How To SSH To IoT Device: Simple Steps For Remote Access
Getting your smart gadgets and tiny computers to listen to you from afar can feel like a real superpower, and it's actually pretty simple with the right tools. Many folks wonder how to SSH to IoT device setups without a fuss, especially when those devices are tucked away in hard-to-reach spots or are running headless, meaning they don't have a screen attached. This guide walks you through connecting securely to your internet-connected things, helping you manage them from anywhere you have an internet connection, so you know, that's pretty neat.
Think about it: your small home server, a sensor hub in the garden, or even a little robot could all benefit from remote control. Using SSH, or Secure Shell, gives you a safe way to send commands and move files back and forth, very, very useful for updates or quick fixes. It's a standard method for a good reason, as a matter of fact, offering strong protection for your connection.
This approach helps you keep an eye on your devices and make changes without physically touching them. It is, in some respects, like having a direct line to your tiny computers, giving you full command. We will go over what you need, how to set things up, and even tackle some common head-scratchers you might bump into along the way, basically making it easier for you to get started.
- What Does Ig Mean
- Blowout Taper Straight Hair
- What Happened To Jessica Tarlov
- Sophie Rain Spiderman Video
- Do Female Cats Spray
Table of Contents
- What is SSH and Why It Matters for IoT?
- Getting Your IoT Device Ready for SSH
- Setting Up Your Client Machine
- Connecting to Your IoT Device
- Security Best Practices for IoT SSH
- Troubleshooting Common SSH Problems
- Frequently Asked Questions About SSH and IoT
- Next Steps with Your IoT Device
What is SSH and Why It Matters for IoT?
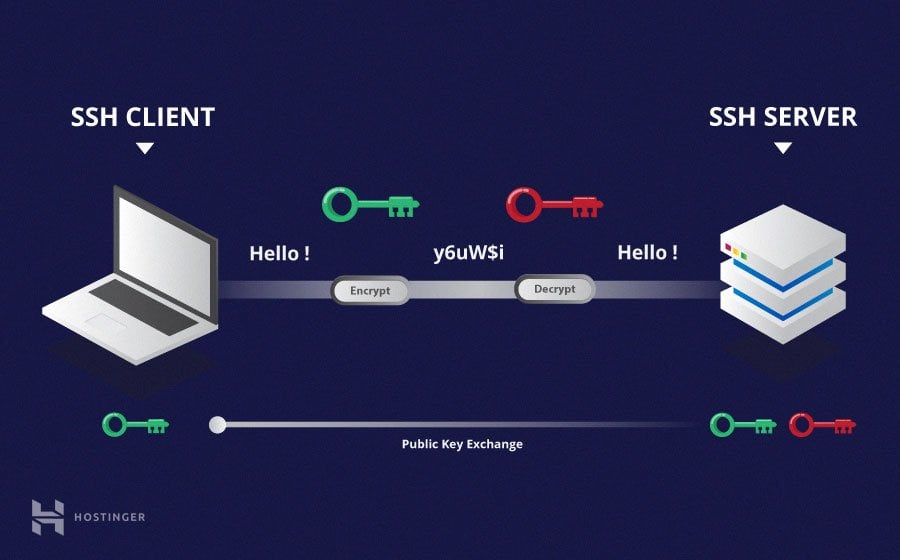
SSH, which stands for Secure Shell, is a network protocol that lets you operate network services securely over an unsecured network. It provides a strong cryptographic connection between a client and a server. For your small IoT devices, this means you can send commands, manage files, and even run programs on them from a different computer, anywhere in the world, assuming you have the right network setup, that is.
The Security Advantage
The main reason SSH is so popular for IoT devices is its focus on security. It encrypts all the traffic between your computer and the device, meaning no one can easily snoop on your commands or the data coming back. This is pretty important for devices that might be in less secure places or connected to public networks, so you know, it keeps your information safe.
Without SSH, sending commands to your device might be like shouting them across a crowded room. Anyone listening could hear what you are saying. With SSH, it is more like whispering a secret message through a private, coded tube, making it very, very hard for others to intercept your communication.
- Dress To Impress Creator Gigi
- What Does Nvm Mean
- What Is A Torta
- How Long Does It Take For Eyelashes To Grow Back
- How To Make Birria Tacos
Remote Control Made Easy
Beyond security, SSH offers amazing convenience. Imagine you have a tiny computer running your smart home lights, and you need to change a setting. Instead of unplugging it, hooking up a monitor and keyboard, and then making the change, you can just open a terminal on your laptop and SSH into it. This saves a lot of time and effort, naturally, making device management much simpler.
You can restart services, check system logs, install updates, or even write new code directly on the device, all from your desk. This remote access is absolutely vital for devices that operate without a screen or keyboard, like many IoT gadgets. It really does make a big difference in how you manage your systems, you know.
Getting Your IoT Device Ready for SSH
Before you can connect to your IoT device using SSH, you need to make sure the device itself is set up to accept incoming SSH connections. This usually involves getting the right operating system in place and then installing the SSH server software. It is a bit like preparing a special door for guests to enter your device, so to speak.
Operating System and Network Setup
Most IoT devices, especially those based on single-board computers like a Raspberry Pi, run some version of Linux. For instance, our team recently set up an Ubuntu Server 22.04.3 LTS, which is a very popular choice for these kinds of tasks. This operating system comes with many tools you need, and it is pretty stable, which is good.
You will need to get your device connected to your local network, either through Wi-Fi or an Ethernet cable. It is also a good idea to find out its IP address on the network. You can often do this by logging into your router's administration page or by using a network scanning tool. Knowing the IP address is pretty important, as you will use it to tell your computer where to connect, you see.
Installing the OpenSSH Server
Once your IoT device is running its operating system and is on the network, the next step is to install the OpenSSH server package. This software listens for incoming SSH connection requests. On an Ubuntu system, like the one our team used, this is quite straightforward.
You typically open a terminal on your IoT device (if you have a screen and keyboard attached for initial setup) and type a few commands. For Ubuntu, you would usually update your package lists first, then install the server. This is what you would generally do:
sudo apt updatesudo apt install openssh-server
After the installation finishes, the SSH server should start running automatically. You can check its status to make sure everything is working as it should, usually with a command like sudo systemctl status ssh. If it is active and running, you are in good shape, basically.
Setting Up Your Client Machine
Your client machine is the computer you will use to connect to your IoT device. This could be your laptop, desktop, or even another server. It also needs to have an SSH client installed, which is the software that initiates the secure connection.
Installing an SSH Client
Most modern operating systems come with an SSH client pre-installed. If you are using macOS or Linux, you can usually just open your terminal application and type `ssh`. Windows users on Windows 10 or newer also have an OpenSSH client built-in, which you can access through PowerShell or Command Prompt. If you are on an older Windows version, you might need to install a program like PuTTY, which is a very popular choice, by the way.
To check if you have SSH installed, just open a command prompt or terminal and type `ssh -V`. If you see a version number, you are good to go. If not, you might need to enable it in Windows features or download a client program, you know, just to get it ready.
Basic SSH Commands
The main command you will use is pretty simple. It follows this pattern: `ssh username@ip_address`. The `username` is the account you want to log into on your IoT device, and `ip_address` is the network address of your IoT device. For instance, if your device's username is `pi` and its IP address is `192.168.1.100`, you would type `ssh pi@192.168.1.100`. This command starts the process, you see.
When you connect for the first time, your client might ask you to confirm the device's authenticity. This is a security measure to make sure you are connecting to the correct device and not some imposter. Just type `yes` to continue, and the device's "fingerprint" will be saved for future connections. Then, you will be prompted for the password for the user account on your IoT device, usually.
Connecting to Your IoT Device
With both your IoT device and client machine ready, establishing the connection is the next step. It is pretty much just running that basic SSH command we talked about. Open your terminal or command prompt on your client machine, and then type the command with your device's details.
For example, if your IoT device is a Raspberry Pi with the default username `pi` and its local IP address is `192.168.1.150`, you would type: `ssh pi@192.168.1.150`. Press Enter. You will then be asked for the password associated with the `pi` user on your Raspberry Pi. Type it carefully, as you won't see the characters appear on the screen, which is normal for security. After entering the correct password, you should see a command prompt that looks like it belongs to your IoT device, meaning you are in, so to speak.
From this point, you can run commands as if you were sitting right in front of your IoT device. You can check disk space with `df -h`, list files with `ls -l`, or even update software with `sudo apt update && sudo apt upgrade`. It is a very powerful way to manage your small systems, honestly.
Security Best Practices for IoT SSH
While SSH itself is secure, there are some extra steps you can take to make your IoT device even safer from unwanted access. These are pretty important, especially since IoT devices can sometimes be targets for less friendly folks on the internet, you know.
Using SSH Keys Instead of Passwords
Relying solely on passwords for SSH access is not the strongest method. Passwords can be guessed or cracked. A much better way is to use SSH keys. This involves creating a pair of cryptographic keys: a private key that stays on your client machine and a public key that you place on your IoT device. When you try to connect, the two keys "talk" to each other to verify your identity, without ever sending your password over the network, which is really cool.
To generate SSH keys on your client machine, you typically use the command `ssh-keygen`. Then, you copy the public key to your IoT device using `ssh-copy-id username@ip_address`. After this is set up, you can usually disable password authentication on your IoT device's SSH server for an extra layer of security. This is done by editing the `/etc/ssh/sshd_config` file on your IoT device and changing `PasswordAuthentication yes` to `PasswordAuthentication no`, and then restarting the SSH service. This is a very good step to take, honestly.
Changing the Default SSH Port
By default, SSH uses port 22. Many automated bots scan the internet looking for devices listening on this port to try and break in. You can make your device less of an obvious target by changing the SSH port to something else, like 2222 or 22022. This is done by editing the `/etc/ssh/sshd_config` file on your IoT device and changing the `Port 22` line to your new port number, then restarting the SSH service. Remember to specify the new port when connecting from your client: `ssh -p new_port_number username@ip_address`. This is just a little extra protection, you see.
Keeping Software Updated
Just like any other computer, your IoT device's operating system and installed software need regular updates. These updates often include security patches that fix vulnerabilities that attackers could exploit. Regularly running `sudo apt update` and `sudo apt upgrade` on your Ubuntu-based IoT device helps keep it secure. This is a fairly simple but very effective habit to get into, you know.
Troubleshooting Common SSH Problems
Sometimes, things do not go exactly as planned, and you might run into issues when trying to connect. Our team has faced a few of these, and knowing what to look for can save you a lot of frustration. Here are some common problems and how to approach them.
ssh_config Versus sshd_config Confusion
One common mix-up involves the two main SSH configuration files: `/etc/ssh/ssh_config` and `/etc/ssh/sshd_config`. The `ssh_config` file is for the SSH *client*, meaning your computer trying to connect out. The `sshd_config` file is for the SSH *server*, which is your IoT device listening for incoming connections. Our team actually found that they had options listed in their `ssh_config` that really belonged in `sshd_config`, which caused some trouble.
If you are having connection problems, especially with forwarding or authentication, double-check which file you are editing. If you are changing server settings, like the port or allowing key-based authentication, make sure you are editing `/etc/ssh/sshd_config` on your IoT device. If you are setting up client-side aliases or specific connection options for your own machine, then `/etc/ssh/ssh_config` (or `~/.ssh/config` for user-specific settings) is the place. It is a subtle difference, but it is pretty important, honestly.
Error: Invalid Host for SSH Forwarding
This error, "Error invalid host for ssh forwarding," typically pops up when you are trying to set up SSH port forwarding or X11 forwarding, and the host you are trying to forward to or through is not recognized or allowed. This often points to an issue with the SSH server's configuration on your IoT device, specifically in the `sshd_config` file. Sometimes, there are restrictions on what hosts can be used for forwarding, or the syntax in your command is a bit off.
To fix this, first check the forwarding options in your `sshd_config` on the IoT device. Look for directives like `AllowTcpForwarding` or `X11Forwarding`. Make sure they are set to `yes` if you intend to use them. Also, verify the hostname or IP address you are using in your forwarding command is correct and reachable from your IoT device. It could also be a DNS issue on the IoT device side, so you know, check that too.
Could Not Resolve Hostname
The error "Could not resolve hostname node01" means your client computer cannot figure out the IP address that goes with the name "node01". When you use a hostname instead of an IP address (like `ssh user@node01`), your computer needs a way to translate that name into numbers. This is usually done through DNS (Domain Name System) or by looking at your local hosts file.
Here are a few things to check:
Is the hostname correct? Make sure you spelled "node01" exactly as it is configured on your IoT device or in your network's DNS.
DNS issues: If your network uses a local DNS server, make sure it knows about "node01". Sometimes, small devices do not register their hostnames automatically. You might need to add a static entry in your router's DNS settings.
Local hosts file: You can manually add an entry to your client computer's hosts file. On Linux/macOS, this is `/etc/hosts`. On Windows, it is typically `C:\Windows\System32\drivers\etc\hosts`. Add a line like: `192.168.1.150 node01` (replace the IP with your device's actual IP). This tells your computer to directly associate "node01" with that IP address, which is very helpful sometimes.
Network connectivity: Make sure your client computer can actually reach the IoT device on the network. A simple `ping 192.168.1.150` (using the device's IP) can tell you if there is basic network communication, you know, just to be sure.
Frequently Asked Questions About SSH and IoT
Here are some common questions people have when setting up SSH for their IoT devices.
Q: Is SSH safe enough for my home IoT devices?
A: Yes, SSH is very secure when set up properly. Using strong passwords or, even better, SSH keys, and keeping your software updated, makes it a very safe way to access your devices remotely. It encrypts all the data, which is a big plus, honestly.
Q: Can I SSH to my IoT device from outside my home network?
A: Yes, you can, but it requires extra steps and care. You would typically need to set up port forwarding on your home router to direct incoming SSH requests from the internet to your specific IoT device. This opens a port on your router to the internet, so you must be extra careful with security, like using SSH keys and changing the default port. Some people prefer using a VPN or a service like Tailscale for more secure remote access, as a matter of fact.
Q: What if I forget my IoT device's password or lose my SSH key?
A: If you forget the password or lose the private SSH key, you might need to connect a keyboard and monitor directly to your IoT device to log in locally and reset the password or add a new SSH key. In some cases, if you cannot log in locally, you might have to re-flash the operating system onto the device's storage, which means starting over. So, keeping your passwords and keys safe is very, very important, you know.
Next Steps with Your IoT Device
Getting SSH working is a big step towards truly controlling your IoT devices. With a secure connection, you can now explore all sorts of possibilities. Consider automating tasks on your device, perhaps setting up a small web server, or connecting it to cloud services. You might also want to explore more about network security for your home setup to keep everything safe.
Keep practicing with your SSH commands and try different configurations. There is always more to learn about making your devices work for you. For more detailed guides on server configurations and managing services, you can always check out more pages on our site, perhaps like this one about Linux commands. Happy connecting, and remember to keep those devices updated for the best experience!
- Sophiexyz Spiderman
- Filmy Fly Com
- 405 Howard Street San Francisco
- How Tall Is The Rock
- Surrealism Dress To Impress
SSH Tutorial: What is SSH, Encryptions and Ports

What Is SSH? | How to Use SSH (Secure Shell) | Gcore

Windows SSH Server | Learning, Secure shell, Software engineer