Securely Connect Your Remote IoT Raspberry Pi To AWS VPC: A Practical Example
Have you ever felt that sinking feeling when a message pops up saying, "Your device is at risk because it's out of date and missing important security and quality updates?" It's a real worry, especially when you're working with remote gadgets like a Raspberry Pi. That sense of an "untrusted connection" or a "problem connecting securely" can be quite frustrating, and it's a signal that your system needs some serious attention.
We all want our tech to just work, right? But when it comes to connecting devices over the internet, like a little Raspberry Pi out in the field talking to your cloud setup on AWS, security can feel like a big puzzle. You might have tried different browsers, as one person mentioned, or maybe even struggled with basic login issues like a "Pin not working to login to my account." These little hiccups often point to bigger security gaps that need closing, and honestly, they can be a bit of a headache.
Getting your remote IoT devices, say a Raspberry Pi, to talk safely with your AWS Virtual Private Cloud (VPC) is a really important step for any project. It's not just about making the connection work; it's about making sure that connection is trusted and protected from prying eyes. This article will show you a way to do just that, giving you peace of mind about your remote operations, so you can focus on what your devices are meant to do.
- What Does Asl Mean
- How To See Deleted Sms
- Chris Jones 40 Yard Dash
- Mid Taper Textured Fringe
- How To Say I Love You In French
Table of Contents
- The Growing Need for Secure IoT Connections
- Why Your Raspberry Pi Needs a Secure AWS VPC Link
- Understanding the Risks
- The AWS VPC Advantage
- Setting Up Your AWS Environment for Secure IoT
- Creating a Dedicated VPC
- Configuring Subnets and Security Groups
- Setting Up AWS IoT Core
- Preparing Your Raspberry Pi for Secure Connection
- Updating and Hardening Your Pi
- Installing Necessary Software
- Establishing the Secure Connection: A Step-by-Step Guide
- Generating Certificates and Keys
- Configuring AWS IoT Policies
- Connecting Your Pi to AWS IoT Core
- Using a VPN for Added Security (Optional but Recommended)
- Maintaining Security for Your Remote IoT Devices
- Common Connection Issues and How to Solve Them
- Frequently Asked Questions
The Growing Need for Secure IoT Connections
More and more gadgets are getting connected to the internet these days, aren't they? From smart home devices to industrial sensors, these "things" are constantly sending and receiving information. This widespread connection, while incredibly useful, also opens up new avenues for potential trouble. It's like having many doors into your digital home, and if those doors aren't locked tight, well, you could have problems, you know?
When your device is out there, maybe gathering sensitive data or controlling important systems, its safety becomes a top concern. A message like, "Your device is at risk because it's out of date," is a serious warning. It means there might be holes in its defenses that bad actors could use. That's why making sure these connections are really secure isn't just a good idea; it's pretty much a must-do.
Think about the information your IoT devices might handle. Could it be personal details, operational secrets, or even controls for physical equipment? If someone gets in through an "untrusted connection," that information could be stolen, or worse, your devices could be taken over. This kind of risk is why folks are paying much more attention to how they shield their IoT setups, especially when they're spread out remotely.
- More Than A Married Couple
- Wasmo Somali Chanel
- How Do I Say Goodbye Lyrics
- Lagu Waiting For You
- Brandi Passante Pics
Why Your Raspberry Pi Needs a Secure AWS VPC Link
A Raspberry Pi is a fantastic little computer, quite versatile, actually. People use them for all sorts of projects, from home automation to industrial monitoring. But because they are often out in the open, connected to the internet, they become a target. Just like your home computer, if it's "out of date and missing important security and quality updates," it's more exposed to dangers, so this is a concern.
Understanding the Risks
Imagine your Raspberry Pi sending data back to your main system, perhaps to AWS. If that connection isn't properly protected, that information could be intercepted. It's a bit like sending a postcard through the mail; anyone could read it. An "untrusted connection" means your Pi can't be sure it's talking to the right place, or that its messages are private. This could lead to information leaks or even someone pretending to be your Pi, which is pretty scary, right?
Beyond just data, an unsecured Pi could be taken over. Someone might use it to launch attacks on other systems, or simply mess with your project. This is where the idea of a "device at risk" really hits home. You've worked hard on your IoT setup, and you definitely don't want it compromised because of a simple oversight in security. It's something to think about, certainly.
The AWS VPC Advantage
AWS Virtual Private Cloud, or VPC, offers a way to build your own private, isolated section of the AWS cloud. Think of it as having your own dedicated, fenced-off area where you can keep your servers and services. No one else can just wander in. This isolation is a huge step in making your connections more secure, you know?
By placing your cloud resources within a VPC, you get fine-tuned control over who and what can communicate with them. You can set up specific rules, almost like bouncers at a club, deciding exactly which traffic gets in and out. This helps prevent those "untrusted connection" warnings and makes sure only your approved devices, like your Raspberry Pi, can get through. It's a very helpful feature for keeping things tidy and safe.
Using a VPC gives you a strong foundation for your IoT setup. It helps you manage your network traffic with a lot more precision, which is quite important when you're dealing with many different devices. This kind of setup means your Raspberry Pi has a safe place to send its data, reducing the chances of any "problem connecting securely" issues due to outside interference. It's a good way to build trust in your system.
Setting Up Your AWS Environment for Secure IoT
Before your Raspberry Pi can chat securely with AWS, you need to prepare the AWS side of things. This involves setting up a few key components that work together to create a protected space for your IoT operations. It's a bit like building the walls and doors of your secure digital home, and it's something you'll want to get right from the start, you know?
Creating a Dedicated VPC
First off, you'll want to create a brand-new VPC. This isn't just for show; it's your own private network within AWS. You get to choose its size and where it sits in terms of IP addresses. This separation means your IoT traffic doesn't mix with other things you might have running in AWS, adding a layer of protection right away. It's a foundational step, and pretty important, honestly.
When you make your VPC, you're essentially carving out a piece of the cloud just for your needs. This helps avoid conflicts and keeps things organized. It's also where you'll define the ranges of IP addresses your devices and services will use, giving you a lot of control over your network layout. This kind of dedicated space is, in a way, the first line of defense for your remote IoT gadgets.
Configuring Subnets and Security Groups
Inside your VPC, you'll divide it into smaller sections called subnets. You might have one subnet for public-facing services and another for private ones, like where your IoT data will land. This segmentation helps you control traffic flow even more. It's a bit like having different rooms in your house, each with a specific purpose, and you know, that helps keep things neat.
Then come security groups. These are like virtual firewalls that control what kind of network traffic can go in and out of your AWS resources. For your IoT setup, you'll create rules that only allow necessary communication, blocking everything else. This helps prevent those "untrusted connection" attempts by making sure only authorized messages get through. It's a pretty powerful tool for keeping things safe, actually.
Setting Up AWS IoT Core
AWS IoT Core is the central hub for your connected devices. It's the service that lets your Raspberry Pi securely connect, send its data, and receive commands. You'll register your Pi as a "thing" within IoT Core, giving it a unique identity. This is where the magic of secure communication truly begins, and it's quite an important part of the whole setup.
IoT Core also handles device authentication and authorization. It makes sure that only devices you've approved can connect and that they can only do what you've told them they can do. This helps prevent any "problem connecting securely" issues that come from unauthorized access. It's a very robust system for managing a fleet of remote gadgets, and it really helps with peace of mind.
You'll define "rules" in IoT Core that tell it what to do with the information your Pi sends. For example, you might set a rule to store data in a database or trigger an alert. This means your data is handled securely from the moment it leaves your Pi until it reaches its destination within your AWS VPC, giving you a good level of control over your information flow.
Preparing Your Raspberry Pi for Secure Connection
Your Raspberry Pi needs a little tender loving care before it can join the secure club. Just like any computer, it needs to be up-to-date and have the right tools installed. This step is pretty crucial, honestly, for making sure your connection is as strong and reliable as possible. It's about setting the stage for good communication.
Updating and Hardening Your Pi
Remember that message, "Your device is at risk because it's out of date?" That applies directly to your Raspberry Pi. The very first thing you should do is update its operating system and software. This fixes known security weaknesses and improves overall performance. It's a simple step, but it makes a huge difference in protecting your device from common threats, so it's worth doing right away.
Beyond just updating, "hardening" your Pi means making it tougher to break into. This includes changing default passwords, setting up SSH keys instead of passwords for remote access, and putting a firewall in place. A firewall acts like a gatekeeper, only letting approved network traffic in and out. These steps reduce the chances of an "untrusted connection" or unauthorized access to your Pi, which is pretty vital for remote operation.
Installing Necessary Software
To talk with AWS IoT Core, your Raspberry Pi will need some specific software. Typically, this involves installing the AWS IoT Device SDK, which provides the libraries and tools for your Pi to communicate using secure protocols. You might also need a programming language like Python, as many IoT projects use it for their device logic. This software acts as the translator between your Pi and the cloud, you know?
Getting the right software in place is a bit like making sure your Pi has the correct language skills to talk to AWS. Without it, the communication just wouldn't happen, or it wouldn't happen securely. This setup ensures that when your Pi tries to connect, it's using the proper methods and protocols, helping to avoid any "problem connecting securely" messages that come from mismatched systems. It's a key part of the puzzle.
Establishing the Secure Connection: A Step-by-Step Guide
Now for the main event: getting your Raspberry Pi and AWS to talk to each other in a truly secure way. This involves a few careful steps, but once you have it set up, you'll have a robust connection for your remote IoT project. It's a bit like building a bridge, making sure every part is strong and reliable, and that's pretty important, honestly.
Generating Certificates and Keys
For a secure connection, your Raspberry Pi needs a digital identity, like a passport. This comes in the form of security certificates and private keys. You'll generate these through AWS IoT Core. These files prove that your Pi is who it says it is and that its messages haven't been tampered with. It's a fundamental part of establishing trust, you know, between your device and the cloud.
These certificates and keys are unique to your device. When your Pi tries to connect, it presents its certificate, and AWS verifies it. If everything matches up, the connection is allowed. This process helps prevent "untrusted connection" warnings because both sides are sure of each other's identity. Keeping these keys safe on your Pi is extremely important, as they are the very foundation of its secure link.
Configuring AWS IoT Policies
Even with a certificate, your Pi needs permission to do things within AWS IoT Core. This is where IoT policies come in. A policy is a set of rules that define what actions your device is allowed to perform, such as publishing data to a specific topic or subscribing to receive commands. You'll attach this policy to your device's certificate, which is pretty neat.
By creating a policy, you're giving your Pi just enough access to do its job, and no more. This concept is called "least privilege," and it's a very important security practice. If your Pi only has permission to send data to one specific place, it can't accidentally (or maliciously) mess with other parts of your AWS setup. This helps prevent "problem connecting securely" issues that arise from over-permissioned devices.
Connecting Your Pi to AWS IoT Core
With the certificates, keys, and policies in place, your Raspberry Pi is ready to make the connection. You'll use the AWS IoT Device SDK that you installed earlier. The SDK helps your Pi establish a secure communication channel, typically using MQTT over TLS, which is a very common and secure way for IoT devices to talk. It's like having a special, encrypted phone line, you know?
Your Pi's code will load its certificate and private key, specify the AWS IoT endpoint, and then try to connect. If everything is set up correctly, the connection will be established, and your Pi can start sending its information or listening for commands. This is the moment your remote IoT setup truly comes alive, securely communicating with your cloud resources. It's quite a feeling when it all works out.
Using a VPN for Added Security (Optional but Recommended)
While AWS IoT Core provides strong security for device communication, adding a Virtual Private Network (VPN) can give you an extra layer of protection, especially for management access or if your Pi needs to reach other resources within your VPC directly. A VPN creates an encrypted tunnel over the public internet, making it incredibly difficult for anyone to snoop on your traffic. It's like building a secret passage, which is pretty cool.
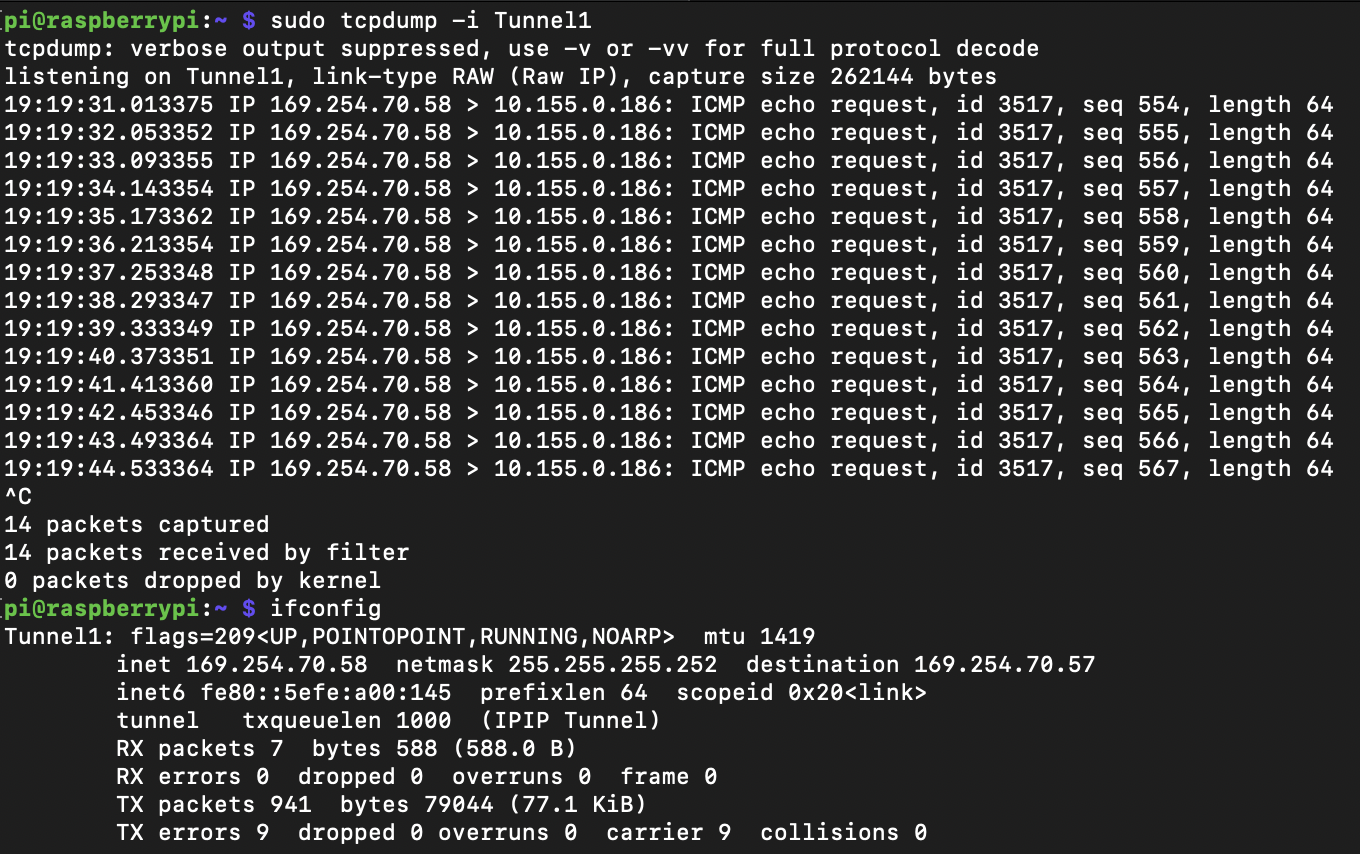
You could set up a VPN server within your AWS VPC and configure your Raspberry Pi to connect to it. This means all traffic between your Pi and your VPC travels through that secure tunnel. This is particularly useful if you need to SSH into your Pi remotely for maintenance or updates, or if your Pi needs to access databases or other services that aren't directly exposed to IoT Core. It really helps to secure your remote interactions, so it's a good idea to consider.
Tools like OpenVPN or WireGuard are popular choices for setting up a VPN on a Raspberry Pi. This approach helps to prevent those "untrusted connection" warnings by ensuring that the entire path your data takes is encrypted and authenticated. It adds a robust layer of defense against various network threats, giving you even more confidence in your remote IoT setup. It's a bit of extra effort, but often worth it for the peace of mind.
Maintaining Security for Your Remote IoT Devices
Getting your secure connection set up is a big win, but keeping it secure is an ongoing task. Security isn't a one-time thing; it's a continuous process, you know? Just like your home computer needs regular updates, your remote Raspberry Pi and its AWS connection need constant attention to stay safe from new threats. It's a bit like tending a garden, always looking for weeds.
Regularly updating your Raspberry Pi's operating system and any installed software is super important. New security patches come out all the time, and applying them helps close any newly discovered vulnerabilities. If you ignore these updates, you might find your "device is at risk" again. It's a simple habit that makes a world of difference in preventing future problems, and it's something to remember.
Monitoring your AWS IoT Core logs and your VPC network traffic can also give you early warnings of potential issues. If you see unusual connection attempts or strange data patterns, it could mean someone is trying to get in. Being proactive about watching these things can help you catch problems before they become serious, avoiding those "untrusted connection" scenarios. It's about staying vigilant, basically.
Consider rotating your security certificates and keys periodically. While they are designed to be long-lasting, changing them every so often adds another layer of security. It's like changing the locks on your doors, even if they haven't been picked. This practice, along with reviewing your AWS IoT policies to ensure they still follow the "least privilege" principle, helps keep your remote IoT setup strong and resilient against changing threats. It's a good habit to get into, really.
Common Connection Issues and How to Solve Them
Even with the best planning, sometimes things don't go perfectly. You might run into a "problem connecting securely to this website" type of message, or your Pi just won't seem to talk to AWS. Don't worry, these issues are often solvable with a bit of troubleshooting. It's like trying to fix a leaky faucet; you just need to find the source of the drip, you know?
One common issue is incorrect certificates or keys. If the files on your Raspberry Pi don't exactly match what AWS IoT Core expects, the connection will fail. Double-check that you've downloaded the correct files and placed them in the right spot on your Pi. Also, make sure their permissions are set correctly so your application can read them. This is often the first thing to check if you're getting an "untrusted connection" message.
Network configuration in your AWS VPC can also cause problems. Are your security group rules allowing the necessary traffic from your Pi to reach IoT Core? Is your network ACL set up correctly? Sometimes, a simple blocked port can prevent the whole system from working. It's worth reviewing your VPC setup carefully to make sure there are no unintended barriers, and that's pretty important.
Another thing to look at is your AWS IoT policy. Is your device actually allowed to publish or subscribe to the topics it's trying to use? If the policy is too restrictive, your Pi might connect but then be unable to do anything useful. Check the policy details in the AWS console to ensure your device has the necessary permissions. These little details can often be the source of a "problem connecting securely," so it's good to be thorough.
Frequently Asked Questions
How can I make sure my Raspberry Pi connection to AWS is truly secure?
Making your Raspberry Pi connection to AWS truly secure involves several layers of protection. First, you need to use strong authentication methods, like X.509 certificates and private keys, which prove your device's identity. Then, you should use secure communication protocols, typically MQTT over TLS, which encrypts the data moving between your Pi and AWS IoT Core. Furthermore, restrict what your Pi can do in AWS using tightly defined IoT policies, granting only the necessary permissions
- No Te Duermas Morena
- Yes Yes Yes Meme
- How To Get Rid Of Gnats
- Nagi Hikaru
- How To Get Nail Glue Off Skin

Securely Connect RemoteIoT VPC Raspberry Pi AWS Example

Securely Connect Remote IoT VPC Raspberry Pi AWS: A Comprehensive Guide
Secure Connection between AWS VPC and a Raspberry Pi | Tales of a