How To Connect SSH IoT Devices Over The Internet Without Windows, Free
Connecting your Internet of Things (IoT) devices from afar, especially without needing a Windows computer and without spending money, is a big deal for many folks. It opens up so many possibilities, you know, for controlling things at home, checking on sensors in a garden, or even managing a small remote setup for a project. People often wonder how to get their little gadgets talking to them when they are not right next to them, and they also want to do it in a way that feels safe and does not cost anything extra.
There is a real desire, it seems, to keep things simple and accessible, particularly for hobbyists or small businesses. Nobody wants to be tied down to one kind of computer, or, you know, have to pay for special software just to check on a tiny sensor. This guide, you see, aims to show you how to set up that kind of connection using tools that are freely available and work on pretty much any operating system that is not Windows, like Linux or macOS.
So, if you have been thinking about how to reach your little internet-connected things from anywhere, and you are using something other than a Windows machine, this is for you. We will go through the steps, more or less, to make that happen, keeping it secure and, very importantly, free. It is a bit like setting up a secret passageway for your devices, only it is totally allowed and rather helpful.
- How To Remove Acrylic Nails
- Blowout Taper Straight Hair
- King Edward Love Chair
- Pam Bondi Have Children
- Shut Up In Spanish
Table of Contents
- Understanding SSH for IoT Devices
- Getting Your IoT Device Ready
- Setting Up Secure Remote Access
- Dynamic DNS for Changing IPs
- Connecting From Your Computer
- Security Best Practices
- Troubleshooting Common Issues
- Frequently Asked Questions
- Final Thoughts
Understanding SSH for IoT Devices
What is SSH and Why It Matters
SSH, or Secure Shell, is a way to get into another computer over a network, and it is very safe. It lets you run commands, move files, and even set up secure tunnels, all while keeping your data private. For IoT devices, this is super important, you know, because many of these little gadgets do not have a screen or a keyboard attached. So, connecting with SSH means you can control them from anywhere, just like you were sitting right in front of them, which is that kind of convenience people really like.
It creates a protected path, so your commands and any information going back and forth are scrambled, making it really hard for anyone else to snoop. This security aspect, that, is what makes SSH the top choice for remote access to tiny computers like Raspberry Pis or other Linux-based IoT things. It is basically the standard for this kind of work, very, very reliable.
Why No Windows and Free?
Many people, perhaps, use Linux or macOS for their daily computer tasks. These operating systems, it turns out, have SSH tools built right in, so you do not need to download anything extra. This makes the whole process simpler and, well, completely free. You are not paying for software licenses or special programs.
- How To Get Rid Of Gnats
- Nice And Slow Lyrics
- Drew Pritchard Divorce
- Sophie Rain Height In Feet
- Randy Travis Jackson Mall Investment
The "free" part also means you can experiment and learn without any upfront cost. This is rather appealing for hobbyists and students, or, you know, anyone just getting started with IoT. It keeps the barrier to entry quite low, allowing more people to get involved and try out their ideas, which is a good thing for innovation, generally.
Getting Your IoT Device Ready
Choosing the Right IoT Device
For this kind of setup, you will typically want an IoT device that can run a full operating system, or at least something that supports SSH. Things like a Raspberry Pi, an Orange Pi, or even some older Android phones repurposed for IoT work really well. These devices, you see, are powerful enough to handle the SSH server software and manage network connections.
Make sure your chosen device has a way to connect to your home network, either with Wi-Fi or an Ethernet cable. Most small single-board computers, as a matter of fact, come with these options built in. It is pretty essential for getting them online in the first place, obviously.
Initial Setup and Network Access
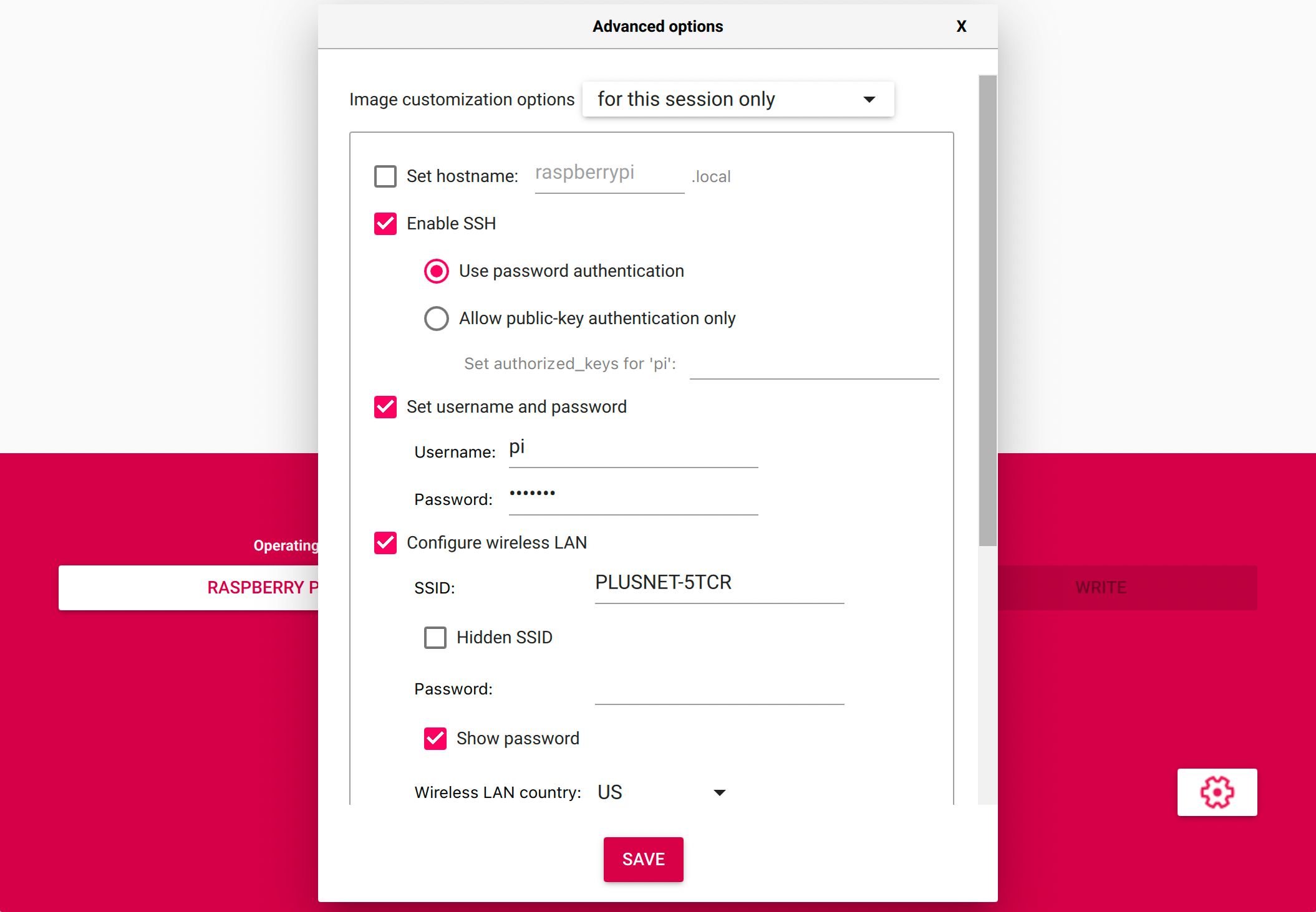
First things first, you need to get your IoT device powered on and connected to your local network. This usually involves flashing an operating system image, like Raspberry Pi OS (formerly Raspbian) for a Raspberry Pi, onto a micro SD card. Then, you put the card into the device, plug it in, and connect it to your router.
Once it is on your network, you will need to find its local IP address. You can often do this by logging into your router's administration page and looking at the list of connected devices. Or, you might use a network scanning tool on your computer. Knowing this local IP is basically how you will first talk to your device before setting up internet access, so, you know, it is a key step.
Setting Up Secure Remote Access
Installing an SSH Server on Your Device
Most Linux-based IoT operating systems do not come with an SSH server running by default, though some might have it pre-installed. You will need to install OpenSSH Server. You can usually do this by connecting a keyboard and monitor to your device, or by using an initial local SSH connection if it is already enabled. Then, you open a terminal and type a command like sudo apt update and then sudo apt install openssh-server. This gets the server software onto your device, making it ready to listen for incoming connections, which is pretty neat.
After installation, the SSH server should start automatically. You can check its status by typing sudo systemctl status ssh. If it is running, you are in good shape. If not, you might need to start it manually with sudo systemctl start ssh. This step is pretty straightforward, but it is, you know, the heart of getting your remote connection going.
Generating and Managing SSH Keys
Using SSH keys for authentication is a much safer way to connect than just using a password. It involves creating a pair of keys: a private key that stays on your computer and a public key that you put on your IoT device. When you try to connect, your computer uses the private key to prove it is you, and the device checks it against the public key it has.
To make these keys on your Linux or macOS computer, you open a terminal and type ssh-keygen. It will ask you where to save the keys and for a passphrase. A passphrase is like a password for your private key, adding an extra layer of security. Once generated, you copy the public key to your IoT device using a command like ssh-copy-id username@device_ip. This is a very secure method, arguably the best practice, for remote access.
Port Forwarding and Router Configuration
For your IoT device to be reachable from the internet, your home router needs to know where to send incoming SSH requests. This is called "port forwarding." You log into your router's administration page, find the port forwarding section, and create a new rule. You will tell the router to send any traffic coming in on a specific external port (like 2222, not the default 22 for security reasons) to your IoT device's local IP address and its SSH port (usually 22).
This step, so, is a bit like telling your mail carrier that letters addressed to "IoT Device" should actually go to a specific apartment number inside your house. Every router is a little different in how you set this up, but the basic idea is the same. It is a pretty crucial step for getting outside access, you know, to work.
Dynamic DNS for Changing IPs
What is Dynamic DNS?
Most home internet connections use what is called a "dynamic IP address," meaning your public IP address changes from time to time. This is a problem if you want to connect to your IoT device from the internet, because you need to know its current public IP. Dynamic DNS (DDNS) solves this. It links a memorable hostname (like "myiotdevice.ddns.net") to your ever-changing public IP address.
When your public IP changes, a small client on your router or device updates the DDNS service with the new IP. So, you can always use the same hostname to reach your device, no matter what your current IP address is. It is, basically, a clever way to keep track of a moving target, which is very helpful for remote access.
Selecting a Free DDNS Provider
There are several services that offer free DDNS accounts. Some popular ones include No-IP, DuckDNS, and Afraid.org. Each has its own sign-up process and might require you to periodically confirm your hostname to keep it active. You will want to pick one that is easy to set up and, you know, seems reliable for your needs.
Look for a provider that has good documentation and perhaps even direct support in your router's firmware. This makes the setup process much smoother. It is a bit like choosing a good mailing service for your dynamic address, so, you know, choose wisely.
Configuring DDNS on Your Router or Device
The easiest way to set up DDNS is usually directly on your router. Most modern routers have a section in their settings for DDNS, where you can select your provider, enter your account details, and the hostname you chose. The router will then automatically update the DDNS service whenever your public IP address changes. This is, apparently, the most common way to do it.
If your router does not support DDNS, or does not support your chosen provider, you can install a small client program on your IoT device itself. This client will periodically check your public IP and update the DDNS service. This might be a little more involved, but it certainly gets the job done. It is, in a way, like having a dedicated messenger for your device's address.
Connecting From Your Computer
Using the Terminal for SSH
On Linux and macOS, connecting via SSH is as simple as opening a terminal window. You use the ssh command, followed by your username on the IoT device and the hostname you set up with DDNS, plus the port number if you changed it. For example, it might look like ssh -p 2222 pi@myiotdevice.ddns.net. The -p specifies the port number, so, you know, make sure that matches your port forwarding rule.
The first time you connect, your computer might ask you to confirm the device's fingerprint. This is a security measure to ensure you are connecting to the right device and not, you know, some imposter. Once confirmed, you will be prompted for your SSH key passphrase if you set one, and then you will be logged into your IoT device's command line, ready to issue commands. It is pretty cool, actually, how quickly you can get connected.
SSH Client Alternatives
While the terminal is the most common way, there are graphical SSH clients available for Linux and macOS if you prefer a visual interface. Tools like Termius or Remmina offer features like connection profiles, tabbed sessions, and sometimes even built-in SFTP for file transfers. These can make managing multiple IoT devices a little easier, especially if you have many of them. They basically wrap the command-line SSH tool in a friendlier package, which some people find very helpful.
These clients, too, often support SSH key management, so you can easily select which key to use for which connection. They might also offer other connection types, like VNC or RDP, if your IoT device supports those as well. For someone who prefers clicking buttons over typing commands, these are great options, apparently.
Security Best Practices
Strong Passwords and Key Security
Even though you are using SSH keys, your IoT device still has a password for the user account. Make sure this password is very strong and unique. Do not use default passwords like "raspberry" for a Raspberry Pi. Change it immediately after the first setup. Also, protect your private SSH key on your computer with a strong passphrase. This passphrase, you know, stops anyone who gets hold of your key file from using it.
Treat your private SSH key like a house key. Do not share it, and keep it in a secure place on your computer. If you suspect your private key has been compromised, generate a new one and remove the old public key from your IoT devices. Security is, quite frankly, an ongoing effort, so, you know, always be vigilant.
Limiting Access and Firewall Rules
On your IoT device, you should configure its firewall (like UFW on Linux) to only allow SSH connections from specific IP addresses if possible. If you have a static IP address at your main location, you can set the firewall to only accept SSH connections from that IP. This dramatically reduces the risk of unwanted access. It is a bit like putting up a very specific gate for only certain visitors.
Also, consider changing the default SSH port (22) on your device to something else, like 2222 or 54321. This does not make it truly more secure, but it helps prevent automated scanning bots from finding your SSH server easily. It is, basically, a way to fly under the radar of casual attackers, which is a good thing for security, generally.
Troubleshooting Common Issues
Sometimes, things do not work right away, and that is perfectly normal. If you cannot connect, first, double-check your port forwarding settings on your router. Make sure the external port, the internal IP address of your device, and the internal port all match up correctly. A common mistake is using the wrong internal IP, especially if your device's IP changes locally.
Next, check your IoT device's firewall. Make sure it is not blocking incoming SSH connections. You can temporarily disable it for testing, but remember to re-enable it afterwards. Also, verify that the SSH server is actually running on your device. You can use the sudo systemctl status ssh command to see its current state. Often, it is just a small typo or a setting that is off, so, you know, take your time checking things.
Frequently Asked Questions
Can I connect to my IoT device if it is behind a cellular network?
Connecting to an IoT device behind a cellular network can be a bit tricky, you know, because cellular providers often use something called "CGNAT" (Carrier-Grade NAT). This means your device does not get a public IP address directly, making port forwarding impossible. For these situations, you might need to use a VPN service that offers a public endpoint, or perhaps a reverse SSH tunnel to a server with a public IP. It is a more involved setup, apparently, but certainly doable.
Is SSH secure enough for sensitive IoT data?
SSH itself is very secure for the connection it creates. It encrypts all data exchanged and authenticates both ends of the connection. However, the overall security of your sensitive IoT data also depends on other factors, such as the security of the operating system on your IoT device, the applications running on it, and how you manage your SSH keys. It is, basically, one strong link in a chain, so, you know, make sure all the other links are strong too.
What if my internet service provider blocks certain ports?
Some internet service providers (ISPs) might block common ports, like port 22, for security reasons or to prevent customers from running servers. If you suspect this is happening, you can try changing the external port you use for SSH in your router's port forwarding settings to a less common one, like 2222 or 8080. Most ISPs do not block these higher-numbered ports, so, you know, it is worth a try. You will just need to remember to specify that new port when you connect. Learn more about secure remote access on our site, and link to this page for more IoT security tips.
Final Thoughts
Setting up remote SSH access to your IoT devices without Windows and for free is absolutely possible, and it gives you a lot of freedom. It is a process that builds on basic networking and security ideas, so, you know, taking it step by step makes it very manageable. With a bit of patience and attention to detail, you will have your tiny computers talking to you from anywhere in no time. It is a pretty empowering feeling, actually, to have that kind of control over your own devices.
- Remoteiot Monitoring Ssh Download Android
- Julesari Leaks
- Help I Accidentally Forgot How Gravity Works
- Blowout Taper Straight Hair
- 6 Guard Buzz Cut

How To Connect SSH IoT Device Over Internet On Mac Without Extra Hassle
How To Connect SSH IoT Device Over Internet On Mac Without Extra Hassle
Secure SSH For IoT: Remote Access & Control Guide