Securely Connect Remote IoT: Raspberry Pi To AWS VPC Explained
Connecting your tiny devices, like a Raspberry Pi, to the vast cloud, particularly Amazon Web Services (AWS), feels like a big step for many, and it's a rewarding journey, truly. You might have felt that familiar pang of worry, like when your computer warns, "Your device is at risk because it's out of date and missing important security and quality updates," or maybe you've seen those unsettling messages, "This connection is untrusted," when trying to reach a website. That feeling of uncertainty, that something isn't quite right with a connection, is a real concern for anyone looking to build something with remote gadgets.
As the internet of things (IoT) continues to expand, getting remote devices safely linked up to an AWS Virtual Private Cloud (VPC) using a Raspberry Pi has, you know, become a pretty important part of many projects. People often wonder how to make sure their small, far-off devices can talk to powerful cloud services without opening up a bunch of risks. It's a common worry, and frankly, it's a valid one.
This article will walk you through how to securely connect remote IoT devices, specifically a Raspberry Pi, to your AWS VPC. We'll look at the best ways to set things up, making sure your information stays private and your system stays protected. It's all about getting you back on track so your IoT setup can run more securely, and you can trust that your connections are sound, which is really what everyone wants, isn't it?
- Shut Up In Spanish
- Twin Where Have You Been
- Lagu Waiting For You
- Kendrick Lamar Mustard Song
- Grab The Mic Game
Table of Contents
- The Need for Secure IoT Connections
- What is AWS VPC and Why It Matters for IoT
- Getting Your Raspberry Pi Ready
- Setting Up Your AWS VPC for IoT
- Methods for Secure Connection
- Implementing Security Best Practices
- Common Challenges and Solutions
- Frequently Asked Questions
- Moving Forward with Your Secure IoT Project
The Need for Secure IoT Connections
In today's interconnected world, securely connecting remote IoT devices through AWS VPC and Raspberry Pi has become a critical need for businesses and tech enthusiasts alike. Think about it: every device you add to your network is, in a way, another door. If those doors aren't locked tight, you could have problems. This is particularly true for small, remote gadgets like a Raspberry Pi, which might be sitting somewhere far away, gathering important information. If that connection is untrusted, or if the device itself is out of date, you're looking at a pretty big risk.
The risks aren't just theoretical, either. You know, like when Jerrywoods2 mentioned having trouble with "this connection is untrusted" across multiple platforms, from MS Edge to Firefox and Chrome. That kind of widespread connection problem can stop a project dead in its tracks. A lack of security updates or a poor setup can mean your data is exposed, your device gets taken over, or your whole system could be messed with. So, making sure everything is buttoned up from the start is, well, just smart.
Getting your Raspberry Pi securely connected to AWS within a VPC is, you know, a very smart move for any IoT project. It's about building a solid foundation, a place where your devices can communicate without fear of eavesdropping or tampering. This foundational step is really important for making sure everything runs smoothly and safely.
- Is A Fish An Animal
- In The Clerb We All Fam
- How To Remove Acrylic Nails
- 405 Howard Street San Francisco
- Yes Yes Yes Meme
What is AWS VPC and Why It Matters for IoT
An AWS Virtual Private Cloud (VPC) is essentially your own private network within the AWS cloud, providing an isolated and highly controllable environment for your resources. Think of it like having your own dedicated office building in a huge city. You get to decide who comes in, where they go, and what they can do. This isolation is incredibly valuable for IoT projects, especially when you're talking about securely connecting remote IoT devices.
For your Raspberry Pi, or any remote IoT gadget, a VPC means you're not just throwing your device onto the open internet and hoping for the best. Instead, you're giving it a secure, private pathway directly into your cloud resources. This means your data doesn't have to travel across public networks any more than it absolutely has to, reducing opportunities for someone to snoop or mess with things. It's a bit like having a private tunnel for your sensitive information, which is pretty cool, actually.
The control you get with a VPC is also a big deal. You can set up specific rules about what traffic goes in and out, which services your Raspberry Pi can talk to, and what kind of information it can share. This level of fine-tuned access helps you build a system where only authorized communication happens, making it much harder for unwanted access. So, for securely connecting remote IoT VPC AWS Raspberry Pi setups, a VPC is, arguably, a cornerstone of your security plan.
Getting Your Raspberry Pi Ready
Before you can securely connect remote IoT VPC AWS Raspberry Pi, your Raspberry Pi needs to be properly set up and configured. This foundational step is crucial for ensuring a smooth and secure connection. It's like preparing a tool before you use it for a big job; you want to make sure it's in top shape and ready for what's ahead.
Initial Setup and Updates
First things first, get your Raspberry Pi operating system up to date. You know, sometimes you get those messages saying, "Your device is at risk because it's out of date and missing important security and quality updates." That's exactly what we want to avoid here. Running `sudo apt update` and `sudo apt upgrade` regularly is just basic practice, but it's super important. These commands pull down the latest security patches and bug fixes, which helps keep your device from having known weaknesses.
It's also a good idea to change the default password right away. The standard "pi" username with the "raspberry" password is, well, pretty well-known. If you leave that as is, it's like leaving your front door unlocked. A strong, unique password for your Raspberry Pi is a really easy win for security, and it's something you should do the moment you get things running.
Basic Pi Security Measures
Beyond updates, there are a few other simple things you can do to harden your Raspberry Pi. For instance, you should disable SSH password authentication and switch to key-based authentication. This means only devices with the correct cryptographic key can connect, which is much safer than relying on a password that could, you know, theoretically be guessed.
Another thing to consider is removing any unnecessary software. If your Raspberry Pi is just doing one job, like collecting sensor data, it doesn't need a web browser or a bunch of other applications. Less software means fewer potential weak spots for someone to exploit. It's about keeping things lean and mean, which often makes them more secure, too it's almost a rule of thumb.
Setting Up Your AWS VPC for IoT
Once your Raspberry Pi is prepped, the next big step is setting up your AWS VPC. This is where you create that private, secure space in the cloud for your IoT project. It's a bit like building a custom, secure garage for your remote devices to park their data.
Creating Your Private Network
Start by creating a new VPC in the AWS console. You'll define its IP address range, which is like picking a street address for your private network. Inside this VPC, you'll then create subnets. You might want a public subnet for things that need to talk to the internet (like a NAT Gateway for your Pi to send data out) and private subnets for your more sensitive resources, like databases or application servers. The Raspberry Pi will typically connect into a private subnet, so its direct exposure to the public internet is very limited, which is really what we're aiming for.
For communication between your Raspberry Pi and your VPC, you'll often set up a Virtual Private Gateway (VGW) or a Transit Gateway. These are the entry points for your remote connections. A VGW, for example, is what you'd use to create a VPN connection back to your Raspberry Pi, making it feel like your Pi is right there on your private network, even if it's miles away. This setup is pretty standard for securely connecting remote IoT VPC AWS Raspberry Pi setups.
Network Access Control Lists and Security Groups
This is where you put up your digital fences and guards. Network Access Control Lists (NACLs) act like firewalls for your subnets, controlling traffic at a broader level. They're stateless, meaning they don't remember previous connections, so you have to allow both inbound and outbound traffic explicitly. You might, for instance, only allow very specific types of traffic into your private subnets from your VPN connection.
Security Groups, on the other hand, act as firewalls for individual instances or devices within your subnets. These are stateful, so if you allow outbound traffic, the return inbound traffic is automatically permitted. For your Raspberry Pi connection, you'd create a security group that only allows necessary ports open, like SSH for management (from specific IPs only!) or the port for your IoT data transfer. This layered approach to security is quite effective, giving you fine-grained control over who and what can communicate with your devices.
Methods for Secure Connection
Now that your Raspberry Pi is ready and your AWS VPC is set up, it's time to talk about the actual ways your little device can securely talk to your big cloud network. There are a few main paths you can take, each with its own benefits, and it's worth looking at them closely.
VPN Connection (Site-to-Site)
One of the most common and secure ways to connect a remote device like a Raspberry Pi to an AWS VPC is through a VPN (Virtual Private Network) connection. This creates an encrypted tunnel between your Raspberry Pi (or the network it's on) and your AWS VPC. It's like building a private, secure bridge over public roads. This means all the data flowing between your Pi and AWS is scrambled, so even if someone intercepts it, they can't make sense of it.
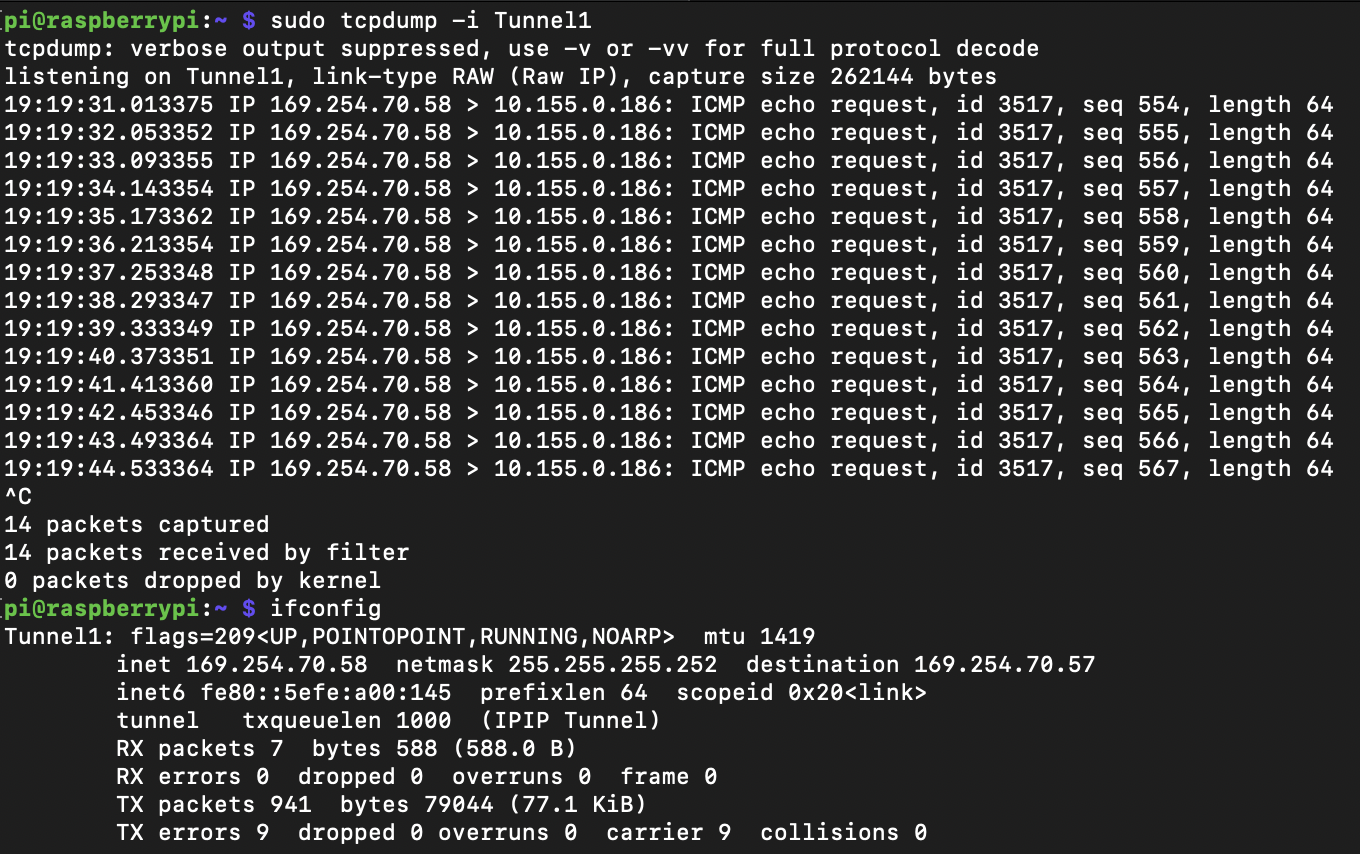
For a Raspberry Pi, you would typically set up a VPN client, such as OpenVPN or WireGuard, on the Pi itself. On the AWS side, you'd configure a Customer Gateway (representing your Pi's public IP or the network it's behind) and then create a Site-to-Site VPN connection to your Virtual Private Gateway in the VPC. This method makes your Raspberry Pi effectively part of your VPC's private network, which is a very high level of security for securely connecting remote IoT VPC AWS Raspberry Pi devices.
AWS IoT Core and Device Shadows
While the primary focus here is VPC connectivity, it's worth mentioning AWS IoT Core as it often works hand-in-hand with VPCs for IoT solutions. AWS IoT Core provides a managed service that allows billions of IoT devices to connect to AWS services easily and securely. It handles device authentication, authorization, and message routing. Your Raspberry Pi would connect to IoT Core using MQTT, a lightweight messaging protocol, often over TLS for encryption.
IoT Core also offers Device Shadows, which are persistent, virtual versions of your devices in the cloud. This means you can interact with your Raspberry Pi's state even if the device itself is offline. While IoT Core itself doesn't directly put your Pi *inside* your VPC in the same way a VPN does, it can securely bridge your device's data into your VPC through VPC endpoints or by triggering Lambda functions that then interact with resources in your VPC. This combination is, you know, a very popular approach for scalable IoT systems.
SSH Tunneling (with Caution)
SSH tunneling is a way to create a secure, encrypted tunnel between your local machine (or another server) and your Raspberry Pi. While it's great for remote management and troubleshooting, it's generally not recommended as the primary method for securely connecting remote IoT VPC AWS Raspberry Pi data streams for long-term, production IoT applications. It's more of a point-to-point connection for administrative tasks.
If you do use SSH, you absolutely must use key-based authentication and disable password logins, as mentioned earlier. Furthermore, limit SSH access to only specific, trusted IP addresses. Leaving SSH open to the world is like leaving a door wide open, which is definitely not what we want when we're talking about secure connections. So, use it wisely, and sparingly, if at all, for your main IoT data flow.
Implementing Security Best Practices
Setting up the connections is just one part of the puzzle. To truly securely connect remote IoT VPC AWS Raspberry Pi, you need to follow some best practices that cover identity, data, and ongoing vigilance. It's like having good locks on your doors, but also knowing who has the keys, encrypting your valuables, and having a security camera.
Identity and Access Management (IAM)
AWS Identity and Access Management (IAM) is incredibly important. Instead of using root AWS account credentials (which is a big no-no), you should create specific IAM users and roles with the minimum permissions needed for your IoT project. For instance, your Raspberry Pi, when interacting with AWS IoT Core or other services, should use credentials that only allow it to do what it absolutely needs to do, and nothing more. This concept is called the "principle of least privilege."
This means if your Pi only needs to publish messages to a specific MQTT topic, its IAM role should only have permission for that specific action. It shouldn't be able to delete resources or access other parts of your AWS account. This significantly limits the damage if, by some chance, your device's credentials were to be compromised. It's a fundamental part of keeping things safe, and it's a practice you should always follow.
Data Encryption
Data should be encrypted both in transit and at rest. When your Raspberry Pi sends data to AWS, make sure the connection uses TLS/SSL encryption, which is standard for MQTT connections to AWS IoT Core and for VPN tunnels. This ensures that the data is unreadable if intercepted while it's moving across networks. You know, like when you get that "This connection is untrusted" message because the encryption isn't working right. We want to avoid that.
For data stored in AWS services, like S3 buckets or databases, make sure encryption at rest is enabled. AWS offers various encryption options, including server-side encryption with AWS Key Management Service (KMS). Encrypting data at rest means that even if someone gains unauthorized access to your storage, the data itself is still protected and unreadable without the proper decryption keys. It's a pretty good layer of defense, actually.
Monitoring and Logging
You can't protect what you don't see. Setting up robust monitoring and logging for your Raspberry Pi and your AWS VPC resources is absolutely essential. Use AWS CloudWatch to monitor your VPC flow logs, which show all the traffic going in and out of your network interfaces. This can help you spot unusual activity, like unauthorized connection attempts or unexpected data transfers.
For your Raspberry Pi, make sure its system logs are being collected and, if possible, sent to a centralized logging service like AWS CloudWatch Logs. This allows you to keep an eye on what your device is doing, detect potential intrusions, or troubleshoot problems. Regularly reviewing these logs can help you catch issues before they become major security incidents. It's a bit like having a watchful eye on everything, which is, you know, a very important part of security.
Common Challenges and Solutions
Even with the best plans, setting up securely connected remote IoT VPC AWS Raspberry Pi systems can hit a few bumps. It's like any project; you'll run into things that make you scratch your head. But usually, there's a way around them.
One common challenge is dealing with dynamic IP addresses on the Raspberry Pi's side. If your Pi is at a remote location and its public IP address changes frequently, setting up a static VPN connection can be tricky. A solution for this is to use a dynamic DNS service, which updates a hostname to point to your Pi's current IP. Alternatively, using AWS IoT Core, which doesn't rely on a static public IP for device connectivity, can bypass this issue entirely.
Another issue can be firewall rules at the remote site where the Raspberry Pi is located. Sometimes, local network firewalls block outgoing VPN traffic or specific ports needed for communication. You might need to work with the network administrator at that location to open the necessary ports or allow the VPN traffic. It's a bit of a coordination effort, but it's often necessary to get things working.
Sometimes, people also struggle with credential management for their Raspberry Pi. Hardcoding API keys or secrets directly onto the device is a bad idea. A better approach involves using secure credential storage, like AWS Secrets Manager, and retrieving credentials at runtime, or employing certificate-based authentication with AWS IoT Core. This way, if the Pi is compromised, the actual secrets aren't directly exposed.
Frequently Asked Questions
How do I keep my Raspberry Pi safe for IoT projects?
To keep your Raspberry Pi safe, you should regularly update its operating system and software, change default passwords immediately, and use strong, unique ones. Also, switch to key-based authentication for SSH access, remove any software you don't need, and set up a firewall on the Pi itself to limit incoming connections. These steps help protect it from common threats, which is pretty important, actually.
What's the big deal about AWS VPC for my IoT stuff?
AWS VPC is a big deal because it lets you create your own private, isolated network inside the AWS cloud. This means your Raspberry Pi and other IoT devices can communicate with your cloud resources over a secure, private pathway, rather than the open internet. It gives you a lot of control over who can access your network and what kind of traffic goes in and out, making your IoT system much more secure. It's like having your own dedicated, secure space, which is very helpful.
Can I really trust my Raspberry Pi connection to the cloud?
You absolutely can build a trustworthy connection for your Raspberry Pi to the cloud, but it takes careful planning and setup. By using methods like VPNs to create encrypted tunnels, implementing strong authentication (like certificates or IAM roles), encrypting all data, and consistently monitoring your connections, you can establish a very high level of trust. It's about taking proactive steps to ensure your connection is secure, so you don't get those "This connection is untrusted" messages.
Moving Forward with Your Secure IoT Project
Getting your Raspberry Pi securely connected to AWS within a VPC is, you know, a very smart move for any IoT project. It's about creating a solid foundation for your remote devices to operate safely and effectively. The journey from an unsecured, outdated device to a fully protected, cloud-connected system involves careful steps, but each one adds a layer of peace of mind.
Remember, security is not a one-time setup; it's an ongoing process. You need to keep your devices updated, monitor your connections, and adapt to new threats as they appear. Just like you wouldn't want your Windows machine to be out of date and missing important security updates, your IoT devices need that same attention.
So, if you're ready to build a robust and secure connection between your Raspberry Pi, located in a remote IoT environment, and your AWS server residing within a virtual private cloud, take these steps seriously. It's a rewarding challenge that pays off in system stability and data protection. To learn more about IoT security best practices, you might want to check out some official resources. You can also learn more about secure connections on our site, and find more information about Raspberry Pi projects here.
- Lagu Waiting For You
- Help I Accidentally Forgot How Gravity Works
- How Long Is A Fortnight
- Remoteiot Monitoring Ssh Download Android
- Boo Did I Scare You Im A Job Application

Securely Connect Remote IoT VPC Raspberry Pi AWS: A Comprehensive Guide
Securely Connect Remote IoT VPC Raspberry Pi AWS Free: A Comprehensive

Securely Connect Your IoT Devices Using Raspberry Pi And AWS VPC