a dedicated server, which can be a big cost saver, obviously.
- How Do You Spell
- Sophie Rain Spiderman Vid
- Randy Travis Jackson Mall Investment
- Michael B Jordan Girlfriend
- Grab The Mic Game
Why Secure Remote IoT Connections Matter
The importance of secure connections for your remote IoT devices really cannot be overstated. Your devices, after all, often handle sensitive information or control important functions. If these connections aren't protected, well, you're opening yourself up to some serious risks, as a matter of fact.
Think about it: an unsecured IoT device could be a doorway for unwanted access to your home network or even your personal data. It's not just about the device itself; it's about the broader system it's connected to. So, keeping things locked down is, quite frankly, a priority.
This is where solutions like securely connecting remote IoT P2P SSH Raspberry Pi free become invaluable. They offer a way to protect your digital assets without breaking the bank. It's about peace of mind, really, knowing your smart devices are doing their job safely.
Untrusted Connections and Risks
You might have seen messages like, "This connection is untrusted you have asked Firefox to connect securely to www.xxxxxxxxxxxx.com, but we can't confirm that your connection is secure." Or perhaps, "There is a problem connecting securely to this website." These warnings, you know, are red flags.
Such messages mean your browser, whether it's MS Edge, Firefox, or Chrome, can't verify the security of the connection. This is a big deal because it suggests that someone could potentially intercept your data. It's like sending a postcard through the mail for all to read, which isn't what you want for your IoT device communications, naturally.
When you're dealing with remote IoT, an untrusted connection means your device's data, commands, or even its very operation could be at risk. This is why having a system that ensures trust, like SSH, is so important. It's about building a secure tunnel, basically, for your data.
Outdated Devices and Security
Another thing to consider is device updates. You might get a message saying, "Your device is at risk because it's out of date and missing important security and quality updates." This is, honestly, a common problem, and it's a serious one for IoT devices.
Older software or firmware often has known weaknesses that hackers can exploit. It's like leaving a window open in your house; someone could just walk right in. Keeping your IoT devices patched and updated is, therefore, a fundamental part of their security posture.
So, letting Windows run more securely, for instance, or ensuring your Raspberry Pi's operating system is current, is not just a suggestion; it's a necessity. This helps prevent issues that could compromise your P2P SSH connection, too.
The Appeal of Free P2P SSH for IoT
The idea of securely connecting remote IoT devices using P2P SSH for free is, quite frankly, incredibly appealing. For many hobbyists, small businesses, or even larger organizations on a budget, avoiding server costs is a huge plus. You're not paying for a cloud instance or a dedicated VPN server, which can add up, you know.
Beyond the cost savings, it offers a level of direct control that some centralized solutions might not. You're setting up the connection between your devices directly, which can feel more personal and, in a way, more secure since fewer intermediaries are involved. This is, actually, a big draw for many users.
This approach also promotes self-sufficiency. You're learning how to manage your own secure connections, which is a valuable skill in today's interconnected world. It's about empowering you to take charge of your IoT security, which is pretty cool, if you ask me.
Getting Started: Tools You'll Need
To securely connect remote IoT devices using P2P SSH, you'll need a few key tools. These aren't super complicated, and most are, in fact, readily available. Having the right setup from the start will make the whole process much smoother, you know.
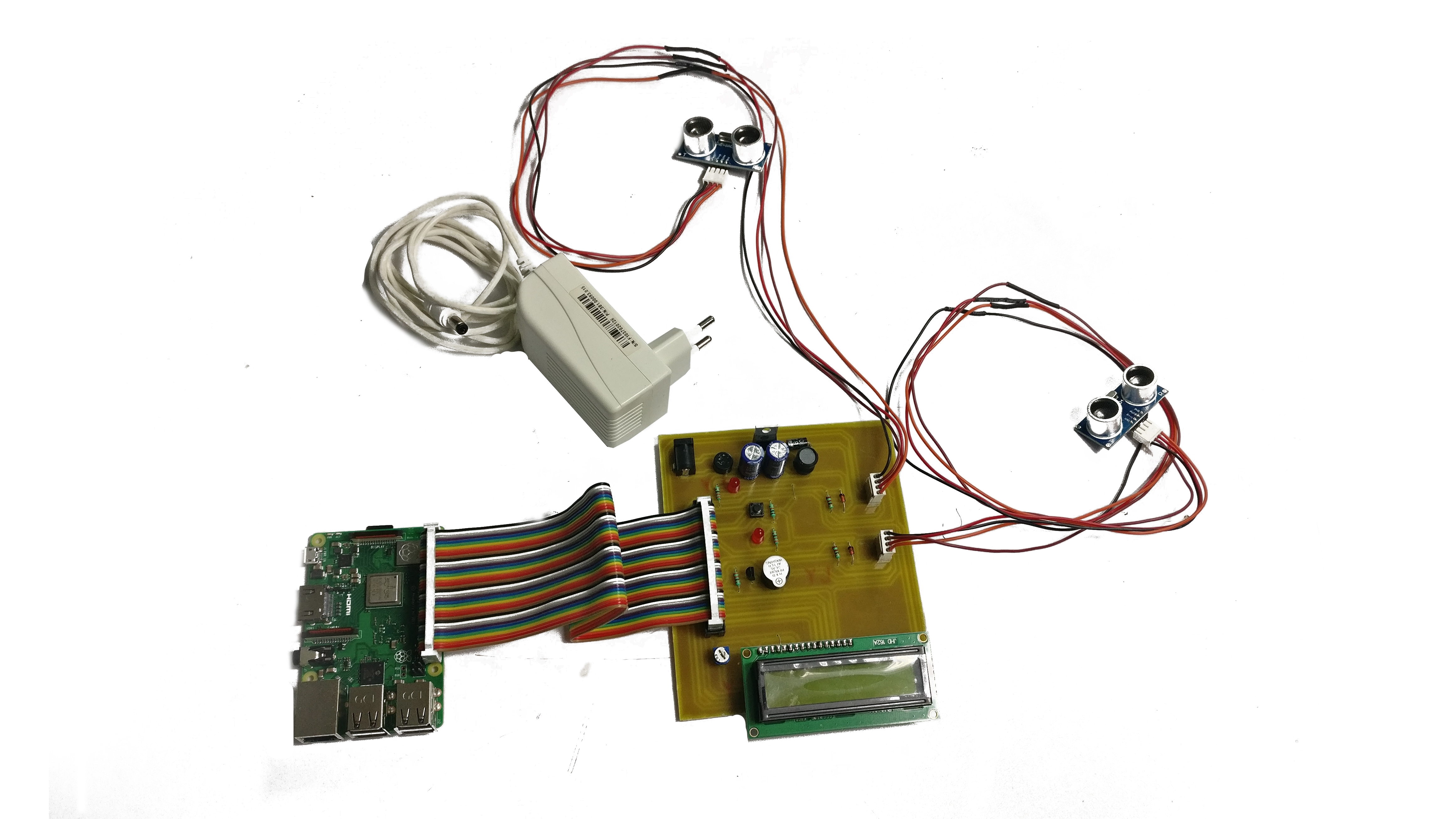
First off, you'll need your IoT device itself, like a Raspberry Pi. These little computers are, arguably, perfect for this kind of project because they're versatile and relatively inexpensive. Then, you'll need a stable internet connection for both your controlling device and the IoT device.
Finally, you'll need an SSH client on your computer, the one you'll be using to connect to your IoT device. OpenSSH is a very popular choice, and it's free. It's basically the standard for secure shell connections, and it's widely supported across different operating systems.
OpenSSH for Windows Users
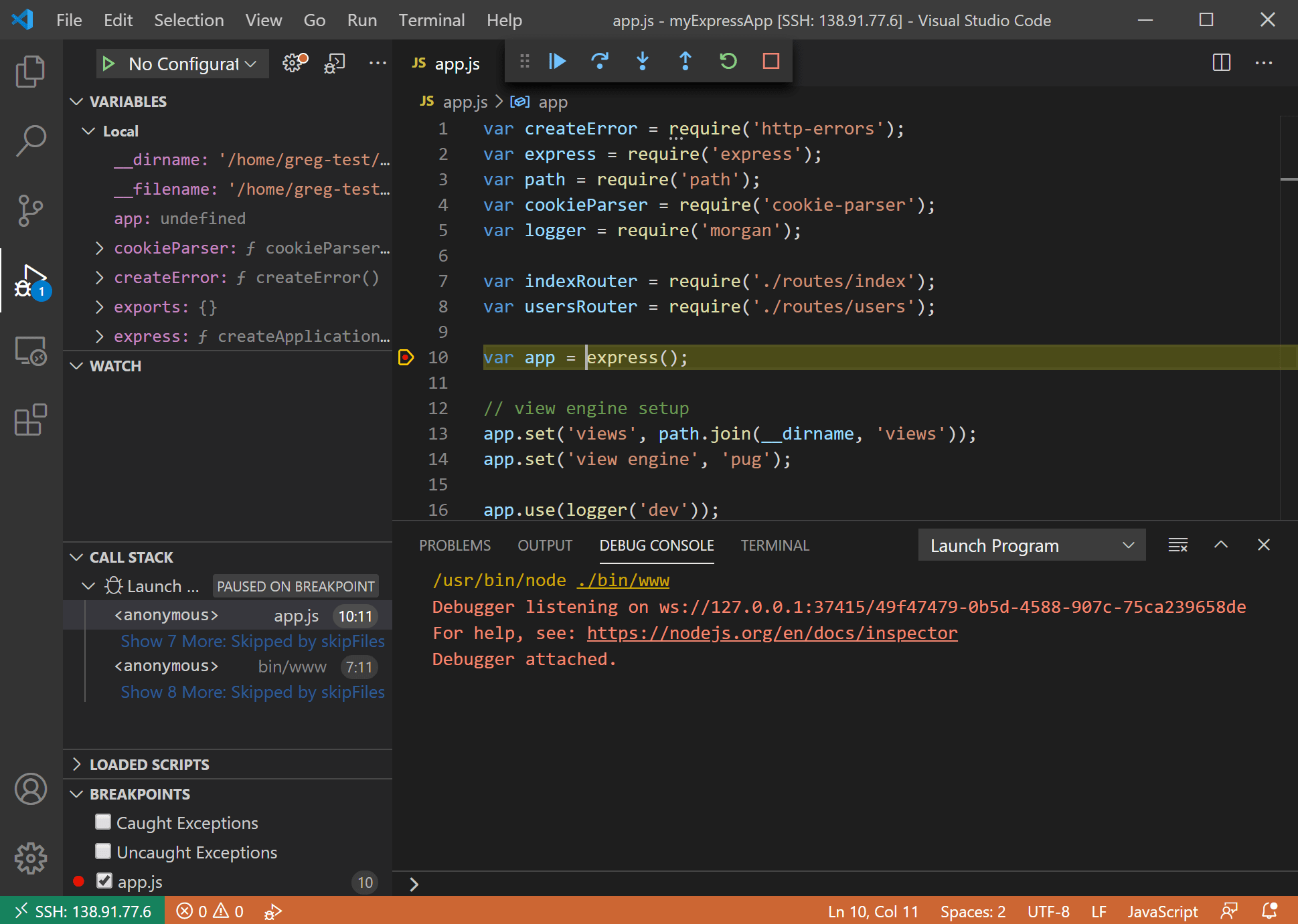
As mentioned earlier, OpenSSH is a great option for Windows users. For a long time, Windows users had to rely on third-party tools like PuTTY for SSH connections. But now, OpenSSH client and server components are built right into Windows 10 and Windows Server, which is really convenient.
This means you can enable the OpenSSH client directly from your Windows settings, making it easier than ever to establish secure connections. You don't need to download extra software, which simplifies things quite a bit, you know. It's a testament to how far Windows has come in supporting open-source tools.
Having OpenSSH readily available on Windows means you can use the command line to connect to your remote IoT devices, just like Linux or macOS users do. This provides a consistent and powerful way to manage your devices, which is, honestly, a huge benefit.
A Step-by-Step Approach to Secure P2P SSH
We'll break down the process of securely connecting your remote IoT devices using P2P SSH. While the exact steps might vary slightly depending on your specific setup, the general flow remains similar. This isn't, you know, rocket science, but it does require attention to detail.
The goal is to establish a direct, encrypted channel between your controlling computer and your IoT device. This channel will allow you to send commands and receive data safely. It's about creating a secure handshake, essentially, between two points.
So, let's get into the practical side of things. We'll cover the main stages you'll go through to get your free P2P SSH connection up and running. It's a pretty satisfying feeling once you get it all working, too.
Setting Up Your Raspberry Pi
First, you'll need to prepare your Raspberry Pi. This means installing an operating system, usually Raspberry Pi OS, and making sure it's fully updated. You'll also want to enable SSH on the Raspberry Pi itself, which is a standard setting, you know.
Many guides online can walk you through the initial setup of a Raspberry Pi. It's a fairly straightforward process, and there are tons of resources if you get stuck. Just make sure you've got a good, stable power supply and a reliable SD card.
Once your Pi is up and running and SSH is enabled, you'll need to figure out its local IP address. This is usually done through your router's interface or by running a command on the Pi itself. This address is what you'll use for the initial local connection, basically.
Configuring SSH
Configuring SSH involves generating SSH keys. These keys are like a digital padlock and key for your connection. You'll have a public key on your Raspberry Pi and a private key on your computer. This is, in fact, a much more secure way to connect than using just a password.
You'll generate these keys on your computer and then copy the public key to your Raspberry Pi. There are specific commands for this, like `ssh-keygen` and `ssh-copy-id`. It sounds a bit technical, but it's really just following a few clear instructions, you know.
Disabling password-based SSH login on your Raspberry Pi after setting up key-based authentication is a very good security practice. This means only someone with your private key can connect, which significantly reduces the risk of brute-force attacks. It's a small step, but it makes a big difference, honestly.
Establishing P2P Connection
Establishing the P2P connection without port forwarding can be done using various methods, often involving a reverse SSH tunnel or services that facilitate NAT traversal. For a free solution, a reverse SSH tunnel is, arguably, the most common approach. This creates a secure "hole" through your firewall, allowing you to connect in.
This usually involves having a third, publicly accessible server (even a very small, free-tier cloud instance or another Raspberry Pi with a public IP) act as a rendezvous point. Your remote IoT device connects *out* to this rendezvous point, and then your controlling computer connects *in* to the same point, effectively creating a tunnel between them. It's a bit like two people meeting in the middle, you know.
There are also free services and tools designed to help with NAT traversal for SSH, which can simplify this step significantly. These tools abstract away some of the complexities, making it easier to securely connect remote IoT devices using P2P SSH free, which is, obviously, what we're aiming for. You might want to explore OpenSSH's official documentation for more advanced tunneling options, too.
Common Challenges and How to Overcome Them
Even with the best intentions, you might run into a few bumps along the road when trying to securely connect remote IoT devices using P2P SSH for free. It's, you know, pretty normal for technology to throw a curveball or two. The good news is, most of these issues have common solutions.
One common area of trouble can be network configurations, especially with firewalls or routers blocking connections. Another might be permissions on your keys or files. It's important to remember that troubleshooting is part of the learning process, and it often leads to a deeper understanding of how things work.
We'll touch on some specific problems that might sound familiar, perhaps from other tech issues you've faced. This will help you get back on track if things don't go perfectly the first time. Persistence is key, honestly.
Browser-Specific Download Issues
You might have experienced something like, "Hi Albert Edelstein, as per your description, it seems issue only happened in Microsoft Edge browser when you are downloading an .msg file from SharePoint online document library." This shows that browsers can, sometimes, behave differently with certain file types or security settings.
While this specific issue is about downloading files, it highlights a broader point: browser-specific quirks can affect how you interact with secure connections or even download necessary tools. If you're having trouble accessing a resource or a setup page, try a different browser. Sometimes, that's all it takes, you know.
Making sure your browser is updated is also a simple but effective step. Outdated browsers can have security vulnerabilities or compatibility problems that prevent smooth operation. It's a basic check, but it can solve a lot of mysterious issues, actually.
General Connection Hurdles
You might encounter messages like, "This connection is untrusted you have asked Firefox to connect securely to bay173.mail.live.com, but we can't confirm that your connection is secure." Or, "I have tried multiple platforms (MS Edge, Firefox, Chrome etc) and to no avail." These indicate a deeper issue with trust or certificate validation.
For P2P SSH, these kinds of browser-related trust issues usually don't directly apply to the SSH tunnel itself, which relies on SSH keys, not browser certificates. However, if you're trying to access a web interface on your IoT device, or if your network setup is causing certificate errors, these messages can appear. It's, like, a symptom of something else.
Troubleshooting general connection hurdles often involves checking your network configuration, firewall rules, and ensuring your SSH keys are correctly set up and have the right permissions. Sometimes, it's just a typo in an IP address or a username. A little patience and systematic checking can usually resolve these problems, which is pretty much the case with most tech issues.
Frequently Asked Questions
Here are some common questions people often have about securely connecting remote IoT devices using P2P SSH for free:
How can I access my Raspberry Pi remotely without port forwarding?
You can access your Raspberry Pi remotely without directly forwarding ports by using a reverse SSH tunnel. This involves setting up a connection from your Raspberry Pi to an intermediate server, then connecting from your local computer to that same intermediate server. This creates a secure pathway, which is, honestly, quite clever. There are also services and tools designed to facilitate NAT traversal for SSH, making this process a bit simpler, too.
Is SSH secure for IoT devices?
Yes, SSH (Secure Shell) is considered a very secure protocol for remote access, including for IoT devices, when implemented correctly. It uses strong encryption to protect data in transit and relies on robust authentication methods like SSH keys. However, its security depends on proper configuration, such as using strong passwords (if you use them at all) and, crucially, keeping your private keys safe. An unpatched device or a weak password can, of course, compromise even a secure protocol.
What is P2P SSH, and how does it work for IoT?
P2P SSH, or Peer-to-Peer Secure Shell, is basically a way to establish a direct, secure connection between two devices without necessarily relying on a central server for the primary connection path. For IoT, this often means your remote device and your controlling computer can communicate directly or via a minimal intermediary that facilitates the initial connection. This is often achieved through techniques like reverse SSH tunnels or specialized P2P networking protocols that help devices find and connect to each other even behind firewalls. It streamlines remote access and can reduce infrastructure costs, which is pretty appealing, you know.
Securely connect remote IoT devices using P2P SSH free solutions is a vital step in protecting your data and devices. By following the guidelines outlined in this article, you can take control of your IoT ecosystem. Learn more about secure IoT connections on our site, and perhaps you'd like to check out our other remote access tips.
- How To Remove Acrylic Nails
- Wasmo Somali Chanel
- Just Give Me My Money
- Lagu Waiting For You
- Steve Horstmeyer Dogs
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide
Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide

Securely Connect Remote IoT P2P SSH Free Download: Your Ultimate Guide