Securely Connect Remote IoT P2P Raspberry Pi: Your Guide To Safe Connections
Connecting small devices, like your Raspberry Pi, to the wider internet for IoT projects can feel a bit like stepping into a wild, open space. You want your smart home gadgets or industrial sensors to talk to each other, or to you, from far away. Yet, this kind of connection, you see, often brings up big worries about keeping things safe. It's not just about getting things to link up; it's about making sure those links are truly secure, especially when your system might be feeling a bit out of date, or you get those messages saying a connection is untrusted, which, honestly, can be pretty unsettling.
People often wonder if their devices are really protected when they're out there, doing their thing. You might have seen messages, perhaps like the one Jerrywoods2 mentioned, about a device being at risk because it's missing important updates. Or maybe you've had Firefox tell you it can't confirm a connection is secure, just like with a mail server or some other website. These moments, quite frankly, highlight a real need for solid, trustworthy ways to manage your remote IoT setups, particularly when you're using something like a Raspberry Pi, which is so versatile, but also needs care.
This guide is here to help you get a handle on how to **securely connect remote IoT P2P Raspberry Pi** setups. We will look at how these tiny computers can talk directly to other machines, without always needing a big central server, and how to keep those conversations private and protected. It's about getting you back on track so your connections run more securely, making sure your remote IoT projects are not just working, but working safely, which, arguably, is the most important part.
- Two Babies One Fox Comic
- What Does Wap Mean
- Deep Winter Color Palette
- Boo Did I Scare You Im A Job Application
- Randy Travis Jackson Mall Investment
Table of Contents
- Understanding P2P for IoT with Raspberry Pi
- Setting Up Your Raspberry Pi for Secure P2P
- Making Your P2P Connections Strong
- Practical Steps for Secure Remote Access
- Frequently Asked Questions
- Final Thoughts on Secure IoT with Raspberry Pi
Understanding P2P for IoT with Raspberry Pi
When we talk about IoT, we're thinking about devices that connect and share information. Think smart light bulbs, temperature sensors in a greenhouse, or even a tiny camera watching your pet. Usually, these devices might send their data to a central server, like a cloud service, and then you check that server to see what's happening. But with P2P, which means "peer-to-peer," it's a bit different. It's almost like your Raspberry Pi talks directly to another device, or to your computer, without that middleman server. This decentralized way of doing things, you know, can be really useful.
Why P2P Matters for Your Remote IoT
A P2P setup offers some good things for your remote IoT projects. For one, it can mean lower costs, since you might not need to pay for a big, always-on central server. This is especially true if you're looking to **securely connect remote IoT P2P Raspberry Pi** devices without spending a dime on servers, which, quite honestly, sounds pretty appealing. Also, direct connections can sometimes be quicker and more reliable because there are fewer steps for the data to travel. It gives you, in a way, more direct control over your devices, which is a nice feeling.
This approach means your Raspberry Pi connects straight to other devices or machines. It means they can communicate with each other directly, which, in some respects, is a very strong way to look after and control your network from just about anywhere. This kind of setup, you see, offers a different way to manage your remote gadgets, making them feel more like part of your local network, even when they are far away. It's a method that gives you a lot of freedom, which is something many people appreciate.
- How Long Does It Take For Eyelashes To Grow Back
- Wasmo Somali Chanel
- Kay And Tay Abuse Allegations
- Timothee Chalamet Net Worth
- Jamaican Restaurants Near Me
Common Connection Worries
However, with this freedom comes the need for careful handling. Just like Jerrywoods2 mentioned, sometimes devices can be at risk if they are out of date, missing important updates. You might also run into messages saying a connection is untrusted, like when Firefox can't confirm a secure link to a website. These warnings, they really do tell us that simply connecting isn't enough; we need to make sure those connections are truly safe. A problem connecting securely to a website, for instance, shows us that security is a big piece of the puzzle, and it's something we need to think about from the very beginning.
The promise of interconnected devices, from smart homes to industrial sensors, is immense, that is true. But so are the security challenges. The ability to **securely connect remote IoT P2P Raspberry Pi** devices is not just a nice extra; it's a fundamental requirement for anyone working with IoT. If your connection is untrusted, or your device is at risk because it's missing updates, your whole system could be open to problems. We need to make sure our Raspberry Pi devices are set up to handle these connections safely, which, quite frankly, is a task that needs our attention.
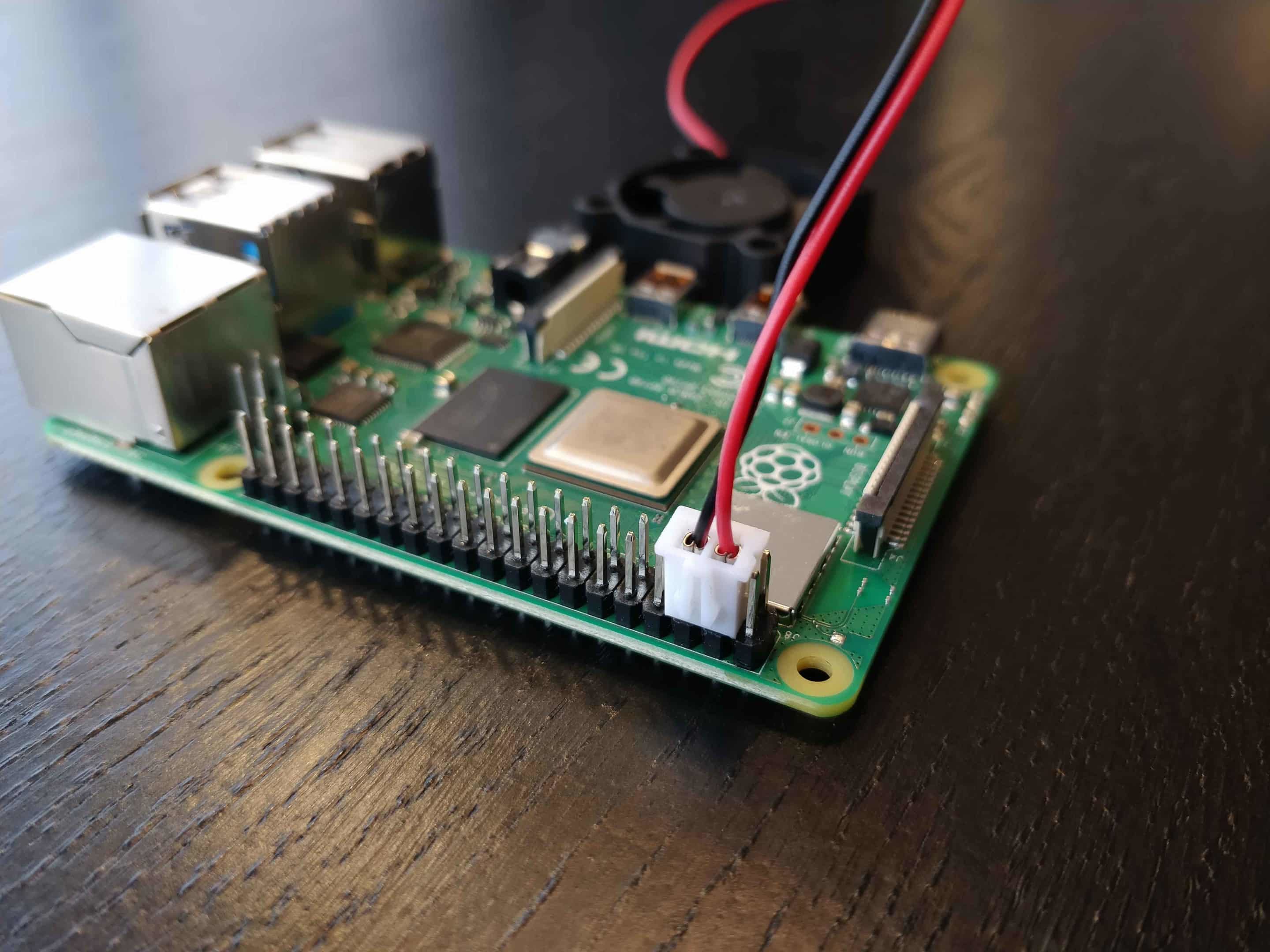
Setting Up Your Raspberry Pi for Secure P2P
Getting your Raspberry Pi ready for secure P2P connections involves a few important steps. It's not overly complicated, but it does mean paying attention to some key details. Think of it like preparing your home for visitors; you want to make sure the doors are locked and only the right people can come in. The goal is to establish a connection that is not only functional but also trustworthy, which, basically, means protecting your data and your devices from unwanted access.
Keeping Your Pi Up-to-Date
One of the most straightforward ways to keep your Raspberry Pi secure is to keep its software current. Just like your Windows computer needs updates to run more securely, your Pi needs them too. An out-of-date system can be missing important security and quality updates, which leaves it vulnerable. This is a common issue, as Jerrywoods2's original title suggested, where a device is at risk because it's out of date. Regularly updating your Raspberry Pi's operating system and installed programs is a simple yet very powerful step. You can usually do this with just a few commands in the terminal, which is pretty convenient.
It's a good idea to set up a routine for checking and applying updates. This helps make sure your Pi always has the latest security fixes, protecting it from known weaknesses. Think of it like putting on a fresh coat of armor; it helps keep everything safe. This practice, you know, is a core part of maintaining any secure system, whether it's a big server or a small Raspberry Pi handling your remote IoT tasks. It helps you avoid those troubling messages about untrusted connections, too, which is always a plus.
SSH: Your Secure Doorway
When you want to connect to your Raspberry Pi remotely, especially for managing IoT devices, SSH (Secure Shell) is your best friend. It's a way to access your Pi's command line over an encrypted connection. This means that whatever you send or receive is scrambled, making it very hard for anyone else to understand. This guide will walk you through the process of **securely connect remote IoT P2P SSH Raspberry Pi** environments, offering a free download option for essential software, which is quite helpful.
Using SSH is a pretty strong way to look after and control your network from just about anywhere. It ensures that your commands and data stay private as they travel across the internet. Without SSH, your connection might be like talking in a public square; with it, it's more like a private conversation. So, setting up SSH correctly is a big piece of the puzzle for a secure P2P setup. It's the standard for secure remote access, and for good reason, too.
Firewall and NAT Considerations
Often, your Raspberry Pi will be sitting behind a firewall or a NAT (Network Address Translation) router, especially in a home or office network. These devices act as a barrier between your internal network and the outside world. While they offer protection, they can also make it tricky to connect directly to your Pi from somewhere else. Key features of remote IoT, like remotely accessing a Raspberry Pi behind a firewall or NAT router, mean you can connect to it from anywhere as if it was on the local network. This is where P2P methods really shine, which, you know, is quite useful.
To make P2P connections work through these barriers, you might need to set up port forwarding on your router or use special services that help punch through. Some solutions allow you to send commands and batch jobs to your Raspberry Pi from the web, which is pretty neat. The idea is to create a direct path for your P2P connections while still keeping your network safe from unwanted visitors. It's about finding that balance between accessibility and security, which, in some respects, is a continuous effort.
Making Your P2P Connections Strong
Beyond the basic setup, there are more ways to make your P2P connections for your Raspberry Pi even stronger. It's like adding extra locks to your doors or setting up an alarm system. These steps help ensure that your remote IoT devices are not only talking to each other but doing so in a way that truly protects your data and privacy. It's about building trust in your connections, especially when you're dealing with sensitive information or controlling important systems, which, honestly, can be a big responsibility.
Choosing the Right Tools
When you're looking to **securely connect remote IoT P2P Raspberry Pi** devices, the software and services you pick matter a lot. There are various tools available that help facilitate P2P connections, some free, some paid. If you're looking to do this without spending a dime on servers, you're in a good spot because there are many open-source options. These tools often come with built-in security features, like strong encryption, which is very important.
It's worth looking into solutions that are specifically designed for secure P2P communication, especially those that offer end-to-end encryption. This means that your data is scrambled from the moment it leaves one device until it reaches the other, and only the two communicating devices can unscramble it. This provides a really high level of security, which, honestly, gives a lot of peace of mind. Checking reviews and community support for these tools can also give you a good idea of their reliability and safety.
Password and Key Management
Your passwords and cryptographic keys are like the literal keys to your digital kingdom. For your Raspberry Pi, especially when using SSH, you should always use strong, unique passwords. Even better, consider using SSH key pairs instead of passwords for login. This involves a private key on your computer and a public key on your Raspberry Pi. It's a much more secure method because even if someone guesses your password, they can't get in without your private key, which, you know, is a powerful layer of protection.
Managing these keys carefully is also very important. Keep your private keys safe and never share them. If you suspect a key might be compromised, change it right away. Similarly, if you're dealing with any kind of account access, like Jerrywoods2's problem with a PIN not working to log in, it highlights the general need for robust access control. For your Raspberry Pi, it means making sure only authorized users can connect and control it, which, basically, keeps your IoT network safe from unauthorized hands.
Monitoring Your Remote IoT Network
Once your P2P connections are up and running, it's a good idea to keep an eye on them. Monitoring your remote IoT network means looking for unusual activity or signs of trouble. This could involve checking logs on your Raspberry Pi for failed login attempts or unexpected data transfers. Tools exist that can help you do this, giving you alerts if something seems off. This is a bit like having a security camera watching your property; it helps you catch problems early.
Regular checks can help you spot if a device is behaving strangely or if there's an attempt to access your system without permission. This proactive approach helps you respond quickly to potential threats, keeping your **securely connect remote IoT P2P Raspberry Pi** setup sound. It's about being aware of what's happening on your network, which, quite frankly, is a key part of maintaining security over time. Staying informed helps you react better.
Practical Steps for Secure Remote Access
Let's get down to the actual steps you can take to make sure your Raspberry Pi is ready for secure P2P connections. Establishing a Raspberry Pi P2P connection, you see, involves a sequence of steps to ensure a seamless and secure linkage. It's not just about turning it on and hoping for the best; it's about setting things up thoughtfully from the start. This practical section will guide you through some of the most important parts.
Initial Pi Setup for Remote Access
First things first, you need to prepare your Raspberry Pi. This means installing the operating system, usually Raspberry Pi OS, and making sure it's fully updated. As we talked about earlier, an out-of-date device is a risk. So, right after you install the OS, open a terminal and run these commands:
sudo apt update(This refreshes the list of available updates)sudo apt full-upgrade -y(This installs all available updates)
Also, change the default password for the 'pi' user, or even better, create a new user and disable the 'pi' user. This is a very basic but important security measure. Many people overlook this, but it's like leaving your front door unlocked, which, frankly, is not a good idea. Initially, people must configure their Raspberry Pi devices with strong security practices, which is a good habit to form.
Configuring SSH for P2P
SSH is usually enabled by default on newer Raspberry Pi OS versions, but if not, you can enable it via the Raspberry Pi Configuration tool or by creating a file named 'ssh' in the boot partition of your SD card. Once SSH is on, the next step for a truly **securely connect remote IoT P2P Raspberry Pi** setup is to use SSH keys. Here's a simplified way to do it:
Generate an SSH key pair on your local computer (if you don't have one):
ssh-keygen -t rsa -b 4096Copy your public key to your Raspberry Pi:
ssh-copy-id pi@your_pi_ip_addressDisable password login for SSH on your Raspberry Pi by editing the
/etc/ssh/sshd_configfile. Find the linePasswordAuthentication yesand change it toPasswordAuthentication no. Then restart the SSH service:sudo systemctl restart ssh.
This setup means you can only log in with your private key, which is a much safer way to connect. It helps avoid those untrusted connection messages, too, by making the connection inherently more trustworthy. This method is a key part of how to **securely connect remote IoT devices using P2P SSH on a Raspberry Pi without spending a dime on servers**, which, you know, is pretty appealing.
Handling Firewalls and NAT Routers
To connect to your Raspberry Pi from outside your local network, you'll need to deal with your router's firewall and NAT. This can involve setting up port forwarding for SSH (port 22) to your Raspberry Pi's local IP address. However, exposing SSH directly to the internet is generally not recommended unless you have very strict security rules in place,
- Securely Connect Remote Iot Vpc Raspberry Pi Download Windows Free
- More Than A Married Couple
- How Many Children Does Pam Bondi Have
- Caitlin Clark Rookie Card
- Kendrick Lamar Mustard Song
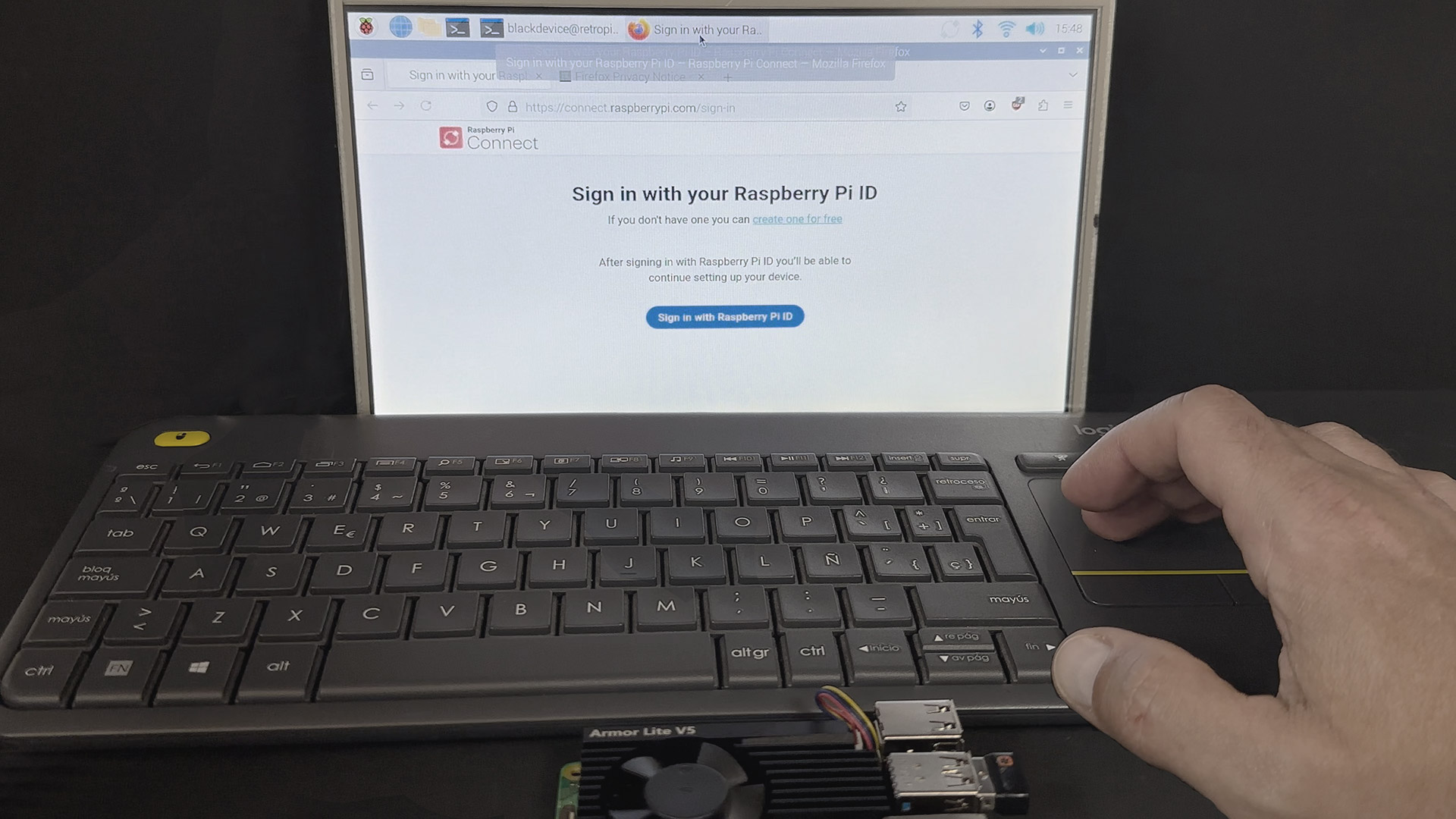
Connect to your Raspberry Pi remotely with Raspberry Pi Connect
Securely Connect IoT Devices To VPC With Raspberry Pi

Securely Connect Remote IoT P2P Raspberry Pi Download Android: A