Securely Connect Remote IoT Raspberry Pi To AWS VPC: A Guide For Peace Of Mind
Connecting tiny devices like a Raspberry Pi to a bigger cloud network, especially when they are far away, can feel a bit like setting up a complex puzzle. You want your little computer, perhaps gathering weather data or watching a space, to talk to your main cloud services without any trouble. But more than just making it work, you really need to make sure those connections are safe and sound. It's like making sure a door is securely fastened, so nothing unwanted gets in or out, and your information stays private. This is about building trust in your system, which, you know, is pretty important.
Think about it: your Raspberry Pi might be in a field, a factory, or even your home, sending information to your private cloud space on Amazon Web Services (AWS). This connection needs to be free from danger, just like keeping important documents securely put away so they cannot be lost or stolen. An untrusted connection, similar to what you might see with a browser warning, can put your device at risk. We want to avoid that entirely, as a matter of fact.
This guide will walk you through how to securely connect a remote IoT Raspberry Pi to an AWS Virtual Private Cloud (VPC). We will talk about keeping your data safe and ensuring everything stays under your control, giving you a real sense of peace. It's about setting things up right from the start, so you can have confidence in your system today, on June 12, 2024, and well into the future, you see.
- Steve Horstmeyer Dogs
- Mid Taper Textured Fringe
- Hannah Love Is Blind
- Dress To Impress Creator Gigi
- Niece In Spanish Language
Table of Contents
- Why Security Matters for IoT Devices
- What is AWS VPC and Why Use It for IoT?
- Raspberry Pi as an IoT Edge Gadget
- Foundational Security Steps for Your IoT Set-Up
- How to Securely Connect Your Pi to AWS VPC: A General Approach
- Frequently Asked Questions
Why Security Matters for IoT Devices
Putting a Raspberry Pi out in the world to gather information or control things means it becomes a part of your digital life, you know. Just like keeping your home safe, or making sure your school devices are secure when they come home, these little IoT gadgets need protection. If they are not securely attached, anything that falls could cause a problem, and sudden changes can affect everything. An insecure device is an open door, basically.
Consider the information it might handle. Maybe it is temperature readings, maybe it is security camera footage, or perhaps it is something even more personal. If someone can access that device without permission, they could steal data, mess with operations, or even use your device to cause trouble elsewhere. This is why having things securely guarded is so important. It brings a lot of peace of mind, really.
When we talk about "securely," we mean free from danger, where everything stays under your control. An untrusted connection is a big warning sign, telling you there is a problem connecting safely. We want to avoid that feeling entirely, so your information and systems are always protected. This means building a system where you can quickly account for everything, even in an emergency, you see.
- Punta Cana Missing Girl
- Randy Travis Jackson Mall Investment
- Sophie Rain Spiderman Video
- What Is A Golden Birthday
- Nice And Slow Lyrics
What is AWS VPC and Why Use It for IoT?
An AWS Virtual Private Cloud, or VPC, is like having your own private section of the AWS cloud. You get to set up your own network within AWS, with your own IP addresses, subnets, and network rules. It is a bit like having your own private office building within a much larger city, where you control who comes and goes, and how they get around. This is a pretty big deal for keeping things separate and safe, actually.
For IoT, using a VPC is super helpful because it lets you keep your devices' communications separate from the public internet. Instead of your Raspberry Pi talking directly to a public server, it can talk to services within your private VPC. This significantly reduces the chances of unwanted access. It means your data travels on a path you define, which is, in a way, like having your own dedicated, guarded road for your information.
This isolation means that even if someone were to try and get to your IoT system, they would first have to get into your private VPC. That adds a very strong layer of protection. It is about creating a safe space for your IoT data and applications, so you can feel confident that your systems are well-protected, more or less.
Raspberry Pi as an IoT Edge Gadget
The Raspberry Pi is a tiny, affordable computer that has become a favorite for many IoT projects. It is small, uses little power, and can do quite a lot, from collecting information to running small applications right where the action is. We call this "edge computing" because the processing happens closer to where the data is created, rather than sending everything straight to the cloud, you know.
Because of its size and flexibility, a Raspberry Pi can be placed in many different spots, often far from your main office or data center. This makes it a perfect fit for remote IoT tasks. However, its remote nature also means it needs careful thought about how it connects and stays secure. A device out in the open needs to be securely fastened, after all, to avoid any issues.
When a Raspberry Pi is out there, it is not just a simple sensor; it is a computer. This means it has an operating system, software, and network connections, all of which need to be protected. Just like your home computer needs security updates, so does your Pi. It is a bit like making sure all the windows and doors of a house are locked, even if it is in a quiet area, because you just never know, apparently.
Foundational Security Steps for Your IoT Set-Up
Building a secure connection for your remote Raspberry Pi to AWS VPC means putting several layers of safety in place. It is not just one thing; it is a combination of good practices that work together to keep your system free from danger. This approach helps ensure everything stays under your control, offering that peace of mind we talked about, you see.
Network Separation: VPC, Subnets, and Security Groups
Within your AWS VPC, you can create subnets, which are smaller, isolated parts of your network. Think of them as different rooms in your private office building. You can put your IoT-related services in one subnet and other services in another. This way, if one part gets compromised, the damage is contained. It is a good idea to separate things, basically.
Security groups act like firewalls for your individual devices or services within the VPC. They control what kind of network traffic can go in and out. You can set rules that say, for example, "only allow connections from this specific IP address" or "only allow traffic on this particular port." This helps make sure that only trusted connections are made, which is pretty important, actually.
Using these tools means you are not just hoping for the best; you are actively defining the boundaries and rules for your network traffic. It is a bit like having very specific access cards for different areas, making sure only the right people can get to the right places. This helps keep things very secure, so you can rest easy, more or less.
Identity and Access Control: IAM and Certificates
Every device and service that connects to your AWS account needs an identity. AWS Identity and Access Management (IAM) helps you manage who or what can do what in your cloud. For your Raspberry Pi, you would give it a specific identity and permissions, so it can only perform the tasks it needs to, and nothing more. This is about making sure everything is securely attached to its proper role, you know.
For IoT devices like the Raspberry Pi, certificates are often used for identification. These are like digital passports. When your Pi tries to connect to AWS IoT Core, it presents its unique certificate. AWS checks if that certificate is valid and if the Pi has the right to connect. If the connection is untrusted, it will be stopped. This system helps confirm that your connection is secure, which is a big deal, frankly.
This process ensures that only your authorized devices can talk to your AWS services. It is a very strong way to control who gets in. This kind of careful identity checking helps keep everything under your control, and that gives you a lot of peace of mind, you see.
Data Scrambling: TLS/SSL
Even if you have strong identity checks, the information itself needs protection as it travels across the network. This is where Transport Layer Security (TLS) and Secure Sockets Layer (SSL) come in. These are methods for scrambling data, so if someone were to intercept it, they would just see gibberish. It is like putting your important messages in a secret code that only the sender and receiver can understand, you know.
When your Raspberry Pi sends data to AWS, or when AWS sends commands back to your Pi, this communication should always happen over a TLS/SSL encrypted channel. This ensures that the data remains private and cannot be tampered with while in transit. An untrusted connection usually means this scrambling is not happening, leaving your data exposed. We definitely want to avoid that, so.
Making sure all your IoT communications use TLS/SSL is a basic but absolutely vital step. It is about making sure your data is free from danger as it moves from your Pi to your VPC. This helps you take full control over your privacy, which is something everyone wants, pretty much.
Device Handling: AWS IoT Core and Device Defender
AWS IoT Core is a managed service that helps you connect and manage billions of IoT devices. It acts as a central hub for your devices to communicate with AWS services. It handles things like device authentication, message routing, and shadow states (a virtual representation of your device). It is a very useful tool for keeping track of your devices, basically.
AWS IoT Device Defender helps you audit and monitor your IoT device configurations to make sure they stick to security best practices. It can detect unusual behavior that might point to a security problem, like a device trying to communicate from an unexpected IP address or sending too much data. This is like having a watchful eye on all your devices, ready to quickly account for any issues, you know.
Using these services helps you keep a close watch on your entire IoT fleet. It is about being proactive rather than reactive when it comes to security. This helps ensure that your devices are always securely attached to your network, reducing risks and giving you more peace of mind, really.
Software Updates for Your Pi
Your Raspberry Pi runs an operating system and various software programs. Just like any computer, these need regular updates. Software updates often include fixes for security weaknesses that bad actors could exploit. If your device is out of date and missing important security updates, it is at risk. This is a very common problem, actually.
It is important to set up a process for regularly updating your Raspberry Pi's operating system and any software it runs. This could involve automated updates or a schedule for manual updates. Keeping your Pi's software current is a straightforward way to keep it more securely connected. It is a bit like making sure all your physical locks are always in good working order, so.
Neglecting updates is like leaving a door unlocked. It creates an easy way for problems to get in. So, make sure to keep your Pi's software fresh to maintain its safety. This simple step helps ensure your entire setup stays free from danger, giving you better control, you see.
Physical Safety for Your Pi
While we talk a lot about digital security, the physical safety of your Raspberry Pi is also important. If someone can physically access your device, they might be able to bypass some of your digital protections. This is especially true for remote deployments. The door was securely fastened for a reason, after all.
Consider putting your Raspberry Pi in a secure enclosure, perhaps one that is tamper-proof or requires tools to open. Place it in a location that is not easily accessible to unauthorized individuals. If it is in a public or semi-public space, this becomes even more important. The offices were securely guarded for a reason, you know.
Physical security is the first line of defense for any device. It helps prevent someone from directly manipulating your Pi, which could lead to bigger security problems. So, give some thought to where and how your Pi is placed. This step, while seemingly basic, contributes significantly to keeping everything securely attached and free from danger, in a way.
How to Securely Connect Your Pi to AWS VPC: A General Approach
Bringing all these pieces together to securely connect your remote Raspberry Pi to an AWS VPC involves several steps. This is a general guide, and specific details might change based on your exact project, you know. But the core ideas remain the same for keeping things safe, so.
Step 1: Set Up Your AWS VPC and Subnets
Start by creating a new VPC in your chosen AWS region. Give it a private IP address range, like 10.0.0.0/16. Inside this VPC, create at least two subnets: one public and one private. The public subnet might have an internet gateway for limited, controlled outbound access, while your private subnet will house your sensitive resources. This separation is key for security, basically.
You might put your AWS IoT Core endpoints or other services your Pi needs to talk to in the private subnet. This way, they are not directly exposed to the public internet. This helps make sure your internal network is a bit more protected, you see.
Step 2: Configure Security Rules
Set up network Access Control Lists (ACLs) for your subnets and security groups for your instances. ACLs act like a firewall for your subnets, controlling traffic at a broader level. Security groups are more specific, acting as a firewall for individual devices. For your Raspberry Pi, you will want a security group that only allows necessary inbound and outbound connections. This is about being very specific with permissions, you know.
For example, you might allow outbound HTTPS traffic to AWS IoT Core endpoints and specific ports for any remote management tools you use, but nothing else. This helps ensure that your connection is trusted and not open to just anything. It is a bit like having a very strict bouncer at the door, only letting in those who are supposed to be there, apparently.
Step 3: Prepare Your Raspberry Pi
Install the latest version of Raspberry Pi OS on your device. Make sure it is fully updated with all the latest security patches. Install any necessary software or libraries for your IoT application. This might include the AWS IoT Device SDK for Python or Node.js, depending on your programming language choice. This step is about getting your Pi ready for its job, you see.
Also, disable any services you do not need on the Pi to reduce its attack surface. For example, if you are not using a desktop environment, you can often remove it to save resources and improve security. Less software means fewer potential weaknesses, which is, in a way, a good thing, so.
Step 4: Link Your Pi to AWS IoT Core
In AWS IoT Core, register your Raspberry Pi as a "thing." This will involve creating a unique thing name, generating X.509 certificates for authentication, and attaching an IAM policy. The policy defines what your Pi is allowed to do within AWS IoT Core, like publish messages to certain topics or subscribe to others. This is about giving your Pi its proper identity and permissions, basically.
Copy these certificates and the private key to your Raspberry Pi. Configure your IoT application on the Pi to use these credentials when connecting to AWS IoT Core. This ensures that all communication between your Pi and AWS IoT Core is authenticated and encrypted using TLS/SSL. It helps confirm that your connection is secure, so you can avoid any untrusted warnings, you know.
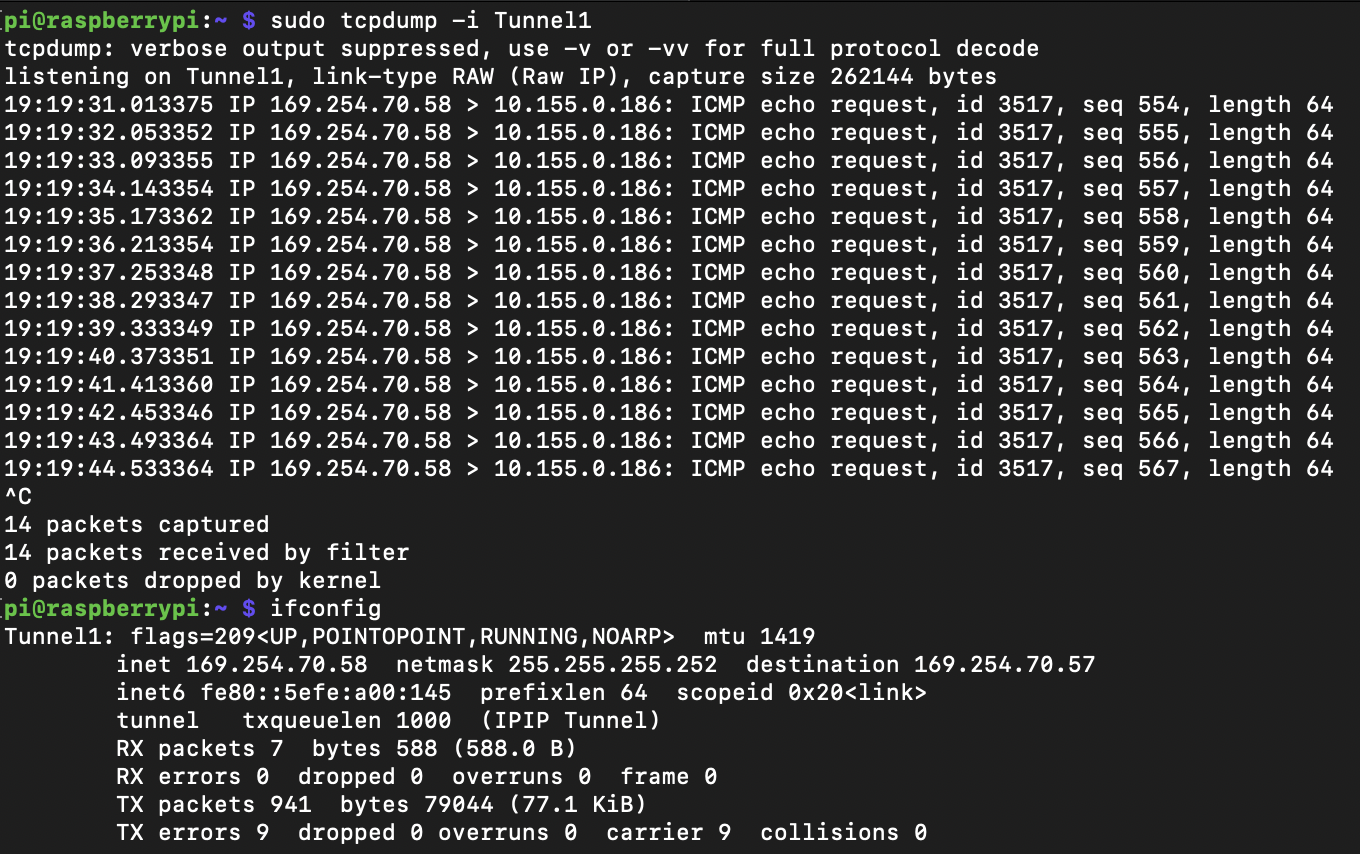
Step 5: Create a Secure Pathway
For remote access to your Pi or for direct Pi-to-VPC communication, you have a few options. One common way is to use a Virtual Private Network (VPN) connection. You could set up an OpenVPN server within your VPC, or use AWS Client VPN endpoint. Your Raspberry Pi would then connect to this VPN, creating a secure, encrypted tunnel into your private network. This is like building a secret tunnel directly to your private office, you see.
Alternatively, for simpler IoT data exchange, AWS IoT Core itself provides secure, authenticated communication channels. Your Pi connects to IoT Core over MQTT or HTTPS, and IoT Core then routes messages to other AWS services within your VPC, like Lambda functions or databases, without the need for a direct VPN tunnel to the Pi itself. This is often simpler for just data movement, basically.
Choose the method that best fits your needs for direct access versus just data exchange. Both approaches help ensure your connection is free from danger. It is about picking the right tool for the job to keep everything securely attached, you know.
Step 6: Watch and Check Your System
After setting everything up, it is very important to monitor your system. Use AWS CloudWatch to keep an eye on your Pi's connection status, data usage, and any errors. AWS IoT Device Defender can help you audit your device configurations and detect unusual behavior. Regularly check your security group logs and VPC flow logs for any suspicious activity. This is like having a security guard always watching, you know.
Also, perform regular security audits and penetration tests if your project is critical. This helps you find any weaknesses before bad actors do. Remember to keep your Raspberry Pi's software updated and rotate your certificates regularly. This ongoing care helps ensure your system remains free from danger and gives you peace of mind, basically. Learn more about AWS IoT security on our site, and link to this page for general
- Timothee Chalamet Net Worth
- Abbey Love On The Spectrum
- 405 Howard Street San Francisco
- How To Remove Acrylic Nails
- In The Clurb We All Fam

Securely Connect Remote IoT VPC Raspberry Pi AWS: A Comprehensive Guide
Securely Connect Remote IoT VPC Raspberry Pi AWS Free: A Comprehensive
Securely Connect Your IoT Devices Using Raspberry Pi And AWS VPC